Virtual Data Room Permissions for Due Diligence (Most Over-Share) in 2026
Co-founder and CEO at Peony. I built the data room platform with a background in document security, file systems, and AI. Founded Peony in 2021 in San Francisco.
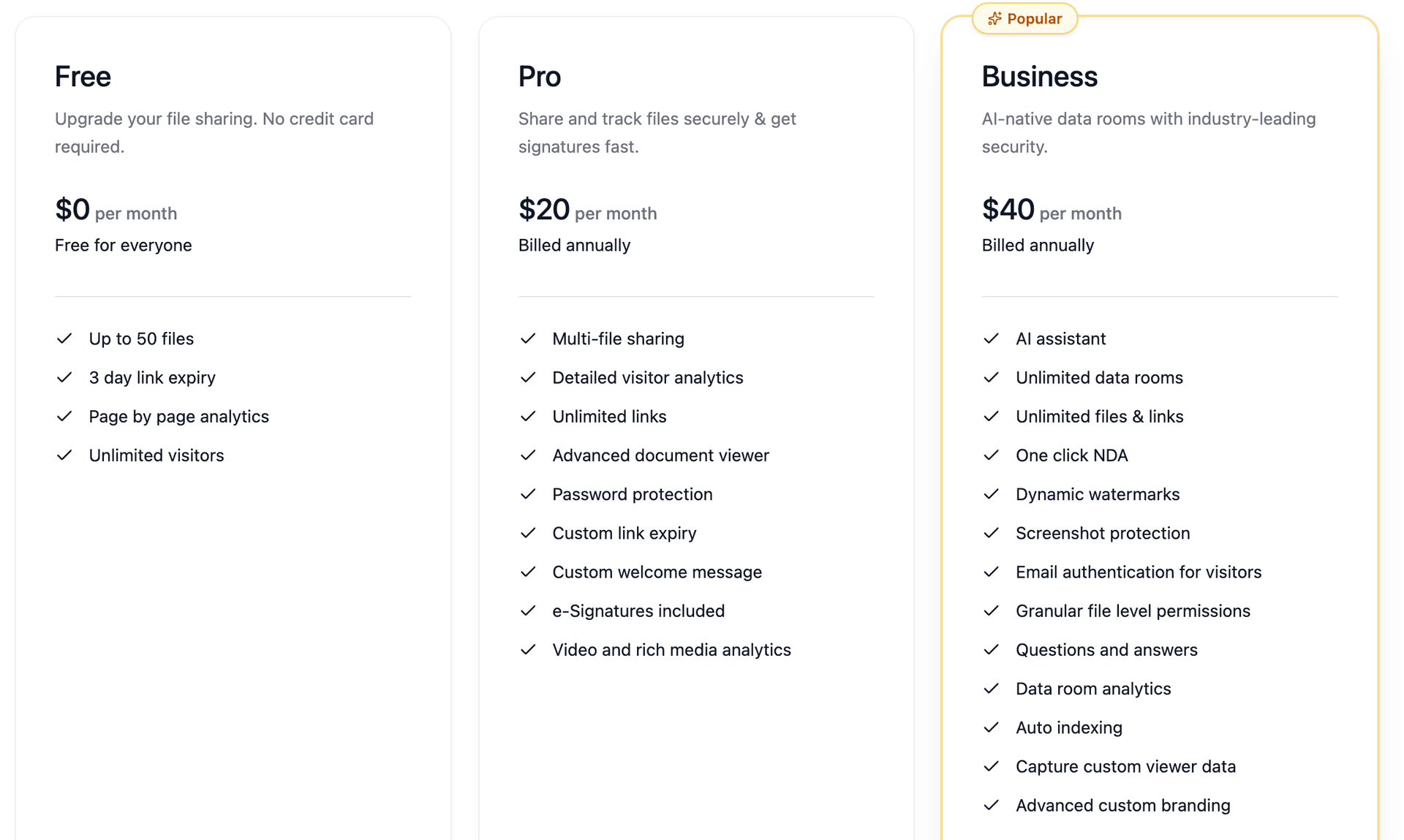
Virtual data room permissions for due diligence define who can view, download, print, and share documents during fundraising or M&A processes — and getting them wrong is the fastest way to leak confidential information to the wrong party. I run Peony (a data room platform starting free), and I have watched founders accidentally expose their full cap table to 30 investors simultaneously because they set up one access group instead of tiered roles.
TL;DR: Most teams either over-share (faster now, dangerous later) or lock everything down so hard that investors cannot do their jobs. The fix is a role-based permission model with 4 folder sensitivity levels and 4-6 access groups. Peony lets you configure this in under 5 minutes with AI auto-indexing that organizes documents into a permission-ready structure, dynamic watermarks that trace every viewer, and page-level analytics that show who actually reviewed what.
Last updated: March 2026
I have set up data rooms for hundreds of deals through our platform — seed rounds with 5 investors, growth rounds with 20, and M&A processes with competing bidders who absolutely cannot see each other's diligence activity. The pattern is consistent: teams that spend 20 minutes setting up role-based permissions before launch avoid the emergency permission reversals that slow deals down by weeks.
The most common failure I see is the "one group for all investors" approach. A founder shares their entire data room with every investor they have met, then realizes too late that a passing acquaintance from a conference now has access to their detailed financial model and pending legal matters. By the time they revoke access, the documents have been downloaded.
This guide gives you the practical, pressure-tested permission framework I recommend to every founder using Peony.
Who This Is For
Use this guide if you are:
- a founder running seed to growth fundraising,
- a finance or legal lead preparing for M&A,
- or an operator managing sensitive documents with multiple external parties during due diligence.
If you need the broader data room setup first, start with our data room guide, then come back here for permissions.
The Core Rule: Permission by Role, Not by Person
The fastest way to lose control is granting access person-by-person from day one.
Instead, create role-based groups first, then assign users to groups. This scales cleanly from 5 users to 50 without creating admin chaos.
Recommended Permission Groups
For most diligence processes, these groups are enough:
- Internal Admins — Full control: upload, organize, permission changes, invite and remove users.
- Internal Reviewers — View and comment where needed, but no global permission changes.
- Lead Investors or Lead Buyer Team — Broad view access, limited download, no resharing.
- Other Investors / Secondary Bidders — Restricted view, fewer folders, no sensitive appendices initially.
- Legal / Audit / Advisors (External) — Access only to their workstreams.
- Management Presentation Access (Optional) — Narrow, read-only access to selected files.
Keep naming explicit (e.g., EXT_Investor_Tier1, EXT_Buyer_Round2). Fancy names become admin mistakes under pressure.
Start With a Folder Sensitivity Map
Before toggling any settings, label your folders by sensitivity. This single decision prevents 80% of accidental oversharing.
4-Level Sensitivity Model
- Level 1: Public-ish context — Company overview, product deck, high-level KPI summary.
- Level 2: Standard confidential — Financial model, customer contracts (non-critical), operating metrics.
- Level 3: High confidential — Detailed cap table, major commercial terms, pricing logic, board materials.
- Level 4: Restricted / clean room — IP-sensitive details, pending legal matters, personally identifiable data.
Then map each folder to a minimum group eligibility rule:
- L1: Most external groups
- L2: Qualified external groups
- L3: Lead party plus advisors only
- L4: Named subset only, often time-bound
Peony's AI auto-indexing organizes uploaded documents into logical folder structures in under 3 minutes — but the sensitivity labels are your responsibility. Classify folders first, then upload.
Permission Settings That Matter Most
You do not need every switch. You need the right switches at the right deal stage.
1. View vs Download
Default to view-only for first access waves.
Move to download only when:
- legal diligence requires offline review,
- counterparties are committed and identified,
- and you have set watermark plus audit log retention.
2. Print Restrictions
If printing is enabled by default, assume your files have effectively left your data room.
Keep print disabled unless explicitly requested and justified.
3. Dynamic Watermarks
Enable watermarks for all external groups from day one.
At minimum include: user email, timestamp, and session identifier. That alone changes user behavior and reduces casual leakage. Peony's dynamic watermarks bake viewer identity into every rendered frame — if a document surfaces somewhere it should not be, you know exactly who leaked it.
4. Screenshot Protection
Screenshot protection blocks and logs capture attempts on sensitive documents. This matters most for Level 3 and Level 4 folders where a single screenshot of your cap table or pending litigation could cause material harm.
5. NDA Gates
Require external parties to sign an NDA before accessing any documents. This is especially important for M&A processes where competing bidders must acknowledge confidentiality obligations before seeing any materials. Peony's built-in NDA gates handle this automatically — no separate DocuSign workflow needed.
6. Expiration Controls
Set user or link expiration for external parties, especially in multi-bidder processes.
Use short windows (7 to 14 days) and renew intentionally, not automatically.
7. Access Revocation Speed
Test revocation before launch. If you remove a user now, how fast is access actually cut off?
In live deals, "eventual revocation" is not acceptable. Peony provides instant revocation — access is cut the moment you click.
Practical Rollout Plan for Fundraising
Fundraising is iterative. Your permissions should be, too.
Stage A: First Meetings (Broad, Controlled)
- Share Level 1 and selected Level 2 folders.
- View-only for all external users.
- Watermarks on.
- No print or download.
Goal: Qualify interest without exposing core risk.
Stage B: Partner Diligence (Deeper, Still Segmented)
- Add deeper financial and customer diligence folders.
- Split lead investors from others.
- Allow limited download only for lead group if needed.
Goal: Help serious investors move fast while keeping optionality.
Stage C: Term Sheet / Confirmatory Diligence
- Provide targeted high-confidence access to requested files.
- Use advisor-specific workstreams.
- Tight expiry plus active monitoring.
Goal: Close quickly without creating permanent overexposure.
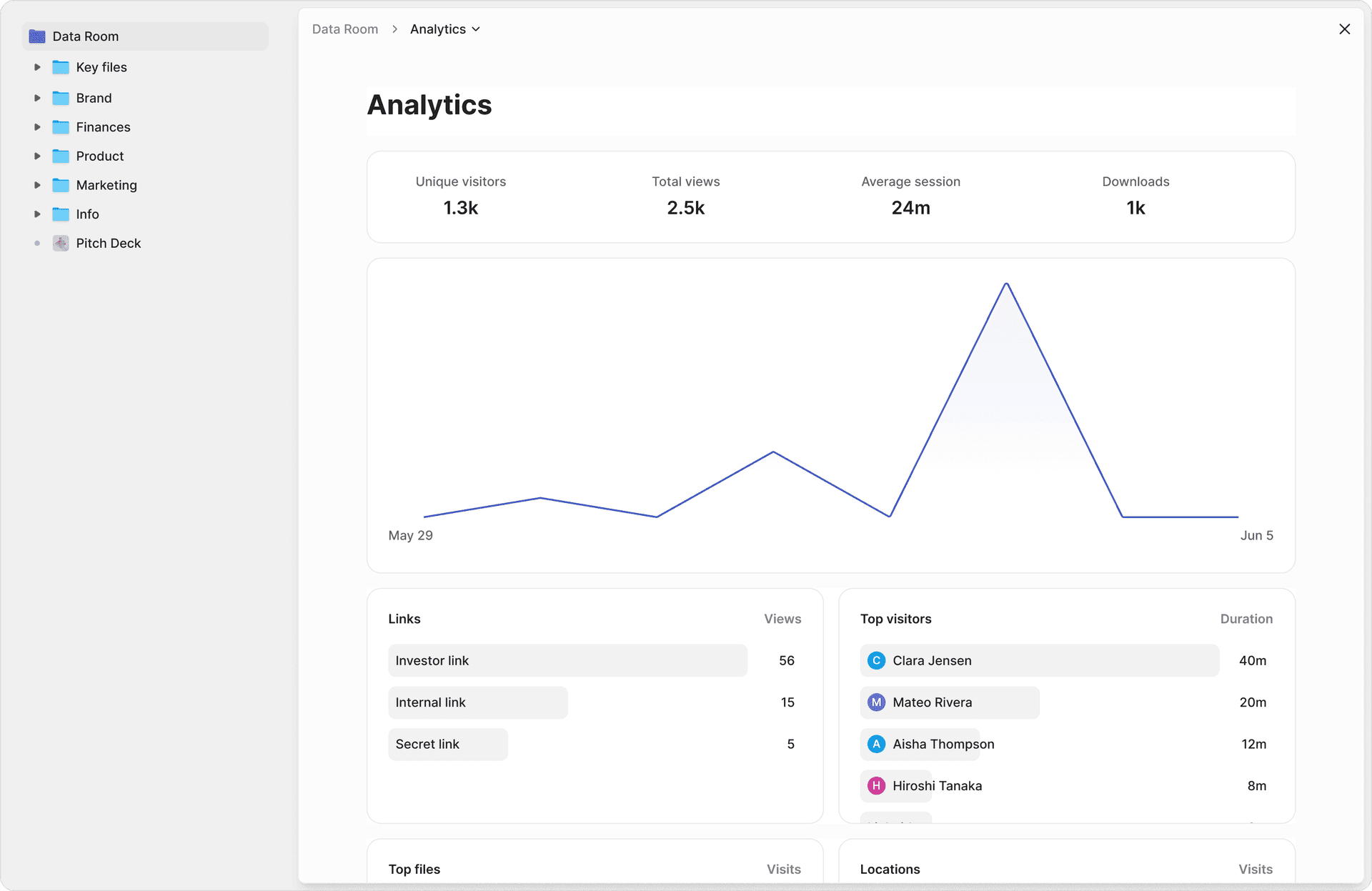
Use page-level analytics throughout all three stages so your team sees what investors are actually reviewing — not just what they requested access to.
Practical Rollout Plan for M&A
M&A needs tighter segmentation and cleaner auditability than fundraising.
Phase 1: Teaser to IOI
- High-level materials only.
- Separate bidder groups early — bidders must never see each other's activity.
- Strict no-download and no-print.
Phase 2: Management Meetings to LOI
- Broader operational and financial folders for shortlisted bidders.
- Buyer-by-buyer isolation.
- Counsel and advisor access split from bidder access.
Phase 3: Exclusivity / Confirmatory
- Controlled release of high-confidential folders.
- Short expiries and fast revocation.
- Daily permission review during intense diligence windows.
Common Permission Mistakes (and Fixes)
Mistake 1: "All investors" in one group forever
Why it fails: Different parties are at different conviction stages and should see different documents. Fix: Split by stage or tier and update weekly.
Mistake 2: Letting multiple admins change rules ad hoc
Why it fails: Inconsistent decisions and no ownership. Fix: One permission owner plus one backup owner.
Mistake 3: Folder-level chaos
Why it fails: Users get accidental inheritance from parent folders. Fix: Define inheritance policy before upload; override only when necessary.
Mistake 4: No permission change log review
Why it fails: Drift accumulates silently. Fix: Quick audit every 48 hours in active diligence. Peony's page-level analytics log every access event automatically.
Mistake 5: Upload-first, classify-later
Why it fails: Sensitive files are exposed before controls are set. Fix: Classify folders first, set permissions, then upload. AI auto-indexing handles the organization, but sensitivity labels are your call.
The 20-Minute Pre-Launch Permission Audit
Run this before inviting any external user to your data room.
- Create test users for each external role.
- Open the room as each role and verify visible folders.
- Try downloading and printing where it should be blocked.
- Check watermark visibility on viewed documents.
- Revoke one test user and confirm immediate loss of access.
- Export access logs and confirm activity is captured clearly.
If any step is ambiguous, fix it before launch. Twenty minutes now prevents weeks of cleanup later.
How to Measure If Permissions Are Working
Permissions are not "set and forget." Track operational signals throughout your deal process.
Good Signals
- External users rarely ask "I cannot find files" after onboarding.
- No emergency permission reversals late in process.
- Internal team can explain exactly who has access to what.
- Time-to-answer diligence requests improves week over week.
Warning Signals
- Frequent last-minute access exceptions.
- Same folder repeatedly toggled between public and restricted.
- No one can confidently list external users by access tier.
- Downloads increase without corresponding deal progress.
Use page-level analytics and audit logs to catch warning signals early. A good system makes auditability easy, not painful.
By the Numbers
- $4.88 million — average cost of a data breach in 2024, much of which stems from unauthorized access to confidential documents (IBM Cost of Data Breach Report, 2024)
- 68% — percentage of data breaches involving a human element like accidental sharing, phishing, or credential theft (Verizon DBIR, 2024)
- 80% — estimated share of accidental oversharing prevented by implementing a folder sensitivity map before granting access
- 48 hours — recommended permission review cycle during active due diligence
- 20 minutes — time required for a pre-launch permission audit that prevents weeks of cleanup
- Under 5 minutes — time to set up a Peony data room with AI auto-indexing, role-based permissions, and dynamic watermarks
Implementation Checklist
Use this checklist with your team before opening your data room to external parties:
- Define deal stage and external audience
- Create role groups before adding individual users
- Label folders with sensitivity levels (L1 through L4)
- Set default view-only for new external groups
- Enable dynamic watermarking for all external access
- Enable screenshot protection for Level 3 and Level 4 folders
- Add NDA gates for all external groups
- Disable print and download unless explicitly required
- Configure expiration windows for external users (7 to 14 days)
- Run the 20-minute pre-launch permission audit
- Assign single permission owner plus backup
- Schedule permission drift review every 48 hours during live diligence
Bottom Line
The difference between a well-run data room and a liability is 20 minutes of permission setup before your first external invite. Role-based groups, folder sensitivity labels, view-only defaults, and dynamic watermarks handle 90% of real-world diligence risk.
Set up your data room with Peony (free) — AI auto-indexing organizes your documents in under 3 minutes, page-level analytics show exactly who reviewed what, and NDA gates plus screenshot protection protect your most sensitive materials from the moment you share them.
Frequently Asked Questions
What are the most important virtual data room permissions to configure first?
Start with role-based access groups, view versus download rules, dynamic watermarking, and link expiration controls. Those four settings handle most real-world diligence risk. Peony lets you configure all four in under 5 minutes with AI auto-indexing that organizes your documents into a permission-ready folder structure automatically.
Should investors be allowed to download files from a data room?
Not by default. Use view-only access for the first wave of external users, then allow selective downloads for committed parties when there is a clear diligence need. Peony dynamic watermarks bake viewer identity into every rendered frame, so even if a file is downloaded, you can trace exactly who distributed it.
How many permission levels should a startup data room have?
Most teams operate well with 4 folder sensitivity levels and 4 to 6 access groups. More than that adds complexity without improving control. Peony data rooms support granular role-based access that maps cleanly to this model, with page-level analytics showing which permission tier is most actively reviewing documents.
How often should we review data room permissions during due diligence?
In active fundraising or M&A, review every 48 hours. During peak deal phases like confirmatory diligence, daily checks are better. Peony page-level analytics make this easy by showing exactly who accessed what and when, so you can spot permission drift before it becomes a problem.
Can one data room setup work for both fundraising and M&A?
Yes, if you use stage-based access groups and keep bidder and investor cohorts segmented. The permission model is similar but M&A requires stricter segmentation between competing bidders. Peony supports both workflows from a single data room with separate trackable links per party.
How do I prevent accidental oversharing in a data room?
Map folders to sensitivity levels before uploading any files, then assign minimum group eligibility per level. This single mapping decision prevents 80 percent of accidental oversharing. Peony NDA gates add an additional layer by requiring external parties to sign before accessing any documents, and screenshot protection blocks and logs unauthorized capture attempts.
What is role-based access control in a virtual data room?
Role-based access control means creating permission groups like Internal Admins, Lead Investors, and External Advisors, then assigning users to groups rather than granting access person by person. This scales cleanly from 5 to 50 external users. Peony data rooms support role-based groups with inheritance rules that propagate permissions across folder hierarchies automatically.
How do I track which documents investors actually reviewed in my data room?
Peony provides page-level analytics showing exactly which pages each reviewer read and for how long, not just whether they opened a file. Combined with personalized sharing links per investor, you can compare engagement across 30 parties simultaneously and identify who spent 20 minutes on your financial model versus who skimmed the pitch deck in 45 seconds.
Related Resources
- What Is a Virtual Data Room — comprehensive VDR guide
- Data Room for Investors — what investors expect in a data room
- Due Diligence Data Room Checklist — due diligence preparation
- Vendor Due Diligence Checklist — TPRM framework
- How to Track Pitch Deck Engagement — analytics for fundraising
- Dynamic Watermarking Guide — protecting documents with viewer identity
- Secure File Sharing Guide — comprehensive security practices
- M&A Solutions — Peony for mergers and acquisitions
- Fundraising Solutions — Peony for fundraising data rooms
- Due Diligence Solutions — Peony for due diligence

