Win defense contracts. Keep CUI locked down.
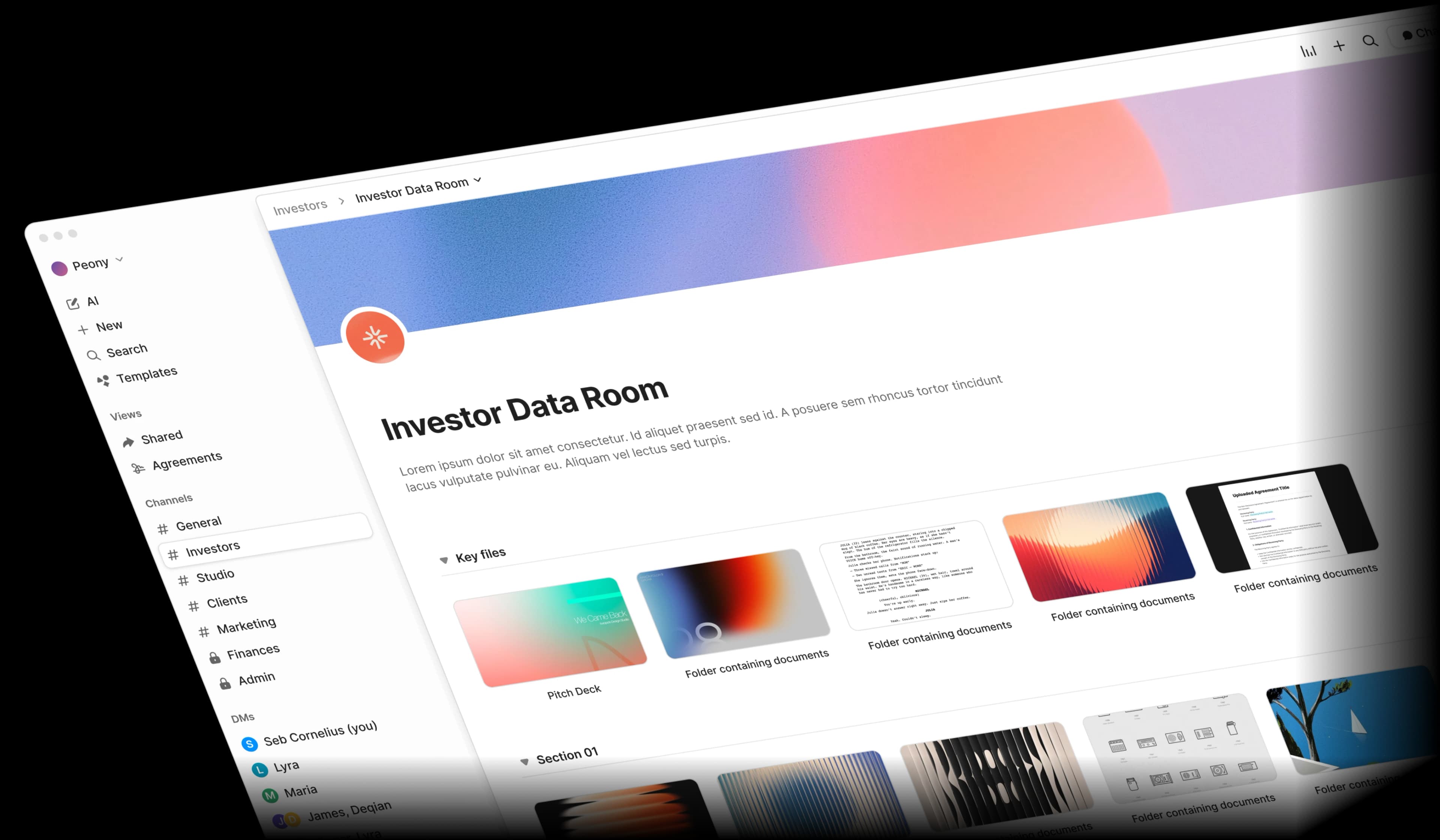
The data room purpose-built for defense contractors and government suppliers. Share ITAR-controlled technical data packages, manage CUI, and run multi-tier subcontractor due diligence with enterprise-grade security.Set up in under 5 minutes.
24/7 dedicated support for enterprise deals
Defense document sharing is a compliance minefield
Between ITAR-controlled technical drawings, CUI handling requirements, and multi-tier subcontractor document flows, defense teams risk export violations every time they share a file insecurely.
ITAR export risk
Technical data packages, DD254 forms, and controlled drawings shared via email or generic cloud storage risk unauthorized foreign access and export violations.
CUI handling gaps
Controlled Unclassified Information requires NIST 800-171 compliant handling. Most file-sharing tools cannot prove access controls or generate proper audit trails.
Subcontractor sprawl
Contract Data Requirements Lists and technical approaches flow across multiple tiers of suppliers. Managing who sees what across primes, subs, and government reviewers is error-prone.
Proposal leak prevention
Contract proposals with sensitive pricing, technical approaches, and SF1449 forms need leak-proof sharing. Competitors gaining access can cost you the contract.
Built for how defense teams actually work
Peony gives you enterprise-grade security that supports ITAR compliance workflows, CMMC-aligned audit trails, and AI-powered document intelligence — all at a fraction of legacy VDR pricing.
Screenshot protection, watermarks, NDA gates, and mandatory 2FA
ITAR-controlled technical drawings and distribution-statement documents deserve more than a password. Peony blocks screenshots, stamps every page with the viewer's identity, requires NDA signatures before access, and enforces two-factor authentication for all users.
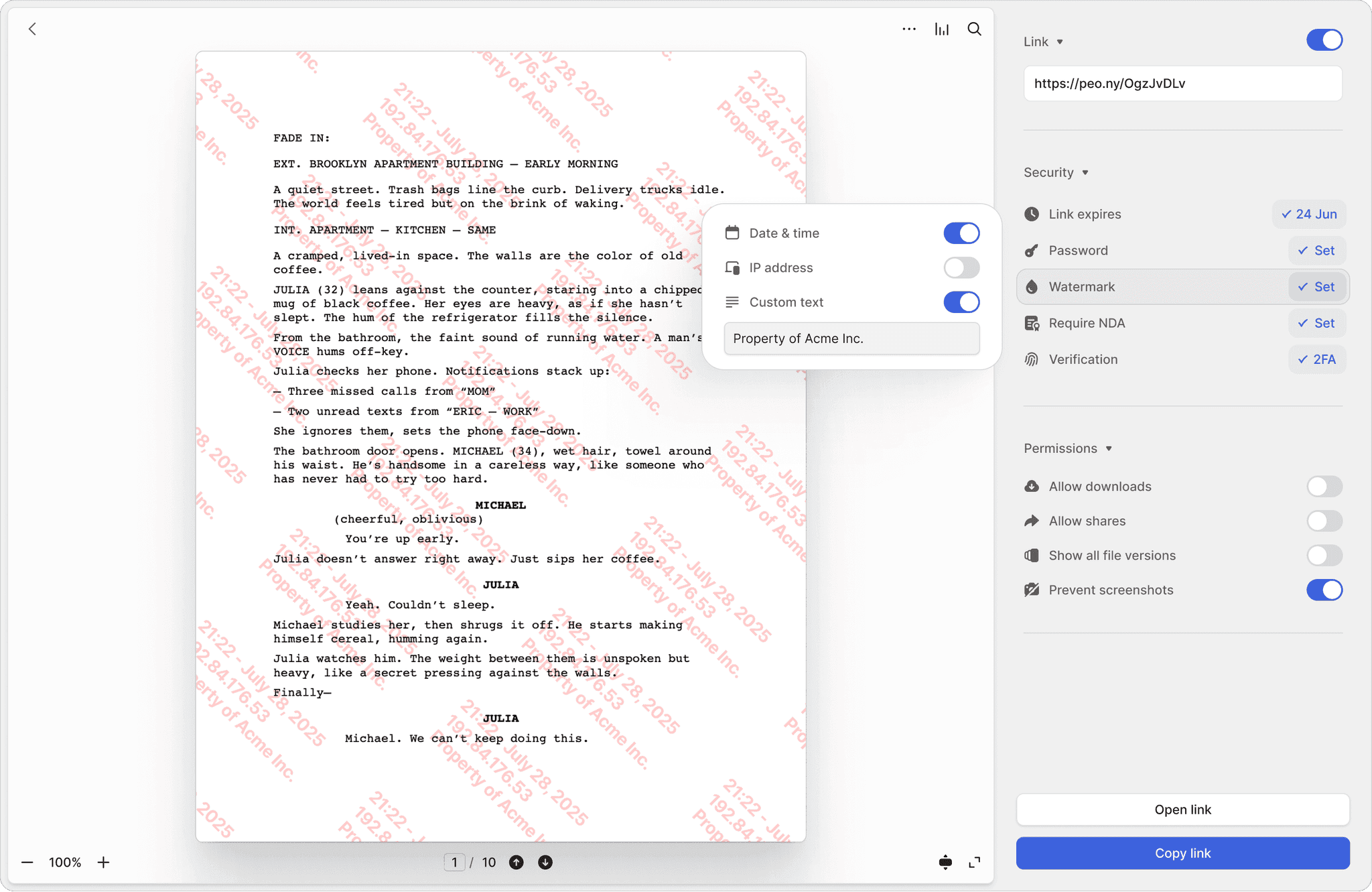
Screenshot protection
Block screen captures of ITAR-controlled technical drawings, engineering specifications, and distribution-statement documents. Prevent unauthorized duplication of export-controlled data.
Dynamic watermarks
Every page stamped with the viewer's identity and timestamp. If a controlled document leaks, you have a clear trail back to the source for compliance investigations.
NDA-gated access
Require subcontractors and partners to sign non-disclosure agreements before viewing technical data packages or DD254 forms. Fully integrated e-signatures included.
Mandatory 2FA
Enforce two-factor authentication for every user accessing your data room. Meet NIST 800-171 multi-factor authentication requirements for CUI protection.
CMMC-aligned logs for every document interaction
Track every view, download, and signature with timestamped logs. Page-by-page analytics show exactly which sections of your technical data packages and Contract Data Requirements Lists reviewers focused on — exportable for NIST 800-171 and CMMC readiness assessments.
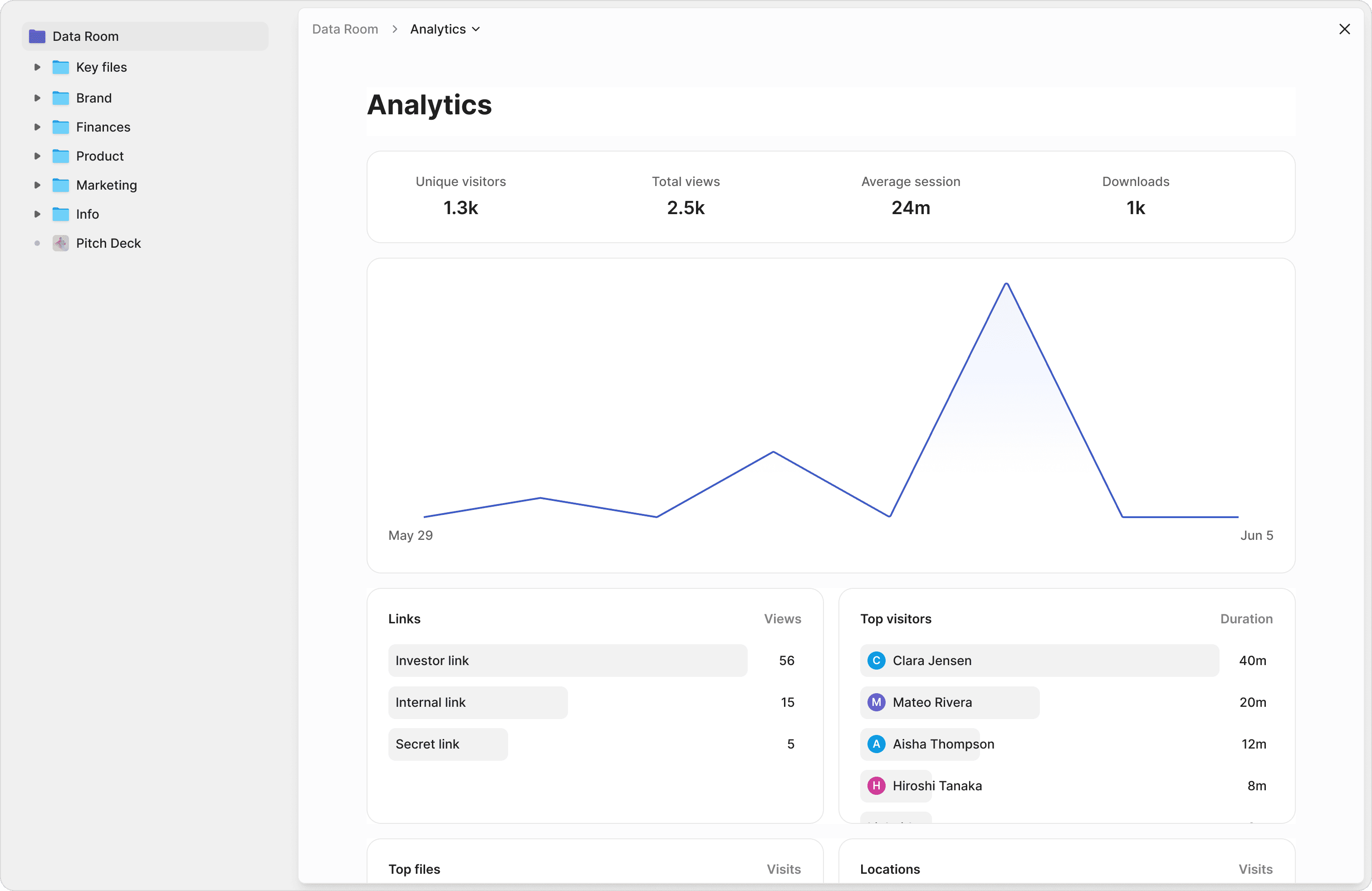
Page-by-page tracking
See which pages of your technical data packages, engineering drawings, or contract proposals government evaluators and subcontractors spent the most time reviewing.
Exportable compliance reports
Generate audit trails with timestamps, IP addresses, and device details. Support NIST 800-171 access control documentation and CMMC assessment evidence collection.
Granular access control
Give prime contractors full access to proposals, limit subcontractors to their specific work packages, and provide government contracting officers read-only access to compliance documentation.
Search across proposals, compliance docs, and contract files
Stop digging through hundreds of PDFs. Ask natural language questions across your entire document library and get instant, sourced answers from technical proposals, DFARS clauses, and compliance documentation.
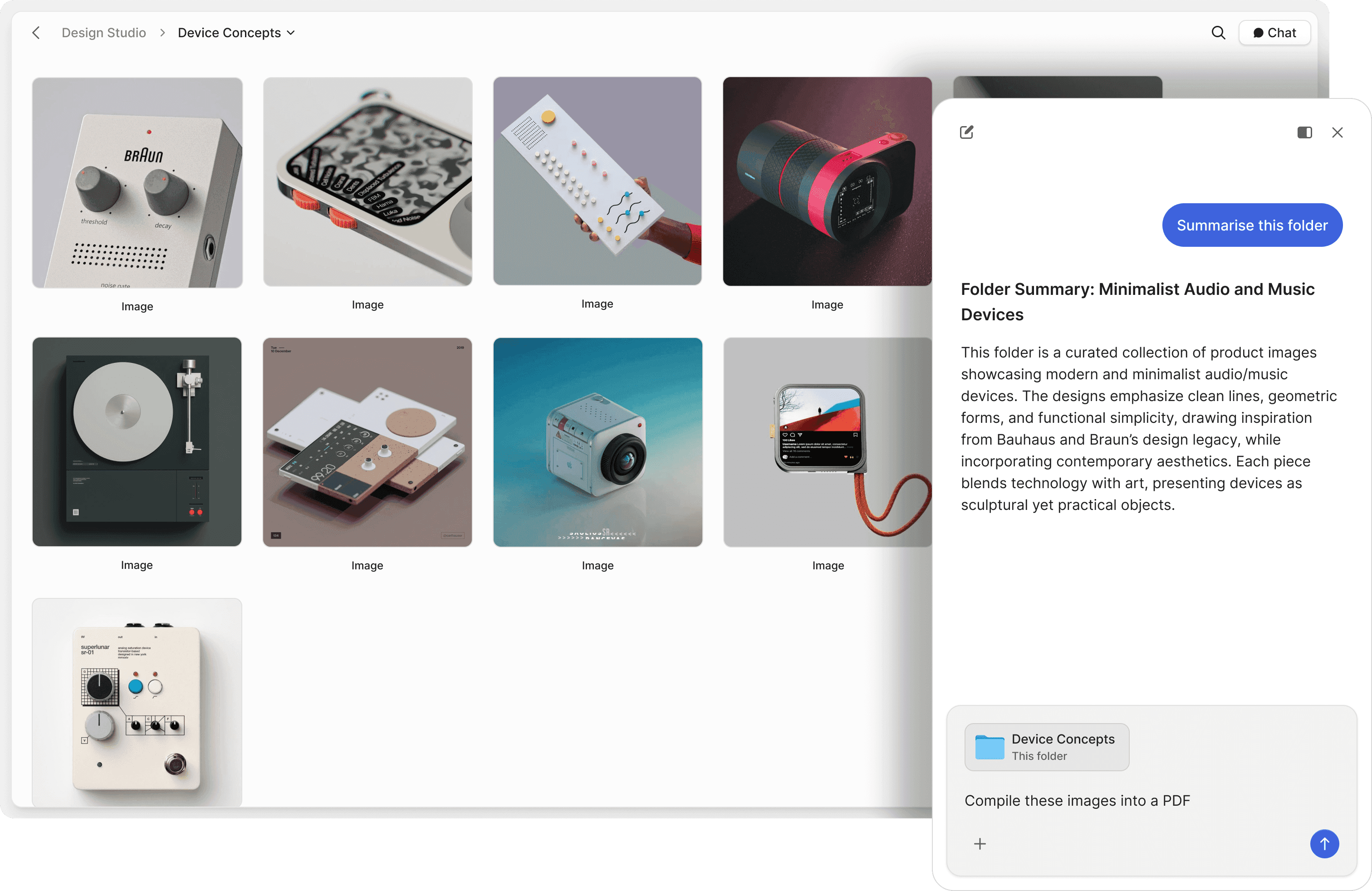
Chat with contract files
Ask questions across technical proposals, Contract Data Requirements Lists, and compliance documents. AI retrieves answers with exact source references.
Find DFARS clauses instantly
Search your data room in plain English. Find specific DFARS requirements, contract clauses, or technical specifications without remembering file names or clause numbers.
Proposal review on autopilot
Let AI answer reviewer questions about your technical approach, past performance, and compliance posture 24/7. Track what evaluators ask to strengthen future proposals.
"Peony is exactly what we needed — clean interface, enterprise-grade security, and it just works. Our team was up and running in minutes."
Panos Moutafis
Founder & CEO, Zenus
Akash Ghavalkar
Co-founder & COO, Third Space
"We'd been searching for a solution like Peony for ages, and it has completely transformed our workflows. What used to take hours every week is now effortless — Peony saves us so much time that we were finally able to move away from Dropbox Sign. It's been a total game changer!"
Frequently asked questions
What documents do defense contractors include in a data room for classified program reviews?
A defense data room typically includes ITAR-controlled technical data packages, DD254 forms, engineering drawings, contract proposals with SF1449 forms, Contract Data Requirements Lists (CDRLs), DFARS compliance documentation, technical approaches, past performance volumes, and subcontractor flow-down agreements. Peony's AI-generated due diligence checklists tailored to defense contracts track which documents are uploaded versus missing, giving you completeness scoring before submission deadlines.
How does a data room support ITAR compliance?
ITAR requires strict access controls to prevent unauthorized foreign persons from viewing export-controlled technical data. Peony enforces two-factor authentication for all users, provides screenshot protection to prevent unauthorized duplication, stamps every page with dynamic watermarks for leak traceability, and generates exportable audit trails with timestamps and IP addresses for DDTC compliance documentation. All documents are secured with AES-256 encryption at rest and TLS 1.3 in transit on Peony's SOC 2-ready infrastructure. Peony is GDPR, CCPA, and HIPAA compliant.
What is CMMC and how does a data room help with certification?
CMMC (Cybersecurity Maturity Model Certification) is the Department of Defense framework for protecting Controlled Unclassified Information (CUI). Peony supports CMMC readiness with NIST 800-171 aligned access controls, mandatory 2FA, complete audit trails for every document interaction, and granular permissions that restrict CUI access to authorized personnel only.
How do I prevent proposals and technical approaches from leaking to competitors?
Contract proposals containing sensitive pricing, technical approaches, and proprietary methods are prime targets for competitors. Peony blocks screenshots, stamps every page with the viewer's identity and timestamp via dynamic watermarks, requires NDA signatures before access with integrated e-signatures, and lets you revoke access instantly if a subcontractor relationship changes. Peony's controlled redaction also lets you permanently black out sensitive pricing figures or proprietary methods before sharing proposals with subcontractors.
Can a data room manage multi-tier subcontractor document flows?
Yes. Defense contracts involve document flows across primes, subs, and government contracting officers who each need controlled access. Peony supports folder-level and document-level permissions so prime contractors see full proposals, subcontractors access only their work packages, and government evaluators get read-only access to compliance documentation — all with separate audit trails per viewer.
How does AI help with defense contract document review?
Defense proposals and compliance packages involve hundreds of pages across technical volumes, CDRLs, and DFARS clauses. Peony's AI-powered document chat lets reviewers ask natural language questions across the entire data room and get sourced answers with exact page references. AI-powered Q&A is available on the Business plan ($40/admin/month) — a fraction of what legacy VDRs like Ideals or Firmex charge for similar capabilities.
How much does a defense data room cost for a CMMC-compliant contractor managing CUI?
Legacy VDRs like Ideals and Datasite charge enterprise prices for basic compliance features. Peony offers a free plan ($0) with 2 GB of storage, scales to Pro at $20 per admin per month (200 GB) and Business at $40 per admin per month (unlimited storage) with screenshot protection, dynamic watermarks, NDA gating, and AI-powered Q&A. Peony has no per-viewer, per-page, or per-link limits, so costs stay predictable as your subcontractor team scales.
What support does Peony provide defense contractors during active program reviews?
Peony provides 24/7 dedicated support for enterprise clients — because when a government contracting officer or prime contractor cannot access ITAR-controlled technical data during a submission deadline, the contracts team needs immediate resolution. Enterprise support is available to teams who book a demo with our deal infrastructure team. Every plan includes in-app help, documentation, and email support. For defense programs where access failures can jeopardize contract timelines, Peony ensures no authorized party hits a dead end.
What audit trail features does Peony provide for CUI handling?
Peony generates timestamped access logs with IP addresses, device details, and page-by-page view duration for every document interaction. These exportable compliance reports support NIST 800-171 access control documentation and CMMC assessment evidence collection, showing exactly who accessed controlled information and when.
