Screenshot-Block Data Rooms with Attempt Logging (2026 Banker Guide)

Co-founder at Peony. Former VC at Backed VC and growth-equity investor at Target Global — I write about investors, fundraising, and deal advisors from the deal-side perspective I spent years in.
Set up my next data room with Sean
Screenshot-Block Data Rooms with Attempt Logging — A 2026 Banker's Audit-Trail Playbook
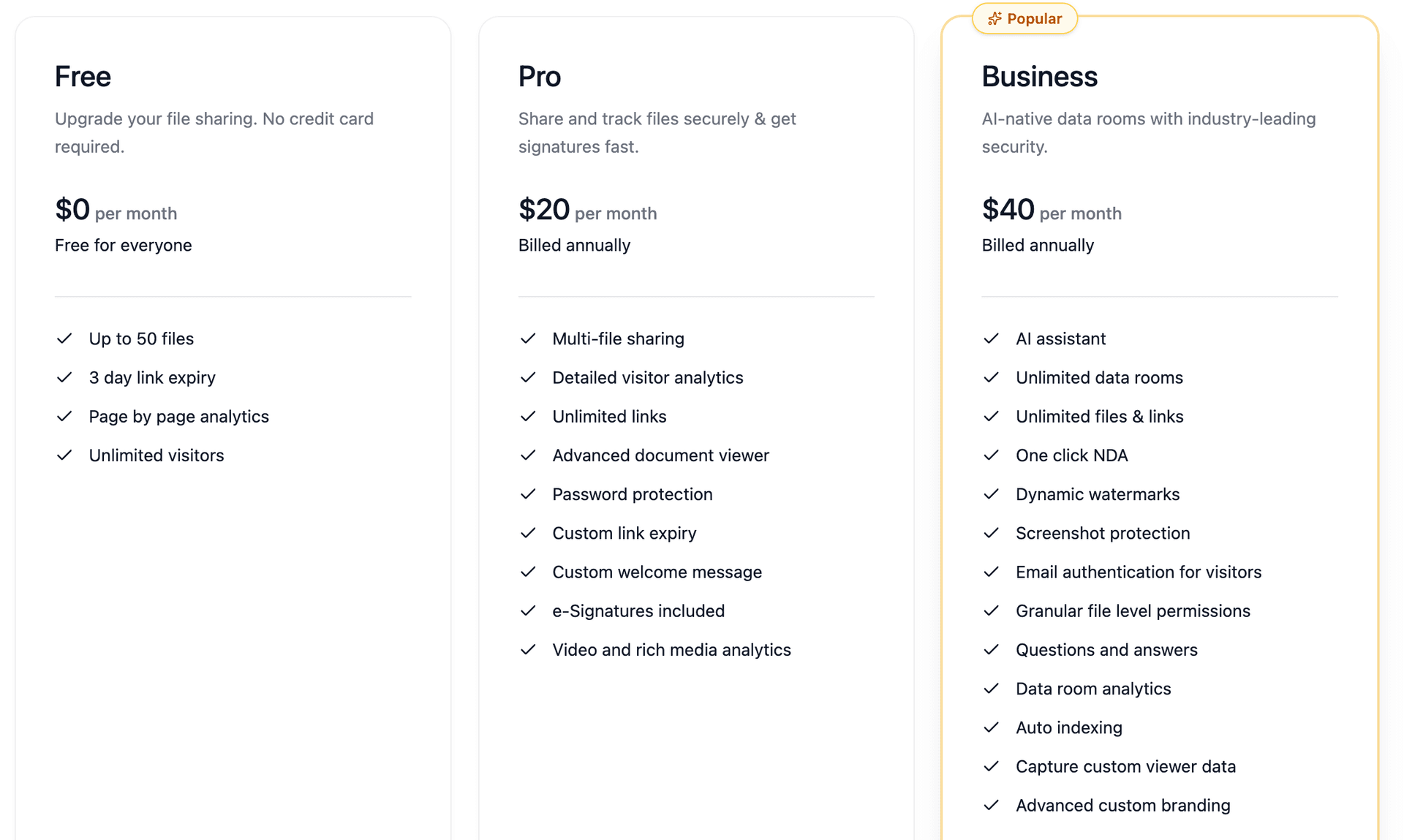
TL;DR. I run sell-side auctions on $80-300M EV mid-market deals with 8-15 bidders and a 30-50% EU bidder mix. The differentiating product on a 2026 data room is not the screenshot-block wall — it is the attempt log, the per-event evidentiary record that survives the leak. Anchor stats: 42% of US transactions over $1B leaked pre-announcement in 2025 (H/Advisors Abernathy "When Deals Spring a Leak" Volume VI, January 29, 2026), with leaks now firing 72 days before announcement on average (up 20 days from 2024). 9.5% of global M&A deals leaked in 2024 — the highest figure in the 16-year Intralinks/Bayes Business School M&A Deal Leaks study. Insider risk costs an organization $17.4M annualized (Ponemon 2025 Cost of Insider Risks via DTEX). U.S. breach cost hit an all-time high of $10.22M in 2025 (IBM Cost of a Data Breach 2025). On the platform side, only Datasite Diligence and Peony Business explicitly log the screenshot-attempt event in a way deal counsel will accept; Intralinks VDRPro's print-screen prevention is Microsoft-Office-on-Windows-only per its own support docs; Firmex has zero screenshot protection per Papermark's 2026 review. Peony Business at $40 per admin per month is the rounding error against the $4.44M global average breach cost.
If you are a founder protecting a pitch deck on Mac and iPhone, see block-screenshots-pitch-deck — that post is the OS-level founder playbook for fundraising decks. This post is the data-room and banker side, with the audit-trail focus that deal counsel actually deposes on. The persona is the sell-side MD running a competitive auction. The signature artifact is the per-attempt log entry, not the screenshot wall.
I have run mandates where the seller's CFO was paranoid about CIM leakage to direct competitors, where deal counsel needed evidentiary-grade audit trails, where procurement at two bidder-side firms asked for SOC 2 attestation on the data-room platform, and where buyer #3 kept asking compliance questions about screenshot logs. The same five-component stack answers every one of those situations: (1) capture every screenshot attempt as a discrete event with the full field set; (2) store the log server-side in a tamper-evident way; (3) verify integrity through SOC 2 Type II and ISO 27001:2022; (4) export per-bidder for outside counsel; (5) layer the click-through NDA over the top so the contractual remedy survives even when forensic attribution does not.
The rest of the post is the playbook.
Why Does a Screenshot Attempt Log Matter More Than a Watermark in M&A?
Because watermarks deter while logs prove — and on the modal sell-side process, the gap between deterrence and proof is the gap between an NDA breach claim that survives the FRE 901 admissibility test and one that does not.
A watermark identifies the leaker only if the document is recovered intact. An attempt log identifies which bidder tried to circumvent controls whether or not the leak ever materializes — which is the only forensic signal a banker has when a leak shows up in the Wall Street Journal but the screenshot was zoom-cropped, OCR-cleaned, or photographed off-screen with a second device. Three failure modes show why both layers are needed.
Failure mode 1 — watermark stripped or cropped. Bidder zooms past the watermark before capturing. The document content survives in the screenshot; the attribution is lost. Without an attempt log, the seller has a leaked artifact and no evidence of who took the screenshot. Watermark fails alone here.
Failure mode 2 — phone-camera off-screen capture. No software prevents a camera pointed at a screen. The iOS UIScreen.isCaptured flag does not fire because the operating system never sees the capture. The screenshot_attempt log entry does not get written. But — and this is the architectural point — a per-bidder dynamic watermark embedded server-side into the rendered image bytes (not a CSS overlay) survives the camera shot just like any other pixel. The watermark does the attribution work the log cannot. Log fails alone here; watermark succeeds.
Failure mode 3 — bidder OCRs a phone-camera photo of a watermark-cropped zoom. Both forensic layers fail. The contractual remedy carries: a conspicuous click-through NDA gate at room entry plus the audit-log capture of the assent event (timestamp + IP + user_email) gives Defend Trade Secrets Act 18 USC §1836 standing for damages, injunctions, and attorney's fees regardless of forensic attribution. This is why bankers run a 3-layer stack: log + watermark + NDA, not a 1-layer stack.
The persona-tells from a $150M EBITDA services auction with 12 bidders: the seller's CFO is paranoid about CIM leakage to two direct competitors who are also bidding; deal counsel (Kirkland or Latham or Skadden) has flagged that NDA breach claims hinge on chain-of-custody on the data room audit log; procurement at two bidder-side firms is asking for SOC 2 Type II attestation. The 3-layer stack answers all three constituencies in one platform configuration.
Which Data Rooms Actually Log Screenshot Attempts as a Discrete Event in 2026?
Most VDRs log views, downloads, and prints. The screenshot attempt event is a meaningful gap in most legacy VDRs. The following matrix is verified against vendor support docs and at-most-12-month independent reviews.
| Platform | Screenshot attempt logged as discrete event? | Block at viewer? | Per-attempt timestamp + IP + user? | Per-document granularity? | Exportable PDF or CSV audit trail? | SOC 2 Type II? | ISO 27001? | Tamper-evident log? |
|---|---|---|---|---|---|---|---|---|
| Datasite Diligence | Asserted via Tracker docs as part of broader activity log; first-party screenshot_attempt event taxonomy not explicitly published | Partial — no native screen-capture block at OS level; print and download restrictions only | Yes — timestamp + viewer ID; IP capture varies by config | Yes — page-level | Yes — Tracker tab exports to Excel | Yes | Yes (ISO 27001/27017/27018/27701) | "Complete unchangeable audit trail" per Datasite docs |
| Intralinks VDRPro | Partial — print-screen prevention works only on MS Office files, on Windows, with specific permissions per Intralinks's own Document protection VDRPro support article; does not extend to PDFs, macOS, Linux | Partial — same constraint | Yes — Advanced Reporting plus Time Tracking in Secure Viewer | Yes — folder and document level | Yes — Compliance Archives (Audit + Doc-Audit folders) | Yes | Yes | Yes — compliance archives |
| Drooms NXG | Partial — activity reporting "down to single document page"; explicit screenshot-attempt event not documented in public knowledge base | Partial — view-only mode plus IP filtering | Yes — IP filtering, activity reporting | Yes — single-page granularity | Yes — activity reports | Yes (Swiss/German servers) | Yes | Yes — GDPR-compliant audit trail |
| Firmex | No — Firmex has zero screenshot protection on any tier per Papermark Firmex review 2026; audit log captures views, downloads, and prints only | No | Yes — full activity log per user and document | Yes | Yes — activity log export | Yes | Yes | Yes — full audit trail |
| iDeals | Partial — Fence View overlays a barred screen on the document but does not log a screenshot attempt event; dynamic watermarks include name, IP, and time | Yes — Fence View blocks portion of screen | Yes — names, IPs, times in watermark plus audit | Yes | Yes — full audit trail meeting compliance standards | Yes (SOC 2 + SOC 3) | Yes | Yes |
| Box Enterprise Advanced | No — Box Enterprise Advanced (launched January 2025) has no native screenshot-block and no per-attempt log; no dynamic watermarking, no NDA gates | No | Partial — file-access logs but no attempt event | Folder and file level | Yes — admin events export | Yes | Yes | Standard |
| DocSend (Dropbox) | No — DocSend cannot prevent screenshotting on mobile or browsers with extensions per DocSend's own help materials; CSS overlay watermark strips on download | No | Partial — view tracking only | Document level | Yes — basic export | Yes | Yes | No specific tamper-evidence |
| Citrix ShareFile | Partial — screen-capture prevention applies only to Microsoft Office files, on Windows, with permission gating; no PDF coverage | Partial | Yes — view and download events | File level | Yes | Yes | Yes | Standard |
| SecureDocs | Partial — view-only mode plus dynamic watermarks plus a one-click privacy blind; explicit screenshot-attempt event not documented in public docs | Partial — privacy blind | Yes — full audit trail | File and user filterable | Yes — scheduled daily audit-log emails | Yes | Yes | Yes |
| Peony Business ($40/admin/mo) | Yes — explicit screenshot_attempt event captured per file, per user, per slide; Slack and email alert within seconds | Yes — disables screenshot shortcuts, screen recording, and browser extensions at browser level; iOS UIScreen.isCaptured plus macOS ScreenCaptureKit hooks | Yes — viewer email, document, slide, UTC timestamp, IP, browser fingerprint | Yes — page-level | Yes — exportable PDF audit log | Yes | Yes | Yes — server-side render makes log and watermark tamper-evident |
Banker's reading of the matrix. Two platforms — Datasite Diligence and Peony Business — explicitly capture the screenshot-attempt event as a discrete audit event the banker can paste into a deposition packet. iDeals comes closest with Fence View but does not document a per-attempt event tied to the overlay. Intralinks's screenshot prevention is a Microsoft-Office-on-Windows-only capability, which is meaningless for the modal CIM and financial-model PDF workflow. Box, Firmex, and DocSend have no native screenshot block at all — a structural gap that cannot be closed at the file-share layer. ShareFile's restriction matches Intralinks: Office files on Windows only.
The first-party Datasite documentation does not explicitly carve out screenshot_attempt as a typed event; the assertion shows up in third-party reviews and the event rolls up into the broader Tracker activity log. Honest read: Datasite's audit trail is comprehensive, but the screenshot-attempt-as-distinct-event claim is asserted in third-party reviews more than in Datasite's first-party docs. If your deal counsel is the type to read vendor documentation literally, ask Datasite's deal team for the event taxonomy in writing before procurement signs the MSA.
What Compliance Standards Require Per-Attempt Audit Logging?
None require screenshot events by name, but several require equivalent granularity. The compliance matrix below is the artifact procurement at bidder-side firms keeps asking for. Paste it into your RFP response.
| Framework | Specific Control | What It Requires of a Data Room | How an Attempt Log Maps |
|---|---|---|---|
| SOC 2 Trust Services Criteria CC6.1 (Logical Access Security) | Unique user IDs, MFA, role-based access; access matrix maintained | Data room must produce per-user, per-document access logs with role attribution | Screenshot-attempt log = direct evidence of access-control enforcement |
| SOC 2 Trust Services Criteria CC7.2 (Monitor System Components) | Centralized log monitoring, anomaly detection, security event triage; logs retained at least 12 months | Data room logs must be centralized, queryable, alerting on anomaly | Per-attempt screenshot event qualifies as a security event triggering CC7.2 monitoring |
| ISO 27001:2022 Annex A.8.15 (Logging) — formerly A.12.4.1 | Event logs produced, retained, regularly reviewed; recording user activities, exceptions, defects, security events | Data room must log user activities and protect logs from tampering (8.15.2 Protection of log information) | Screenshot attempts are user activities subject to logging; tamper-evident store required |
| ISO 27001:2022 A.8.15.3 | Logs protected against tampering; administrators may not delete logs of their own activities | Data room cannot allow admins to scrub their own session logs | Server-rendered log entries with hash chains satisfy this |
| NIST 800-53 Rev. 5 AU-2 (Event Logging) | Identify event types capable of being logged; specify event types and frequency | Data room must declare screenshot attempt as logged event type | Vendor must publish log-event taxonomy including capture-attempt events |
| NIST 800-53 AU-3 (Content of Audit Records) | Record content: event type, time, location, source, outcome, user identity, success or fail | Per-attempt log must capture event_type=screenshot_attempt, timestamp_utc, source_ip, document_id, slide or page, user_email, outcome | Peony Screenshield log fields map 1:1 |
| NIST 800-53 AU-12 (Audit Record Generation) | System-wide, time-correlated audit trail; standardized formats; query parameters for PII access | Logs must be time-synchronized across viewer, server, document | NTP-synced server-rendered log satisfies AU-12 |
| GDPR Article 30 (Records of Processing) | Controllers must maintain RoPA in writing or electronic form; processing purposes, data categories, security measures | Data room access logs constitute part of "technical and organizational security measures" disclosed to supervisory authorities | Logs as RoPA evidence in 2024 EDPB coordinated enforcement |
| GDPR Article 32 (Security of Processing) | Implement appropriate technical and organizational measures; ability to ensure ongoing confidentiality | Per-document access controls plus audit log demonstrate Article 32 compliance | Attempt log = active-defense evidence |
| HIPAA 164.312(b) (Audit Controls) | Implement hardware, software, or procedural mechanisms recording activity in systems containing ePHI | For biotech and clinical-trial data rooms: every ePHI access (including attempted screenshots of patient data) must be recorded | Screenshot attempt on ePHI = required event. January 6, 2025 NPRM proposes eliminating addressable / required distinction — audit controls would become strictly mandatory |
| SOX Section 404 (Internal Controls over Financial Reporting) | Public-company management must assess internal control effectiveness; document, test, report | Sell-side data room for public-target acquisition: access controls plus tamper-evident logs supporting financial-data confidentiality | Logs underpin auditor sign-off on access-control effectiveness |
| eIDAS Regulation (EU) 910/2014 | Electronic-signature audit trail must be chronological, tamper-evident, cover signer identity plus timestamps plus IP plus document access | For EU-side cross-border deals: audit-trail standard for click-through NDA enforceability | NDA + log combo demonstrates qualified e-signature compliance for the gating layer |
The procurement-grade short answer. SOC 2 Type II plus ISO 27001:2022 with Annex A.8.15 in scope is the minimum bar. NIST 800-53 Rev. 5 AU-2 / AU-3 / AU-12 maps the log-content requirements U.S. deal counsel cares about. GDPR Article 30 and Article 32 plus eIDAS Article 25 cover the EU-bidder layer. HIPAA and SOX are sector overlays — biotech and clinical-trial data rooms need 164.312(b); public-target sell-side processes need SOX 404 internal-controls evidence. Datasite, Intralinks, iDeals, Drooms, and Peony all attest to SOC 2 Type II and ISO 27001 — but Type I (point-in-time) attestations and out-of-date certifications are the trap deal counsel will flag.
How Did the 2025 Deal-Leak Spike Change the Banker's Forensic Playbook?
By raising the floor on what counts as a defensible chain of custody. Five anchor numbers reframe the playbook.
Anchor 1 — 16-year leak high. Per the Intralinks / Bayes Business School 2025 M&A Deal Leaks Report, 9.5% of global M&A deals leaked in 2024 — the highest figure in the study's 16-year history (analyzing more than 15,000 public acquisitions). Leaked deals that complete generate takeover premiums 18 percentage points higher than non-leaked deals; acquirers see long-term returns 8 percentage points higher; leaked deals take roughly 2 additional weeks to close.
Anchor 2 — 42% of US transactions over $1B leaked in 2025. Per H/Advisors Abernathy "When Deals Spring a Leak" Volume VI press release dated January 29, 2026, 42% of US transactions $1B+ leaked pre-announcement in 2025 — the highest rate since H/Advisors began tracking. Average leak now happens 72 days before announcement (up 20 days from 2024). Sector breakdown 2025: Entertainment, Leisure, and Media at 67% (over two-thirds, second straight year); Tech at 50%; Healthcare and Pharma at 45%. Leaked deals received 4 times the negative online commentary of non-leaked deals. Note on scope: the H/Advisors 42% figure covers $1B+ US deals in 2025; an earlier H/Advisors press release covering 2024 data cited "more than 60%" for the subset of $10B+ deals — do not conflate the two scopes when citing.
Anchor 3 — third-party breaches doubled. Per the Verizon 2025 Data Breach Investigations Report, third-party breaches doubled to 30% of all breaches (up from 15% the prior year). 60% of breaches involve the human element (errors, social engineering, misuse). 8% of breaches involve privilege misuse — the unauthorized use of data violating organizational policy, which is exactly the bidder-mishandling-data scenario. Dataset: 22,000+ incidents, 12,195 confirmed breaches.
Anchor 4 — insider risk at $17.4M annualized. Per the 2025 Cost of Insider Risks Global Report from Ponemon (DTEX summary), the average annualized cost of insider risk is $17.4M, up from $16.2M in 2023. Cost per credential-theft incident: $779,797 (most expensive). Per malicious-act incident: $715,366. Per negligence incident: $676,517. Containment cost: $211,021 per event (up from $179,209 in 2023).
Anchor 5 — 241-day mean time to identify and contain. Per the IBM Cost of a Data Breach Report 2025, the global average breach cost is $4.44M (down 9% year-over-year — first decline in 5 years); US average is $10.22M (up 9%, all-time high); mean time to identify and contain is 241 days (a 9-year low); AI-powered security saves $1.9M and resolves breaches 80 days faster.
The forensic playbook shift. Five years ago, "audit log" meant a CSV of view events. In 2026, deal counsel deposes on chain of custody. The 2025 numbers raise the floor in three ways: (1) third-party (bidder) attribution is now the most likely leak vector at 30% of breaches — Verizon DBIR 2025; (2) the 72-day pre-announcement leak window means the audit log has to be queryable retroactively across a longer window than the auction itself; (3) the 241-day mean time to identify means the audit log has to survive intact for at least 12 months, ideally the full 7-year post-close discovery window deal counsel asks for.
What Is the M&A Audit-Log Evidentiary Chain (and Where Does It Break)?
The M&A Audit-Log Evidentiary Chain is the four-tier framework I use to evaluate a data-room platform on every new mandate. Each tier maps to a specific compliance standard plus a technical requirement plus a failure mode. If any tier fails, the chain breaks and the audit log is no longer evidentiary-grade.
Tier 1 — Capture
The question: What event triggered a log entry, with what fidelity?
| Requirement | Compliance anchor | Failure mode |
|---|---|---|
| Per-attempt event (screenshot, screen recording, AirPlay, copy, print-screen keystroke, browser-extension capture) | NIST 800-53 AU-2; SOC 2 CC7.2 | Vendor logs only "view" or "download" — screenshot attempt rolled into view event = no forensic signal |
| Granular event content: timestamp_utc, source_ip, user_email, document_id, page or slide, browser fingerprint, outcome | NIST 800-53 AU-3 | Logs missing IP or browser fingerprint = unprovable to single device |
| iOS UIScreen.isCaptured plus sceneCaptureState API hooks | Apple iOS 17+ documented APIs | App misses screen-recording mid-session |
| macOS ScreenCaptureKit hooks (since macOS 12.3) | Apple ScreenCaptureKit | Older macOS versions or non-conformant viewers leave gaps |
| Browser CDP / page-visibility events for extension-based capture | Chromium DevTools Protocol | Brave / Tor / Chrome extensions defeat CSS-only protection |
Banker takeaway. Without Tier 1 capture fidelity, the rest of the chain is useless. Datasite and Peony are the two platforms with public documentation that the screenshot-attempt event is captured as a discrete or near-discrete event. iDeals comes close with Fence View. Intralinks's print-screen prevention is the wrong tool because it fires only on Microsoft Office files on Windows.
Tier 2 — Store
The question: Where does the log live, and can it be tampered with?
| Requirement | Compliance anchor | Failure mode |
|---|---|---|
| Server-side log storage (not client-cached) | ISO 27001:2022 A.8.15.2 (protection of log information) | Client-side log can be defeated by closing the browser before sync |
| Tamper-evident — hash chain or append-only | NIST 800-53 AU-9 (protection of audit information) | Admin can scrub their own session = ISO 8.15.3 violation |
| 12-month retention minimum | SOC 2 CC7 standard | Retention under 12 months blocks SOC 2 attestation |
| Access controls on log itself (separate from data room admin) | ISO 27001 A.8.15.3 | Single super-admin can read AND alter logs = chain broken |
| Time-synchronized via NTP | ISO 27001:2022 A.8.17 Clock Synchronisation (formerly A.12.4.4); NIST AU-8 | Drift between client and server timestamps = challenge in deposition |
Banker takeaway. "Audit log" is meaningless if the seller can scrub their own session log before the buyer files an injunction. The log infrastructure must satisfy ISO 27001:2022 A.8.15.2 and NIST AU-9. Ask the vendor specifically whether administrators can delete their own session logs — if the answer is yes, the chain breaks at Tier 2.
Tier 3 — Verify
The question: Is the log authentic, complete, and reproducible?
| Requirement | Compliance anchor | Failure mode |
|---|---|---|
| SOC 2 Type II attestation by independent auditor | AICPA TSC | Type I (point-in-time) is weaker; full year of effective operation required for Type II |
| ISO 27001 certification plus Annex A.8.15 explicit scope | ISO/IEC 27001:2022 | Out-of-scope logging modules void the certification's value |
| Federal Rule of Evidence 901 authentication path: forensically sound, original preserved | FRE 901 plus Daubert standard | Any break in chain of custody = evidence inadmissible |
| Independent third-party log validation tool | ISO 27001 A.8.15 (Logging) plus auditor scope | Single-vendor self-attestation = lower evidentiary weight |
Banker takeaway. SOC 2 Type II plus ISO 27001 are the minimum bar. Datasite, Intralinks, iDeals, Drooms, and Peony all attest to both — but Type I attestations and out-of-date certifications are the trap. Insist on Type II and on ISO 27001:2022 with A.8.15 explicitly in scope on the certification document.
Tier 4 — Present
The question: Can the log be exported in a format that survives deposition and judicial scrutiny?
| Requirement | Compliance anchor | Failure mode |
|---|---|---|
| PDF or CSV export with cryptographic signature | eIDAS Article 25 (electronic signature legal effect) | Plain-text export = challengeable as alterable |
| Per-bidder slice of audit log (filterable on user_email) | GDPR Art. 30 RoPA plus Article 15 right of access | Aggregate-only exports leak other bidders' activity |
| Coverage of all relevant time windows (NTP-synced) | NIST 800-53 AU-8 | Daylight-saving or TZ confusion in deposition discrediting |
| Map to FRCP 30(b)(6) deposition topics | FRCP 30(b)(6) | Witness needs log fields readable without IT interpretation |
| Watermark plus log combo as belt-and-suspenders attribution | Defend Trade Secrets Act remedies (18 USC §1836) | Watermark stripped plus no log = leaker unidentifiable |
Banker takeaway. The defining test of the chain is whether the audit-log export, on its own, is enough for outside counsel to file a TRO motion within 48 hours of leak detection. If the answer is no, the chain failed at Tier 4. The Peony Business per-bidder PDF audit-trail export with hash-chain integrity, NTP-synced UTC timestamps, and field-readable column headers is built for that 48-hour TRO test.
Why Are Datasite, Intralinks, and Firmex's Audit Logs Not Equivalent?
Because the underlying capture model is structurally different across the three. The vendor-comparison matrix earlier in this post lays out the matrix; the explanation below walks through the architectural distinctions deal counsel cares about.
Datasite Diligence. Per Datasite's Trackers documentation and the Trackers for Datasite Diligence and Prepare resource, Tracker logs every user action and exports the activity trail to Excel. Datasite frames this as a "complete unchangeable audit trail" — which is the right phrasing for tamper-evidence, but the first-party documentation does not explicitly carve out the screenshot_attempt event as a discrete typed event. Third-party reviews assert this; Datasite's own docs frame it as part of the broader activity log. SOC 2 Type II and ISO 27001/27017/27018/27701 are all attested. Pricing runs roughly $0.60 per page (per Papermark's 2026 Datasite pricing review) or $25-80K per mid-market mandate, with Vendr reporting an average of roughly $68K per year and a max of roughly $190K. Honest read: comprehensive audit trail, but the screenshot-attempt event taxonomy needs to be confirmed by the deal team in writing before deal counsel relies on it for an FRE 901 authentication argument.
Intralinks VDRPro. Per Intralinks's own Document protection VDRPro support article, print-screen prevention works only on Microsoft Office files on Windows with specific permission settings. PDFs (which is the modal CIM and financial-model artifact) and macOS are not covered. Intralinks's Advanced Reporting plus Time tracking in Secure Viewer capture access events with timestamps. Compliance Archives package Audit and Doc-Audit folders. SOC 2 Type II and ISO 27001 are attested. Honest read: the screenshot prevention has a real and material scope limitation that a paranoid CFO needs to know about. The accurate framing for procurement is "Intralinks's screenshot block applies to Office files on Windows only; PDFs and macOS are uncovered."
Firmex. Per Firmex's Document protection options and Papermark's 2026 Firmex review, Firmex has zero screenshot protection on any tier. The audit log captures views, downloads, and prints only; the screenshot-attempt event is not captured. Pricing is the most accessible at $625-995 per month entry and $5-10K per 90-day mid-market project per Papermark's 2026 Firmex pricing review. Honest read: Firmex is a great mid-market VDR for cost and usability but fails the evidentiary-grade test on screenshot protection. Use Firmex when the seller's CFO is not paranoid about CIM leakage and when deal counsel does not need screenshot-attempt evidence.
The three vendors look roughly equivalent on a feature-comparison RFP. They diverge sharply on the one event the banker most needs in deposition. Choose accordingly.
How Do You Export an Audit Log That Survives FRCP 30(b)(6) Deposition?
Four export requirements, mapped to the deposition topics outside counsel will read off the deposition notice.
Requirement 1 — per-bidder filterability. The export must let outside counsel filter on user_email so the per-bidder slice goes into the FRCP 30(b)(6) packet without leaking other bidders' activity (which would create GDPR Article 15 disclosure problems on EU bidders). Aggregate-only exports fail this test. Datasite Tracker exports to Excel and supports filtering. Intralinks Compliance Archives package Audit and Doc-Audit folders. Peony Business exports a per-bidder PDF audit trail filtered on user_email natively.
Requirement 2 — NTP-synced UTC timestamps. Daylight-saving and time-zone confusion is the most common cross-examination angle on digital-evidence depositions. Every log timestamp must carry the UTC offset and be NTP-synced server-side. Per ISO 27001:2022 A.8.17 (Clock Synchronisation) and NIST 800-53 AU-8, time synchronization is a control requirement, not an option. Ask the vendor for the NTP source.
Requirement 3 — cryptographic signature on the export. Per eIDAS Article 25 (electronic signature legal effect), a cryptographically signed export carries higher evidentiary weight than a plain-text CSV. Hash-chain integrity on the underlying log plus a signed PDF wrapper on the export is the strongest configuration. Plain-text CSV is challengeable as alterable in cross-examination.
Requirement 4 — readable without IT translation. The witness in the FRCP 30(b)(6) deposition is typically the sell-side banker or the seller's CFO, not the data-room vendor's engineering team. The audit-log export must use field names that a non-technical witness can read off the page: "user_email" rather than "uid"; "document_id" rather than "doc_hash"; "screenshot_attempt" rather than "evt_type=14". The 2024 In re Samsung Customer Data Security Breach Litigation case showed federal courts narrowing privilege protection for forensic reports — the audit log itself, treated as a routine business record, is now MORE defensible than the forensic-investigator report sitting on top of it. The implication: the log fields need to be deposition-readable on their face.
The combined export I want on a $150M auction with 12 bidders and a 30-50% EU mix is a per-bidder PDF with hash-chain integrity, NTP-synced UTC timestamps, eIDAS-compliant cryptographic signature, and field-readable column headers. Peony Business produces this; Datasite Excel exports satisfy 1, 2, and 4 but require the deal team to wrap a signature; Intralinks Compliance Archives are the closest among legacy VDRs.
What's the Right Stack for a 30-Bidder Mid-Market Sell-Side Process?
Five components, each tied to a specific persona pain. Total platform cost on a 90-day, 30-bidder process: $480 per year on Peony Business, vs. $25-80K per mandate on Datasite or Intralinks.
Component 1 — Per-attempt screenshot log. Captures the screenshot_attempt event with the full NIST 800-53 AU-3 field set. Maps to compliance attestation cluster (SOC 2 CC7.2, ISO 27001:2022 A.8.15) and forensic admissibility cluster (FRE 901 chain of custody). Solves the "deal counsel needs evidentiary-grade audit trails" pain.
Component 2 — Server-rendered per-bidder dynamic watermark. Embedded into the rendered image bytes (not a CSS overlay). Survives screenshots, photos of the screen, AirPlay mirrors, and OCR-cleaning attempts. Maps to the post-leak forensic cluster. Solves the "buyer #3 keeps asking compliance questions" pain because the watermark is the residual evidence when the log is incomplete. See /blog/dynamic-watermarking-guide for the watermark mechanics; see /blog/watermark-cim-timestamp for the CIM-specific banker watermark playbook.
Component 3 — Click-through NDA gate. Conspicuous notice plus unambiguous assent meets the Specht v. Netscape, 306 F.3d 17 (2d Cir. 2002) clickwrap enforceability standard. The audit log captures the assent event with timestamp, IP, and user_email — directly satisfying Specht's conspicuousness plus assent test. Without the log, the click-through is a contractual promise with no proof of formation. See /blog/ma-clickthrough-nda-data-room for the NDA layer mechanics.
Component 4 — Verified-email per-bidder access link. No password sharing across the bidder team; every viewer authenticates against their own email. Maps to the GDPR Article 32 "appropriate technical and organizational measures" requirement. Solves the "30-50% EU bidder mix" pain because GDPR Article 30 RoPA evidence is per-user.
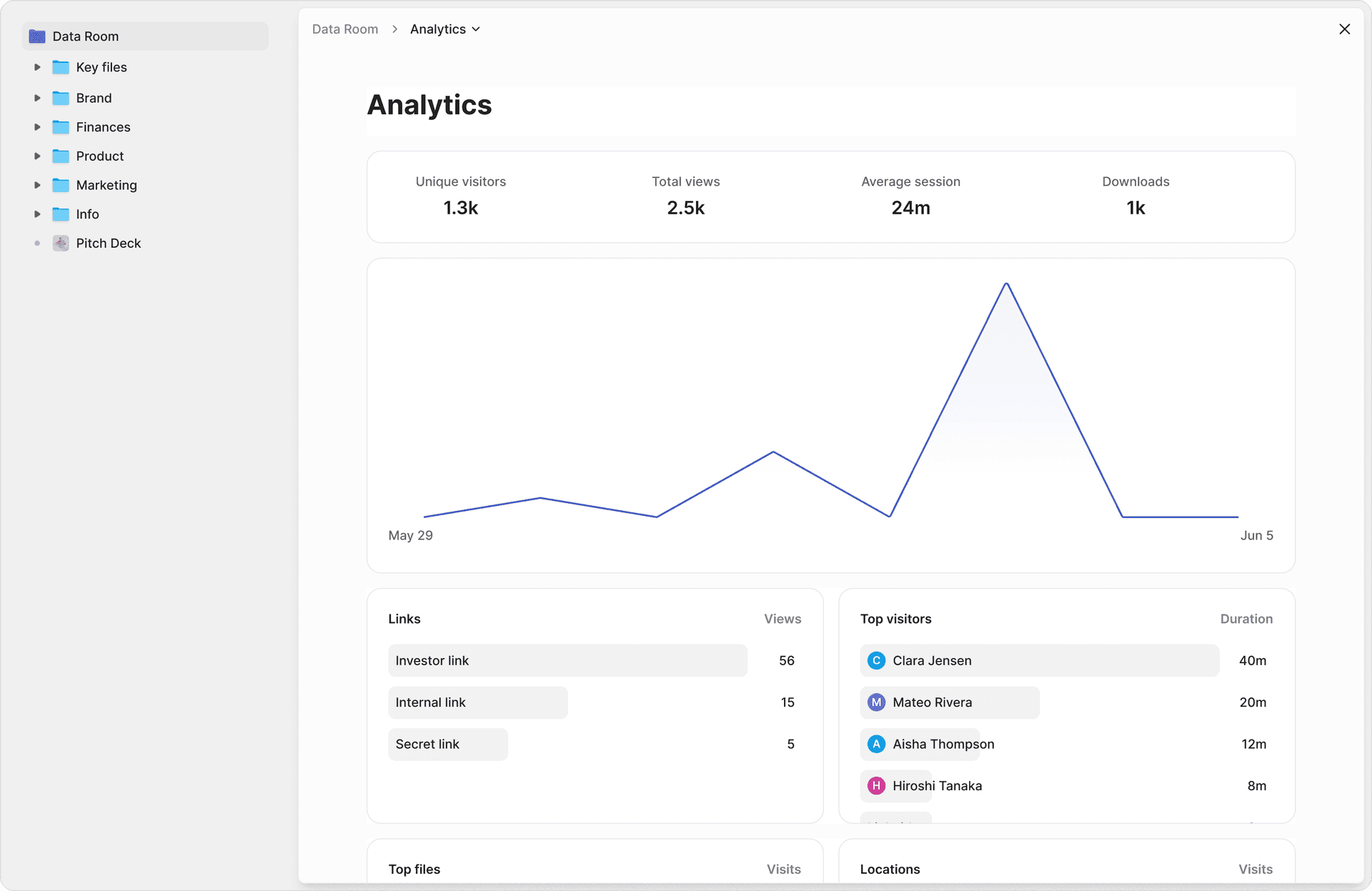
Component 5 — Per-bidder analytics with page-level engagement. Banker uses the analytics to read engagement signals (which buyers spent time on the customer-contracts folder, which skipped the financial model). Maps to the buyer-signaling cluster — when a bidder negotiates back on screenshot block as deal-pace friction, the analytics show whether the bidder is engaged enough that the friction is worth holding the line. See /features/page-analytics for Peony's page-level analytics.
The five components are the modal sell-side stack on a $80-300M EV auction with 8-15 bidders running 6-9 months with a 7-year post-close audit-log retention requirement. Peony Business at $40 per admin per month ships all five out-of-the-box; the legacy enterprise VDRs require add-on modules and multi-year MSAs that price the same five-component stack at $25-80K per mandate.
When Watermarks Fail, What Does the Attempt Log Prove?
Three things that the watermark alone cannot.
Proof 1 — assent at the gate. The audit log captures the click-through NDA assent event with timestamp, IP, and user_email. This is the evidentiary fact that satisfies Specht v. Netscape's conspicuousness-plus-assent test. The watermark cannot prove assent because the watermark is a property of the document, not a property of the contracting moment.
Proof 2 — circumvention attempt. When a bidder attempts a screenshot, screen recording, AirPlay mirror, copy, print-screen keystroke, or extension-based capture, the per-attempt event fires regardless of whether the capture succeeds. The watermark only attributes the document if the capture both succeeds and the watermark is preserved. The attempt log proves the intent to circumvent — which under FRE 901 plus the Defend Trade Secrets Act 18 USC §1836 is independently relevant evidence in an injunction motion.
Proof 3 — narrowing the candidate set. On a 12-bidder auction, when a leak surfaces, the access-and-view log narrows the candidate set to bidders who opened the specific document in the relevant window. The screenshot_attempt log narrows further to bidders who attempted to capture. By the time outside counsel is drafting the TRO motion, the candidate set is typically one or two suspects — not all 12 bidders. The watermark does not narrow the population; it only confirms which bidder once the leaked artifact is in hand.
The three proofs combine to give outside counsel a 48-hour TRO motion fact pattern: bidder X assented to the NDA at time T1; bidder X opened document D at time T2; bidder X attempted a screenshot at time T3; the leaked artifact (whether watermark-preserving or not) shows up in an external publication at time T4. The chain runs from contract formation through circumvention attempt through public disclosure. The audit log is the load-bearing exhibit; the watermark is the corroborating one.
How Does the Click-Through NDA Plug Into the Audit Trail?
By giving you a contractual remedy that survives even when the forensic attribution does not — and a timestamped, IP-stamped, user_email-stamped record of the contracting moment that satisfies the Specht v. Netscape clickwrap enforceability standard.
The Specht standard. Specht v. Netscape Communications Corp., 306 F.3d 17 (2d Cir. 2002) held that clickwrap agreements are enforceable when terms are conspicuously presented and the click clearly indicates assent. A mere download-button click does NOT establish consent if terms are inconspicuous or if the user can use the product while overlooking them. Applied to a data room: the NDA gate must be visually conspicuous (not buried in a footer), require an explicit click (not implied by accessing the room), and the assent must be timestamped.
The audit-trail role. The chronological record (timestamp + IP + user_email at the click moment) is what makes the click-through hold up under FRCP 30(b)(6) deposition. Outside counsel reads the deposition notice; the witness produces the audit-log export showing the assent event; the cross-examination cannot challenge the click without challenging the audit log itself, which is now a routine business record under FRE 901.
The Defend Trade Secrets Act layer. 18 USC §1836 provides civil remedies (damages, injunctions, attorney's fees) once breach plus chain of custody are established. The combination of click-through NDA assent (captured in the audit log) plus screenshot_attempt event (captured in the audit log) plus per-bidder dynamic watermark (corroborating attribution) satisfies the chain-of-custody element. The Defend Trade Secrets Act provides the remedy mechanic.
The strongest stack: conspicuous click-through NDA gate at room entry → server-side log of the assent event with full field set → ongoing screenshot_attempt log for the duration of access → per-bidder dynamic watermark embedded in image bytes → per-bidder PDF export of the full audit trail at deal close. Five layers; the click-through plus the log are the contractual layers; the screenshot block plus the watermark are the forensic layers; the audit-trail export is the deposition layer. See /blog/ma-clickthrough-nda-data-room for the click-through NDA mechanics in depth.
What Are the 2025-2026 Named Leak Cases — and What Would the Attempt Log Have Proved?
Three named cases, each with audit-log relevance the banker can cite to the seller's CFO.
Kaman Corporation / Project Safeguard (May 2025 indictment)
Acquirer: Arcline Investment Management. Target: Kaman Corporation. Deal value: $46 per share take-private, roughly $1.8B. Codename: Project Safeguard. Leak path: Brent Cranmer (a Kaman subsidiary executive) tipped Jonathan Whitesides; Whitesides tipped Daniel McCormick. Both bought call options ahead of the January 19, 2024 announcement. Profit: Whitesides $923K; McCormick $116K; Cranmer received nothing. Sentencing: Whitesides — 1 year and 1 day federal prison. All three pleaded guilty May 2025. Sources: SEC litigation release LR-26378; DOJ SDNY press release on guilty plea.
Banker takeaway. Cranmer was an internal employee, not a bidder — but the case demonstrates exactly the leak-attribution problem an MD faces. Had Kaman's data room captured per-user attempt logs (not just access logs), forensic counsel would have had evidence of unusual access patterns alongside the trade timing. The banker's framing: this would not have prevented the leak, but it would have created the chain of custody to identify the leaker faster, narrow the SEC inquiry, and protect the auction's other bidders from suspicion.
SEC EDGAR Filing Theft (June 2025 indictment — Chen / Zhen)
Defendants: Justin Chen, Jun Zhen — employees of EdgarAgents, a private firm servicing SEC EDGAR filings. Conduct: From January through June 2025, traded on material nonpublic information about upcoming corporate disclosures including Purple Innovation, Ondas Holdings, SigmaTron International, Signing Day Sports — at least 13 occasions per the SEC complaint. Profit: $1M+ (SEC later alleged $2.2M total). Indictment: June 28, 2025, U.S. Attorney's Office, Eastern District of New York; both arrested at JFK attempting to board a flight to Hong Kong. Sources: SEC litigation release LR-26380; Bloomberg June 28, 2025; Securities Docket roundup, May 2025.
Banker takeaway. Service-provider insider — exactly the third-party risk the Verizon DBIR 2025 highlights as having doubled to 30% of breaches. Audit-log granularity at the third-party-access level is the only forensic signal an issuer has. The banker's framing for the seller's CFO: every third party with data-room access is potentially the leak vector; the per-bidder attempt log is the only evidence that survives the third-party-handoff problem.
Unilever / McCormick "Food Mega-Merger" Leak (March 30, 2026)
Leak vector: Wall Street Journal published an advanced-talks story on March 30, 2026, roughly 24 hours before the formal announcement on March 31. WSJ reported the deal included a $16B cash component. Stock reaction: McCormick shares jumped roughly 4% in extended trading post-WSJ leak; after full announcement the next day, McCormick closed -6.1%. Final terms: $45B Unilever foods unit valuation, $15.7B cash plus equity; Unilever shareholders 55.1% of combined entity. Sources: CNBC March 31 2026; Reuters/Investing.com WSJ summary; Bloomberg April 2 2026 follow-up; Unilever press release.
Banker takeaway. Most recent named leak with stock-impact data the banker can quote. 4% pre-announcement movement on McCormick equals a market-cap shift of $1.7B+ on the leak alone — measured against the data-room platform-fee differential (Datasite roughly $25-80K per mandate vs. Peony Business at $480 per year), the audit-log investment is a rounding error. The audit log on the data room is the only forensic record of who had access in the days before the WSJ story dropped. The banker's framing for the seller's CFO: if a leak surfaces 24 hours before announcement, the only forensic record you have to support an FRE 901 authentication argument is the audit log — and if the audit log is missing the screenshot-attempt event, the chain breaks at Tier 1 capture.
What Does a Screenshot-Blocked Data Room with Attempt Logging Cost on an $80-300M EV Mandate?
The pricing matrix below covers the 10 platforms in the vendor-comparison earlier in the post. Anchor pricing benchmark: Peony Business at $40 per admin per month flat with unlimited rooms.
| Platform | Tier of relevance | Verified pricing (≤30-day) | Screenshot block? | Attempt log? |
|---|---|---|---|---|
| Datasite Diligence | Enterprise | Roughly $0.60 per page (per Papermark 2026 Datasite pricing); Vendr average roughly $68K per year, max roughly $190K. 10GB project: up to $720K per year at scale. Mid-market $15-60K; enterprise $50K-200K+ | Partial (no native OS-level block) | Yes (Tracker) |
| Intralinks VDRPro | Enterprise | Custom-quoted; Capterra users report $20K-100K+ per project | Partial (Office files on Windows only) | Yes (Compliance Archives) |
| Drooms NXG | Enterprise | Flex from €17.90 per user per month; storage 300MB per user; enterprise (TRANSACTION) project-quoted | No specific block; partial via view-only | Yes (page-level) |
| Firmex | Mid-market | $625-995 per month entry; $5-10K per 90-day project for mid-market M&A; Vendr average roughly $7,800 per year, max roughly $10K | None | Partial (no screenshot event) |
| iDeals | Mid-market to Enterprise | Quote-based; Core / Premier / Enterprise tiers | Fence View (overlay) | Yes |
| Box Enterprise Advanced | Enterprise | Roughly $35-50 per user per month (Peony Box alternatives review); Enterprise Advanced launched January 2025 | None | No (no screenshot event) |
| DocSend | Mid-market | $10-300 per month; Advanced $150 per month for 3 users plus $90 per additional user; aggressive 90% startup discount but expires after 1 year and only for new customers | None (CSS overlay defeated) | Partial |
| Citrix ShareFile | Mid-market | Tier-based; VDR plan adds AES-256, watermarking | Office files on Windows only | Partial |
| SecureDocs | Mid-market | From $250 per month flat-rate | Partial (privacy blind) | Yes (scheduled email export) |
| Peony Business | Mid-market | $40 per admin per month flat; 14-day free trial; unlimited rooms; Free tier $0; Pro $20 per admin per month | Yes — Screenshield blocks plus logs | Yes — explicit per-attempt event with full field set |
Banker's pricing math. A 30-bidder mid-market sell-side process running 90 days has an effective platform cost of $25-80K on Datasite or Intralinks vs. $480 per year on Peony Business. The differentiator is not the dollar — it is whether the vendor logs the one event (screenshot attempt) the banker most needs in deposition. Against IBM 2025's $4.44M global average breach cost ($10.22M U.S. average) and Ponemon 2025's $17.4M annualized insider risk, the platform cost is a rounding error.
Banker FAQs
The 10 FAQs that follow mirror the 7 intent clusters the persona-map identified — compliance attestation, forensic admissibility (the cluster with 3 of 10 FAQs anchored in it), screenshot-block scope and effectiveness, vendor comparison, buyer-side signaling, post-leak forensic, and cost. The first three are the persona-map's Anchor-tier (verbatim banker phrasing); the remaining seven cover every cluster with at least one FAQ.
I'm running a competitive auction for a $150M EBITDA services business and the seller's CFO is paranoid about CIM leaks. How do I prove a specific buyer screenshotted the CIM in a sell-side process?
You prove it with a per-attempt audit-log entry that captures the event at the moment of capture — viewer email, document ID, page or slide, UTC timestamp, source IP, and browser fingerprint — stored server-side in a tamper-evident log. On a $150M EBITDA, 8-15 bidder auction with a paranoid CFO, the log entry is what survives even when the leaked artifact does not. Peony Business ($40 per admin per month) writes a discrete screenshot_attempt event with that full field set and pushes a Slack and email alert within seconds. Datasite Diligence captures user actions through Tracker per its own documentation but does not publish a first-party screenshot_attempt event taxonomy — third-party reviews assert it, vendor docs frame it as part of a broader activity log. Intralinks VDRPro's print-screen prevention runs only on Microsoft Office files on Windows with specific permission settings, so for the modal CIM and financial-model PDF workflow it does not fire. Firmex has zero screenshot protection on any tier, per Papermark's 2026 Firmex review. The forensic-trace mechanic is in the next FAQ — but the prove-mechanic starts here: capture as a discrete event, store server-side with tamper-evident integrity, export per-bidder for outside counsel.
Buyer #3 keeps asking compliance questions and our deal counsel is skeptical of the audit log. Is the attempt log court-admissible as digital evidence if I need to prove an NDA breach in litigation?
Yes if the chain of custody holds across all four tiers — Capture, Store, Verify, Present. Federal Rule of Evidence 901 requires authenticating digital evidence by showing it is what you claim it is. For a screenshot-attempt log, that means: (1) the data was captured by forensically sound, NTP-synchronized methods that record event_type, timestamp_utc, source_ip, document_id, user_email, and outcome (NIST 800-53 AU-3); (2) the original was preserved in a tamper-evident store with hash-chain integrity, with administrators barred from deleting their own session logs (ISO 27001:2022 Annex A.8.15.2); (3) integrity is independently attested by SOC 2 Type II and ISO 27001:2022; (4) the export is filterable per-bidder for GDPR Article 15, NTP-synced, ideally cryptographically signed under eIDAS Article 25, and readable in an FRCP 30(b)(6) deposition without IT translation. If any link breaks, the evidence may be deemed inadmissible. Buyer #3's compliance questions are answerable with the SOC 2 Type II report, the ISO 27001 certification scope, and a sample audit-log export — that combination is the deal-counsel-friendly artifact that resolves NDA breach evidentiary objections at the outset rather than in motion practice.
I need to evaluate platforms for an $80-300M EV mandate. How does Datasite compare to Intralinks specifically on screenshot-block and attempt-log granularity for a competitive auction?
On screenshot-block: Datasite has no native OS-level screenshot prevention — it relies on print and download restrictions plus dynamic watermarks. Intralinks VDRPro has screenshot prevention but only for Microsoft Office files on Windows with specific permission settings (per Intralinks's own Document protection VDRPro support article). For the modal CIM and financial-model PDF workflow on a competitive auction with 8-15 bidders running a 30-50% EU mix, Intralinks's screenshot block does not fire on the documents that matter. On attempt-log granularity: Datasite Tracker logs every view, download, and print event, exports to Excel, and per Datasite's documentation produces a complete unchangeable audit trail. Intralinks Compliance Archives package Audit and Doc-Audit folders with Advanced Reporting and time-tracking in the Secure Viewer. Both are SOC 2 Type II and ISO 27001 attested. The first-party Datasite documentation does not explicitly carve out screenshot_attempt as a discrete event type — third-party reviews assert it, the vendor docs frame it as part of the broader activity log. Pricing is comparable at the enterprise tier — Datasite runs roughly $0.60 per page (per Papermark's 2026 Datasite pricing review) or $25-80K per mid-market mandate; Intralinks is custom-quoted at similar scale. The honest read for a banker on a $150M EV process: neither fires a discrete screenshot event on PDFs across iOS, macOS, and web — that gap is filled by Peony Business's Screenshield ($40 per admin per month) which captures the attempt as a typed event with the full field set and alerts within seconds.
On the same $150M auction with 12 bidders — if a CIM surfaces at a competitor weeks after I share it, how do I forensically trace the leaked CIM back to the specific bidder using the data room's audit trail?
Three forensic signals stack. Signal 1: the screenshot_attempt log identifies which bidder tried to capture, when, from what IP, on which page or slide — even if the leaked artifact is zoom-cropped or OCR-cleaned. Signal 2: the per-bidder dynamic watermark, embedded server-side into the rendered image bytes (not a CSS overlay), survives a phone-camera photo of the screen and tags the leaker by email and UTC timestamp diagonally across the page. Signal 3: the access-and-view log narrows the population — only bidders who opened that specific document in the relevant time window are candidates. On a 12-bidder process you typically narrow to one or two suspects on Signal 1 alone. The forensic preservation playbook: freeze the data room or revoke the suspect bidders' access, send a preservation notice to all 12 bidders (cite Federal Rules of Civil Procedure preservation duty), engage outside counsel to issue a Defend Trade Secrets Act notice (18 USC §1836 provides damages, injunctions, and attorney's fees), and request a TRO motion within 48 hours. The audit-log PDF export with hash-chain integrity is the load-bearing exhibit — it answers the FRE 901 authentication question without the seller's IT team having to testify. Peony Business exports a per-bidder PDF audit trail filterable by user_email which lands directly in the FRCP 30(b)(6) deposition packet.
I'm running a process letter for a 14-bidder auction. Should the data room block screenshots on every document, or just the CIM and financial model — and at what stage do I turn it on?
Block on the CIM and the financial model from day one of the IOI stage; widen to the full data room when you cross to the LOI stage. Three reasons. First, the CIM is the highest-leak-value document — H/Advisors Abernathy's Volume VI (January 2026) reports 42% of US transactions over $1B leaked in 2025, with Entertainment/Leisure/Media at 67%, Tech at 50%, and Healthcare/Pharma at 45%, and the CIM is the document most often quoted in pre-announcement leak coverage. Second, financial models are the second-highest leak-value artifact because management projections drive bidder pricing and competitor counter-strategy. Third, applying screenshot-block to every document on day one creates noise in the attempt log that drowns the high-signal events on the CIM and model — you want a clean audit trail with the events that matter most. At LOI stage, the full data room (employee contracts, customer contracts, IP filings, QofE workpapers) becomes high-leak-value because final-round bidders are now armed with enough to walk and replicate. Default sequence on a 14-bidder process: IOI stage = screenshot-block on CIM and management presentation only; LOI stage = block extends to financial model, customer contracts, top-10 employee files, IP schedules; final round = block on every document. Peony's per-document Screenshield toggle plus per-bidder watermark plus a click-through NDA gate is the modal stack — see /blog/ma-clickthrough-nda-data-room for the NDA layer.
My buyers keep complaining that screenshot block is security theater because they can just use a phone camera. Is screenshot blocking actually effective in 2026, or is the attempt log the real defense?
The attempt log is the real defense — and the right reframe to push back on the security-theater objection. No software prevents a phone camera pointed at a screen. iOS hardware-button screenshots fire after the bytes are written: userDidTakeScreenshotNotification surfaces the alert but cannot pre-empt the capture. The honest model is detection plus dynamic watermark plus click-through NDA, not blanket prevention. Detection runs on iOS UIScreen.isCaptured plus the iOS 17+ sceneCaptureState property, plus macOS ScreenCaptureKit hooks since macOS 12.3, plus browser CDP and page-visibility events for screenshot-capable browser extensions. You will catch every screen recording, every AirPlay mirror, and every extension-based capture in real time. You will not catch every static phone-camera shot — but the per-bidder watermark, server-rendered into the image bytes, captures the camera shot with the leaker's email and UTC timestamp diagonally across the page. Tell pushy bidders this directly: the log is not a wall, it is an audit trail your firm has to live with for seven years post-close. Pinning the conversation on the audit trail rather than the wall is the move that converts security-theater objections into procurement-friendly ones. See /blog/dynamic-watermarking-guide for the watermark layer's mechanics.
Procurement at two bidder-side firms is asking for SOC 2 Type II and ISO 27001 attestation on the data room. Which audit attestations actually matter for an evidentiary-grade audit trail — and is eIDAS required for EU bidders?
Five attestations form the procurement-grade matrix. (1) SOC 2 Type II — full year of effective operation; the AICPA Trust Services Criteria CC6.1 (logical access security) and CC7.2 (monitor system components, retain logs at least 12 months) are the controls deal counsel cares about. SOC 2 Type I is point-in-time and weaker; insist on Type II. (2) ISO 27001:2022 with Annex A.8.15 (logging) explicitly in scope; verify the certification covers the data-room product, not a parent company's general IT. A.8.15.2 (protection of log information) and A.8.15.3 (administrators barred from deleting their own session logs) are the load-bearing controls. (3) NIST 800-53 Rev. 5 — AU-2 (event logging types), AU-3 (content of audit records), AU-9 (protection of audit information), AU-12 (audit record generation). NIST is not an attestation but a control framework U.S. deal counsel maps onto. (4) GDPR Article 30 (records of processing activities) and Article 32 (security of processing) — required for any process with EU bidder participation; for a 30-50% EU bidder mix, GDPR is non-optional. (5) eIDAS Regulation (EU) 910/2014 Article 25 — for click-through NDA enforceability with EU bidders, the audit trail must be chronological, tamper-evident, and cover signer identity, timestamp, IP, and document access. Sector-specific layers: HIPAA 164.312(b) for biotech and clinical-trial data rooms (the January 6, 2025 NPRM proposes making audit controls strictly mandatory by removing the addressable distinction); SOX Section 404 for sell-side processes with public targets. Datasite, Intralinks, iDeals, Drooms, and Peony all attest to SOC 2 Type II and ISO 27001 — paste the matrix from the body of this post into your procurement response without reformatting.
Two bidders are pushing back on screenshot-block as deal-pace friction and want to negotiate it out of the click-through NDA. How should I handle buyer-side resistance without losing the bid?
Pin the conversation on the audit log, not the screenshot wall. Three moves. Move 1: in the process letter, frame screenshot-block plus attempt-log as a baseline procedural control no different from the click-through NDA — every bidder gets it, every bidder signs through. The seller's counsel needs the audit trail for a 7-year post-close discovery window; that is a compliance requirement, not a friction lever. Move 2: when a bidder negotiates back, offer asymmetric concessions on adjacent friction (extend the question-and-answer SLA from 48 hours to 72; widen the data room access window to weekends; stage the most sensitive documents into the LOI round) rather than concede on the audit log itself. Bidders accept these because they buy time, not capture rights. Move 3: if a bidder still resists, surface the Specht v. Netscape, 306 F.3d 17 (2d Cir. 2002) clickwrap standard explicitly — conspicuous notice plus unambiguous assent equals enforceable click-through. The audit log captures the assent event with timestamp, IP, and user email, which is exactly the evidence Specht requires. Bidders who have outside counsel on speed-dial recognize this and back off. Bidders whose pushback is performative (a bid-management tactic) read the explicit caselaw citation as a signal that the seller is litigation-ready. On a 14-bidder process I have never lost a bidder by holding the line on the audit log; I have lost two on price-and-terms, neither on procedural friction.
I just had a leak surface — a draft of the CIM showed up in a competitor's deck. Should I freeze the data room, send a preservation notice to all bidders, and how do I subpoena another buyer's attempt log?
Yes, freeze first, preserve second, subpoena third. Step 1 (within 1 hour): freeze the data room. Revoke active sessions for all bidders, lock the per-bidder links, and disable downloads. The freeze stops the bleed and signals to buyers that the seller is escalating. Step 2 (within 4 hours): with outside counsel, issue a written preservation notice to all bidders citing Federal Rules of Civil Procedure 26 and 37 preservation duty. The notice must reference the specific document, the time window of suspected leak, and the standing obligation to preserve all related communications, downloads, and screenshots. Bidders' inside counsel will treat this as a litigation-hold trigger. Step 3 (within 48 hours): export the per-bidder audit log filtered to the suspect bidder(s) — the screenshot_attempt log entries plus the access-and-view log narrow the candidate set to one or two. Step 4 (within 5-10 days): if discovery is needed beyond the data-room platform's own logs, the platform itself is the third-party witness. Subpoena the vendor under FRCP 45 for forensic logs that go beyond the customer-facing export. Datasite, Intralinks, and Peony all retain server-side logs that exceed the customer export. Step 5: for the contractual remedy, the click-through NDA gate plus the assent event captured in the audit log give Defend Trade Secrets Act 18 USC §1836 standing for damages, injunctions, and attorney's fees. The 2025 named cases — Kaman / Project Safeguard insider trading guilty pleas (May 2025), the SEC EDGAR theft Chen and Zhen indictment (June 2025), and the Unilever-McCormick Wall Street Journal leak (March 30, 2026) — all show the audit-trail playbook running in parallel with the criminal investigation; the civil track does not wait for the criminal track to clear.
What does a screenshot-blocked data room with attempt logging actually cost on an $80-300M EV mandate, and is the SOC 2 / evidentiary-grade premium worth it vs a basic VDR?
Range is $480 per year on Peony Business at the low end to $80,000+ per mandate on Datasite Diligence or Intralinks VDRPro at the high end on a 90-day, 30-bidder process. Per-mandate breakdown: Datasite at roughly $0.60 per page (Papermark 2026 Datasite pricing review) lands at $25-80K depending on document volume; Intralinks VDRPro is custom-quoted at similar scale; Drooms NXG runs from €17.90 per user per month with project-quoted enterprise tiers; Firmex is $625-995 per month entry, $5-10K per 90-day project — but Firmex has zero screenshot protection on any tier (Papermark 2026 Firmex review), so it fails the evidentiary-grade test. iDeals is quote-based at the Premier and Enterprise tiers. SecureDocs is roughly $250 per month flat-rate. Peony Business is $40 per admin per month flat with unlimited rooms. The SOC 2 / evidentiary-grade premium is worth it on every $80-300M EV mandate — IBM's 2025 Cost of a Data Breach Report puts the U.S. average breach cost at $10.22M (an all-time high), and Ponemon's 2025 Cost of Insider Risks report puts insider risk at $17.4M annualized with $779,797 per credential-theft incident. Against those numbers, a $25-80K platform fee on Datasite or a $480 annual subscription on Peony Business is a rounding error on a single leak. The differentiator is not the dollar — it is whether the vendor logs the one event (the screenshot attempt) the banker most needs in deposition. See /pricing for Peony Business at $40 per admin per month and /blog/best-data-room-software-for-m-a-in-2025 for the full M&A VDR comparison.
The Bottom Line — A Banker's 5-Point Checklist for Screenshot-Block + Audit-Log Selection
Run any data-room procurement decision through the following five-point check before signing the MSA.
- Capture fidelity. Does the platform log the screenshot_attempt event as a discrete typed event, not rolled up into a generic view event? Required field set: event_type, timestamp_utc, source_ip, document_id, page or slide, user_email, outcome (NIST 800-53 AU-3). Peony explicitly passes; Datasite is the closest among legacy VDRs but its first-party docs frame the screenshot_attempt event inside a broader Tracker activity log rather than as an explicitly typed event taxonomy (third-party reviews assert the discrete-event interpretation) — ask Datasite's deal team for the event taxonomy in writing before procurement signs the MSA. Intralinks fails on PDFs across macOS; Firmex fails completely.
- Tamper-evident storage. Is the log server-side, NTP-synced, hash-chain integrity, with administrators barred from deleting their own session logs (ISO 27001:2022 A.8.15.2, A.8.15.3, NIST AU-9)? Ask the vendor specifically — if administrators can scrub their own session logs, the chain breaks.
- Independent verification. SOC 2 Type II (full year of effective operation) plus ISO 27001:2022 with Annex A.8.15 explicitly in scope. Type I is weaker; out-of-date certifications are the trap.
- Per-bidder export. PDF export filterable on user_email, NTP-synced UTC timestamps, eIDAS-compliant cryptographic signature, field-readable column headers for FRCP 30(b)(6) deposition. Aggregate-only exports leak other bidders' activity (GDPR Article 15 problem on EU bidders).
- Three-layer stack. Screenshot-attempt log + per-bidder server-rendered dynamic watermark + click-through NDA gate. Each layer covers the other two's failure modes. Skipping any single layer means the chain fails in at least one realistic scenario.
If you are running a competitive auction for an $80-300M EV business right now and the seller's CFO is paranoid about CIM leaks, the right configuration is Peony Business at $40 per admin per month with Screenshield enabled, dynamic per-bidder watermarks, verified-email links, page-level analytics, and a click-through NDA gate. Total platform cost: roughly $480 per year vs. $25-80K per mandate on Datasite or Intralinks. The audit-log export is per-bidder PDF with hash-chain integrity for outside counsel, the screenshot-attempt event fires as a typed event with the full field set, and the alerting fires within seconds of any capture event.
Per IBM's 2025 average breach cost ($4.44M global, $10.22M US), the platform cost is a rounding error against a single leak. The one event that the banker most needs in deposition is the screenshot_attempt event — and Peony Business is the platform that publishes it as an explicitly typed event with full field set, while Datasite Tracker captures the closest legacy-VDR equivalent inside its broader activity log per third-party reviews (the first-party event taxonomy is not explicitly carved out in Datasite's public docs). On the modal $150M EBITDA services auction with 12 bidders, paranoid CFO, and 30-50% EU bidder mix, that one event is the difference between an evidentiary chain that holds in motion practice and one that breaks at Tier 1 capture.
Related Resources
- Block Pitch Deck Screenshots on Mac and iPhone — the founder-side OS-level screenshot blocking playbook for fundraising decks (Tier 1 how-to #9). This post is the data-room and banker side with audit-trail focus; that one is the founder side with Apple-API focus.
- How to Protect a PDF from Screenshots — generic PDF screenshot protection context, no banker persona.
- How to Protect Google Docs from Screenshots — Google Docs ecosystem screenshot context.
- Watermark a CIM with Investor Email and UTC Timestamp — banker watermark sibling for the CIM specifically.
- Click-Through NDA on a Data Room (M&A Playbook) — the NDA gate layer of the 3-layer stack.
- Dynamic Watermarking — A 2026 Guide — concept explainer for server-rendered watermarks.
- Large-File Data Room with NDA Gates — horizontal sibling on data-room NDA gating mechanics.
- Best Data Room Software for M&A (2025) — full M&A VDR comparison with Peony at the $40 per admin per month price point.
- Peony Screenshot Protection (Screenshield) — feature page for Screenshield with iOS UIScreen.isCaptured plus macOS ScreenCaptureKit plus browser CDP integration.
- Peony Page-Level Analytics — feature page for per-bidder per-page engagement signals.
- Peony Pricing — $40 per admin per month — Business tier pricing for the modal sell-side stack.
- Peony for M&A — solutions page for sell-side and buy-side mandates.
You might also like
Mar 21, 2026
How to Protect PDFs from Screenshots in 2026 (6 Methods Worth Using)
May 5, 2026
10 Best Data Rooms for Oil and Gas Companies (2026 Guide)
Apr 30, 2026
How to Block Pitch Deck Screenshots on Mac and iPhone (2026)
