How to Protect PDFs from Screenshots in 2026 (6 Methods Worth Using)

Co-founder at Peony — I built the data room platform, with a background in document security, file systems, and AI.
Connect with me on LinkedIn! I want to help you :)Last updated: March 2026
You have a PDF that matters — investor financials, M&A due diligence documents, enterprise pricing, a board pack — and you need to share it externally. The moment you hit send, one thought keeps nagging: what stops someone from just screenshotting the whole thing?
I run Peony, a data room platform, and this is the single most common security question our users ask. The honest answer is that no tool can make screenshots mathematically impossible — a determined person with a camera phone will always find a way. But here is what I have learned after two years of building screenshot protection into our product: you can make casual screenshots nearly impossible and deliberate ones personally risky and traceable. That changes behavior far more than any promise of absolute prevention.
Verdict: The best method to protect PDFs from screenshots is a layered approach: screenshot protection that blacks out content during capture + dynamic watermarks that embed the viewer's identity + identity-bound access controls + analytics. Peony (free, $0) provides all four layers in one platform — no app installation required for recipients. With the Verizon DBIR reporting that 60-68% of breaches involve a human element and screenshots being one of the easiest exfiltration paths, the ROI on proper PDF protection is clear.
Peony is an AI-powered data room that gives you what basic PDF tools architecturally cannot: screenshot protection that interferes with OS-level capture, dynamic watermarks with viewer identity on every page, per-page view analytics, password-gated links, and instant access revocation. We built it because we got burned sharing a fundraising deck through Google Drive — an investor forwarded it to people we had never met, and we only found out when a stranger quoted our revenue numbers back to us.
Quick guide — match the method to the threat:
- Need the strongest screenshot protection available? Upload to Peony with screenshot blocking + watermarks + identity-bound access — Method 1
- Want dynamic watermarks that make leaks traceable? Peony or standalone watermarking — Method 2
- Sharing externally and need view-only controls? Disable downloads and force viewer-only access — Method 3
- Enterprise with managed devices? DRM software or endpoint DLP — Method 4
- Internal users on virtualized desktops? Screen capture protection in VDI — Method 5
- Minimum viable protection on a budget? Static watermarks + access policy — Method 6
Why PDFs leak through screenshots (and why disabling downloads is not enough)
Most PDF leaks are not sophisticated encryption attacks. They are mundane, human-level failures that the CISA insider threat guide catalogs in painful detail:
-
The screenshot-and-forward pattern. You share a PDF with restricted access. The recipient opens it, takes screenshots of the sensitive pages, and drops those images into Slack, WhatsApp, or their personal notes. Your access controls are now irrelevant — the content exists as uncontrolled image files.
-
The "we disabled downloads" false confidence. Many teams rely on disabling download, print, and copy in their cloud viewer. This removes one exfiltration path. But screenshots remain the path of least resistance. I tested this myself — it took about 30 seconds to capture a "download-disabled" document using nothing but the built-in OS screenshot tool. That is friction, not security. For broader protection strategies, see our secure file sharing guide.
-
The endpoint capture explosion. Modern devices have rich built-in capture features: OS-level screen recorders, clipboard managers, third-party grabbers. Data loss prevention best-practice guides explicitly flag screenshot monitoring as a critical gap in most organizations' document security posture.
-
The anonymous link problem. "Anyone with the link" sharing completely breaks accountability. If you do not know who is viewing your PDF, you cannot trace a leak, attribute a screenshot, or revoke access. It is the digital equivalent of leaving copies on a park bench.
The pattern that actually works in 2026 is not "prevent every pixel from being captured." It is friction + visibility + consequences: make screenshots hard, make them traceable, and make the viewer know they are traceable.
6 methods to protect PDFs from screenshots
Method 1: Use Peony's screenshot protection (recommended)
This is the method I recommend because it addresses all four layers — blocking, deterrence, attribution, and analytics — in one platform with no software installation for recipients.
How to do it:
-
Upload your PDF to a Peony data room. Create a room for the context — "Series B - Financials," "Client X - Contract Pack," "Board - Q1 2026." Upload the PDF there instead of emailing it as an attachment.
-
Enable screenshot protection. In the room security settings, turn on screenshot protection. Peony's viewer integrates with browser and OS-level capture APIs — when a standard screenshot or screen recording is detected, the document content is blacked out in the capture.
-
Add dynamic watermarks. Enable watermarking so every page displays the viewer's name, email, and timestamp. If someone bypasses screenshot protection with a camera phone, their identity is literally embedded in every image they capture.
-
Restrict access to verified identities. Grant access to specific email addresses or trusted domains (e.g.,
@fund.com,@client.co). No anonymous "anyone with the link" viewing for sensitive material. -
Disable downloads. Set the room to view-only so content can only be seen through Peony's protected viewer — not downloaded as a raw PDF where all your protections vanish.
-
Share one secure link, not the file. Send a Peony link instead of an attachment. If you update the PDF later, replace the file behind the same link. If a relationship ends, revoke access instantly.
Peony's data room gives you a controlled viewing environment for your PDFs — organized folders, branded presentation, and security settings that travel with every document.
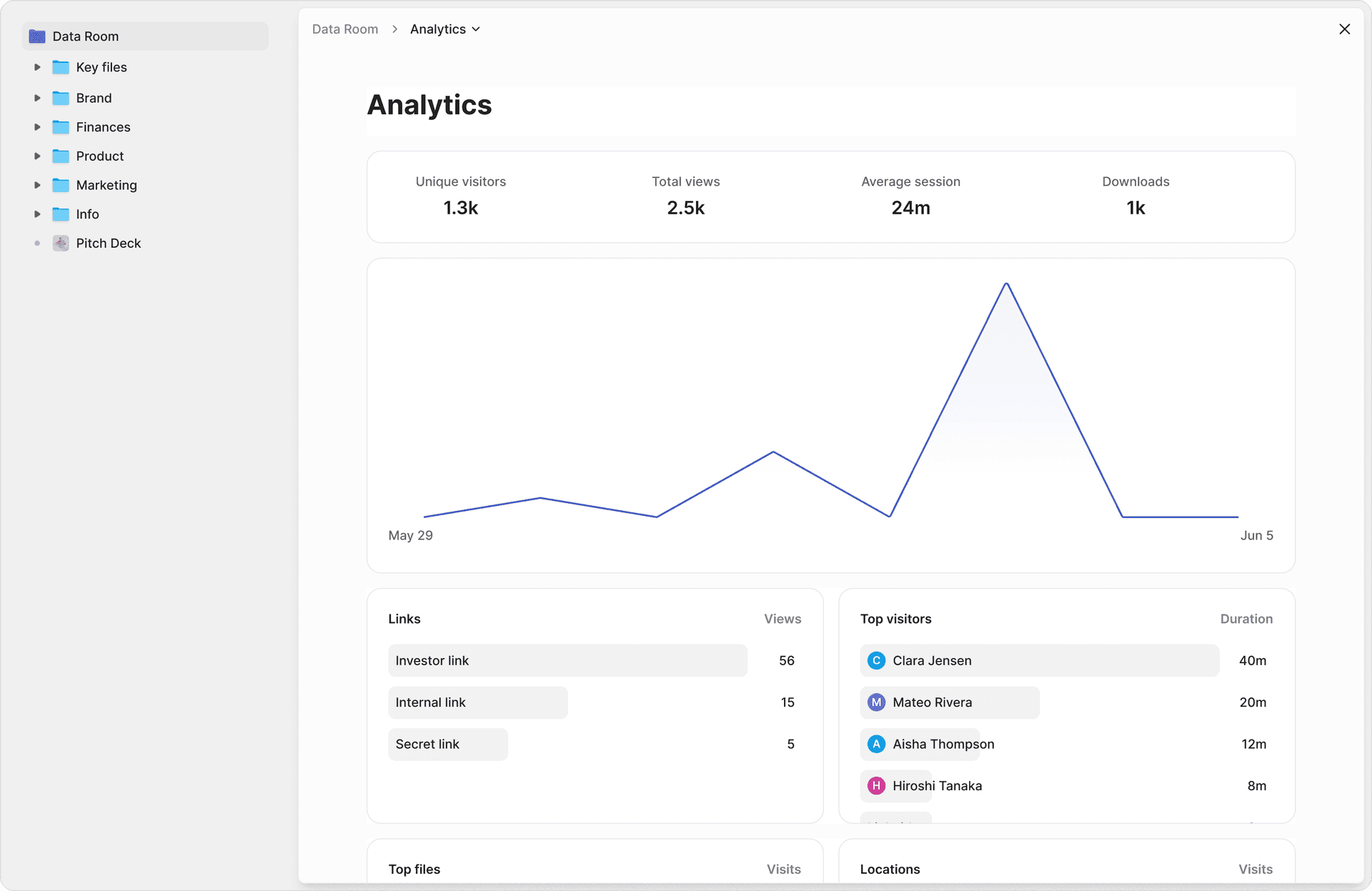
The analytics dashboard shows exactly who viewed your PDF, when, which pages they spent time on, and how long each session lasted — visibility that basic PDF sharing cannot provide.
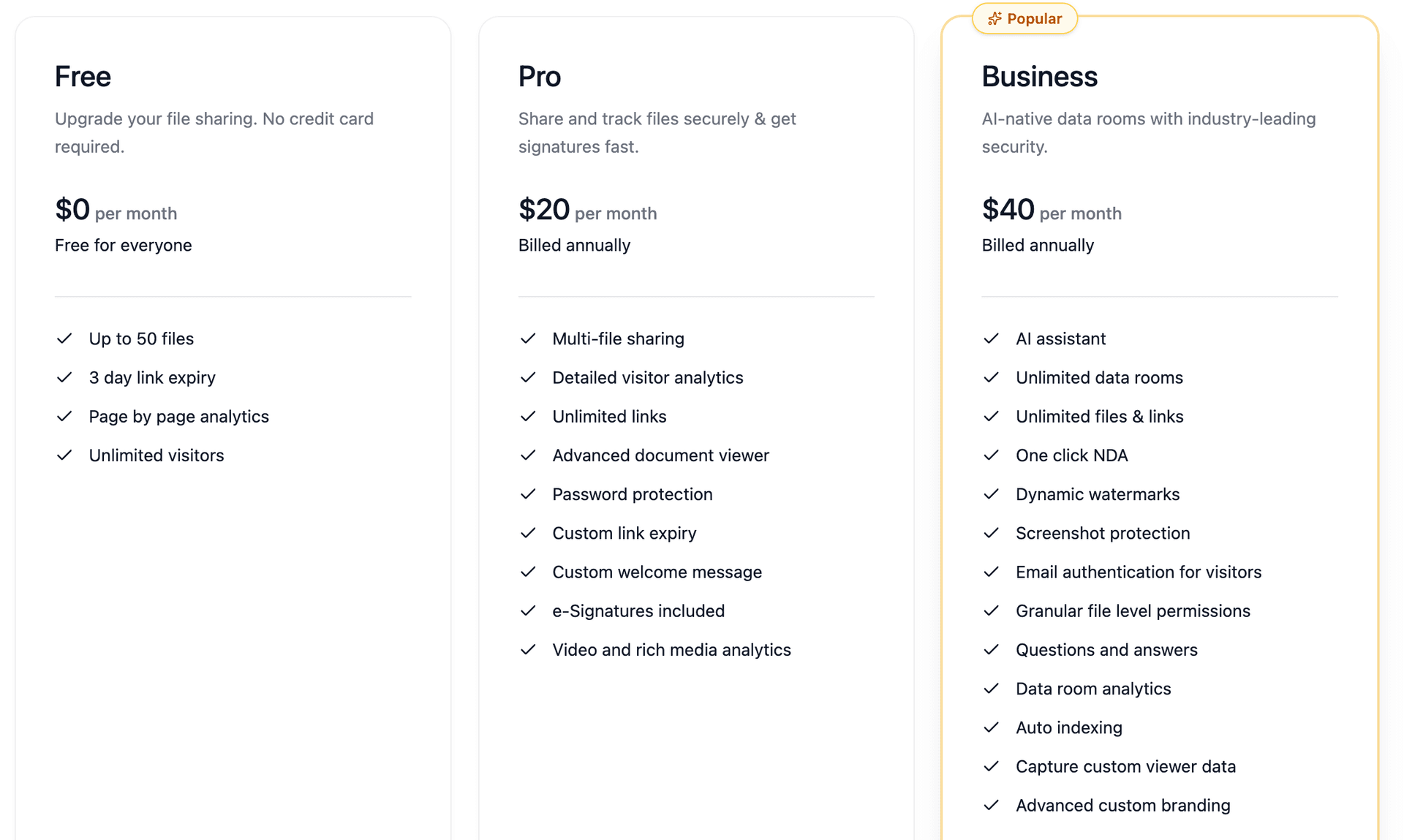
Peony starts free ($0/month, 2 GB) with page-level analytics on every plan. Screenshot protection and dynamic watermarks are included on the Business plan at $40/admin/month. Pro at $20/admin/month adds password protection and e-signatures.
Pros: Strongest available screenshot protection combined with dynamic watermarks, identity-bound access, and per-page analytics. Browser-based — no app installation for recipients. Free tier available. Works for fundraising, M&A due diligence, client deliverables, and any external PDF sharing.
Cons: Requires recipients to view through Peony's secure viewer (which is by design — that is where the protection lives). Does not protect against camera-phone captures, though dynamic watermarks make those traceable.
Best for: Any PDF where a screenshot leak would have real consequences — investor financials, M&A documents, enterprise pricing, board packs, legal agreements, HR documents, IP, and product roadmaps. This is what we use for every sensitive document that leaves our organization.
Method 2: Dynamic watermarking (deterrence + attribution)
Even if you cannot use a full screenshot protection platform, dynamic watermarking alone is one of the strongest practical deterrents. The UK NCSC recommends watermarking as a core control for sensitive data, and DRM vendors consistently rank per-viewer watermarks as the single most effective anti-screenshot measure.
How to do it:
- With Peony: Enable dynamic watermarks in your room settings. Peony automatically overlays the viewer's name, email, and timestamp on every page — no manual PDF editing required.
- Without Peony: Use Adobe Acrobat Pro or a PDF editor to add static watermarks before sharing. This is weaker (same watermark for everyone, easier to crop) but better than nothing.
Why it works: The psychology is powerful. When someone sees their own email address stamped across a document, "let me just screenshot this for reference" becomes "do I really want my name on that image if it leaks?" That shift in calculus prevents more leaks than any technical blocking alone.
Pros: One of the most effective practical deterrents. In Peony, watermarks are automatic and per-viewer. Makes leaks attributable even after they happen. Works alongside every other method.
Cons: Does not technically prevent the screenshot action. Static watermarks (without Peony) are the same for all viewers and can be cropped or edited out. Dynamic, per-viewer watermarks require a platform like Peony.
Best for: Any document sharing scenario. Watermarking should be your baseline for every sensitive PDF, combined with other methods for defense in depth.
Method 3: View-only sharing with download restrictions
Force recipients to view PDFs in a controlled viewer rather than downloading raw files. This is a prerequisite for every other screenshot protection method — if someone has the raw PDF, all viewer-level protections are irrelevant.
How to do it:
- With Peony: Set room permissions to view-only with downloads disabled. Content is viewed in Peony's secure viewer where screenshot protection and watermarks are active. Configure identity-bound access so only verified recipients can view.
- With Google Drive: Share with "Restricted" access and uncheck "Viewers and commenters can see the option to download, print, and copy." Note: this does not prevent screenshots or provide analytics.
- With Microsoft OneDrive/SharePoint: Set permissions to "View only" and disable downloads. Similar limitations to Google Drive.
Pros: Removes the easiest exfiltration path (downloading the raw file). Forces viewing through a controlled environment where additional protections can apply. Available on most cloud platforms at some level.
Cons: On Google Drive and OneDrive, does not prevent screenshots, screen recordings, or manual retyping. No watermarking or analytics on free cloud tiers. In Peony, view-only mode works alongside screenshot protection and watermarks for a much stronger posture.
Best for: As a baseline layer combined with screenshot protection and watermarking. On its own, view-only sharing is friction — not security.
Method 4: Dedicated PDF DRM software
Enterprise DRM tools encrypt PDFs and control viewing through specialized applications that integrate directly with OS-level capture APIs.
How to do it:
Products like Locklizard Safeguard, Fasoo, and Vitrium provide:
- Encrypted PDF viewers that block standard screenshot and screen recording tools
- Dynamic watermarks and detailed audit logs
- Offline viewing with persistent DRM controls
- Policy-based access (expiry, print limits, copy restrictions)
Pros: Deep OS-level integration can block a wider range of capture tools than browser-based solutions. Strong for organizations with managed endpoints and dedicated IT teams.
Cons: Recipients must install a dedicated viewer application — a significant friction point for external sharing with investors, clients, or partners. Licensing is enterprise-oriented ($2,000+ for many tools). Complex to deploy and manage. Not practical for lean teams running a fundraise or client engagement where you need recipients to click a link and view immediately.
Best for: Large regulated organizations (financial services, pharma, defense) with managed endpoints and IT teams that can deploy and support DRM viewers. Not recommended for startup fundraising, M&A data rooms, or any workflow where recipient experience matters.
Method 5: Screen capture protection in virtualized environments
Virtualized desktop platforms can block screenshots and screen recordings at the hypervisor level — the most technically complete screenshot prevention available.
How to do it:
Azure Virtual Desktop and Windows 365 Cloud PC support screen capture protection that:
- Blocks screenshots and screen recordings of remote sessions
- Blanks content in standard capture tools
- Works at the OS level, below application-layer workarounds
Pros: Most technically complete screenshot blocking available. Works against standard screenshot tools, screen recorders, and some advanced capture methods. Good for internal access to highly sensitive documents.
Cons: Only works for users inside your virtualized environment. External investors, clients, and partners will not access documents through your VDI. Requires infrastructure investment and management. Not a solution for external document sharing.
Best for: Internal access to extremely sensitive documents (classified material, regulated personal data, pre-announcement financials) where all viewers are on managed virtual desktops. Complement with Peony for external sharing.
Method 6: Static watermarks + access policy (minimum viable)
The lightest-weight approach — add visible watermarks to your PDFs and pair them with a clear confidentiality policy. Use this as your floor, not your ceiling.
How to do it:
- Add a static watermark ("CONFIDENTIAL - Not for Distribution") using Adobe Acrobat, Preview on Mac, or free tools like SmallPDF. See our Mac watermarking guide for step-by-step instructions.
- Include confidentiality language in your email and in the document itself.
- Use password protection on the PDF file (Adobe Acrobat: File, Protect, Encrypt with Password).
- Restrict sharing to specific recipients by name.
Pros: Free. No platform required. Signals sensitivity and may discourage casual forwarding. Better than sending an unprotected PDF.
Cons: Static watermarks are the same for everyone — no attribution to a specific viewer. Watermarks can be cropped or edited out of screenshots. No screenshot blocking, no analytics, no access revocation. Password protection is file-level only — once someone has the password, they have the file forever. This is a social deterrent, not a technical control.
Best for: Low-sensitivity documents where you want to signal confidentiality, or as a temporary measure until you can implement a proper platform like Peony. Never rely on this alone for documents where a leak would have real consequences.
Comparison table: all methods side by side
| Feature | Peony (Secure Platform) | Dynamic Watermark Only | View-Only Cloud Sharing | DRM Software | Virtualized Desktop | Static Watermark + Policy |
|---|---|---|---|---|---|---|
| Screenshot blocking | Yes (browser + OS API) | No | No | Yes (app-level) | Yes (hypervisor) | No |
| Dynamic per-viewer watermarks | Yes | Peony: Yes / Static: No | No | Most tools: Yes | No | No (same for all) |
| Identity-bound access | Yes | Peony: Yes / Alone: No | Partial (Google account) | Yes | Yes (AD/Entra) | No |
| Per-page view analytics | Yes | Peony: Yes / Alone: No | Limited (Workspace) | Some tools | No | No |
| Access revocation | Yes (instant) | Peony: Yes / Alone: No | Yes (remove user) | Yes | Yes (session) | No (once shared) |
| Download prevention | Yes | N/A | Partial (disables button) | Yes | Yes | No |
| No app install for recipients | Yes (browser-based) | Yes | Yes | No (dedicated app) | No (VDI client) | Yes |
| External sharing friendly | Yes | Yes | Yes | Poor | Poor | Yes |
| Cost | Free - $40/mo | Free (static) - $40/mo | Free - $22+/user/mo | $2,000+ enterprise | Infrastructure cost | Free |
My take: For external sharing — investor decks, M&A documents, client proposals — Peony (free, $0) is the clear choice: screenshot protection, dynamic watermarks, analytics, and access revocation in one browser-based platform with no app install for recipients. For internal documents on managed devices, complement Peony with endpoint DLP or VDI controls. Static watermarks are your floor, never your ceiling.
PDF screenshot protection by the numbers
These statistics explain why "just trust people" is not a document security strategy:
- 60-68% of data breaches involve a human element — people making mistakes, misconfiguring access, or quietly exfiltrating data (Verizon DBIR)
- $4.88 million — average cost of a data breach in 2024, with compromised credentials as the leading cause (IBM Cost of a Data Breach Report)
- 74% of data breaches involve human error, privilege misuse, use of stolen credentials, or social engineering (Verizon DBIR 2023)
- 40.2% of Google Drive files contain sensitive information across 6.5 million files scanned (Metomic, 2023)
- 22% of external Google Drive shares use open "anyone with the link" access (DoControl, 2024)
- 0 number of standard PDF viewers that include screenshot protection (you need a dedicated platform)
Screenshots are one of the easiest "human" exfiltration paths. The person doing it does not even feel like they are doing something wrong — it is just a key combination. That is exactly why layered protection (blocking + watermarking + attribution + analytics) works better than any single control.
Practical tips that prevent real-world PDF leaks
Accept the physics, then design for behavior. You will never defeat a camera pointed at a screen. But you can remove every easy digital capture path, make screenshots personally risky through watermarks, and get enough visibility to react when something looks wrong. That is the realistic standard.
Classify your PDFs before protecting them. Not every PDF needs screenshot protection. Apply data classification: Public, Internal, Confidential, Restricted. Only the top tiers need the full Peony treatment — screenshot blocking, dynamic watermarks, identity-bound access. Overprotecting everything trains people to ignore security signals.
Always pair access control with watermarking. Identity-based access without watermarking is easy to screenshot quietly. Watermarking without access control is noisy but wide open. Together — through Peony's combined approach — they are much stronger than either alone.
Share links, never attachments. The moment you email a PDF attachment, you lose all control. A Peony link keeps the PDF inside the secure viewer where your protections apply. If you update the document, replace the file behind the same link. If a relationship ends, revoke the link.
Audit access quarterly. Every quarter, review which PDFs are in Peony, who has access, and whether downloads are enabled unnecessarily. We do this religiously after learning the hard way — every single audit turns up at least a few shares that should have been revoked months ago.
Send passwords on a separate channel. If you use Peony's password-gated links or encrypt PDFs before sharing, never send the password in the same email thread as the link. Use a text, phone call, or separate messaging app. NIST guidelines recommend long, unique passphrases over complex character requirements.
Bottom line
"Protecting PDFs from screenshots" is not about achieving mathematical impossibility. It is about making leaks rare, risky, and traceable — instead of cheap and invisible.
- Highest protection (investor decks, M&A documents, board packs) — Peony with screenshot protection + dynamic watermarks + identity-bound access + analytics
- Internal high-sensitivity docs on managed devices — Peony for external sharing + endpoint DLP or VDI for internal access
- Moderate sensitivity — View-only sharing with dynamic watermarks through Peony
- Minimum viable — Static watermarks + confidentiality policy + password-protected PDF (use this as a floor only)
The pattern that works in 2026 is simple: author your content wherever you like, then treat Peony as the front door to anything you would hate to see screenshotted and forwarded. Layer screenshot blocking, dynamic watermarks, and identity-bound access instead of hoping people will be sensible.
If you are sharing investor decks, deal documents, or sensitive client files, try Peony for free — set up a screenshot-protected data room in minutes with dynamic watermarks, per-page analytics, and instant access revocation.
FAQ
Can you completely prevent PDF screenshots?
No tool can guarantee 100% screenshot prevention — a camera pointed at a screen will always work. But Peony's layered approach makes casual screenshots nearly impossible and deliberate ones personally risky. Screenshot protection blacks out content during capture, dynamic watermarks embed the viewer's identity in every image, and per-page analytics give you complete visibility into who accessed what.
What is the best way to protect a PDF from screenshots?
The most effective approach is Peony's layered protection: upload your PDF to a secure Peony room, enable screenshot protection (which interferes with OS-level capture tools), add dynamic watermarks (viewer's email and timestamp on every page), restrict access to verified identities, and disable downloads. This combination makes screenshots rare, risky, and traceable.
How does Peony's screenshot protection work?
Peony's screenshot protection integrates with browser and OS-level capture APIs to detect when a screenshot or screen recording is being attempted. When detected, the document content is blacked out or obscured in the capture. Combined with dynamic watermarking and identity-bound access, it creates a layered defense that makes casual leaks nearly impossible — no app installation required for recipients.
Do dynamic watermarks actually prevent screenshots?
Dynamic watermarks do not technically prevent the screenshot action, but they are one of the strongest practical deterrents. Peony's watermarks embed the viewer's name, email, and timestamp on every page. If someone screenshots a watermarked document, their identity is baked into the image — making quiet leaks personally risky. The UK NCSC recommends watermarking as a core control for sensitive data.
Can I see who screenshotted my PDF?
Basic PDFs provide zero screenshot detection. Peony provides complete visibility through per-page analytics — see who accessed your PDF, when, and which pages they viewed. If someone does take a screenshot, Peony's dynamic watermarks embed their identity into the captured image, making the source traceable even after the screenshot is shared.
Is disabling PDF downloads enough to prevent screenshots?
No. Disabling downloads removes one exfiltration path, but screenshots remain the obvious workaround. In Peony, disabling downloads forces viewers into the secure viewer where screenshot protection and dynamic watermarks are active — the two controls work together. Without viewer-level protection, disabling downloads alone is insufficient.
How do I protect sensitive PDFs shared with investors or clients?
Upload PDFs to a Peony data room instead of emailing attachments. Enable screenshot protection, dynamic watermarking, and identity-bound access. Share a single secure link instead of the file. You get per-page analytics showing exactly who viewed what, and you can revoke access instantly when a deal closes or a relationship ends. Peony starts free at $0/month.
What is DRM for PDFs and do I need it?
PDF DRM (Digital Rights Management) encrypts documents and controls how they can be viewed, copied, printed, and captured. Enterprise DRM tools like Locklizard require dedicated viewer apps and complex deployment. Peony provides equivalent protection — screenshot blocking, dynamic watermarks, access controls, and audit trails — through a browser-based viewer with no app installation required, starting free.
Can I protect PDFs from screenshots without requiring recipients to install software?
Yes. Peony's screenshot protection works entirely through the browser — recipients click a secure link and view the document in Peony's protected viewer. No app downloads, no plugins, no special software. Screenshot protection, dynamic watermarks, and access controls all work automatically. This is a key advantage over traditional DRM tools that require dedicated viewer apps.
How much does PDF screenshot protection cost?
Peony starts free at $0/month (2 GB storage) with page-level analytics on every plan. Screenshot protection and dynamic watermarks are included on the Business plan ($40/admin/month). Pro ($20/admin/month) adds password protection and e-signatures. Traditional PDF DRM tools like Locklizard charge $2,000+ for enterprise licenses. Virtual data rooms like Datasite start at $1,000+/month. Peony provides VDR-grade screenshot protection at file-sharing prices.
Related Resources
- How to Download Files from DocSend (Critical Security Flaw) — Chrome extensions bypass DocSend's download protection in one click
- How to Protect Google Docs from Screenshots
- How to Prevent PDF Forwarding
- Dynamic Watermarking Complete Guide
- How to Password Protect PDFs Without Adobe
- How to Add Watermarks to PDFs on Mac
- How to Securely Send Documents via Email
- How to Share Confidential Documents Securely
- Screenshot-Block Data Rooms with Attempt Logging — banker/data-room variant with audit-trail focus for M&A processes
- Secure File Sharing Guide
- How to Password Protect Google Docs
- How to Password Protect Multiple PDFs at Once
- Screenshot Protection Features
- Virtual Data Room Cost Guide
- Peony for M&A Due Diligence
- Peony for Fundraising
- Peony Pricing
You might also like
Apr 7, 2026
How to Prevent PDF Forwarding in 2026 (7 Methods — Only 1 Tracks Who Leaked)
Mar 21, 2026
How to Protect Your Pitch Deck (Before an Investor Leaks It) in 2026
Mar 21, 2026
How to Share Files Securely in 2026 (7 Methods I Actually Trust)
