How to Send Confidential Documents via Email (7 Methods) in 2026

Co-founder at Peony — I built the data room platform, with a background in document security, file systems, and AI.
Connect with me on LinkedIn! I want to help you :)Last updated: March 2026
I run Peony (a data room platform), so I send and receive confidential documents every day — investor decks, legal agreements, financial models, client contracts. I have tested every method in this guide myself, from Gmail Confidential Mode to full S/MIME certificate setup, and I can tell you exactly where each one breaks down.
The core problem is simple: email was designed for communication, not document security. Every method in this guide is a workaround for a system that was never built to protect files. Some workarounds are better than others.
TL;DR — 94% of malware is delivered via email (Verizon DBIR). The IBM 2024 Cost of a Data Breach Report puts the average breach at $4.88 million. And BEC losses exceeded $2.9 billion in 2023 (FBI IC3). Below are seven methods to send confidential docs via email in 2026 — ranked from free built-in options to professional-grade protection.
Quick Guide: 7 Methods at a Glance
| Method | Cost | Encryption | Tracking | Revocation | Best For |
|---|---|---|---|---|---|
| Gmail Confidential Mode | Free | TLS (not E2E) | No | Expiry only | Casual sensitive emails |
| Outlook/M365 Encryption | Free with M365 | OME/RMS | No | Limited | Enterprise B2B |
| Password-Protected PDF/ZIP | Free | AES-256 | No | No | One-off legal files |
| S/MIME or PGP | Free (setup cost) | End-to-end | No | No | Regulated industries |
| Drive/OneDrive Shared Links | Free | TLS + at rest | Basic | Manual | Internal collaboration |
| ProtonMail/Tuta | Free tier | End-to-end | No | Expiry only | Privacy-focused comms |
| Peony | Free | AES-256 + TLS 1.3 | Per-viewer, per-page | One-click | Deals, investors, clients |
Method 1 — Gmail Confidential Mode
Gmail Confidential Mode is the fastest free option if both you and your recipient use Gmail. It is built into every Gmail account — no setup, no downloads, no certificates.
How it works
- Open Gmail and click Compose.
- Click the lock-and-clock icon at the bottom of the compose window (or More options then Confidential mode).
- Set an expiration date (1 day, 1 week, 1 month, 3 months, or 5 years).
- Optionally require an SMS passcode — the recipient must enter a code sent to their phone before viewing.
- Click Save and send your email.
The recipient sees the message in a restricted view. Forwarding, copy, print, and download buttons are disabled in the Gmail interface.
Pros
- Free and built into every Gmail account — zero setup
- Expiration dates give you a time limit on access
- SMS passcode adds a second verification layer
- Disables forwarding, copy, and print buttons in the Gmail UI
Cons
- Not end-to-end encrypted — Google can read the message on their servers
- Recipients can screenshot the content freely — no blocking, no logging
- Restrictions only apply in the Gmail web client and mobile app — email clients that render the full message body may bypass them
- No tracking: you cannot see who opened the email, when, or whether they viewed attachments
- No dynamic watermarking
- Expiration deletes the email entirely rather than revoking document access
- Attachments in confidential mode still sit on Google's servers
Best for
Low-to-medium sensitivity emails where you want a basic expiration layer. Tax receipts, scheduling confirmations with sensitive dates, or draft agreements you want to auto-delete. Not suitable for investor decks, M&A documents, or anything where you need visibility into who actually read the content.
Method 2 — Outlook/Microsoft 365 Message Encryption
If your organization runs Microsoft 365, you already have access to Office Message Encryption (OME) and Azure Rights Management (RMS). These tools encrypt the email and can restrict what recipients do with it.
How it works
- Open Outlook (desktop or web) and compose a new email.
- Click Options then Encrypt.
- Choose your protection level:
- Encrypt-Only — encrypts the message; recipients can forward and download
- Do Not Forward — encrypts and blocks forwarding, printing, and copying the email body
- Confidential or custom labels (if your admin configured sensitivity labels in Microsoft Purview)
- Send the email.
External recipients who do not use Microsoft 365 receive a link to view the encrypted message in a browser, where they authenticate with a Microsoft account or a one-time passcode.
Pros
- Included with Microsoft 365 Business Basic and above — no extra cost
- "Do Not Forward" restricts forwarding, printing, and copy for the email body
- Works with external recipients via browser-based viewing
- Integrates with Microsoft Purview sensitivity labels for organization-wide policies
- Microsoft documents the options here
Cons
- External recipients face friction — they must sign in with a Microsoft account or use a one-time passcode, which some find confusing
- Once an attachment is legitimately downloaded, all restrictions end — the file is a regular unprotected file on their disk
- No per-viewer analytics: you know the email was delivered, not who read the attachment or for how long
- No dynamic watermarking on documents
- No screenshot protection
- "Do Not Forward" does not prevent screenshots, photos of the screen, or verbal disclosure
Best for
Enterprise B2B communication where both parties are on Microsoft 365 or comfortable with the Microsoft authentication flow. Legal notices, compliance correspondence, and internal confidential memos. Less suitable for investor relations or deal rooms where recipients span multiple platforms and you need engagement data.
Method 3 — Password-Protected PDF/ZIP Attachments
The oldest method in the book: encrypt the file itself, send it as an attachment, and share the password through a separate channel.
How it works
For PDFs:
- Open the PDF in Adobe Acrobat (paid) or use a free tool like LibreOffice or macOS Preview.
- Set a document-open password with AES-256 encryption.
- Save and attach the encrypted PDF to your email.
- Send the password via a separate channel — SMS, phone call, Signal, or a different email thread.
See our guide to password protecting multiple PDFs for batch workflows, our complete guide to sending password-protected PDFs for a deeper walkthrough, or our Mac and Windows file protection guides for platform-specific steps.
For ZIP archives:
- Use 7-Zip (Windows) or Keka (Mac) to create an encrypted archive.
- Select AES-256 encryption and check "Encrypt file names" if using .7z format.
- Attach and send. Share the password separately.
Pros
- Free — no paid tools required (7-Zip, LibreOffice, macOS Preview all work)
- AES-256 encryption is genuinely strong when the password is strong
- Works with any email client — no special setup on the recipient's side
- Cross-platform: encrypted PDFs and ZIPs open on Windows, Mac, Linux, and mobile
Cons
- Zero tracking — you have no idea who opened the file, when, or whether they forwarded it
- Zero revocation — once the password is shared, you cannot take it back
- Passwords travel alongside the file in practice (forwarded in the same email thread, shared in Slack, texted to the wrong person)
- No watermarking — if the document leaks, you cannot trace the source
- Recipients get a permanent, uncontrolled copy of the file
- 25 MB attachment limit on Gmail and Outlook means large documents bounce
Best for
One-off legal or compliance documents where the recipient specifically expects an encrypted attachment and you accept full loss of control after delivery. Tax filings, signed contracts for archival, or regulatory submissions with password requirements.
Method 4 — S/MIME or PGP End-to-End Encryption
S/MIME (Secure/Multipurpose Internet Mail Extensions) and PGP (Pretty Good Privacy) provide genuine end-to-end encryption — meaning only the sender and recipient can read the message. Not your email provider, not your IT department, not a government with a subpoena to Google.
How it works
S/MIME:
- Obtain a personal S/MIME certificate from a Certificate Authority (many offer free email certificates — Actalis, Sectigo).
- Install the certificate in your email client (Outlook, Apple Mail, and Thunderbird all support S/MIME natively).
- Exchange public keys with your recipient (they need their own certificate).
- Compose your email and select the encrypt option — the client encrypts using the recipient's public key.
PGP/GPG:
- Generate a PGP key pair using GPG or a client like Thunderbird with OpenPGP built in.
- Publish your public key or exchange it directly with your recipient.
- Import the recipient's public key into your keyring.
- Compose and encrypt using PGP — the recipient decrypts with their private key.
Pros
- True end-to-end encryption — the email provider cannot read the content
- S/MIME is supported natively in Outlook, Apple Mail, and Thunderbird
- PGP/GPG is open source and free
- Both meet regulatory requirements for encrypted communication in industries like healthcare (HIPAA), finance, and legal
Cons
- Both sides must have certificates or keys — this is the dealbreaker for most use cases. You cannot S/MIME-encrypt an email to an investor who has never set up a certificate
- Setup is technical and error-prone for non-technical recipients
- No tracking: once the recipient decrypts, you have no visibility into what happens next
- No revocation: a decrypted email is just a regular email
- No watermarking, no screenshot protection
- Certificate management at scale is an administrative burden
- PGP key servers have had security and privacy issues
Best for
Regulated industries where both parties already have certificate infrastructure — legal firms exchanging privileged documents, healthcare organizations communicating PHI, financial institutions with established S/MIME deployments. Not practical for ad-hoc sharing with investors, clients, or partners who have no certificate setup.
Method 5 — Google Drive/OneDrive Shared Links with Restrictions
Instead of attaching a file, upload it to cloud storage and share a restricted link. This gives you more control than a raw attachment — but less than most people assume.
How it works
Google Drive:
- Upload the document to Google Drive.
- Right-click and select Share.
- Add specific email addresses (requires Google accounts for full restriction).
- Uncheck Viewers can download, print, and copy under the gear icon.
- Copy and email the link.
OneDrive/SharePoint:
- Upload the document.
- Click Share and select Specific people.
- Uncheck Allow editing and optionally set an expiration date (requires Microsoft 365 Business or above).
- Copy and email the link.
Pros
- Free with Google Workspace or Microsoft 365
- Restricts access to specific accounts (not "anyone with the link")
- Can disable download, print, and copy in the viewer
- OneDrive and SharePoint support link expiration (paid plans)
- Recipients view in the browser — no downloads required
Cons
- Google Drive restrictions require recipients to have Google accounts; OneDrive restrictions require Microsoft accounts — friction for external parties
- No per-viewer analytics showing who read which page and for how long
- No dynamic watermarking
- No screenshot protection — the content is visible in the browser and fully capturable
- Revoking access means manually editing share permissions per file
- "Disable download" can be bypassed by tech-savvy users (right-click save, screen recording, browser developer tools)
- No NDA gating, no e-signatures, no audit trail for compliance
Best for
Internal team collaboration or sharing with trusted partners who are already on the same platform (Google Workspace or Microsoft 365). Not suitable for investor relations, M&A due diligence, or any workflow where you need proof of who accessed what.
Method 6 — Encrypted Email Services (ProtonMail, Tuta)
Dedicated encrypted email providers build end-to-end encryption into the platform itself — you do not need certificates, keys, or technical setup.
How it works
ProtonMail:
- Create a free account at proton.me.
- Emails between ProtonMail users are automatically end-to-end encrypted.
- For external recipients (Gmail, Outlook), click the lock icon and set a password. The recipient gets a link to view the encrypted message in their browser, authenticated by the password you share separately.
- Set an optional expiration timer.
Tuta (formerly Tutanota):
- Create a free account at tuta.com.
- Emails between Tuta users are automatically end-to-end encrypted.
- For external recipients, set a shared password. The recipient views the message in Tuta's web viewer.
Pros
- End-to-end encryption by default between users of the same service
- Password-protected messages work for external recipients — no certificates needed
- Free tiers available on both platforms
- Open source and independently audited
- Based in privacy-friendly jurisdictions (Switzerland for ProtonMail, Germany for Tuta)
Cons
- Encrypted emails to external recipients still require password sharing through a separate channel
- No per-document analytics — you cannot see who opened the attachment, which pages they read, or how long they spent
- No dynamic watermarking
- No screenshot protection
- Once the recipient accesses and downloads the attachment, control ends
- External recipients must use a web viewer — some find this friction confusing
- Switching your entire email to a new provider is a major change for most organizations
- Limited storage on free tiers (1 GB on ProtonMail, 1 GB on Tuta)
Best for
Privacy-conscious individuals and organizations that want encrypted communication by default. Whistleblower submissions, journalist-source communication, and personal financial correspondence. Less suitable for business deal workflows where you need analytics, watermarking, and document-level control.
Method 7 — Secure Document Sharing Platform — Peony
Every method above treats the problem as an email encryption challenge. Peony treats it differently: keep the document out of email entirely. Email becomes the notification layer — you send a link, the recipient clicks and views in a secure browser environment. The document never leaves your control.
This is the method I use for everything that matters: investor decks, M&A due diligence packs, client contracts, board materials, and fundraising data rooms. For a deeper look at what makes a VDR different from basic cloud storage, see the full comparison.
How it works
- Upload your documents to a Peony data room — PDFs, Word, Excel, PowerPoint, images, videos. AI auto-indexes and organizes everything in under 3 minutes.
- Set access controls: identity-bound access (specific email addresses or domains), password gating, NDA gates (require a signed NDA before viewing), link expiry, and two-factor authentication.
- Enable protection layers: dynamic watermarks with the viewer's name and email stamped into every rendered frame, screenshot protection that blocks and logs capture attempts.
- Share one link via email — Gmail, Outlook, whatever you use. The recipient clicks, verifies their identity, and views documents in a secure browser viewer.
- Monitor access: page-level analytics show exactly who opened each document, when they accessed it, how long they spent on every page, and whether they returned.
- Revoke access with one click — kill a specific viewer's access or shut down the entire room. Works instantly, even after the recipient has already viewed the document.
If you update a document, replace it in Peony behind the same link. Recipients always see the latest version — no more "NDA_v3_FINAL_realfinal.pdf" in email threads.
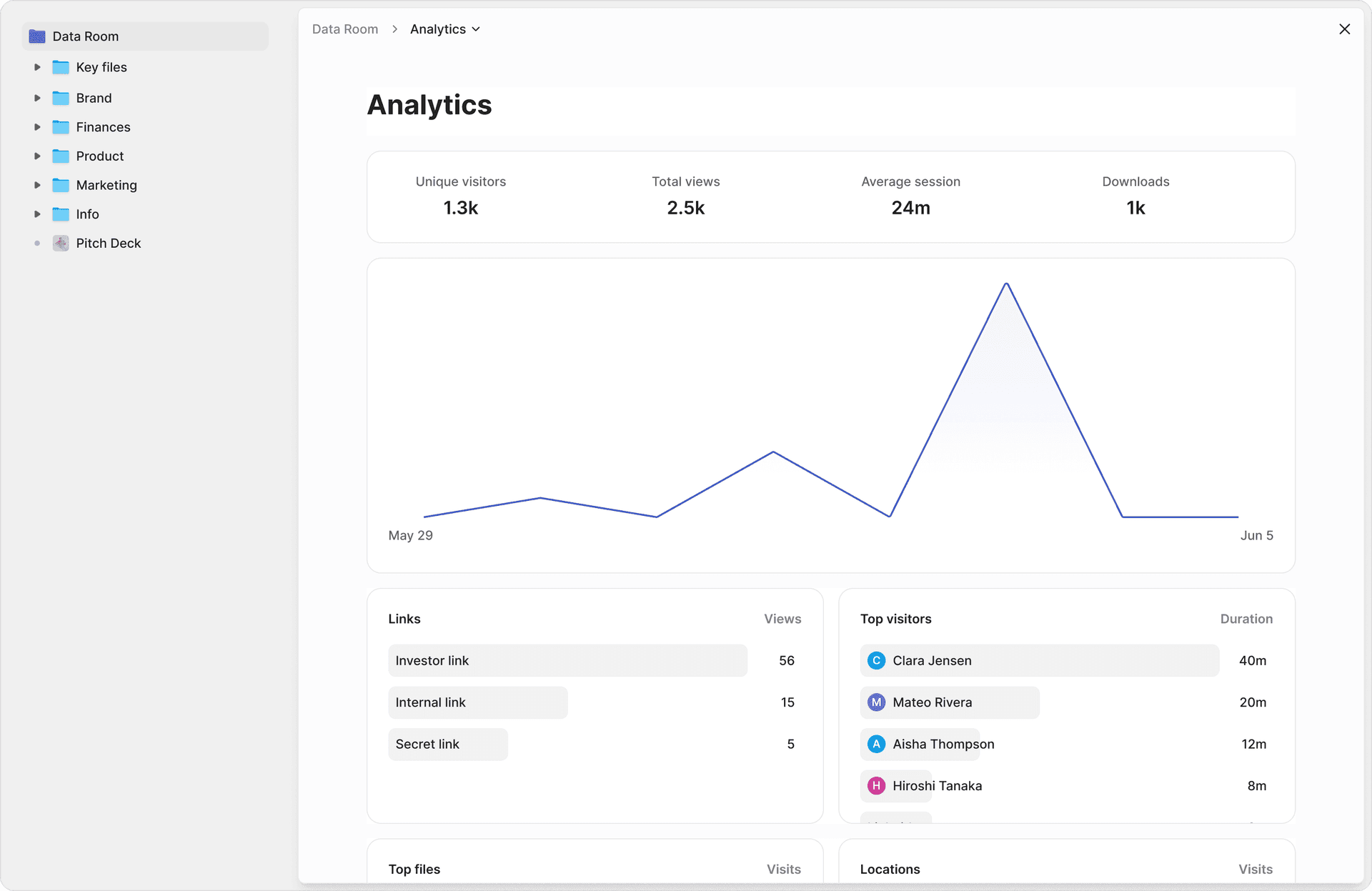
What I actually see when someone views my documents
This changed everything about how I share confidential documents. After uploading a financial model to Peony and emailing the link to a potential acquirer, I can see:
- Which person opened the document, verified by email identity
- How long they spent on each page (the revenue projections got 4 minutes, the appendix got 12 seconds — that tells me something)
- Whether they came back for a second review before our next call
- Whether anyone attempted a screenshot (blocked and logged with a timestamp)
For a full walkthrough of how dynamic watermarks work as a leak deterrent, see our watermarking guide. Before Peony, I was emailing password-protected PDFs with the password in a separate Slack message. I had no idea who actually read the documents, who forwarded them, or whether the password made it to people I never intended to have access.
Why this works better than email encryption
Email encryption protects the message in transit. Peony protects the document itself — permanently. The comparison is not "Peony vs. Gmail Confidential Mode." It is "hoping recipients behave" vs. "controls that work regardless of what recipients do."
- Page-level analytics tell you who is serious and who is stalling — critical for fundraising and due diligence workflows
- Dynamic watermarks mean every frame of every document carries the viewer's identity — if something leaks, there is a forensic trail
- Screenshot protection raises the cost of casual capture from zero to "blocked and logged with your name attached"
- NDA gates ensure legal coverage before anyone sees a single page
- E-signatures are built in with AI-powered field detection — no switching to a separate signing tool
- AI document extraction lets counterparties ask natural-language questions across every document and get cited answers with exact page numbers
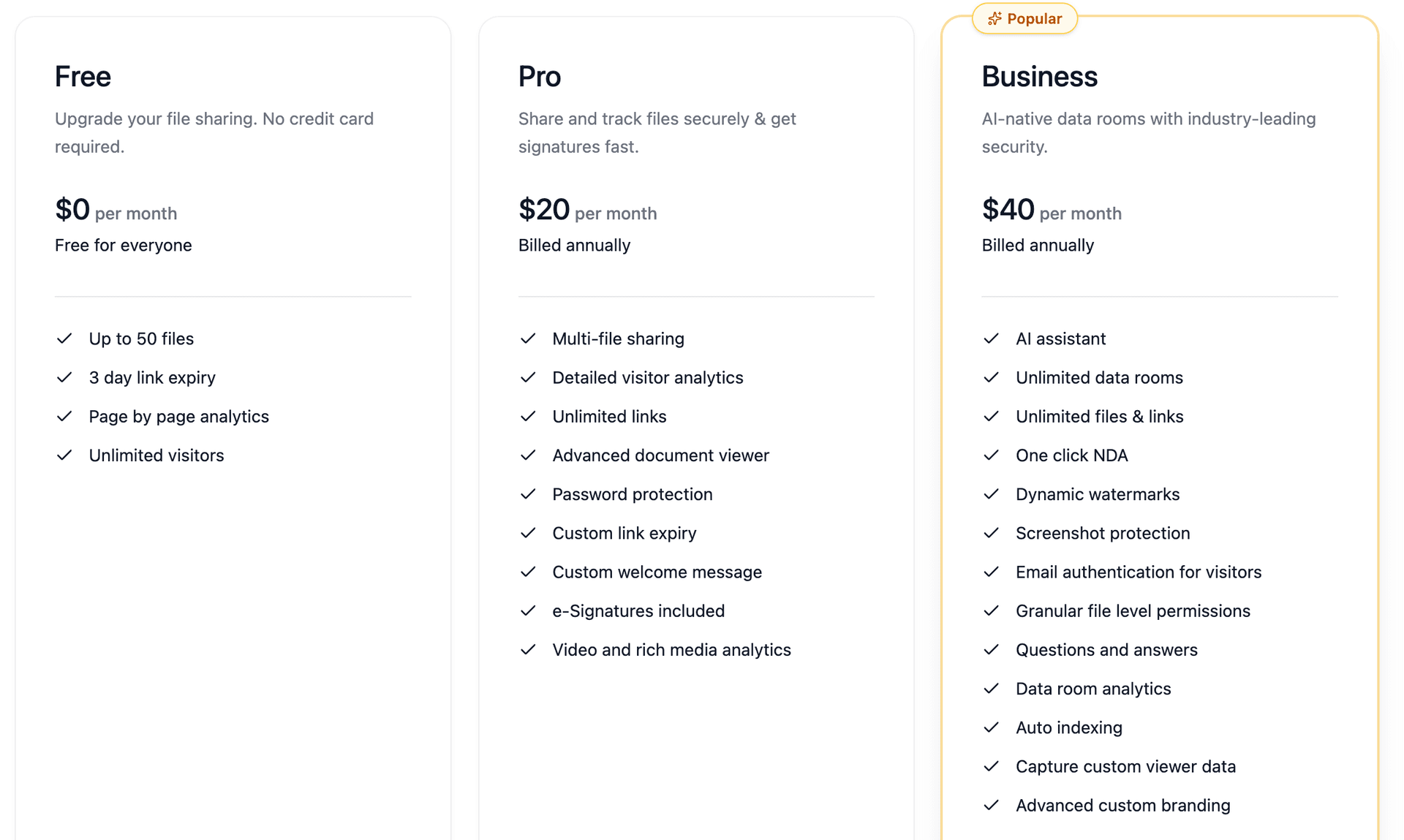
Pricing
Peony's free tier covers most individual workflows. Pro is $20/admin/month, Business is $40/admin/month. Compare that to the $4.88 million average data breach cost (IBM, 2024) or the legal fees from discovering that your confidential financial model was forwarded to a competitor.
Best for
Any confidential document workflow: investor decks, M&A data rooms, due diligence packs, client proposals, board materials, HR documents, legal agreements. If you would be uncomfortable seeing the document forwarded without your knowledge, it should go through Peony, not as an email attachment.
Method Comparison
| Feature | Peony | Gmail Confidential | Outlook OME | PDF/ZIP Password | S/MIME/PGP | Drive/OneDrive | ProtonMail/Tuta |
|---|---|---|---|---|---|---|---|
| Cost | Free | Free | Free with M365 | Free | Free (setup cost) | Free | Free tier |
| Encryption | AES-256 + TLS 1.3 | TLS | OME/RMS | AES-256 | End-to-end | TLS + at rest | End-to-end |
| Per-viewer tracking | Yes | No | No | No | No | No | No |
| Per-page analytics | Yes | No | No | No | No | No | No |
| Dynamic watermarks | Yes | No | No | No | No | No | No |
| Screenshot protection | Yes | No | No | No | No | No | No |
| One-click revocation | Yes | Expiry only | Limited | No | No | Manual | Expiry only |
| NDA gating | Yes | No | No | No | No | No | No |
| E-signatures | Yes | No | No | No | No | No | No |
| No recipient setup | Yes | Yes | Partial | Yes | No | Partial | Partial |
| Works with any email client | Yes | Gmail only | Best with M365 | Yes | Requires certs | Platform-tied | Platform-tied |
By the Numbers
- 94% of malware is delivered via email (Verizon 2024 DBIR)
- $4.88 million — average cost of a data breach in 2024 (IBM Cost of a Data Breach Report)
- $2.9 billion — BEC (business email compromise) losses reported in 2023 (FBI IC3 Annual Report)
- 65% of organizations experienced a successful phishing attack in 2024 (Proofpoint State of the Phish)
- 91% of cyberattacks begin with a spear-phishing email (KnowBe4)
- 347 billion emails sent and received daily worldwide in 2026 (Statista)
- 241 days — average time to identify and contain a data breach (IBM 2024)
- Under 3 minutes — time for Peony's AI to auto-index and organize uploaded documents in a data room
Practical Tips
A few habits that separate confident document sharing from hoping nothing goes wrong:
-
One simple rule: If you would be uncomfortable seeing the document forwarded without your knowledge, do not attach it to an email. Upload it to Peony and share the link. You keep version control, access control, and full analytics. The recipient gets a clean viewing experience.
-
Never send file and password in the same channel. If you use password-protected PDFs or ZIPs, email the file but send the password over a different medium — SMS, phone call, Signal, or a face-to-face conversation. Better yet, use Peony's identity-bound access so no password sharing is needed at all.
-
Double-check the To field. Autocomplete is responsible for more confidential document leaks than hackers are. On high-stakes sends, manually verify every recipient address before hitting send. If you share via Peony link instead, a misdirected email is recoverable — revoke the link and the document is inaccessible.
-
Review access quarterly. Old deals close, investors pass, employees leave, vendor relationships end. Set a calendar reminder to review who has access to your shared documents. In Peony, this takes minutes — one dashboard shows every active viewer across all rooms.
-
Do not rely on "Disable Download" alone. Google Drive and OneDrive let you disable downloads, but tech-savvy users can bypass this with browser developer tools, screen recording, or simply photographing the screen. Dynamic watermarks and screenshot protection are deterrence layers that work even when download restrictions fail.
-
Consider a dedicated document sharing platform. If your team regularly sends confidential files to external parties, a consumer cloud drive may not be enough. See our enterprise file sharing solutions comparison for platforms built specifically for controlled external sharing at scale.
-
Standardize your team's email template. Give everyone a script for sharing confidential links:
"Here is a secure link to the latest version of the materials. This gives us better control and ensures you always see the current numbers. Let me know if anyone else on your team needs access."
Professional. Low friction. No attachment bouncing.
Why Peony for Confidential Documents
I built Peony to solve the exact problem this guide describes: email is fine for communication, but it was never designed to protect documents. Every method in this guide either protects the email (not the document) or hands over a permanent copy (no control after sending).
Peony is the only method here that gives you all six layers at once: identity verification, password gating, dynamic watermarks, screenshot protection, page-level analytics, and instant revocation.
Whether you are sharing a pitch deck with 30 investors, running M&A due diligence with a buyer, or sending HR documents to a new hire, the workflow is the same: upload, set controls, share one link. The document never touches an inbox as an attachment. You keep control for as long as you need it.
Get started free — no credit card required.
Frequently Asked Questions
What is the safest way to send confidential documents via email?
The safest approach is to never attach the document directly. Instead, upload it to a secure sharing platform like Peony and email the link. Peony provides page-level analytics showing who read which page and for how long, dynamic watermarks with the viewer's identity in every frame, screenshot protection that blocks and logs capture attempts, and one-click revocation if access needs to end. Free methods like Gmail Confidential Mode or password-protected PDFs add a layer but give you zero visibility after sending.
Is Gmail Confidential Mode actually secure?
Gmail Confidential Mode disables forwarding, copy, print, and download buttons in the Gmail interface and lets you set an expiration date. But it is not end-to-end encrypted — Google can still read the message. Recipients can screenshot the content, and the attachment restriction only works within Gmail's web client. For documents that need real protection, Peony blocks and logs screenshot attempts, applies dynamic watermarks with the viewer's name in every frame, and lets you revoke access instantly.
Can I recall or revoke a confidential email after sending it?
Gmail and Outlook both offer limited recall features that only work under narrow conditions — same organization, unread, within a short window. Once a recipient opens the email or downloads the attachment, recall fails. Peony solves this completely: because you share a link instead of an attachment, you can revoke access with one click at any time, even after the recipient has already viewed the document.
How do I send confidential documents via email for free?
Three free methods work well for low-stakes documents: Gmail Confidential Mode (set expiry and disable forwarding UI), Microsoft 365 Message Encryption (encrypt and restrict forwarding in Outlook), and password-protected PDF or ZIP attachments sent with the password through a separate channel. For higher-stakes documents, Peony has a free tier that includes page-level analytics, dynamic watermarks, screenshot protection, and instant revocation — all at $0.
Is it safe to send confidential documents as email attachments?
Raw email attachments are the least safe option. Once sent, you cannot control forwarding, copying, or downloading. The IBM 2024 Cost of a Data Breach Report puts the average breach cost at $4.88 million, and the Verizon DBIR found that 94% of malware is delivered via email. Peony eliminates the attachment entirely — recipients view documents in a secure browser viewer with identity verification, NDA gating, and screenshot protection.
What is the difference between email encryption and secure document sharing?
Email encryption (TLS, S/MIME, PGP) protects the message in transit between mail servers. Once the recipient decrypts and opens the email, the attachment is a regular file they can forward, copy, or screenshot. Secure document sharing through Peony protects the document itself — access is identity-bound, every page is watermarked with the viewer's name, screenshot attempts are blocked and logged, and you can revoke access at any time.
Do I need S/MIME or PGP to send confidential documents?
S/MIME and PGP provide genuine end-to-end encryption for email content, but both require certificate setup on both sides, which makes them impractical for external recipients like investors or clients. They also provide zero visibility after decryption — you cannot see who opened the attachment, how long they read it, or whether they forwarded it. Peony requires no setup from recipients: they click a link, verify their identity, and view documents with full page-level analytics tracked on your side.
How do I track who opened a confidential document I sent via email?
Standard email gives you a delivery receipt at best — you know it arrived, not whether anyone read the attachment. Read receipts are easily ignored. Peony provides page-level analytics showing exactly who opened your document, when they accessed it, how long they spent on every page, and whether they attempted a screenshot. This works on the free tier with no per-viewer fees.
Related Resources
- Secure File Sharing Guide
- How to Password Protect Multiple PDFs at Once
- How to Password Protect Files on Mac (5 Methods)
- How to Password Protect Files on Windows (5 Methods)
- Dynamic Watermarking Guide
- Document Security Software
- What Is a Virtual Data Room?
- How to Password Protect Google Docs
- How to Protect PDF from Screenshots
- Startup NDA Guide
- Due Diligence Data Room Checklist
- How to Track Pitch Deck Engagement
