How to Password Protect Files on Windows (BitLocker Isn't Enough) in 2026

Co-founder at Peony — I built the data room platform, with a background in document security, file systems, and AI.
Connect with me on LinkedIn! I want to help you :)Last updated: March 2026
If you are here, you are probably not trying to hide a desktop shortcut.
You are thinking about real files — financial models, contracts, client data, HR documents, board decks — on a Windows PC that would cause genuine damage if they leaked. I run Peony (a data room company), so I test file protection on every major platform. Half my team works on Windows, and this is the setup I put on every one of their machines: BitLocker for full-disk encryption, 7-Zip for anything that needs archiving, and Peony for every file that leaves the PC.
TL;DR — Windows has solid built-in encryption: BitLocker for full-disk (Pro/Enterprise), EFS for file-level, Office encryption for documents, and 7-Zip for AES-256 archives. All free. But none give you any visibility or control after you share a file — no tracking, no revocation, no watermarking. The IBM 2025 Cost of a Data Breach Report puts credential-related breaches at $4.67 million on average, Verizon's 2025 DBIR found ~60% of breaches involve the human element, and the average breach takes 241 days to identify. If your files leave your Windows PC, a password alone is not enough.
Password protecting files on Windows means encrypting or restricting access so that only authorized people can open your content. Windows offers multiple layers of encryption — BitLocker uses AES in XTS mode for full-disk encryption, EFS provides file-level protection tied to your user account, and tools like 7-Zip offer AES-256 for portable archives.
But here is the gap that every Windows user hits: all of these methods protect files at rest on your PC. The moment you attach a file to an Outlook email, drop it in a Teams chat, or upload it to a shared OneDrive folder, you lose all control — see our secure file sharing guide for the full picture. That is why I split my workflow into "local protection" (Windows built-in tools) and "sharing protection" (Peony — identity-bound access, password gating, page-level analytics, and one-click revocation).
This guide covers all five methods so you can pick what fits your situation. (On a Mac instead? See our Mac file protection guide.)
Quick Guide: 5 Methods Compared
| Method | Cost | Protects | Tracking | Revocation | Best For |
|---|---|---|---|---|---|
| BitLocker | Free (Pro/Enterprise) | Entire disk | No | No | Baseline for every Windows Pro PC |
| EFS (Encrypted File System) | Free (Pro/Enterprise) | Files/folders | No | No | Sensitive local files |
| Office Built-In Encryption | Free with Office | Office documents | No | No | Quick single-file protection |
| 7-Zip AES-256 Archives | Free (any edition) | File bundles | No | No | Cross-platform file delivery |
| Peony (secure sharing) | Free | Shared files | Per-viewer, per-page | Yes | Client files, investor decks, HR docs |
Method 1 — BitLocker (Full-Disk Encryption)
BitLocker is Windows' answer to macOS FileVault — it encrypts your entire drive so that if your laptop is lost or stolen, the data cannot be read without authentication.
How to enable BitLocker
- Open Settings then Privacy & security then Device encryption (Windows 11) or search for "Manage BitLocker" in the Start menu.
- Click Turn on BitLocker for each drive you want to protect.
- Choose how to back up your recovery key: Microsoft account, USB flash drive, file, or print.
- Choose encryption mode: XTS-AES for internal drives (recommended), AES-CBC for removable drives that need cross-device compatibility.
- Encryption runs in the background — your PC stays usable.
Important edition note: Full BitLocker with Group Policy controls is available on Windows Pro, Enterprise, and Education editions. Windows 11 Home includes Device Encryption on supported hardware (requires TPM 2.0 and UEFI Secure Boot), which provides similar drive-level encryption but without BitLocker's advanced management options. Starting with Windows 11 24H2, Device Encryption is enabled by default on clean installs with a Microsoft Account — both Home and Pro.
I enabled BitLocker on my work laptop the day I started handling client data. The performance impact on modern SSDs with hardware AES acceleration is negligible — I have never noticed a slowdown.
Pros
- Ships with Windows Pro and Enterprise, no downloads needed
- Uses AES-128 or AES-256 in XTS mode, the standard NIST recommends for disk encryption
- TPM 2.0 integration on modern PCs stores encryption keys in dedicated hardware
- Protects against physical theft, lost devices, and unauthorized disk removal
- Encrypts external USB drives with BitLocker To Go
Cons
- Not available on Windows Home (only Device Encryption, which is less configurable)
- Protects data at rest only — does nothing for files you share
- Recovery key management is critical — if you lose the key and forget your password, data is unrecoverable
- No per-file granularity (entire drive or nothing)
Best for
Every Windows Pro/Enterprise PC with sensitive data. This is baseline security, not optional.
Method 2 — EFS (File and Folder-Level Encryption)
When BitLocker covers the whole disk but you want encryption on specific files or folders — visible only to your Windows user account — EFS (Encrypting File System) is the built-in answer.
How to encrypt files with EFS
- Right-click the file or folder you want to encrypt.
- Select Properties then click Advanced.
- Check Encrypt contents to secure data and click OK.
- Choose whether to encrypt just the file or the parent folder and all contents.
- Back up your EFS certificate immediately (search for "Manage file encryption certificates" in the Start menu). If your Windows account is lost or reset without the certificate backup, the encrypted files are unrecoverable.
The encrypted files appear normal to you when logged into your account. Other users on the same PC — or anyone who removes the hard drive — see them as inaccessible.
I use EFS for a "Confidential" folder on my work PC that contains client financial models and internal strategy documents. Even if IT accesses the machine for maintenance, those files stay encrypted to my account.
Pros
- Built into Windows Pro, Enterprise, and Education — no third-party software
- Granular: encrypt individual files or specific folders, not the whole disk
- Transparent to the encrypting user — files open normally when you are logged in
- Combines with BitLocker for defense in depth (disk-level + file-level)
Cons
- Not available on Windows Home — this is the biggest limitation
- Tied to your Windows user account — if the account is reset without a certificate backup, files are permanently lost
- No access tracking, no revocation, no watermarking after sharing
- If you copy an EFS-encrypted file to a USB drive or email it, the encryption is typically stripped — the file arrives unprotected
Best for
Sensitive local files on shared PCs (multi-user machines, laptops that IT manages) where you need file-level isolation beyond BitLocker's drive-level protection. Windows Pro/Enterprise only.
Method 3 — Microsoft Office Built-In Encryption
For individual Word, Excel, or PowerPoint files, Microsoft Office includes built-in password protection — no extra software needed.
How to password protect an Office document
- Open the file in Word, Excel, or PowerPoint.
- Go to File then Info then Protect Document (or Protect Workbook / Protect Presentation).
- Click Encrypt with Password.
- Set a strong password and click OK.
- Save the file. It now requires the password to open.
Modern versions of Office (2016 and later) use AES-256 encryption — the same standard used by government agencies. The resulting file opens in any compatible version of Office across Windows, Mac, and mobile.
I used this for years before switching to Peony for anything I share externally. The breaking point came when I password-protected a financial model in Excel, emailed it to a potential acquirer, shared the password over Teams, and three months later discovered the file had been forwarded to two other parties I had never authorized. The Excel encryption was still intact — but the password traveled with it. See our guide to protecting Excel files for more.
Pros
- Free with any Office installation or Microsoft 365 subscription
- AES-256 encryption on modern Office versions
- Cross-platform: protected files open on Windows, Mac, and mobile Office apps
- Simple three-step process familiar to any Office user
Cons
- One file at a time — no batch encryption
- No tracking: you cannot see who opened the file or when
- No revocation: once the password is shared, access is permanent
- Password gets forwarded alongside the file in practice (Teams, Slack, email threads)
- Only works for Office file formats (.docx, .xlsx, .pptx) — not PDFs, images, or other files
Best for
Quick protection for a single Office document you are storing locally or sharing with someone you fully trust.
Method 4 — 7-Zip AES-256 Encrypted Archives
To bundle multiple files into one password-protected package — especially for cross-platform delivery — 7-Zip is the standard free tool on Windows.
How to create an encrypted archive with 7-Zip
- Download and install 7-Zip (free, open source).
- Right-click the file(s) or folder you want to protect.
- Select 7-Zip then Add to archive.
- Choose Archive format: 7z (or ZIP if you need broader compatibility).
- Under Encryption, enter a strong password.
- Set Encryption method: AES-256.
- Check Encrypt file names (7z format only — hides even the file names inside the archive).
- Click OK.
The resulting .7z file is encrypted with AES-256 and can be opened on any platform with 7-Zip or compatible tools (WinRAR, PeaZip, Keka on Mac).
Note on Windows' built-in ZIP: Windows Explorer can create ZIP files natively, but it does not support password protection or encryption. You must use 7-Zip or a similar tool. See our complete guide to password protecting ZIP files for detailed instructions.
Pros
- Free and open source — works on any Windows edition including Home
- AES-256 encryption (the strongest widely available standard)
- "Encrypt file names" option hides the contents list, not just the file data
- Cross-platform: recipients on Windows, Mac, or Linux can open the archive
- Bundles multiple files and folders into one deliverable
Cons
- Requires installing 7-Zip (Windows Explorer cannot create encrypted archives)
- No tracking, no revocation, no watermarking
- You must share the password through a separate channel
- The recipient gets a full copy of all files — you cannot control what happens next
Best for
Cross-platform file delivery when the recipient specifically requests an encrypted archive and you accept the loss of control after sharing.
Method 5 — Peony (Secure Sharing With Tracking and Revocation)
The four methods above all protect files at rest on your Windows PC. They are solid for local security. But the moment you share a file — attach it in Outlook, drop it in Teams, upload it to a shared OneDrive folder — the protection model breaks.
Even OneDrive and SharePoint, which many Windows users rely on for sharing, fall short: you can restrict access to specific Microsoft accounts, but you get no per-viewer analytics (who actually opened the file versus who just received the link), no dynamic watermarking, no screenshot protection, and revoking access means manually removing permissions per file. There is no way to know if someone forwarded the link or downloaded and re-shared the file.
I built Peony to solve this exact gap. Think of it as your sharing perimeter: your Windows PC handles local encryption, and Peony handles everything that leaves your PC.
Honest note: Peony is a secure data room, not a local Windows encryption tool. It does not replace BitLocker or EFS. It replaces the part where you attach raw files to Outlook emails and hope nobody forwards them.
How to share files securely from your Windows PC with Peony
- Create a room in Peony — name it by context ("Series A Fundraise", "Client — Project Alpha", "HR Confidential").
- Upload files from your PC (PDFs, Excel, Word, PowerPoint, images, 7z archives — any format).
- Set access controls:
- Identity-bound access: only specific email addresses or domains can view
- Password gating: add a passcode on top of identity verification
- NDA gate: require a signed NDA before any document is visible
- Link expiry: access automatically ends after a deadline
- Screenshot protection: blocks and logs screenshot attempts (including Print Screen and snipping tools)
- Dynamic watermarks: the viewer's identity is stamped into every rendered frame
- Share one link via Outlook, Teams, Slack, or any channel. Recipients verify their identity and enter the passcode to view.
- Monitor access: page-level analytics show exactly who viewed each file, how long they spent on every page, and whether they returned.
- Revoke instantly: one click to shut down access for a specific viewer or the entire room.
If you update a file, replace it in Peony behind the same link. No more "Q1_Financials_v7_FINAL_realfinal.xlsx" in email threads.
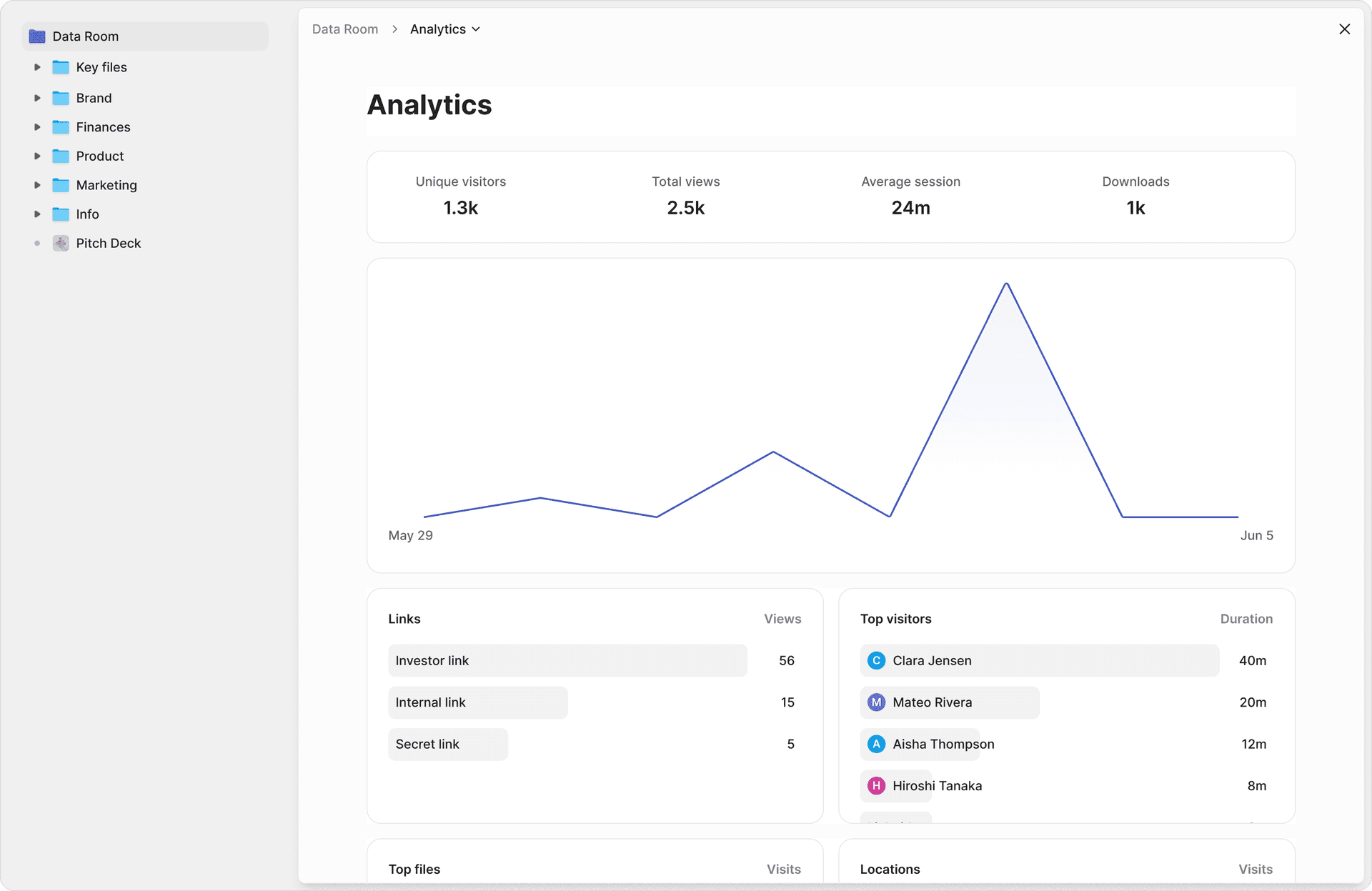
What I actually see when someone views my files
This changed everything about how I share documents from my Windows PC. After uploading a board deck through Peony, I can see:
- Which board member opened it, and when
- How long they spent on each page (the strategic plan got 6 minutes, the appendix got 8 seconds — that tells me something)
- Whether they came back for a second review before the meeting
- Whether anyone attempted a screenshot (blocked and logged)
Before Peony, I was emailing encrypted Excel files from Outlook with the password in a separate Teams message. I had no idea who actually read the materials, who forwarded them, or whether anyone even opened the attachment before the meeting.
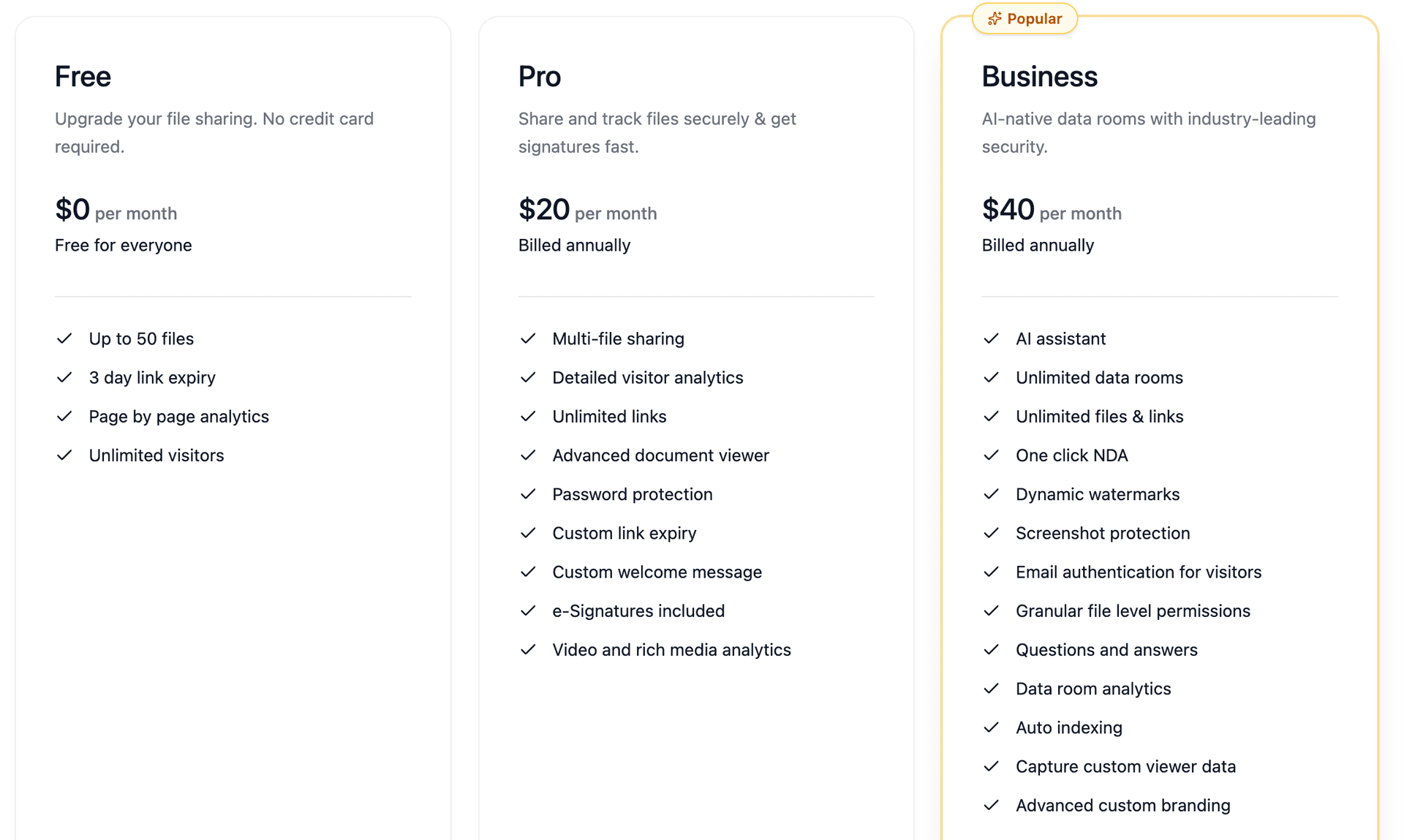
Pricing
Peony has a free tier that covers most individual workflows. Pro is $20/month, Business is $40/month. Compare that to the cost of discovering three months later that your confidential financial model was forwarded to an unauthorized third party.
Pros
- Free tier available — works on any Windows edition through the browser
- Identity-bound access — no password sharing needed
- Page-level analytics — per-viewer, per-page engagement data
- Screenshot protection — blocks Print Screen, Snipping Tool, and third-party capture tools, logs attempts
- Dynamic watermarks — viewer identity in every frame
- One-click revocation — instant access cutoff
- AI auto-indexing — organizes uploaded documents in under 3 minutes
- E-signatures built in with AI field detection
- Advanced Q&A workflow — counterparties submit questions, AI drafts answers, your team reviews before sending
- No Windows software to install — runs entirely in the browser
Cons
- Requires an internet connection (cloud-based sharing platform)
- Not a local encryption tool — does not replace BitLocker or EFS for at-rest protection
- File viewers see documents in Peony's secure viewer, not their native Windows app
Best for
Any file that leaves your Windows PC: investor decks, M&A documents, client deliverables, due diligence files, HR documents, real estate transaction files, LP reports, or anything where you need to know who accessed it and retain the ability to cut off access.
Method Comparison
| Feature | BitLocker | EFS | Office Encryption | 7-Zip | Peony |
|---|---|---|---|---|---|
| Cost | Free (Pro/Enterprise) | Free (Pro/Enterprise) | Free with Office | Free | Free |
| Encryption | AES-128/256 XTS | AES-256 | AES-256 | AES-256 | AES-256 + TLS 1.3 |
| Scope | Full disk | Files/folders | Office files only | File bundles | Shared files |
| Windows Home support | Device Encryption only | No | Yes | Yes | Yes (browser) |
| Per-viewer tracking | No | No | No | No | Yes |
| Access revocation | No | No | No | No | Yes |
| Dynamic watermarks | No | No | No | No | Yes |
| Screenshot protection | No | No | No | No | Yes |
| Works offline | Yes | Yes | Yes | Yes | No |
| Protects after sharing | No | No | No | No | Yes |
Bottom line: For local file protection on Windows, BitLocker plus EFS covers most scenarios — and they ship free with Pro/Enterprise. For Windows Home users, 7-Zip and Office encryption handle the basics. For files you share with anyone outside your PC, Peony is the only method here that gives you tracking, revocation, watermarking, and screenshot protection. The free tier handles most individual workflows.
By the Numbers
- 72%+ of desktop PCs worldwide run Windows, making it the most-targeted operating system for data theft (StatCounter GlobalStats, 2025)
- ~60% of data breaches involve the human element — weak passwords, misdelivery, bad access settings, credential theft (Verizon 2025 DBIR, analyzing 22,052 incidents across 139 countries)
- 15 characters minimum — NIST SP 800-63B Revision 4 (August 2025) now mandates this for single-factor passwords, up from the old 8-character minimum (NIST SP 800-63B-4)
- $4.67 million — average cost of a breach involving stolen or compromised credentials (IBM Cost of a Data Breach 2025)
- 241 days — average time to identify and contain a data breach; organizations using AI and automation cut this by 80 days (IBM 2025)
- 1 in 10 sensitive files is exposed to every employee in the average organization — 157,000 exposed records per company (Varonis 2025 State of Data Security Report)
- AES-256 in XTS mode — the encryption standard available in BitLocker via Group Policy, recommended by NIST for disk encryption (Microsoft BitLocker documentation)
- 22% of breaches start with stolen credentials as the initial access vector (Verizon 2025 DBIR)
Practical Tips
A few habits that put you ahead of most Windows users on security:
-
Stop attaching files to Outlook emails. This is the single biggest behavior change you can make. Every raw attachment you send is a file you can never take back — no tracking, no revocation, no idea who forwarded it. Instead, upload the file to Peony and share the link. You keep version control, access control, and full analytics. The recipient gets a clean viewing experience instead of a 25MB attachment that bounces.
-
Always enable BitLocker (or Device Encryption on Home). Microsoft strongly recommends BitLocker on every PC with sensitive data. On modern SSDs with hardware AES, the performance impact is negligible.
-
Back up your BitLocker recovery key AND your EFS certificate. Store recovery keys in your Microsoft account or a password manager — not on the same drive they protect. Export your EFS certificate immediately after enabling it. Without these backups, a Windows reinstall means permanent data loss.
-
Use long passphrases, not short clever passwords. NIST SP 800-63B-4 now mandates 15+ characters for single-factor authentication and explicitly says composition rules (uppercase, number, symbol) are no longer required. Use a password manager.
-
Never send file and password in the same channel. If you use Office encryption or 7-Zip, email the file but send the password over a different medium (SMS, phone call, Signal). Better yet, use Peony's identity-bound access so no password sharing is needed.
-
Separate "local safety" and "sharing safety" in your mind.
- Local: BitLocker + EFS protect you if your PC or drive disappears.
- Sharing: Peony rooms (with password gating, identity verification, and revocation) protect you when files leave your PC.
-
Encrypt USB drives with BitLocker To Go. If you must transfer files on a USB stick, right-click the drive in File Explorer and select "Turn on BitLocker." This encrypts the entire drive with a password.
Bottom Line
| Situation | What to do |
|---|---|
| Baseline PC security | Turn on BitLocker (Pro/Enterprise) or Device Encryption (Home) |
| Sensitive local files on shared PCs | Enable EFS on specific folders (Pro/Enterprise only) |
| Quick single-document protection | Use Office built-in encryption (AES-256) |
| Cross-platform file delivery | Use 7-Zip with AES-256 encryption (avoid unencrypted ZIPs) |
| Any file you share externally | Use Peony — the only method with tracking, revocation, and watermarking (free tier available) |
| Investor decks and deal rooms | Use Peony data rooms with NDA gating, analytics, and AI auto-indexing |
You do not need to be a sysadmin to do this well. BitLocker for your disk, EFS for your most sensitive folders, and Peony for anything that leaves your PC. That is the whole system.
Frequently Asked Questions
How do you password protect files on Windows?
Windows has four built-in methods: BitLocker for full-disk encryption (Pro and Enterprise editions), EFS for file-level encryption, Microsoft Office built-in encryption for Word, Excel, and PowerPoint files, and 7-Zip for AES-256 encrypted archives. For files you share externally, Peony adds identity-bound access, password gating, page-level analytics, dynamic watermarks, and one-click revocation starting free.
Does Windows Home have file encryption?
Windows 11 Home includes Device Encryption on supported hardware (requires TPM 2.0 and UEFI Secure Boot), which encrypts the entire drive but does not offer the granular controls of BitLocker. Windows Home does not include EFS for file-level encryption. For password protecting individual files on Windows Home, use 7-Zip with AES-256 encryption or Microsoft Office built-in encryption. For secure sharing with tracking and revocation, Peony works on any Windows edition through the browser.
What encryption does BitLocker use?
BitLocker uses AES-128 or AES-256 encryption in XTS mode on internal drives and CBC mode on removable drives. Windows 11 defaults to AES-128 in XTS mode, but you can configure AES-256 via Group Policy. XTS mode is specifically designed for disk encryption and is recommended by NIST. Peony uses AES-256 encryption for documents at rest and TLS 1.3 in transit for anything you share from your Windows PC.
Can you see who opened a password-protected file on Windows?
No. BitLocker, EFS, Office encryption, and 7-Zip archives all provide zero visibility after sharing. Once you email the file and share the password, you cannot see who opened it, when they opened it, or whether they forwarded it. Peony provides page-level analytics showing exactly who accessed each file, how long they viewed every page, and whether they attempted screenshots.
How do I encrypt a USB drive on Windows?
Right-click the USB drive in File Explorer and select "Turn on BitLocker" (Windows Pro, Enterprise, and Education). Set a password, save the recovery key, and BitLocker To Go encrypts the entire drive. On Windows Home, BitLocker To Go is not available so you must use 7-Zip to create an AES-256 encrypted archive on the drive instead. For sharing files without a physical handoff, Peony lets you share a secure link with AI auto-indexing that organizes documents in under 3 minutes, so recipients access files instantly without needing a USB drive.
How do you password protect a folder on Windows?
On Windows Pro and Enterprise, right-click the folder, select Properties, click Advanced, and check "Encrypt contents to secure data." This uses EFS, which ties encryption to your Windows user account. On Windows Home, EFS is not available so you must use 7-Zip to create an AES-256 encrypted archive of the folder. For sharing folders externally, Peony lets you upload an entire folder to a secure data room with NDA gating before access, dynamic watermarks with the viewer's name in every frame, and AI auto-indexing that sorts documents into standard categories in under 3 minutes.
What is the most secure way to share files from Windows?
The most secure approach layers multiple controls: identity-verified access, password gating, dynamic watermarking with the viewer's name in every frame, screenshot blocking that logs attempts, link expiration, and instant revocation. Peony combines all six starting free and works on any Windows edition through the browser, so you never have to email raw attachments from Outlook.
Is BitLocker enough to protect my files?
BitLocker protects files at rest on your drive. If your laptop is lost or stolen, BitLocker prevents unauthorized access to the disk. But BitLocker does nothing after you share a file. Once you email an attachment or upload to a shared drive, BitLocker's protection ends. For files that leave your PC, Peony adds the controls BitLocker cannot: identity-bound access, page-level analytics, dynamic watermarks, screenshot protection, and instant access revocation.
Related Resources
- How to Password Protect Files on Mac (5 Ways)
- How to Password Protect Excel Files
- How to Password Protect PowerPoint
- How to Password Protect ZIP Files
- How to Password Protect PDF Without Adobe
- Secure File Sharing Guide
- How to Password Protect Multiple PDFs at Once
- How to Password Protect a Video (7 Methods)
- Password Protect CSV Files
- Virtual Data Room Guide
You might also like
Mar 26, 2026
How to Password Protect Files on Mac (5 Ways — 1 Tracks Access) in 2026
Apr 23, 2026
How to Set Different Passwords for Different Investors in 2026
Apr 1, 2026
How to Send a Password-Protected PDF (6 Methods, 1 Tracks Opens) in 2026
