How to Send a Password-Protected PDF (6 Methods, 1 Tracks Opens) in 2026

Co-founder at Peony — I built the data room platform, with a background in document security, file systems, and AI.
Connect with me on LinkedIn! I want to help you :)Last updated: April 2026
TL;DR — You can password protect a PDF for free with Adobe Acrobat, Mac Preview, LibreOffice, or Microsoft Word. But a password only controls who can open the file — it cannot stop forwarding, screenshots, or tell you whether anyone actually read it. Verizon's 2025 DBIR reports that 60-68% of breaches still involve a human element like misdirected emails and bad access settings. If your PDF contains anything sensitive, a password is the floor, not the ceiling.
I run Peony — an AI-powered data room for secure document sharing. I have seen thousands of "password protected" PDFs come through investor data rooms, M&A deals, and client onboarding workflows. Most of them share two traits: the password was in the same email thread, and nobody had any idea whether the recipient actually opened the file.
Here is a pattern I see constantly: a founder sends a pitch deck as a password-protected PDF to fifteen investors. The password goes in a follow-up email. Three investors forward the deck to associates. Two associates forward it to colleagues at other firms. Within a week, the deck is sitting in forty inboxes — and the founder has no idea. The "password protection" lasted exactly as long as the first forward.
This does not mean password-protecting your PDF is pointless. It means you should understand what each method actually protects, what it does not protect, and when you need something stronger.
This guide covers six methods for sending a password-protected PDF, starting with free tools you already have. I will be honest about the trade-offs so you can pick the right one for your situation.
Quick Comparison: 6 Methods at a Glance
| Method | Cost | Encryption | Tracks Opens | Revoke Access | Best For |
|---|---|---|---|---|---|
| Adobe Acrobat | Free (online) / $22.99/mo (Pro) | AES-256 | No | No | Industry-standard PDF encryption |
| Mac Preview | Free (built-in) | AES-128 | No | No | Quick protection on macOS |
| Microsoft Word | Microsoft 365 sub | AES-256 | No | No | Office-first workflows |
| LibreOffice | Free (open source) | AES-256 | No | No | Free cross-platform option |
| Online tools | Free / freemium | Varies | No | No | One-off, low-stakes files |
| Peony | Free / Pro $20/mo | AES-256 + TLS 1.3 | Per-viewer, per-page | Yes | Confidential PDFs you need to track |
Before You Start: Encryption Basics
Every method in this guide uses some form of AES (Advanced Encryption Standard) to protect your PDF. Here is what you need to know:
- AES-128 uses a 128-bit key with 10 rounds of encryption. Compatible with Acrobat Reader 5.0 and above. Secure against all known attacks today.
- AES-256 uses a 256-bit key with 14 rounds. Requires Adobe Reader 9.0 or later. Recommended for sensitive documents because it provides stronger resistance to future quantum computing attacks. NIST considers AES-256 sufficient for protecting classified information up to TOP SECRET level.
- Open password vs. permissions password — An open password prevents anyone from viewing the document without the key. A permissions password restricts actions (printing, copying, editing) but does not prevent opening. Permissions-only passwords are trivially stripped by free tools and should never be relied on as a security measure.
If your recipient is using any PDF reader released after 2009, use AES-256. There is no compatibility reason to choose AES-128 anymore unless you know for certain your recipient is on very old software.
One more thing: 40-bit RC4 encryption still exists as an option in some older tools. Never use it. RC4-40 was crackable by consumer hardware in the early 2000s and offers effectively zero protection today. If your tool does not offer at least AES-128, find a different tool.
Method 1: Adobe Acrobat
Adobe Acrobat is the industry standard for PDF encryption. You have two paths depending on whether you pay for Acrobat Pro.
Acrobat Pro (desktop)
- Open your PDF in Acrobat Pro
- Go to All Tools, then Protect a PDF
- Select Encrypt with Password
- Choose Require a password to open the document
- Enter a strong password (12 or more characters — length beats complexity)
- Under Encryption, select AES-256 if available
- Click OK, then save the file
Acrobat Pro also lets you set a separate permissions password that restricts printing, copying, and editing without blocking the document from opening. Be aware that permissions-only passwords are trivially removed with free tools — they are a speed bump, not a wall.
Password tip: NIST's current guidance favors length over complexity. A 16-character passphrase like "correct-horse-battery-staple" is stronger and easier to communicate than "P@ssw0rd!23". Avoid dictionary words on their own, sequential numbers, and anything that appears in known breach databases.
Acrobat Online (free)
- Go to the Acrobat Online password protection tool
- Upload your PDF (the file is processed on Adobe's servers)
- Enter and confirm a password
- Download the encrypted file
The online tool is free and works in any browser, but it uploads your unencrypted document to Adobe's cloud. For highly sensitive files, use the desktop version.
Sending the encrypted PDF
Attach the file to an email as you normally would. Gmail allows attachments up to 25 MB; Outlook allows up to 20 MB. Base64 encoding in transit inflates file size by roughly 33%, so keep your actual file under 15-19 MB.
Send the password through a separate channel — a text message, a phone call, or an encrypted messaging app. Never in the same email thread. This sounds obvious, but I see it violated constantly. The most common pattern: the password is in the very next sentence after "please find attached." If someone gains access to the email, they have both the lock and the key.
Verify before sending — open the encrypted PDF yourself in a different reader (Chrome's built-in viewer, Adobe Reader, Preview) to confirm the password prompt appears. I have seen cases where the encryption silently failed and the file opened without any prompt.
What Acrobat does not do
- No tracking — you cannot tell if the recipient opened the file
- No revocation — once they have the file, you cannot take it back
- No forwarding protection — the recipient can send the file and password to anyone
- No screenshot deterrence — the content renders on screen like any normal document
Method 2: Mac Preview
Every Mac ships with Preview, which can encrypt PDFs without installing anything.
- Open the PDF in Preview
- Go to File, then Export
- Click the Permissions button
- Check Require password to open document
- Enter and confirm your password
- Click Apply, then Save
Preview uses 128-bit AES encryption. This is solid for most use cases but one step below the AES-256 that Acrobat and LibreOffice offer. Preview also does not support setting separate open and permissions passwords — it is all or nothing.
You can also set permissions to restrict printing, copying text, and annotating from the same Permissions dialog. However, as noted above, permissions-only restrictions are easily removed and should not be relied on.
Tip for macOS Sequoia and later: The Preview export dialog may look slightly different depending on your macOS version. If you do not see the Permissions button immediately, make sure the format dropdown is set to PDF before looking for it.
For a deeper walkthrough of every Mac file protection method, see our password protect files on Mac guide.
Limitations
Same as Acrobat: no tracking, no revocation, no forwarding protection, and passwords can be shared freely. Preview's 128-bit AES is secure today but AES-256 is preferred for documents with a long confidentiality window.
Method 3: Microsoft Word
If you already have Microsoft 365, Word can export encrypted PDFs.
- Open or create your document in Word
- Go to File, then Export, then Create PDF/XPS
- Click Options and check Encrypt the document with a password
- Enter and confirm your password
- Click OK, then Publish
Word uses AES-256 encryption, matching Acrobat Pro. The workflow is convenient if your source document is already in Word format.
Mac users: The process is slightly different. Go to File, then Save As, choose PDF from the format dropdown, click More Options, then Security Options, and check Require a password to open the document.
For Windows-specific methods covering BitLocker, EFS, and 7-Zip alongside Office encryption, see our password protect files on Windows guide.
Limitations
The same fundamental constraints apply: no open tracking, no access revocation, no forwarding control. You also need an active Microsoft 365 subscription. The free web version of Word does not support PDF encryption.
Method 4: LibreOffice
LibreOffice is free, open-source, and runs on Windows, Mac, and Linux. It supports AES-256 PDF encryption.
- Open your document in LibreOffice Writer (or open a PDF in LibreOffice Draw)
- Go to File, then Export as PDF
- In the PDF Options dialog, click the Security tab
- Click Set Open Password and enter your password
- Optionally set a permissions password to restrict printing and copying
- Click Export to save the password-protected PDF
LibreOffice is the strongest free option for PDF encryption. AES-256, separate open and permissions passwords, and no subscription required. If you are on Linux or prefer open-source software, this is your best path.
Limitations
The same as every local encryption method: zero visibility after sending, zero revocation capability, and the recipient can share the password freely. LibreOffice's PDF rendering also occasionally introduces minor formatting differences compared to the original document, so double-check the exported file before sending.
Method 5: Online Tools
Browser-based tools like iLovePDF and SmallPDF can add a password to a PDF without installing software. The process is similar across all of them: upload your file, set a password, download the encrypted version.
Privacy warning
Your unencrypted PDF is uploaded to their servers during processing. Read the privacy policy before using these tools with sensitive documents. Most free tiers retain files temporarily (typically 1-2 hours), and their security practices vary. Some process files entirely in the browser using WebAssembly, but many do not.
When online tools make sense
- Low-stakes documents (event invitations, non-confidential reports)
- One-off situations where you cannot install software
- Files that contain no personal data, financial information, or trade secrets
When to avoid them
- Investor materials, contracts, or legal documents
- Anything covered by GDPR, HIPAA, or SOC 2 compliance requirements
- Internal strategy documents, board materials, or cap tables
For a broader look at how email encryption and secure sending methods compare, see our guide to sending confidential documents via email.
A note on all five methods above: every one of them produces a file — a static artifact that leaves your control the moment you hit send. That file can be copied, forwarded, uploaded to a shared drive, or stored indefinitely on someone else's machine. The encryption only protects the file until the password is entered. After that, you are trusting the recipient completely.
There is also a practical headache that most guides ignore: password fatigue. If you password-protect every PDF you send, you are managing a growing list of unique passwords across dozens of recipients. Reusing passwords is insecure. Using the same password for all files is worse. And every recipient has to store or remember their password somewhere — which is rarely secure on their end either.
This is the fundamental trade-off. Local encryption is free, fast, and universally compatible. It is also blind, permanent, and unrevocable. Method 6 exists because some documents deserve better.
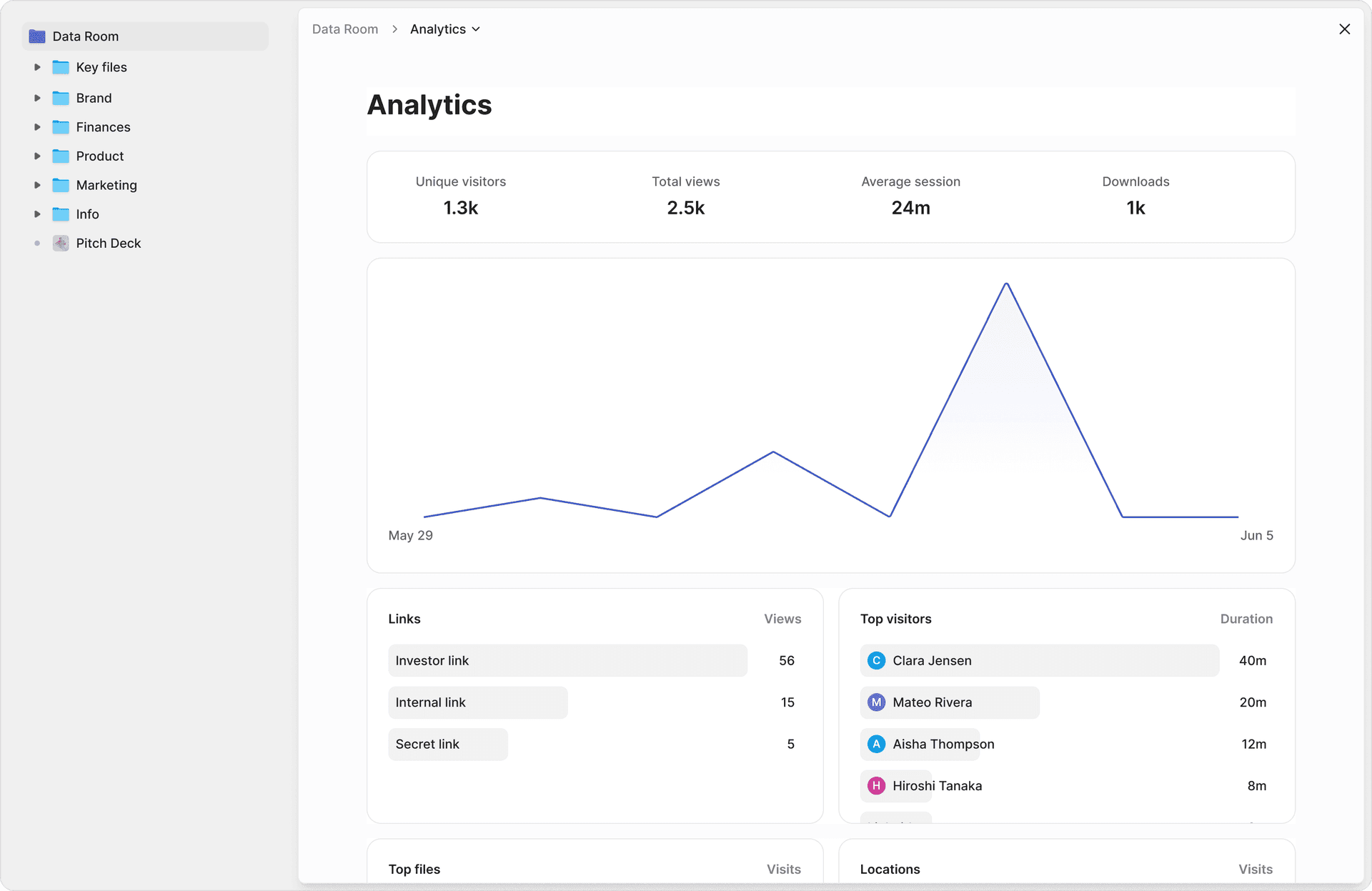
Method 6: Peony
The five methods above all share the same gap: once the recipient has the file and the password, you lose all control and all visibility. You do not know if they opened it, how much they read, or whether they forwarded it to someone else.
Peony takes a different approach. Instead of encrypting a file and hoping for the best, you upload the PDF and share a secure link. The document never leaves your control.
How it works
- Upload your PDF to a Peony data room — drag and drop, done in seconds
- Set access controls — password protection, email-verified identity, NDA gates before viewing, or all three layered together
- Share the link via email, Slack, or any channel — no attachment, no file to forward
- Track engagement — page-level analytics show who opened the document, which pages they read, and how long they spent on each page
- Revoke access at any time — one click disables the link, even after the recipient has viewed the document
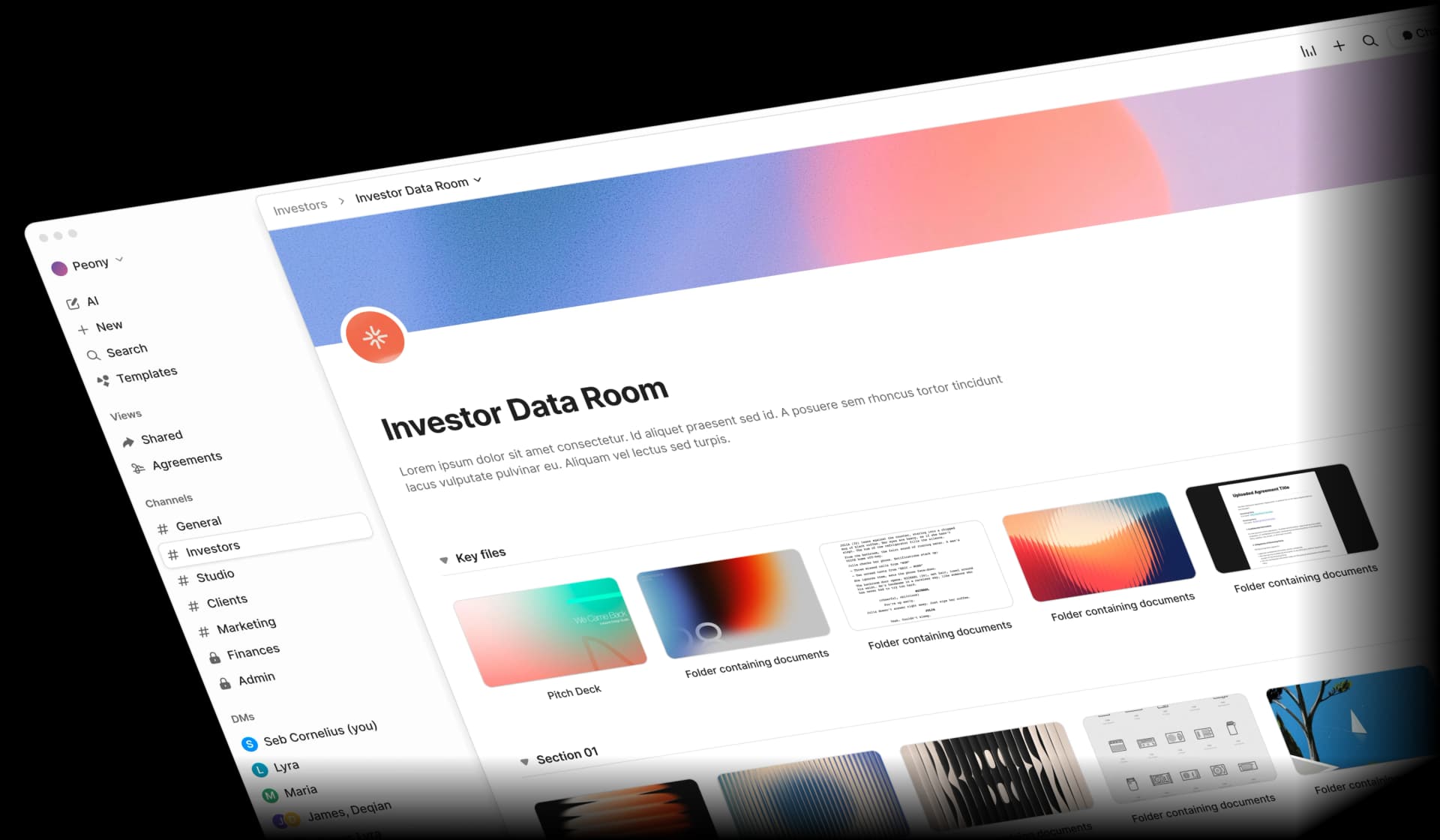
What makes this different from a password-protected PDF
- No password to share — recipients verify via email. No "what's the password?" messages cluttering your inbox
- Screenshot protection — blocks and logs capture attempts instead of hoping nobody takes one
- Dynamic watermarks — the viewer's identity is baked into every rendered frame, making leaks traceable
- Version control — update the PDF without changing the link. Recipients always see the latest version
- AI-powered features — auto-indexing in under 3 minutes, AI document extraction that answers natural-language questions across your files, and smart Q&A workflows for counterparty questions
- E-signatures — built-in, not a separate tool
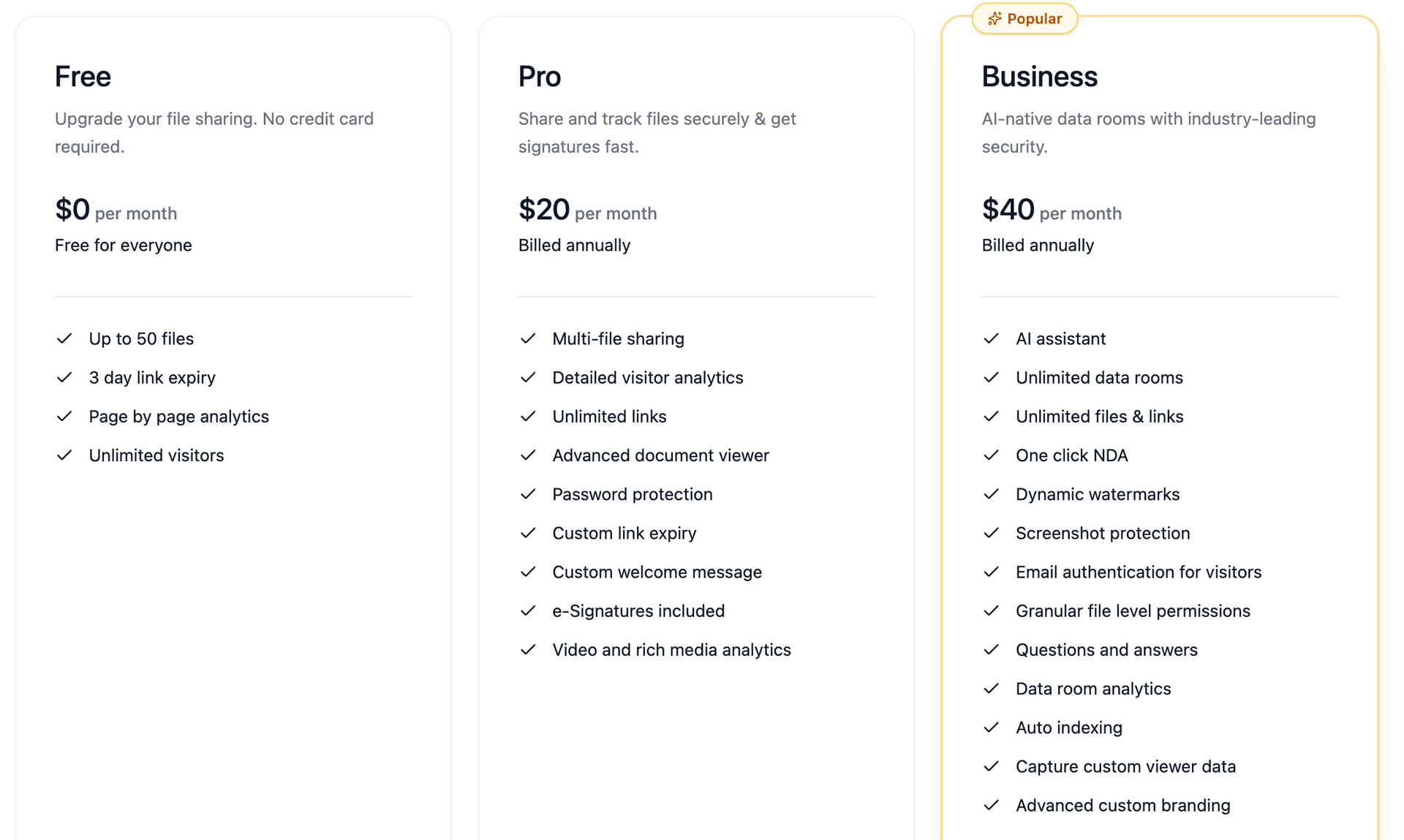
Pricing
Peony starts free with full security features. Pro is $20/admin/month for advanced analytics and custom branding. Business is $40/admin/month for team workflows and priority support. Compare that to Acrobat Pro at $22.99/month — which still gives you zero open tracking.
For fundraising workflows, see how founders use Peony data rooms in our data room for investors guide. For M&A due diligence, our how to set up a data room guide covers the full process. For a side-by-side look at secure sharing platforms, see our top 10 secure file sharing tools comparison.
When Peony is overkill
If you are sending a low-stakes PDF to a single person and do not care whether they read it, a free encryption method from the list above is perfectly fine. Peony is designed for situations where the document matters — investor materials, legal contracts, board reports, M&A due diligence — and where knowing what happens after you share is as important as controlling who can open the file.
The Password Problem: Why Encryption Alone Is Not Enough
Password-protecting a PDF solves one problem — unauthorized opening — and ignores everything else. Here is what a password cannot do:
Forwarding
The recipient can email the file and password to anyone. You will never know. An NDA offers some legal recourse, but zero prevention. In fundraising contexts, pitch decks routinely get passed between investors without the founder's knowledge. In M&A contexts, confidential information memoranda circulate to parties who were never approved to see them.
Screenshots and copy-paste
Once a PDF is open, every operating system allows screenshots. Permissions passwords that disable copying are removed in seconds with free tools. There is no technical barrier. Even if you set permissions to block printing and copying in Adobe Acrobat, a Google search for "remove PDF permissions password" returns dozens of free tools that strip these restrictions in seconds.
No open tracking
You have no idea whether the recipient opened the file, skimmed the first page, or read every word. For investor decks and sales proposals, this is the difference between following up intelligently and guessing. "Did you get a chance to look at the deck?" is a question you should never have to ask.
No revocation
Email attachments cannot be recalled reliably. Gmail and Outlook recall features only work under narrow conditions — same organization, unread, short time window. Once the file is downloaded, it is gone. If a deal falls through or an employee leaves a partner firm, you have no way to cut off their access to the documents you already sent.
Password management overhead
Every password-protected PDF creates a small operational burden: generating a unique password, sending it through a separate channel, dealing with "I forgot the password" messages, and hoping nobody wrote it on a sticky note.
If you are sending one PDF to one person once, this overhead is tolerable. If you are sharing a pitch deck with fifteen investors, a due diligence package with four law firms, or quarterly reports with your board, the password management burden scales linearly while the security value stays flat.
Stale access
A password-protected PDF you sent six months ago is still sitting in someone's email with the same password. You cannot expire it, cannot update it, and cannot know whether it has been forwarded since. For files with time-limited sensitivity — term sheets, draft financials, board materials — this is a real liability.
This is why professional workflows — M&A due diligence, fundraising, legal document exchange — have moved from encrypted attachments to secure link-based sharing with identity verification and audit trails.
By the Numbers
- 60-68% of data breaches involve a human element such as misdirected emails and misconfigured access settings — Verizon 2025 DBIR
- 25 MB — Gmail's attachment limit. Outlook caps at 20 MB. Base64 encoding means your practical file limit is roughly 15-19 MB
- AES-256 — the encryption standard recommended by NIST for sensitive documents, used by Acrobat Pro, LibreOffice, Microsoft Word, and Peony
- AES-128 — used by Mac Preview. Secure today, but AES-256 is preferred for documents with long confidentiality requirements
- 0 seconds — how long it takes to remove a permissions-only PDF password with free online tools. Open passwords with strong encryption remain secure
- $22.99/mo — Adobe Acrobat Pro subscription cost. Mac Preview, LibreOffice, and Microsoft Word all create encrypted PDFs without an additional subscription
- Under 5 minutes — time to upload a PDF to Peony, set access controls, and share a secure link with tracking and revocation
Which Method Should You Use?
Sending a recipe PDF to a friend — any free method works. Mac Preview takes 30 seconds.
Sending a tax form or insurance document — Adobe Acrobat or LibreOffice with AES-256. Strong encryption is appropriate, and the recipient expects a standard PDF workflow.
Sending a contract to a client — Adobe Acrobat or Microsoft Word with AES-256 encryption, password delivered via phone call. Adequate if you do not need to track whether they read it. If you need to know that the client actually reviewed specific sections, use Peony.
Sending a pitch deck to investors — Peony. You need to know who opened it, which pages held their attention, and whether they passed it around. Password-protected attachments are blind. This is the most common use case where founders realize a password is not enough.
Sending a proposal to a prospective client — Peony. Knowing that a prospect spent 8 minutes on your pricing page versus 10 seconds tells you exactly how to structure the follow-up conversation.
Sharing due diligence documents with acquirers — Peony. M&A workflows require audit trails, per-document access controls, version management, and instant revocation when a deal falls through. A password on a PDF covers none of this.
Sending financial reports to your board — Peony. Board members are high-value targets for social engineering. Link-based sharing with email verification and dynamic watermarks is materially more secure than an encrypted attachment.
Sending a one-page NDA for signature — Peony's built-in e-signatures handle this without a separate tool. Upload, sign, countersign, done.
Sharing compliance or regulatory documents — Peony. SOC 2, GDPR, and HIPAA all require demonstrable access controls and audit trails. A password-protected PDF with no logging does not satisfy these requirements. See our document sharing compliance guide for framework-specific details.
Sharing documents with your board — Peony. Board packs contain strategy, financials, and personnel information. Link-based sharing with email verification means you do not have to worry about former board members retaining access after they rotate off.
Bottom Line
For personal or low-stakes PDFs — Mac Preview or LibreOffice. Both are free, both encrypt properly, and both work without uploading your file to a third-party server.
For professional documents you already have in Word — Microsoft Word's PDF export with AES-256 encryption is convenient and solid.
For anything where you need to know who opened it, control forwarding, or revoke access — Peony. Password-protected PDFs are a lock on an envelope you hand to a stranger and walk away from. Peony is a locked room where you control the door, see who enters, and can change the lock at any time.
The best method depends on what happens after you hit send. If you just need basic encryption, the free tools in this guide will serve you well. If you need to actually know what happens to your document, that requires a different approach entirely.
Start with the free method that matches your operating system. When you hit the ceiling — and if you are sharing anything confidential with external parties, you will — try Peony free and see the difference that tracking and access control make.
Frequently Asked Questions
How do I password protect a PDF for free?
You can password protect a PDF for free using Mac Preview (File, Export, Permissions, 128-bit AES), LibreOffice Draw (File, Export as PDF, Security tab, AES-256), or Microsoft Word (export to PDF with encryption). All three work without installing extra software on their respective platforms. None of them tell you whether the recipient actually opened the file. Peony lets you share a PDF with password gating, email-verified identity access, and page-level analytics showing who read which pages, starting on the free plan.
Is it safe to use online PDF password tools?
Online tools like iLovePDF and SmallPDF process your file on their servers, which means your unencrypted document leaves your machine. For low-stakes files this is acceptable, but for anything confidential it is a risk. Their privacy policies vary and most free tiers retain files temporarily. Peony encrypts documents with AES-256 at rest and TLS 1.3 in transit, never exposes raw files to third-party processors, and gives you a full audit trail of every viewer interaction.
What is the difference between AES-128 and AES-256 PDF encryption?
AES-128 uses a 128-bit key with 10 encryption rounds and is compatible with Acrobat Reader 5.0 and above. AES-256 uses a 256-bit key with 14 rounds and requires Adobe Reader 9.0 or later. Both are considered secure today, but AES-256 is recommended for sensitive documents because it offers stronger resistance to future quantum computing attacks. Peony uses AES-256 encryption for all documents at rest and TLS 1.3 for data in transit.
Can I send a password-protected PDF through Gmail?
Yes. Attach the encrypted PDF to a Gmail message as you would any file, up to the 25 MB attachment limit. Send the password through a separate channel like a text message or phone call, never in the same email thread. The limitation is that once the recipient has the file and the password, they can forward both to anyone. Peony eliminates this problem entirely because you share a link instead of a file, and you can revoke access with one click at any time.
Why can someone still screenshot a password-protected PDF?
PDF password encryption only controls who can open the file. Once opened, the content renders on screen like any other document, and every operating system allows screenshots of anything on screen. Permission passwords that block printing or copying are trivially removed with free tools. Peony adds screenshot protection that blocks and logs capture attempts plus dynamic watermarks with the viewer's identity baked into every rendered frame, making leaks traceable.
What is the best way to send a confidential PDF to investors?
Upload the PDF to a secure data room like Peony, enable NDA gating and email-verified access, and share one link. Peony shows which investors opened the document, which pages they read, and how long they spent on each page. AI auto-indexes your documents in under 3 minutes so the entire deal room is ready fast. Password-protected email attachments give you zero visibility into whether anyone actually reviewed your materials.
How do I send a large password-protected PDF over email?
Gmail caps attachments at 25 MB and Outlook at 20 MB, but Base64 encoding inflates file size by roughly 33 percent in transit, so your practical limit is around 15 to 19 MB. For larger PDFs you need a cloud link. Peony handles files of any size through secure links with no attachment limits, and recipients view documents in the browser without downloading, which also means you keep control of the file.
Can I revoke access to a PDF after sending it?
Not with a traditional password-protected PDF. Once someone has the file and the password, you cannot take it back. Email recall features in Gmail and Outlook only work under narrow conditions and fail once the attachment is downloaded. Peony solves this because you share a link, not a file. You can revoke access for a specific viewer, an entire domain, or a whole data room with one click, even after the recipient has already viewed the document.
Do I need Adobe Acrobat Pro to password protect a PDF?
No. Mac Preview, LibreOffice, and Microsoft Word can all create password-protected PDFs for free. Adobe Acrobat Pro adds conveniences like separate open and permissions passwords and batch encryption, but it costs $22.99 per month. Peony takes a different approach entirely: instead of encrypting a file and hoping for the best, you upload the PDF and share a secure link with password gating, identity verification, and page-level analytics starting free.
Should I send the PDF password in the same email?
Never. Sending the password in the same email as the attachment defeats the purpose of encryption because anyone who intercepts or accesses the email gets both the lock and the key. Send the password through a separate channel such as a phone call, SMS, or encrypted messaging app. Better yet, use Peony to share a link with email-verified access so there is no password to manage, share, or lose in the first place.
Related Resources
- How to Send Confidential Documents via Email — 7 methods for secure email communication
- How to Password Protect Files on Mac — 5 methods for macOS file encryption
- How to Password Protect Files on Windows — BitLocker, EFS, Office, 7-Zip, and Peony
- How to Password Protect a Video — 7 methods for secure video sharing
- Secure File Sharing Guide — best practices for sharing sensitive files
- Virtual Data Room vs Cloud Storage — when you need more than Google Drive or Dropbox
- How to Set Up a Data Room — step-by-step data room configuration
- Data Room for Investors — the complete guide to investor data rooms
- Top 10 Secure File Sharing Tools — comparison of platforms for secure sharing
- Document Sharing Compliance Guide — SOC 2, GDPR, HIPAA, and CCPA framework requirements
You might also like
Apr 9, 2026
Best File Sharing Software for Small Business and Startups in 2026
Mar 21, 2026
How to Password Protect Google Docs (Google Won't Tell You This)
Mar 21, 2026
Password Protect 100+ PDFs at Once (6 Methods, 2 Are Free)
