How to Prevent PDF Forwarding in 2026 (7 Methods — Only 1 Tracks Who Leaked)
Co-founder and CEO at Peony. I built the data room platform with a background in document security, file systems, and AI. Founded Peony in 2021 in San Francisco.
TL;DR: You cannot make a PDF un-forwardable. But you can make unauthorized sharing painful, traceable, and operationally rare. The 7 methods below range from free-but-weak (PDF passwords) to purpose-built (secure data rooms). For M&A advisors running 3-5 concurrent deals or founders sharing pitch decks with 20+ VCs, the only method that actually tracks who leaked is a controlled viewer with identity-gated access and per-page analytics — which is exactly what Peony does.
Last updated: April 2026
I run Peony, a data room platform built for sensitive document sharing. PDF forwarding prevention is not an abstract topic for me — it is the core problem my product solves. I have tested every method on this list, from Adobe Acrobat's permission flags to enterprise DRM platforms that cost $6,000 a year.
PDF forwarding is what happens when a recipient of your document shares it — intentionally or accidentally — with someone you did not authorize. Once a PDF leaves your control as an email attachment or unprotected download, you have zero visibility into where it goes next. According to the Ponemon Institute's 2025 Cost of Insider Risks Report, 55% of insider data incidents come from simple employee negligence — forwarding a confidential file to the wrong person is exactly that kind of mistake.
Quick Guide: 7 Methods to Prevent PDF Forwarding
| # | Method | Cost | Protection Level | Tracks Views? | Best For |
|---|---|---|---|---|---|
| 1 | PDF password protection | Free | Weak | No | Low-stakes internal docs |
| 2 | Adobe Acrobat permission restrictions | $19.99/mo | Weak | No | Casual copying deterrence |
| 3 | Cloud storage link restrictions | Free–$20/mo | Medium | Basic | Team collaboration files |
| 4 | Email confidential mode | Free | Medium | No | One-off sensitive emails |
| 5 | Enterprise DRM / IRM | $500+/mo | Strong | Yes | Large enterprises with IT teams |
| 6 | Static watermarking | Free–$20/mo | Medium | No | Deterrence for printed docs |
| 7 | Secure data room with dynamic watermarking | Free–$40/mo | Strongest | Per-page | M&A, fundraising, legal |
1. PDF Password Protection
The most common method — and the weakest.
How it works:
- Open your PDF in any PDF editor (Preview on Mac, Adobe Reader, or free tools like Smallpdf)
- Set an "open password" that recipients need to view the file
- Optionally set a "permissions password" to restrict printing, copying, or editing
Pros:
- Free and built into most PDF tools
- Works without any special software on the recipient's end
- Better than sending a completely unprotected file
Cons:
- Recipients can share the password alongside the file — and they do
- Dozens of free online tools (iLovePDF, Smallpdf, PDF2Go) strip PDF passwords in seconds
- Zero visibility into who opened the file or when
- No revocation — once the password is out, it is out forever
Best for: Low-stakes internal documents where you want a basic speed bump, not real security.
2. Adobe Acrobat Permission Restrictions
Adobe Acrobat Pro ($19.99/month annual, $29.99/month monthly) lets you set granular permissions on PDFs: restrict editing, prevent copying, disable printing.
How it works:
- Open your PDF in Adobe Acrobat Pro
- Go to Tools, then Protect, then Restrict Editing
- Set a permissions password and choose what to restrict
Pros:
- Granular control over editing, copying, and printing
- Familiar workflow for most office workers
- Certificate-based encryption available for enterprise use
Cons:
- Permission flags are metadata — not true encryption. Free tools bypass them trivially
- Does nothing to prevent forwarding. The file is still a portable, shareable attachment
- No view tracking, no analytics, no revocation
- Requires recipients to have Acrobat Reader (or compatible viewer) to respect restrictions
Best for: Preventing casual copy-paste of contract text. Not a forwarding solution.
3. Cloud Storage Link Restrictions
Google Drive, OneDrive, Dropbox, and Box all support sharing links with access restrictions.
How it works:
- Upload your PDF to your cloud storage provider
- Share a link restricted to specific email addresses (not "anyone with the link")
- Set the link to "view only" — no download permission
- Add an expiration date where supported
Pros:
- Free tier available on all major platforms
- Restricts access to named individuals
- "View only" prevents easy downloading (though workarounds exist)
- Link expiration adds a time boundary
Cons:
- 54% of cloud environments have exposed resources containing sensitive data — misconfiguration is rampant
- "Anyone with the link" is the default on most platforms, and people forget to change it
- View-only is easily circumvented (print to PDF, screenshot, browser developer tools)
- Analytics are basic: "someone opened this" — not which pages they read
- No watermarking, no screenshot protection
Best for: Team collaboration on non-critical files. Not sufficient for deal documents, pitch decks, or legal drafts.
4. Email Confidential Mode
Gmail and Outlook both offer "confidential mode" features that restrict forwarding, copying, printing, and downloading of email content.
How it works:
- In Gmail: click the lock icon (confidential mode) when composing. Set an expiration date and optional SMS passcode
- In Outlook: use "Encrypt" or "Do Not Forward" under message options
Pros:
- Free and built into email clients your recipients already use
- Removes forward, copy, and print buttons from the recipient's view
- SMS passcode adds a second authentication layer (Gmail)
- Messages expire automatically
Cons:
- Only protects the email body and inline content — PDF attachments in Gmail confidential mode are still downloadable
- "Do Not Forward" in Outlook is an honor system enforced by the client — screenshots and photos defeat it instantly
- Does not work across all email clients (recipients using third-party apps may see raw content)
- Zero analytics — you do not know if the message was opened, let alone read
Best for: One-off sensitive communications where you want to signal confidentiality. Not a document protection solution.
5. Enterprise DRM / IRM
Enterprise-grade Digital Rights Management encrypts your PDF and ties access to specific user identities or devices.
How it works:
- Choose a DRM platform: Microsoft Purview Information Protection (included in Microsoft 365 E3/E5), Locklizard ($500/month), or Vitrium ($6,000/year)
- Apply a protection policy to your PDF (encrypt, restrict actions, set expiry)
- Recipients authenticate through the DRM platform to view the document
Pros:
- True encryption — not strippable metadata flags
- Microsoft Purview can prevent forwarding, copying, and printing at the OS level, plus add watermarks
- Locklizard and Vitrium offer offline viewing with device binding
- Revocation and expiry built in
- Audit trails for who accessed what
Cons:
- Microsoft Purview requires recipients to be in the Microsoft ecosystem (or use RMS-compatible viewers)
- Locklizard and Vitrium require recipients to install dedicated viewer software — a deal-breaker for external parties in M&A or fundraising
- Expensive: Locklizard at $500/month, Vitrium at $6,000/year, Microsoft 365 E5 at $57/user/month
- Complex to deploy and manage — requires IT involvement
- Overkill for most SMB and startup use cases
Best for: Large enterprises with dedicated IT teams sharing regulated documents internally. Poor fit for external deal processes where you cannot dictate what software counterparties install.
6. Static Watermarking
Adding a visible watermark (company name, "CONFIDENTIAL," or recipient name) to each page of your PDF before sharing.
How it works:
- Use Adobe Acrobat, Canva, or a free tool like iLovePDF to add text or image watermarks
- Export the watermarked PDF
- Send to the recipient
Pros:
- Free with many tools
- Creates a psychological deterrent — people think twice before sharing a document with "CONFIDENTIAL" stamped across it
- If the document leaks, the watermark identifies the source (if you customize per recipient)
Cons:
- Manually creating per-recipient watermarks is tedious and error-prone
- Static watermarks can be cropped, edited, or removed with basic PDF editing tools
- No access control — the file itself is still freely shareable
- No analytics, no revocation, no expiry
Best for: Adding a basic deterrent to printed documents or PDFs where you want a visible confidentiality signal. Combine with other methods for actual protection.
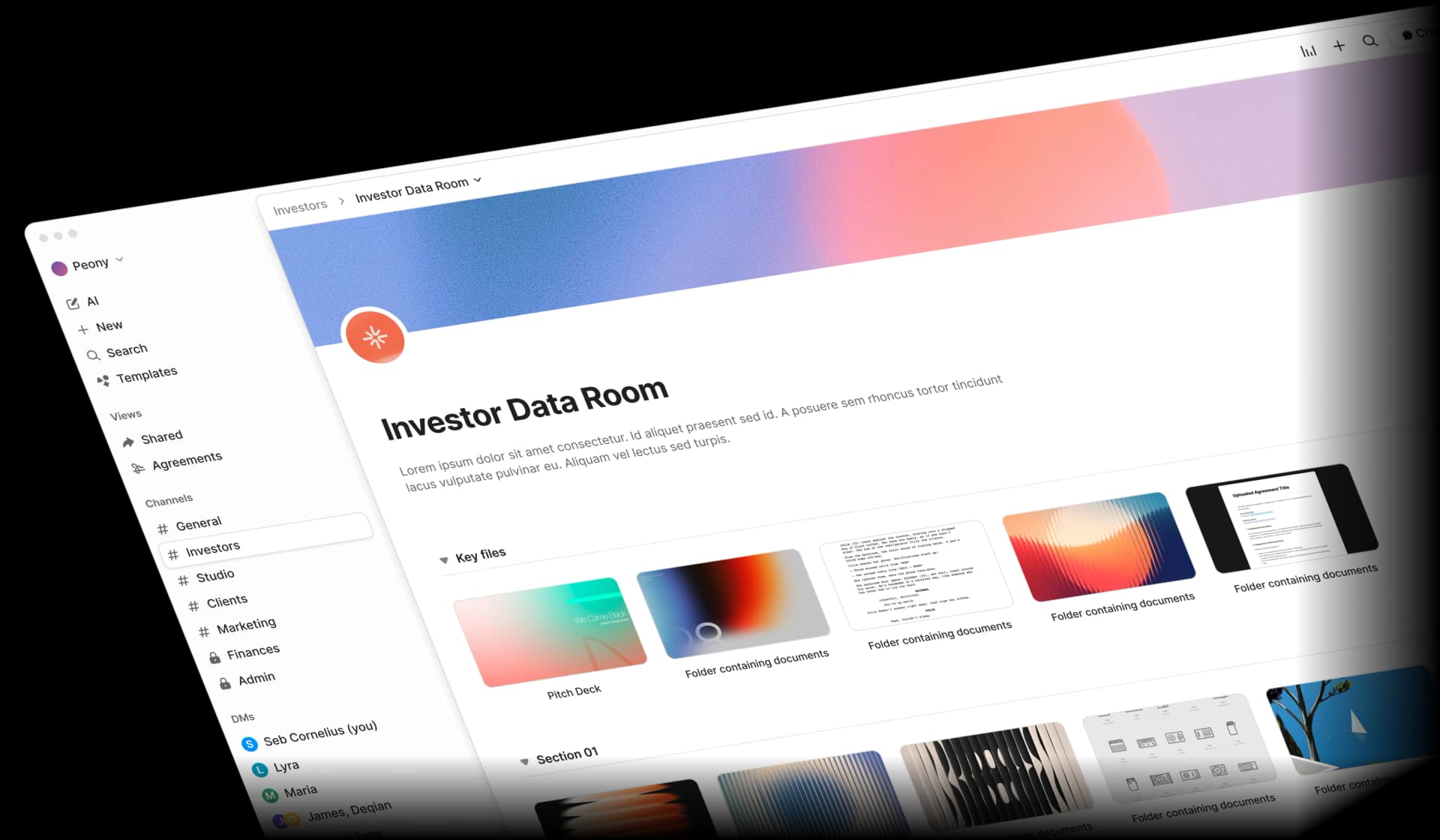
7. Secure Data Room with Dynamic Watermarking
A purpose-built document sharing platform that combines every protection layer into a single system: identity-gated access, controlled viewing, dynamic watermarking, screenshot protection, download controls, and per-page analytics.
How it works with Peony:
- Upload your PDF to a Peony data room — takes under 5 minutes
- Set access rules: restrict to specific email addresses, require NDA acceptance, enable 2FA
- Enable dynamic watermarks — each viewer sees their own email, name, and timestamp burned into every page
- Disable downloads and enable screenshot protection
- Share the link. Recipients view through Peony's controlled viewer — no software installation needed
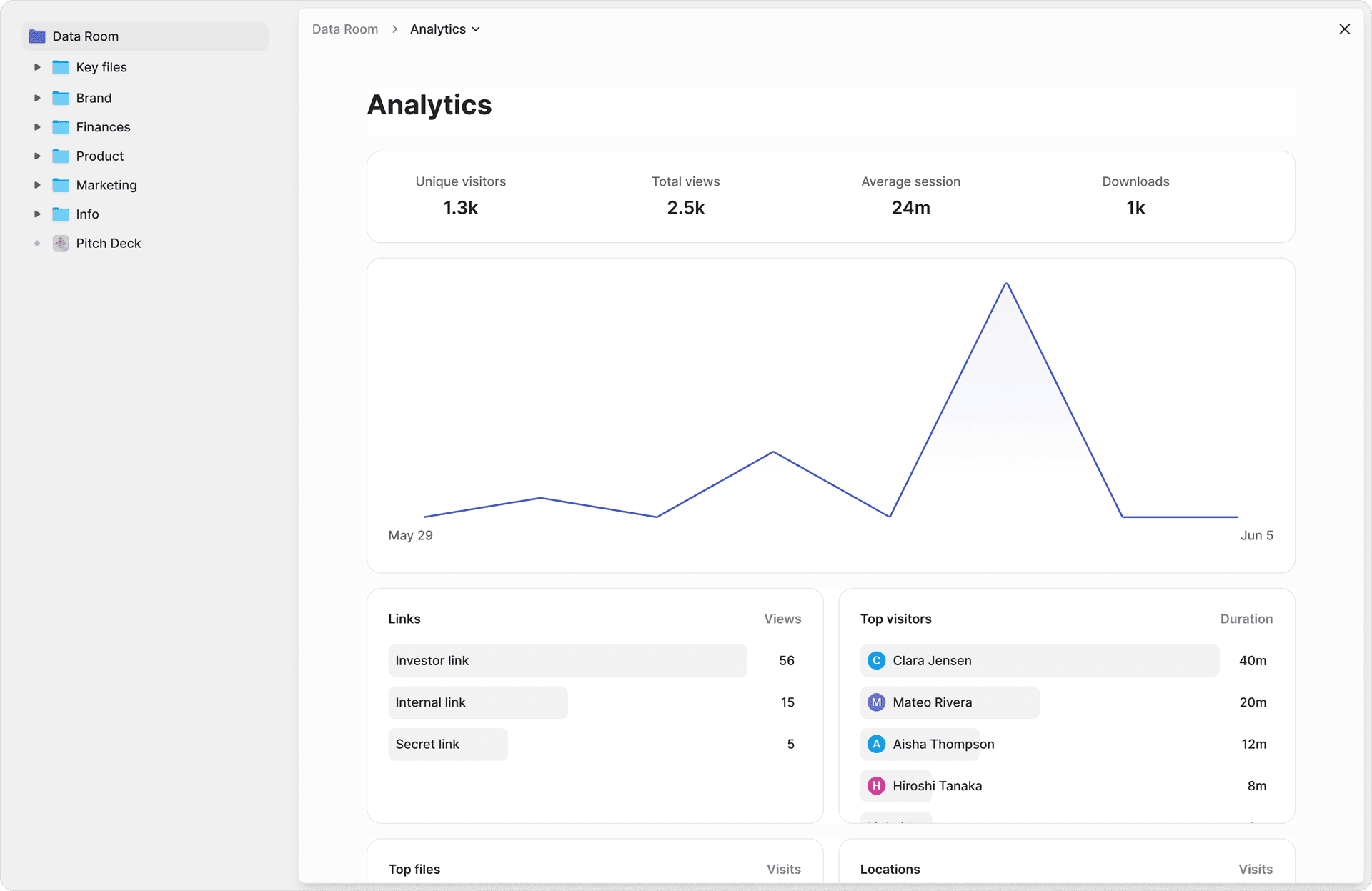
I built this workflow, so I can tell you exactly what it looks like in practice. I uploaded a 180-page CIM with financial exhibits, org charts, and legal opinions. AI auto-indexing sorted everything into deal-standard folders (financials, legal, operations) in under 3 minutes — a task that takes a junior analyst an afternoon on legacy platforms. I set up NDA gates, enabled dynamic watermarks, restricted access to 8 buyer emails, and shared the link. Total setup: 4 minutes. Within an hour, my analytics dashboard showed me that two buyers had spent 12+ minutes on the revenue projections and one had not opened the room at all. That kind of signal changes how you run a process.
Pros:
- If someone forwards the link, unauthorized viewers hit an access wall
- Dynamic watermarks are unique per viewer and per session — impossible to strip because they are rendered in real-time, not embedded as static metadata
- Screenshot protection blocks OS-level capture and logs every attempt
- Per-page analytics show exactly which pages each viewer read and for how long
- AI auto-indexing organizes uploaded documents into deal-ready folders in minutes, and AI-powered Q&A lets counterparties ask questions that your team reviews before answers are sent
- Revoke access for any individual or group instantly
- Update the document without changing the link — recipients always see the latest version
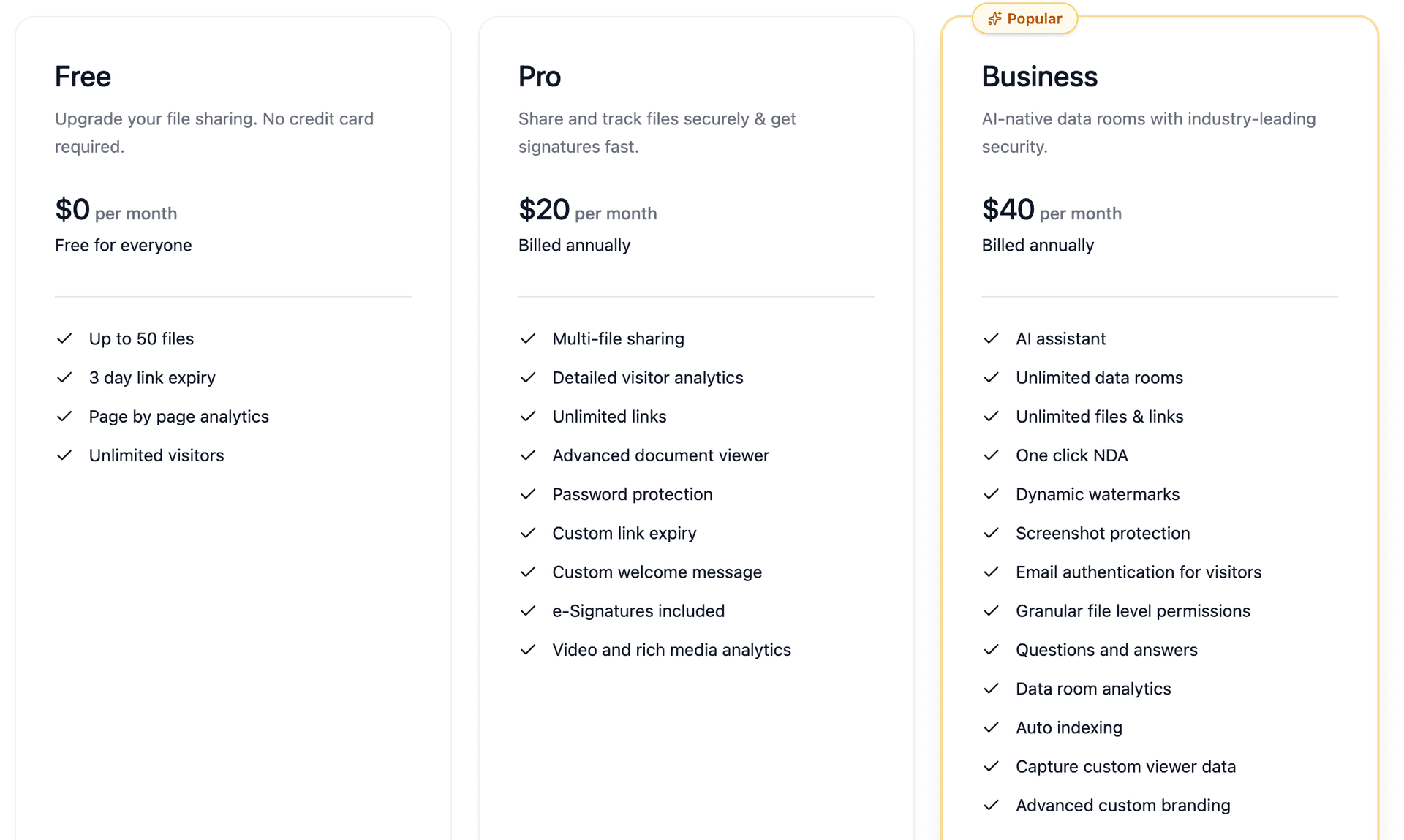
- Enterprise DRM costs $500+/month. Peony Business costs $40/admin/month — 12x less, with no software installation required on the recipient's end
Cons:
- Recipients view through a browser rather than their native PDF reader (though no app installation is needed)
- Requires an internet connection to view
Best for: M&A due diligence, fundraising pitch decks, legal document sharing, LP reports, CIMs, and any document where you need to know who saw what — and prove it.
Comparison: All 7 Methods Side by Side
| Feature | PDF Password | Adobe Permissions | Cloud Links | Email Confidential | Enterprise DRM | Static Watermark | Peony Data Room |
|---|---|---|---|---|---|---|---|
| Prevents file from being forwarded | No | No | Partially | Partially | Yes | No | Yes |
| Identity-gated access | No | No | Yes | Partially | Yes | No | Yes |
| Tracks who viewed | No | No | Basic | No | Yes | No | Per-page |
| Dynamic per-viewer watermarks | No | No | No | No | Some | No | Yes |
| Screenshot protection | No | No | No | No | Some | No | Yes |
| Revoke access after sharing | No | No | Yes | Yes | Yes | No | Yes |
| No software install for recipients | Yes | Yes | Yes | Yes | No | Yes | Yes |
| Cost | Free | $19.99/mo | Free–$20/mo | Free | $500+/mo | Free | Free–$40/mo |
By the Numbers: Why PDF Forwarding Is a $4.44 Million Problem
Here are the statistics that explain why forwarding prevention matters — all sourced and dated.
- 60% of data breaches involve some form of human action — misdirected emails, misconfigured sharing links, and credential reuse (Verizon 2025 Data Breach Investigations Report). PDF forwarding is one of the most common forms.
- $4.44 million — average global cost of a data breach in 2025 (IBM Cost of a Data Breach Report 2025). For US companies specifically, that figure hit an all-time high of $10.22 million.
- 55% of insider incidents are caused by employee negligence — sending files to the wrong person, misconfiguring sharing permissions, or forgetting to revoke access (Ponemon Institute 2025 Cost of Insider Risks).
- $19.5 million — average annual cost of insider risk per organization in 2026 (Ponemon Institute 2026 Cost of Insider Risks Global Report).
- 35% of workers have sent an email to the wrong person, and 46% have received an email clearly intended for someone else (Egress Data Loss Prevention Report).
- 83% of organizations reported data being put at risk from misdirected emails in the last 12 months (Egress).
- 32% of security incidents start with email compromise — the single largest non-intrusion vector (BakerHostetler 2026 Data Security Incident Insights Report).
- 66% of companies expose cloud data to users with anonymous link-sharing access (Varonis 2025 SaaS Risk Report). That means two-thirds of organizations have "anyone with the link" enabled somewhere sensitive.
- 54% of cloud environments have exposed virtual machines or serverless functions containing sensitive data (Techopedia 2025 Cloud Security Report). One misconfigured sharing setting is all it takes.
- $6.93 billion — the global DRM market in 2026, growing at 10.5% CAGR to $11.05 billion by 2030 (Mordor Intelligence, MarketsandMarkets). Document protection is a fast-growing category for a reason.
- 45% of file security breaches stem from insider threats — employees and contractors — costing $2.7 million per incident over two years (Ponemon 2025 State of File Security Report).
- €7.1 billion in cumulative GDPR fines since 2018, with €1.2 billion issued in 2025 alone (Kiteworks GDPR Enforcement Report 2026). Unauthorized document sharing is exactly the kind of infraction regulators penalize.
Practical Playbook: Make PDF Forwarding Useless in 5 Steps
Whether you use Peony or another tool, these principles apply:
1. Never send sensitive PDFs as email attachments. Once the file is attached, you have lost control. Share a link to a controlled viewer instead.
2. Restrict access to named individuals. No "anyone with the link." Every viewer should authenticate with their own identity — their email address, at minimum.
3. Disable downloads by default. Grant download permission as an intentional exception for specific trusted parties, not as the default.
4. Use dynamic watermarks on every sensitive document. Static "CONFIDENTIAL" stamps are better than nothing, but per-viewer watermarks (with the viewer's email, name, and timestamp) create real accountability.
5. Monitor analytics and revoke access when relationships end. Check for unusual access patterns — unexpected locations, sudden spikes, new viewers who were never invited. When a deal closes, a partnership ends, or an employee leaves, revoke access immediately.
Compliance Context: When Forwarding Prevention Is Not Optional
For certain industries, controlling document distribution is a regulatory requirement — not a best practice:
- Financial services (SEC/FINRA): Broker-dealers and investment advisors must maintain books and records of all communications, including document sharing. Unauthorized distribution of material non-public information can trigger insider trading enforcement.
- Healthcare (HIPAA): Covered entities must implement safeguards to prevent unauthorized disclosure of Protected Health Information. HIPAA penalties in 2026 range from $141 per violation to over $2.1 million per violation category.
- GDPR: Organizations that fail to control personal data sharing face fines of up to 4% of annual global revenue. TikTok was fined €530 million in May 2025 for inadequate data transfer safeguards.
Peony's audit trails, NDA gates, and per-viewer access logs help satisfy these requirements with documentation that proves who accessed what, when, and for how long.
Bottom Line
PDF forwarding prevention is not about magical file formats. It is about eliminating casual leakage paths, forcing access through controlled channels, making every view attributable, and preserving your ability to say "access ends now." For seed-stage founders sharing pitch decks with 30 VCs, mid-market M&A advisors managing 5 concurrent buyer processes, or PE fund administrators distributing quarterly LP reports — Peony gives you all four in a data room that takes under 5 minutes to set up, with Business at $40/admin/month for dynamic watermarks, screenshot protection, and AI-powered document intelligence.
FAQ
I'm sharing a confidential CIM with 10 potential buyers — can I completely prevent the PDF from being forwarded?
No tool can make forwarding mathematically impossible — a camera pointed at a screen always works. But you can make unauthorized sharing painful, traceable, and operationally rare. For a sell-side advisor distributing a 200-page CIM to 10 shortlisted buyers on a $40M deal, Peony's layered approach combines identity-gated access, disabled downloads, dynamic watermarks with the viewer's email embedded in every page, and screenshot protection that blacks out content during capture — so even if someone tries, you know exactly who did it. Google Drive's basic view tracking and Dropbox's zero per-page analytics cannot provide this level of accountability.
What is the best way to prevent PDF forwarding for M&A due diligence documents?
For M&A advisors managing 3-5 concurrent deals, the most effective approach is a purpose-built data room like Peony. Upload your CIM, financial models, and legal docs to a secure Peony room, restrict access to verified buyer emails, disable downloads, and enable dynamic watermarks. Peony's page-level analytics show you exactly which pages each counterparty reviewed and for how long — something Adobe Acrobat and email-based sharing cannot do.
How do I stop someone from forwarding a PDF sent via email?
Once a PDF is attached to an email, you cannot prevent forwarding — the recipient owns a copy of the file. The solution is to never send the PDF as an attachment. Instead, share a Peony link where the document lives in a controlled viewer. If the link gets forwarded, unauthorized viewers hit an access wall, and you see every access attempt in your analytics dashboard. For seed-stage founders sharing pitch decks with 20+ VCs, this is the difference between blind distribution and knowing exactly who opened page 7 — something Gmail's Confidential Mode and Dropbox's shared links fundamentally cannot tell you.
Does Adobe Acrobat's "restrict editing" actually prevent PDF forwarding?
No. Adobe Acrobat Pro's permission restrictions (restrict editing, copying, printing) are metadata flags that any free PDF tool can strip in seconds. They prevent casual copying but offer zero protection against forwarding — anyone can still email or upload the file. For PE fund administrators sharing LP reports with sensitive fee data, Peony's identity-gated viewer with disabled downloads and dynamic watermarks provides actual forwarding prevention, not just a suggestion.
Our law firm shares $30M-$50M deal documents with outside counsel — what is PDF DRM and is it worth the cost?
PDF DRM (Digital Rights Management) encrypts your PDF and ties it to specific users or devices. Enterprise DRM vendors like Locklizard ($500/month) and Vitrium ($6,000/year) offer strong protection but require recipients to install dedicated viewer software — which creates friction that kills deal flow when your counterparty's counsel needs access in 20 minutes, not after an IT ticket. For a 5-partner firm managing document flow on a $40M acquisition, Peony's Business plan ($40/admin/month) achieves the same outcome — identity-gated, non-downloadable, watermarked viewing — without any software installation on the recipient's end.
How do I track who forwarded my PDF to unauthorized people?
Standard email and cloud sharing tools cannot tell you who forwarded a PDF — Google Drive shows "someone viewed" and Dropbox shows a download count, but neither reveals which pages were read or for how long. Peony's per-page analytics show you every viewer's identity, which pages they read, how long they spent on each page, and their IP location — so if an unexpected viewer appears, you know exactly when the leak happened and can trace it back. For independent sponsors distributing a CIM to 15 capital partners, this visibility turns forwarding from an invisible risk into a detectable event.
I password-protect my investor updates before emailing them to LPs — is that actually enough to prevent forwarding?
Password protection is better than nothing but fundamentally flawed for forwarding prevention. The recipient can share the password alongside the file, and dozens of free online tools can remove PDF passwords entirely. According to the Ponemon Institute, 55% of insider data incidents stem from simple employee negligence — password-sharing is exactly that kind of low-effort mistake. For a PE fund manager distributing quarterly financials to 20 LPs, Peony's identity-based access on the Business plan ($40/admin/month) eliminates shared credentials entirely: each LP authenticates with their own email, and you see every access individually in your analytics dashboard.
My deal team uses access controls on our data room — do we also need screenshot protection, or is preventing PDF forwarding enough?
Preventing forwarding stops the entire file from reaching unintended recipients — through access control, disabled downloads, and link-based sharing. Preventing screenshots stops viewers from capturing content they can already see. You need both. For a Series A founder who shared pitch materials with 30 VCs, one screenshot of your financial projections on a group chat can be just as damaging as a forwarded file. Peony combines screenshot protection (which blacks out content during OS-level capture), dynamic watermarks (which embed the viewer's identity in every frame), and identity-gated access (which controls who can view in the first place) — three layers most data rooms like Datasite and Intralinks charge $25,000+ per deal to provide.
Related Resources
- How to Protect PDFs from Screenshots (6 Methods)
- How to Send a Password-Protected PDF
- Dynamic Watermarking Guide
- Document Security Software Comparison
- How to Send Confidential Documents via Email
- How to Track Pitch Deck Engagement
- How to Protect Your Pitch Deck
- Virtual Data Room vs. Cloud Storage
- Document Sharing Compliance Guide
- Secure File Sharing Guide
You might also like
Mar 21, 2026
How to Protect PDFs from Screenshots in 2026 (6 Methods Worth Using)
Mar 21, 2026
How to Share Files Securely in 2026 (7 Methods I Actually Trust)
Mar 17, 2026
How to Password Protect a Google Drive Folder in 2026 (7 Methods That Actually Work)

