How to Protect Your Pitch Deck (Before an Investor Leaks It) in 2026

Co-founder at Peony. Former VC at Backed VC and growth-equity investor at Target Global — I write about investors, fundraising, and deal advisors from the deal-side perspective I spent years in.
Set up my next data room with SeanLast updated: March 2026
I'm Sean, co-founder of Peony and a former VC at Backed and Target Global. I have raised capital for my own company, advised six others through their fundraising, and seen exactly what happens to pitch decks once they leave a founder's hands.
During one of our own fundraises, something happened that changed how I think about pitch deck security forever. A partner at a well-known fund told us — casually, over coffee — that he had already seen our financial projections. Not because we sent them to him. Because another investor had forwarded our full deck to his firm's entire partnership, including our unit economics, burn rate, and cap table details. We had no idea it had happened, no way to trace it, and no ability to revoke access. The deck was a PDF attachment sitting in dozens of inboxes we never authorized.
That experience is why we built Peony with pitch deck protection as a core use case. This guide covers every method I know to protect a pitch deck in 2026 — from the approach I recommend (a secure data room with layered controls) to minimum-viable tactics you can use today.
Verdict: The best way to protect your pitch deck is a layered approach: screenshot protection that blacks out content during capture (deep dive: block screenshots on Mac and iPhone) + dynamic watermarks that embed the investor's identity + identity-bound access controls + per-page analytics + instant revocation. Peony (free, $0/month) provides all five layers in one platform — no app installation required for investors. With the Verizon DBIR reporting that 60-68% of breaches involve a human element, treating your pitch deck like a casual email attachment is a risk founders cannot afford.
Quick guide — match the method to your situation:
- Want the strongest protection available? Peony data room with screenshot blocking + watermarks + analytics + NDA gates — Method 1
- Need a quick password-protected PDF? Encrypt before sending — Method 2
- Sharing broadly and need view-only controls? Disable downloads and force viewer-only access — Method 3
- Want leaks to be traceable? Dynamic watermarking on every slide — Method 4
- Need legal documentation before viewing? NDA gates — Method 5
- Want to know who engaged and revoke later? Tracking + revocation — Method 6
- Fundraising at a very early stage? Send a teaser, not the full deck — Method 7
Why pitch deck protection matters in 2026
Pitch decks are not just slides. They contain pricing strategy, margins, product roadmap, IP direction, hiring plans, unit economics, and often customer names. Every fundraising process produces three artifacts:
- A blurb — you want this to travel as far as possible
- A pitch deck — this is where things get sensitive
- A data room — this is where things get critical
The blurb is public by design. The pitch deck and data room are not. The problem is that most founders treat pitch decks with the same casualness as the blurb — attaching PDFs to cold emails, pasting public Drive links into Slack, and hoping for the best.
Here is how pitch decks actually leak in real fundraising scenarios:
Email attachments multiply uncontrollably. You send a PDF to one partner. They forward it to an associate. The associate forwards it to an advisor. Each forward creates a new, untracked copy. You have no revocation, no visibility, and no idea how many copies exist. Our guide on how to send your pitch deck to investors shows how to avoid this trap from the start.
"Anyone with the link" sharing breaks accountability. You paste a Google Drive or Dropbox link because it is easy. That URL gets dropped into group chats, forwarded between partners, and left in Notion workspaces. Security teams routinely flag misconfigured sharing links as a major leak vector.
Internal resharing inside investor firms is invisible. Even with good intent, a principal forwards your deck to a portfolio CEO for competitive analysis. A partner shares it with a co-investor. If access is not identity-bound, you cannot distinguish legitimate internal review from uncontrolled spread.
Downloads create permanent, uncontrollable copies. Once someone downloads the file, they can upload it elsewhere, forward it indefinitely, and it survives every "we're passing on this deal" email. Your access controls become irrelevant.
Screenshots and copy-paste bypass view-only settings. Even with viewer-only links, people screenshot financial slides and drop them into internal memos. I tested this myself — it took fewer than 30 seconds to capture a "download-disabled" document using nothing but the built-in OS screenshot tool.
The pattern that works in 2026 is not "prevent every pixel from being captured." It is friction + visibility + consequences: make leaks hard, make them traceable, and make investors know they are traceable.
7 methods to protect your pitch deck
Method 1: Peony secure data room (recommended)
This is the method I use for every fundraise and the one I recommend to every founder I advise. It addresses all five layers — blocking, deterrence, attribution, analytics, and revocation — in one platform with zero friction for investors.
How to do it:
-
Upload your pitch deck to a Peony data room. Create a room for the fundraise context — "Series B - Pitch Materials," "Seed Round 2026," "Strategic Partners." Upload your deck there instead of emailing it as an attachment.
-
Enable screenshot protection. In the room security settings, turn on screenshot protection. Peony's viewer integrates with browser and OS-level capture APIs — when a standard screenshot or screen recording is detected, the deck content is blacked out in the capture.
-
Add dynamic watermarks. Enable watermarking so every slide displays the investor's name, email, and timestamp. If someone bypasses screenshot protection with a camera phone, their identity is embedded in every image they capture.
-
Restrict access to verified identities. Grant access to specific investor email addresses or trusted domains (e.g.,
@sequoia.com,@a16z.com). No anonymous "anyone with the link" viewing for your financials. -
Disable downloads. Set the room to view-only so the deck can only be viewed through Peony's protected viewer — not downloaded as a raw PDF where all your protections vanish.
-
Share one secure link, not the file. Send a Peony link instead of an attachment. If you update the deck later, replace the file behind the same link — no re-sending, no version confusion. If a fund passes, revoke access instantly.
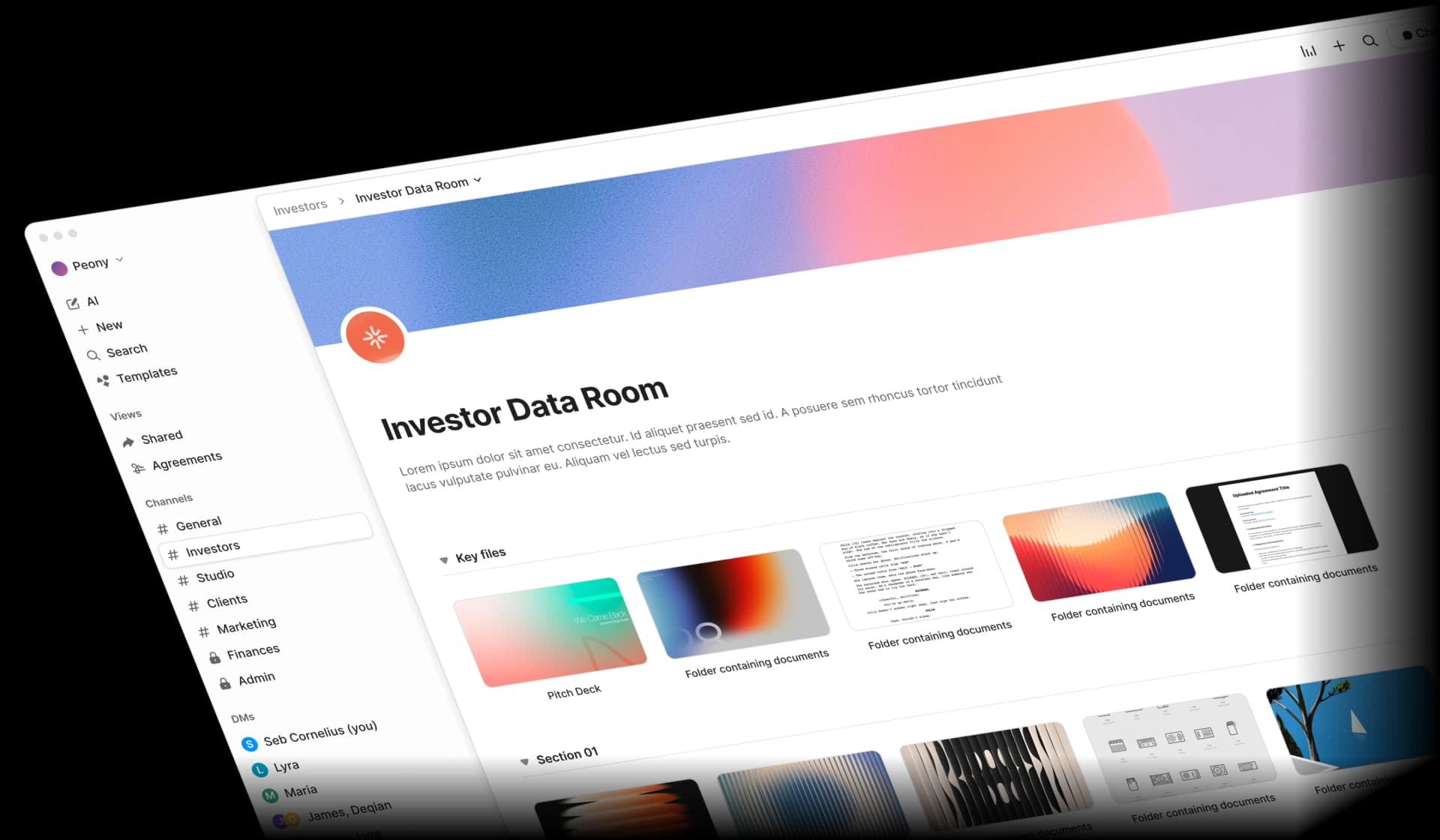
Peony's data room gives you a controlled viewing environment for your pitch deck — organized folders for different investor tiers, branded presentation, and security settings that travel with every document shared during fundraising.
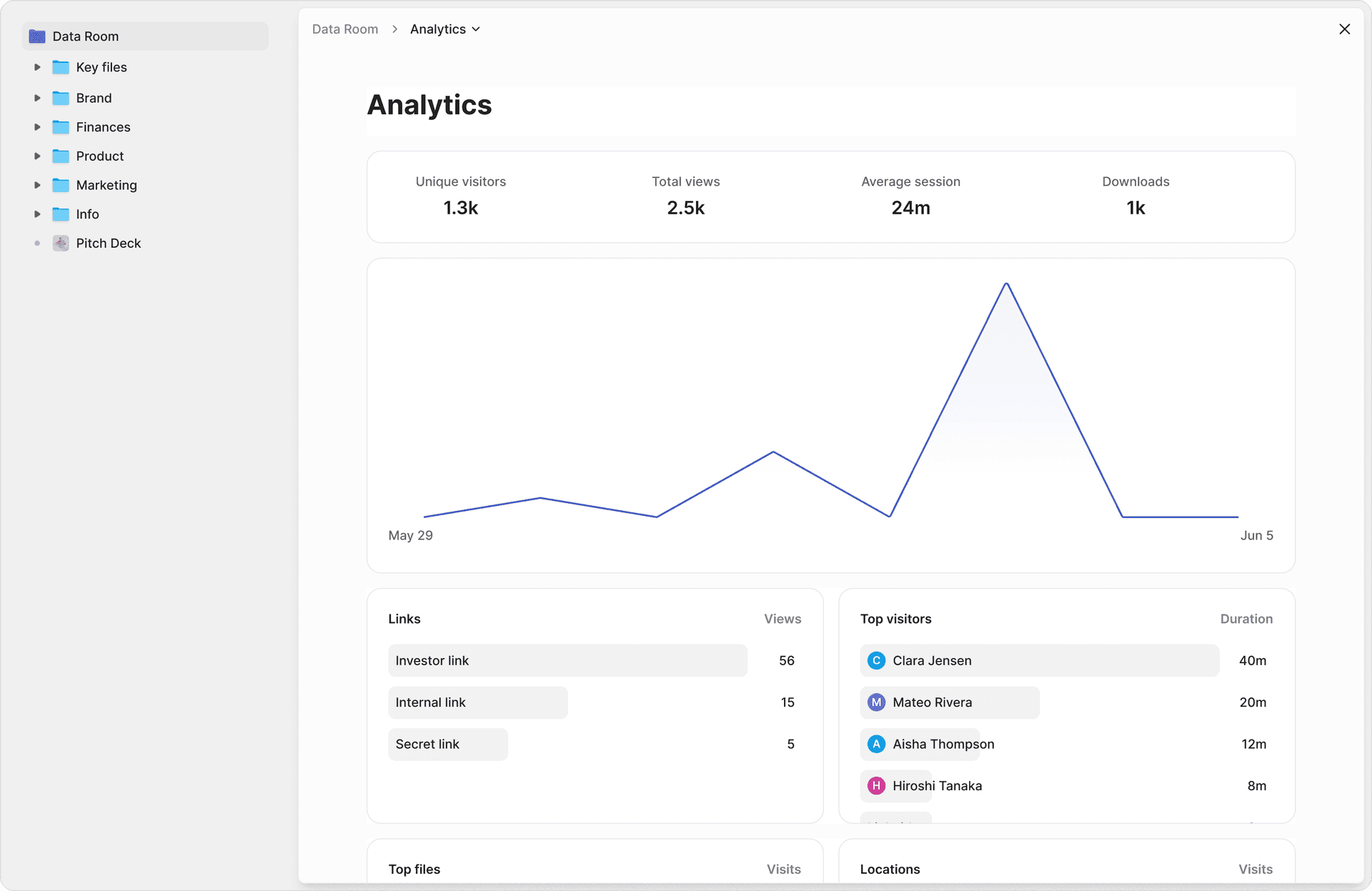
The analytics dashboard shows exactly which investors opened your deck, when they viewed it, which slides they spent time on, and how long each session lasted — signal that tells you who is genuinely interested and who is just tire-kicking.
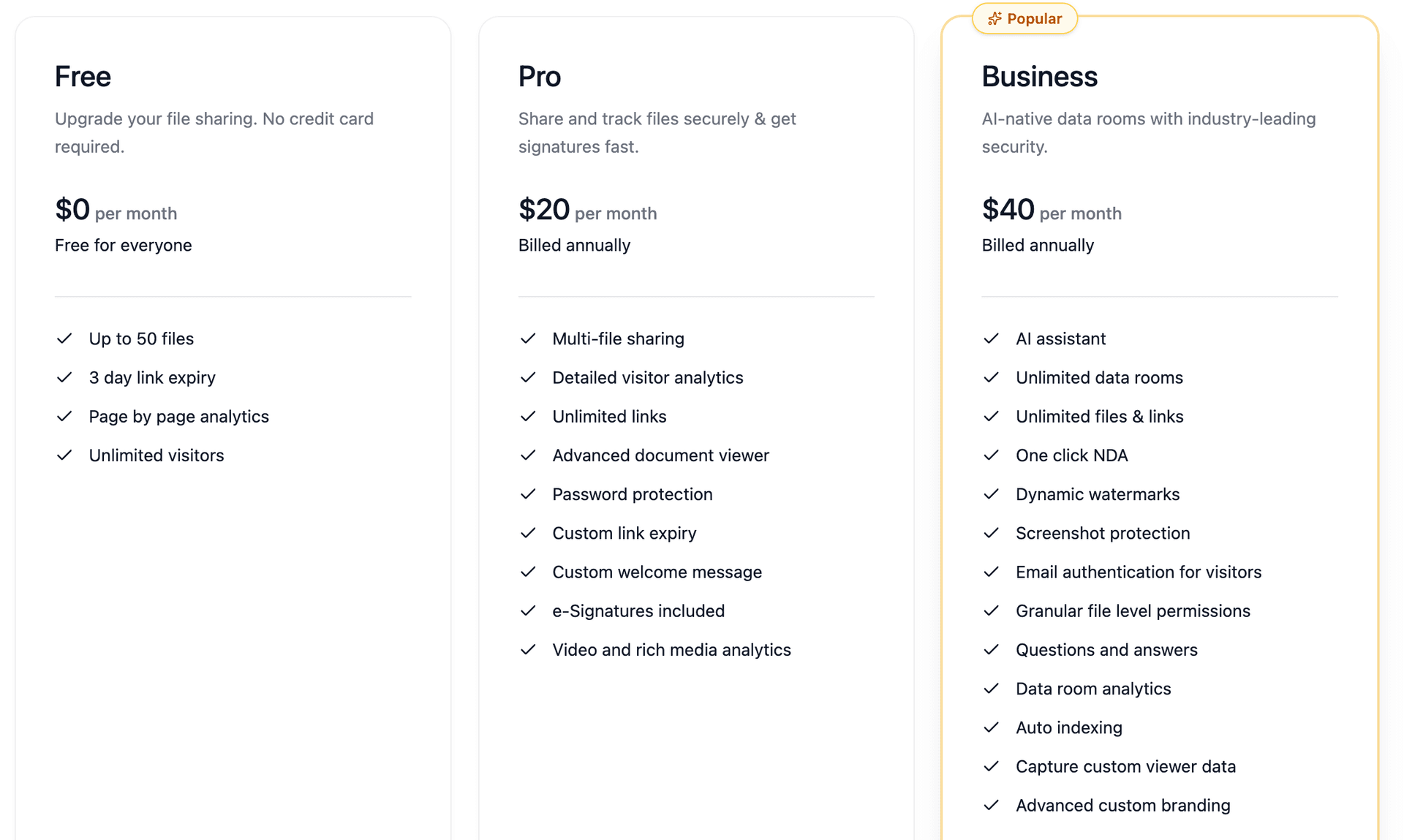
Peony starts free ($0/month, 2 GB) with page-level analytics on every plan. Screenshot protection and dynamic watermarks are included on the Business plan ($40/admin/month). Pro at $20/admin/month adds e-signatures and password protection for growing fundraises.
Pros: Strongest available pitch deck protection. Screenshot blocking, dynamic watermarks, identity-bound access, per-slide analytics, NDA gates, instant access revocation, password-gated links, and link expiry — all browser-based with no app installation for investors. Free tier available. Purpose-built for fundraising and startup workflows.
Cons: Requires investors to view through Peony's secure viewer (which is by design — that is where the protection lives). Does not protect against camera-phone captures, though dynamic watermarks make those traceable.
Best for: Any fundraise where your deck contains financials, unit economics, customer names, IP, or product roadmap. This is the default for founders who treat their deck like the asset it is.
Method 2: Password-protected PDF export
Adding a password to your pitch deck PDF is the simplest form of access control. Most modern PDF readers use AES-256 encryption, which is genuinely strong — nobody is brute-forcing that password.
How to do it:
- Open your pitch deck in Adobe Acrobat, Preview on Mac, or a PDF editor.
- Select File, Protect, Encrypt with Password.
- Set a strong passphrase (NIST recommends long, unique passphrases over complex character requirements).
- Send the PDF via email and the password via a separate channel — text, phone call, or a different messaging app. Never send the password in the same email thread.
Pros: Free and universally supported. Strong encryption (AES-256) means the file itself is secure in transit and at rest. Works offline. Simple for recipients who are comfortable with PDFs.
Cons: Once someone has the password, they have unlimited access forever — they can forward both the file and the password. No visibility into who opened it, no revocation, no analytics, no watermarking. The file lives on their device permanently. Password-protected PDFs are the digital equivalent of a locked box with the key taped to the lid.
Best for: Low-sensitivity decks, or as a temporary measure when you need to send something quickly and cannot set up a data room yet. For anything with real financial details, use Peony instead.
Method 3: View-only link sharing (no download)
Force investors to view your pitch deck in a controlled viewer rather than downloading the raw file. This is a prerequisite for every other protection method — if someone has the raw PDF, all viewer-level protections are irrelevant.
How to do it:
- With Peony: Set room permissions to view-only with downloads disabled. The deck is viewed in Peony's secure viewer where screenshot protection and watermarks are active. Configure identity-bound access so only verified investors can view.
- With Google Drive: Share with "Restricted" access and uncheck "Viewers and commenters can see the option to download, print, and copy." Note: this does not prevent screenshots or provide analytics.
- With OneDrive/SharePoint: Set permissions to "View only" and disable downloads. Similar limitations to Google Drive.
Pros: Removes the easiest exfiltration path (downloading the raw file). Forces viewing through a controlled environment where additional protections can apply. Available on most cloud platforms at some basic level.
Cons: On Google Drive and OneDrive, does not prevent screenshots, screen recordings, or manual retyping. No watermarking or analytics on free cloud tiers. In Peony, view-only mode works alongside screenshot protection and watermarks for a much stronger posture.
Best for: As a baseline layer combined with screenshot protection and watermarking. On its own, view-only sharing is friction — not security.
Method 4: Dynamic watermarking
Even if you use nothing else, dynamic watermarking is one of the strongest practical deterrents against pitch deck leaks. The UK NCSC recommends watermarking as a core control for sensitive data, and it is psychologically powerful in a fundraising context.
How to do it:
- With Peony: Enable dynamic watermarks in your room settings. Peony automatically overlays the investor's name, email, and timestamp on every slide — no manual PDF editing required. Each investor sees their own identity on every page. For the step-by-step setup including bulk per-investor link generation and the NDA × watermark decision matrix by round size, see How to Watermark a Pitch Deck with Each Investor's Email.
- Without Peony: Use Adobe Acrobat Pro or a PDF editor to add a static watermark ("CONFIDENTIAL") before sharing. This is weaker — same watermark for everyone, easier to crop — but better than nothing.
Why it works: When an investor sees their own email address stamped across your financial projections, "let me just forward this to our portfolio company for competitive intelligence" becomes "do I really want my name on those slides if the founder traces the leak?" That shift in calculus prevents more leaks than any technical blocking alone.
Pros: One of the most effective practical deterrents. In Peony, watermarks are automatic and per-investor. Makes leaks attributable even after they happen. Works alongside every other method.
Cons: Does not technically prevent the screenshot or forwarding action. Static watermarks (without Peony) are the same for all investors and can be cropped or edited out. Dynamic, per-viewer watermarks require a platform like Peony.
Best for: Every pitch deck, always. Watermarking should be your baseline for every fundraise, combined with other methods for defense in depth.
Method 5: NDA before access
While most VCs will not sign traditional NDAs for early-stage decks — and asking for one can signal inexperience — there is a middle ground that gives you legal documentation without the friction.
How to do it:
- With Peony: Enable NDA gates on your data room. Before an investor can view your deck, they see a confidentiality agreement and must click to acknowledge it. This is documented with a timestamp and their verified identity. No back-and-forth, no DocuSign delays, no asking permission to ask for an NDA.
- Traditional approach: Send an NDA via email, wait for a signed copy back, then share the deck. This adds days to your fundraise timeline and most investors will refuse at the initial pitch stage.
Pros: Creates a legal record that the investor acknowledged confidentiality terms before viewing. Peony's NDA gates are frictionless — one click, not a multi-day signing process. Useful for later-stage fundraises, strategic partner discussions, and M&A due diligence where NDAs are expected.
Cons: An NDA does not technically prevent a leak — it creates legal consequences after one. At seed and Series A, many VCs view NDA requests as a red flag. Peony's click-through NDA gates reduce this friction significantly but some investors may still hesitate.
Best for: Series B and later fundraises, strategic partnerships, M&A processes, and any situation where the investor expects a confidentiality framework. For early-stage, rely on Peony's technical controls (screenshot protection, watermarks, analytics) rather than legal gates.
Method 6: Tracking and revocation
Knowing who opened your deck — and being able to cut access when a relationship ends — is both a security measure and a fundraising advantage.
How to do it:
- With Peony: Every shared link generates per-page analytics: which investor opened, when, which slides they viewed, and session duration. Use the manage links dashboard to see all active shares. When a fund passes, set a link expiry date or revoke access instantly — the deck disappears from their access immediately.
- Without Peony: Google Drive shows basic "last viewed" information but no per-page analytics. You can remove sharing access manually, but any downloaded copies remain on the investor's device.
Why tracking matters for fundraising: Analytics are not just security — they are pipeline signal. An investor who spent 12 minutes on your financials slide and came back three times is a warmer lead than one who opened the deck for 30 seconds and never returned. I use Peony's analytics to prioritize my follow-up sequence after every batch of outreach. For the full analytics playbook, see our guide on tracking pitch deck engagement.
Pros: Full visibility into investor engagement. Instant revocation when a process closes, a fund passes, or a contact changes firms. In Peony, analytics and revocation work together — you always know who has access and can change it in one click.
Cons: Tracking requires a platform that supports it — email attachments provide zero visibility. Revocation only works for content viewed through the platform; downloaded copies cannot be recalled. Analytics are a fundraising advantage but require discipline to review regularly.
Best for: Every fundraise, regardless of stage. There is no scenario where knowing who opened your deck and being able to revoke access is not an advantage.
Method 7: The "don't share the full deck" strategy
The most underrated pitch deck protection method is not sharing the full deck at all — at least not at first.
How to do it:
- Create a teaser deck (5-8 slides). Include your company name, one-line description, market size, traction highlights (revenue growth, user metrics), and founding team. Exclude detailed unit economics, customer names, product roadmap, and IP details.
- Share the teaser freely. Send it via email, post it on your website, share it with angels and scouts. This is your blurb in slide form — designed to generate interest.
- Gate the full deck behind Peony. When an investor requests the full deck after seeing the teaser, share it through a Peony data room with all protections enabled. This creates a natural qualification step: only investors who are genuinely interested see your sensitive information.
- Reserve the data room for due diligence. Your most sensitive materials — cap table details, detailed financials, customer contracts, IP documentation — live in a separate Peony room with even stricter access controls.
Why it works: This mirrors how the best fundraise processes actually operate. A blurb generates meetings. A teaser generates interest. The full deck generates term sheets. The data room supports due diligence. Each stage reveals more information to a smaller, more qualified audience — and each stage can have stronger protections than the last.
Pros: Minimizes the amount of sensitive information in circulation. Creates a natural investor qualification funnel. Reduces the blast radius if any single document leaks. Aligns with how sophisticated VCs and private equity firms expect to receive information.
Cons: Requires creating and maintaining two versions of your deck. Some investors may want the full deck upfront (especially at seed stage, where processes are less structured). Not practical if you are mass-sending to hundreds of funds.
Best for: Series A and later fundraises, or any process where you are being selective about investor access. Also strong for strategic partnerships and M&A processes where information disclosure should be staged. For the full fundraising timeline, our seed funding guide covers every step from target list to wire transfer.
Comparison table: all methods side by side
| Feature | Peony Data Room (Secure Platform) | Password-Protected PDF | View-Only Cloud Sharing | Dynamic Watermarking | NDA Gate | Tracking + Revocation | Teaser Deck Strategy |
|---|---|---|---|---|---|---|---|
| Screenshot blocking | Yes (browser + OS API) | No | No | No | No | No | N/A |
| Dynamic per-investor watermarks | Yes | No | No | Yes (with Peony) | No | No | N/A |
| Identity-bound access | Yes | No | Partial (Google account) | Yes (with Peony) | Yes | Yes (with Peony) | No |
| Per-slide analytics | Yes | No | Limited | Yes (with Peony) | No | Yes | No |
| Access revocation | Yes (instant) | No (once shared) | Yes (remove user) | Yes (with Peony) | No | Yes (instant) | N/A |
| Download prevention | Yes | No | Partial (disables button) | N/A | No | N/A | N/A |
| Legal documentation | Optional (NDA gate) | No | No | No | Yes | No | No |
| No app install for investors | Yes (browser-based) | Yes | Yes | Yes | Yes | Yes | Yes |
| Cost | Free - $40/mo | Free | Free - $22+/user/mo | Free (static) - $40/mo | Free (Peony) - varies | Free - $40/mo | Free |
My take: For any fundraise where your deck contains real numbers, use Peony as your default sharing platform — the Business plan ($40/admin/month) includes screenshot protection, dynamic watermarks, NDA gates, analytics, and instant revocation in one browser-based platform. Combine it with the teaser deck strategy for maximum control. Password-protected PDFs are acceptable as a temporary floor, never as your ceiling.
When to protect versus when to share freely
Not every pitch deck interaction needs maximum security. Here is how I think about it:
Share freely (teaser deck, no restrictions):
- Cold outreach to angels and scouts
- Accelerator applications
- Networking events and pitch competitions
- Your company website or pitch deck database listings
Moderate protection (Peony with watermarks, view-only, analytics):
- Warm introductions to Series A funds
- Follow-up decks after initial meetings
- Angel syndicate data rooms
- Advisor and board member updates
Maximum protection (Peony with screenshot blocking, NDA gate, watermarks, analytics, revocation):
- Full financial deck for active due diligence
- Strategic partnership discussions with potential competitors
- M&A processes and acquisition discussions
- Late-stage fundraises with cap table and customer details
- Any deck shared with investors you do not yet trust
The principle is simple: the more sensitive the information and the less established the relationship, the stronger the protection. Peony makes it easy to dial security up or down per room and per recipient, so you are not choosing between "open" and "locked down" — you can match the protection to the context.
Practical tips for pitch deck security
Treat your pitch deck like an asset, not a flyer. The way you protect your deck is part of the pitch. An investor who receives a professionally secured Peony link with their name watermarked on every slide knows they are dealing with a founder who takes operational discipline seriously. That signal matters during due diligence.
Never send your deck as an email attachment. The moment you attach a PDF to an email, you lose all control. A Peony link keeps the deck inside the secure viewer where your protections apply. If you update the deck, replace the file behind the same link. If a fund passes, revoke the link.
Use one link per fundraise round, not per version. Multiple links with different deck versions create confusion and version control nightmares. Peony's updatable links mean every investor always sees the latest version through the same URL. Update the deck in your data room and the change is live for everyone immediately.
Review access quarterly. Every quarter during an active fundraise — and immediately after closing — review who has access to your deck and revoke anyone who no longer needs it. We do this religiously at Peony. Every single audit turns up at least a few shares that should have been revoked weeks ago.
Classify your information before sharing. Not every slide needs the same protection. Your market size analysis is probably fine in a teaser. Your detailed unit economics, customer names, and cap table details belong behind Peony's full protection suite — ideally inside a dedicated data room. Think in tiers, not binary.
Send passwords on a separate channel. If you use Peony's password-gated links or encrypt PDFs before sharing, never send the password in the same email thread as the link. Use a text message, phone call, or separate messaging app.
Bottom line
You will not build a perfect shield around your pitch deck — and you do not need to. A determined person with a camera phone will always find a way. What you need is competent, low-friction control that makes casual leaks nearly impossible and deliberate ones personally risky.
- Highest protection (active due diligence, strategic discussions, M&A) — Peony with screenshot protection + dynamic watermarks + NDA gates + identity-bound access + analytics + revocation
- Standard fundraise protection (warm intros, Series A/B outreach) — Peony with watermarks + analytics + view-only + revocation
- Early stage / broad outreach — Teaser deck shared freely + full deck gated behind Peony
- Minimum viable — Password-protected PDF + separate password channel (use this as a floor only)
The way I think about it: author your pitch deck wherever you like — Canva, Figma, PowerPoint, Google Slides — and then treat Peony as the front door to anyone who wants to see it. Layer screenshot blocking, dynamic watermarks, and identity-bound access instead of hoping investors will be sensible with your most sensitive business information.
If you are raising a round in 2026, try Peony for free — set up a protected data room for your fundraise in minutes with screenshot protection, dynamic watermarks, NDA gates, per-slide analytics, and instant access revocation.
FAQ
Can investors still view my pitch deck if I enable protection?
Yes. Peony's protections are designed to be invisible to the viewer experience. Investors click a secure link and the deck opens instantly in any browser — no app installs, no plugins, no friction. Screenshot protection, dynamic watermarks, and analytics all work in the background. The goal is zero-friction viewing with full-control sharing.
What is the best way to protect a pitch deck from leaking?
The most effective approach is Peony's layered protection: upload your deck to a secure Peony data room, enable screenshot protection (which blacks out content during capture), add dynamic watermarks (viewer's email and timestamp on every page), restrict access to verified identities, and disable downloads. This combination makes leaks rare, risky, and traceable.
Should I require NDAs before sharing my pitch deck?
Short answer for early-stage founders: no, a traditional NDA request will get your deck ignored by most Tier-1 VCs — asking for one signals inexperience and creates friction. The strategic nuance (when NDAs do make sense, like later-stage diligence with corporate investors) is covered in our startup NDA guide. For founders who still want a lightweight confidentiality acknowledgement without killing momentum, Peony's click-through NDA gate does the job in one click — see our step-by-step mechanic guide for the exact setup.
How does Peony protect pitch decks from screenshots?
Peony's screenshot protection integrates with browser and OS-level capture APIs to detect when a screenshot or screen recording is attempted. When detected, the deck content is blacked out in the capture. Combined with dynamic watermarks that embed the viewer's name and email on every slide, it makes casual screenshots nearly impossible and deliberate ones personally risky — no app installation required.
Can I see which investors actually opened my pitch deck?
Yes. Peony provides per-page analytics showing exactly which investor opened your deck, when they viewed it, which slides they spent time on, and how long each session lasted. This is critical for fundraising — you can prioritize follow-ups with investors who spent 10 minutes on your financials over those who glanced at the cover slide and bounced.
Is password-protecting a PDF pitch deck enough?
Password protection encrypts the file, but once someone has the password, they have unlimited access forever — they can forward both the file and the password. Peony provides a much stronger alternative: identity-bound access where each viewer is verified, downloads are disabled by default, and you can revoke access instantly. Password-protected PDFs are a floor, not a ceiling.
How do I revoke pitch deck access after a fundraise closes?
In Peony, revoking access takes one click. You can revoke individual investor links, expire all links on a set date using link expiry, or archive the entire data room. The deck disappears from every viewer's access immediately. With email attachments or cloud storage links, you cannot revoke anything — the file lives on their device forever.
What should I share in a teaser deck versus a full pitch deck?
A teaser deck should include your company name, one-line description, market size, traction highlights, and team — enough to generate interest without exposing sensitive financials or IP. Keep it to 5-8 slides with no detailed unit economics, customer names, or product roadmap. Share the teaser freely, then use Peony to share the full deck only with qualified investors who request it.
How much does pitch deck protection cost with Peony?
Peony starts free at $0/month with 2 GB storage and page-level analytics. Screenshot protection and dynamic watermarks are included on the Business plan ($40/admin/month). Pro is $20/admin/month and adds e-signatures and password protection. Traditional virtual data rooms charge $1,000+/month. Peony provides VDR-grade pitch deck protection — screenshot blocking, dynamic watermarks, analytics, NDA gates — at file-sharing prices.
Can I update my pitch deck without sending a new link to investors?
Yes. Peony uses a single updatable link — replace the deck file inside your data room and every investor with access automatically sees the latest version through the same URL. No need to re-send links, no outdated copies circulating in inboxes, no version confusion during due diligence.
Related Resources
- How to Download Files from DocSend (Critical Security Flaw) — why "disable download" does not protect your pitch deck
- How to Require an NDA on a Pitch Deck (Click-Through Gate Mechanic)
- How to Track Pitch Deck Views
- How to Send a Pitch Deck to Investors
- How to Protect PDFs from Screenshots
- Seed Funding Guide for Startups
- Best Data Rooms for Startups
- Startup Data Room Checklist
- Startup Fundraising Strategy
- How to Recover from a Leaked Pitch Deck (Forensic Guide) — what to do in the first 2 hours and the 5-phase recovery framework
- Digital Sales Room Guide
- Best Sales Enablement Software
- Due Diligence Data Room Guide
- Secure File Sharing Guide
- How to Password Protect Videos
- Peony Pricing
You might also like
Apr 22, 2026
How to Require an NDA on a Pitch Deck (Click-Through) in 2026
Apr 29, 2026
How to Watermark a Pitch Deck with Each Investor's Email (2026 Guide)
Apr 7, 2026
How to Prevent PDF Forwarding in 2026 (7 Methods — Only 1 Tracks Who Leaked)
