How to Block Pitch Deck Screenshots on Mac and iPhone (2026)

Co-founder at Peony. Former VC at Backed VC and growth-equity investor at Target Global — I write about investors, fundraising, and deal advisors from the deal-side perspective I spent years in.
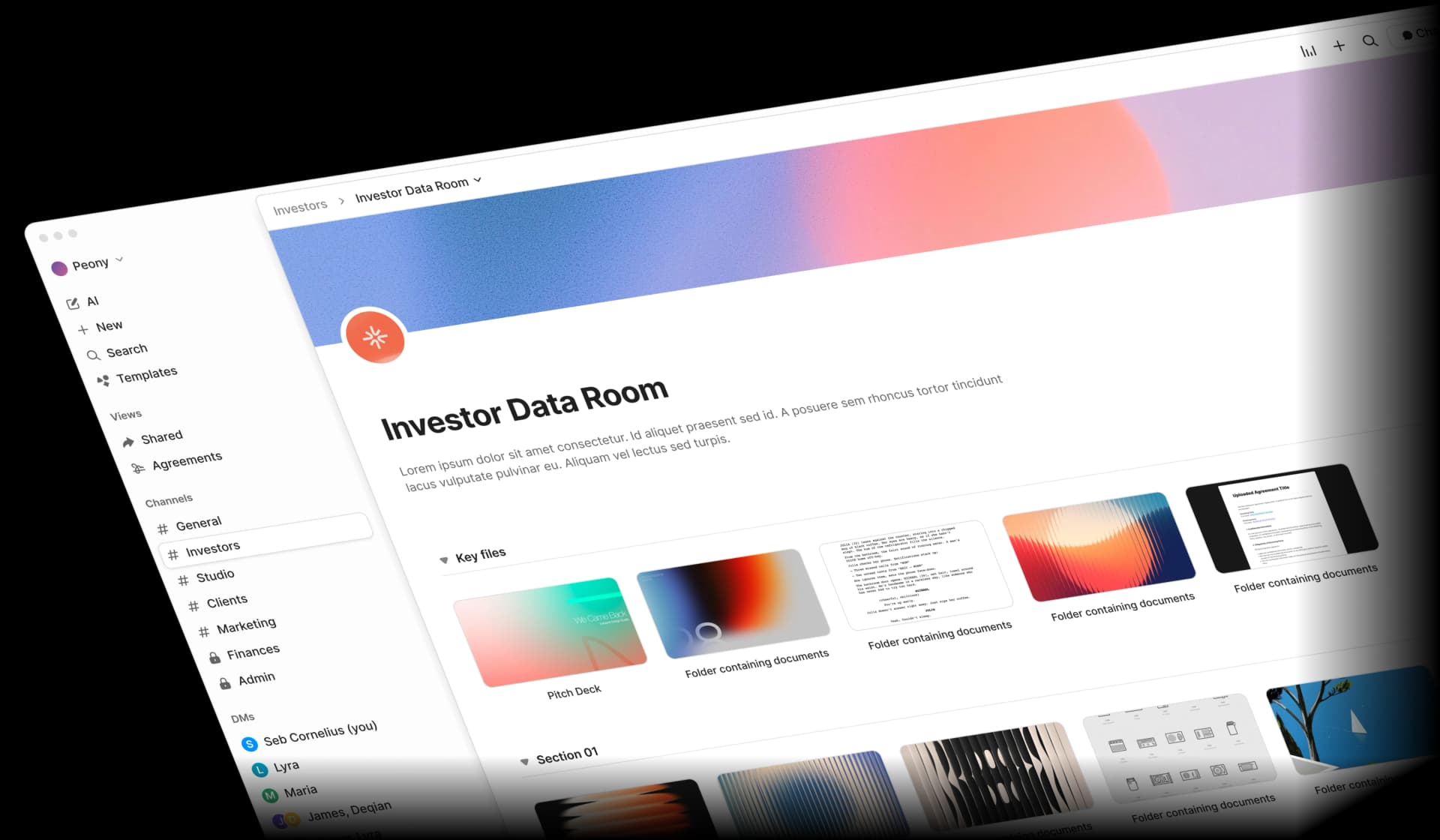
Set up my next data room with SeanLast updated: April 2026
TL;DR. For a modal Seed-to-Series A round (mixed pool of 30+ VCs, no in-house security team), the right pitch-deck screenshot stack is Peony Business at $40/admin/month with Screenshield enabled, dynamic per-investor watermarks, verified-email links, and page analytics. Capture detection fires within seconds on Mac and iPhone; watermarks are server-rendered into slide bytes (so they survive screenshots, unlike DocSend's removable overlay). NDA gates default off until Series B with strategic CVCs. Anchor stat: per IBM 2024, the global mean time to identify and contain a breach is 258 days — by the time a leak surfaces, the term sheet is signed.
In late September 2025, two Andreessen Horowitz LP decks leaked to journalist Eric Newcomer — only the second time in the firm's history that internal documents have leaked publicly. The decks revealed approximately $700M in 2025 fees across reported funds, $25B in net returns since 2009, 56 unicorn investments in the past decade, and a planned $20B mega-fund that would generate another $400M per year in fees during the investment period (Fast Company, Oct 2 2025; Newcomer).
If a16z — with an in-house security team, GP-level compliance, and an elite LP base — could not keep its own decks confidential, the bar for a Series A founder sending a deck to 30 VCs over a free Gmail account is not "as careful as a16z." It is "much more careful, because the surface area is larger and the controls are weaker."
I am Peony's co-founder. I previously invested at Backed VC and Target Global and did a brief stint in M&A at Nomura. The post you are reading is the founder mid-Series-A playbook — the deep dive on the screenshot section of our 7-method pitch deck protection hub, with the Mac and iPhone technical primer the hub doesn't carry. For PDF-generic mechanisms, see how to protect a PDF from screenshots. For Google Docs-specific mechanics, see protect a Google Doc from screenshots. This post is about what a Series A founder does when their deck has to leave their laptop.
Why Are Pitch Deck Screenshots a Real Risk During a Series A Round?
Pitch deck screenshots are a real risk because the M&A leak base rate hit 9.5% in 2024, the average VC partnership review forwards a deck to 4-12 partners and associates, and screen captures account for 31% of all data exfiltration methods in 2025. The Series A surface area — 30+ VCs, every partnership review forwarding the deck internally, no NDA in place — is structurally worse than M&A.
Three numbers founders should hold in their head.
The SS&C Intralinks / Bayes Business School M&A Deal Leaks Report (analyzing 2024 data) found 9.5% of global M&A deals leaked pre-announcement in 2024 — a 16-year high across 15,000+ public acquisitions. Leaked deals took two additional weeks on average to complete. M&A is the cleanest peer benchmark we have for "deal documents in a controlled, NDA-bound process," and the rate is roughly one in ten. Pitch decks have no NDA, the audience is 30+ VCs not 5 banks, and forwarding to portfolio CEOs for "competitive view" is normalized. The pitch-deck rate is presumed worse — there is no public study, but the structural pressure all points up.
The Fortinet 2025 Insider Risk Report (October 2025) found screen captures account for 31% of all data exfiltration methods — the single most common path, ahead of video conferencing apps (29%) and printers (20%). Screen captures beat email forwards in 2025 because the capture happens in seconds, leaves no email trail, and the captured image circulates in Slack and DM channels that the original sender never sees.
The IBM Cost of a Data Breach 2024 report measured the global mean time to identify and contain a breach at 258 days (194 to identify plus 64 to contain) — a seven-year low. That is the silent-leak window. By the time you find out a deck slide is in a competitor's deck, it has been on the loose for the better part of a year.
The "VC forward" pattern is structural, not anomalous. Standard partnership review forwards a deck to 4-12 partners and associates and advisors. Each forward is a new screenshot vector. The standing fundraising-community advice — captured in the Stripe Atlas pitch-deck guide and reflected across investor blogs — is to "go forward on the assumption that your deck will be forwarded to someone you don't want it forwarded to." When I was at Backed VC reviewing inbound decks, the modal pattern was: associate flags interesting deck → partner skims → partner forwards to one or two trusted operators for a "gut-check" → those operators are sometimes founders in adjacent or competitive spaces. Nothing malicious. Just process.
Why watermarks alone don't solve it. Watermarks are an attribution control, not a prevention control. A visible per-recipient watermark deters quiet sharing because the leaker's identity is baked into every page — but the screenshot still happens, the slide still circulates, and the cap-table reveal still ends up in a competing founder's Slack. Watermarks plus capture detection plus per-investor links is the actual stack.
The Verizon 2024 DBIR puts a final number on this: 68% of breaches involve a non-malicious human element. The realistic threat model for a Series A founder is not the rogue partner. It is the well-meaning associate who forwards the deck to one too many people.
How Do Screenshots Actually Work on Mac and iPhone?
Screenshots on Mac and iPhone use system-level OS APIs that no application can fully block — but iOS exposes a real prevention API for native apps (isSecureTextEntry and SwiftUI's .privacySensitive()), iOS detection APIs fire during and after capture (UIScreen.isCaptured, userDidTakeScreenshotNotification, capturedDidChangeNotification), and macOS exposes detection through ScreenCaptureKit since macOS 12.3. Web-based deck viewers in mobile Safari can detect but not fully prevent. The takeaway: aim for detection plus dynamic watermarks, not blanket prevention.
macOS screenshot mechanics
The three system-level shortcuts every Mac user knows:
- Cmd+Shift+3 — full-screen capture
- Cmd+Shift+4 — region capture
- Cmd+Shift+5 — toolbar with screen recording (since macOS Mojave 10.14)
Until macOS 12.3 (March 2022), third-party recorders relied on legacy CGDisplayCreateImage and CGWindowListCreateImage APIs. macOS 12.3 introduced ScreenCaptureKit, the modern framework now powering Zoom, Loom, and CleanShot X. ScreenCaptureKit's SCContentFilter excludingApplications: parameter lets a recorder skip designated apps — but this is opt-in by the recorder, not enforceable by the recorded app. macOS does not expose a system-level "this window cannot be screenshot" flag the way iOS does for password fields. So on macOS, the prevention layer is fundamentally limited.
iOS and iPadOS screenshot mechanics
The capture paths on iOS are wider than people realize:
- Hardware buttons (Face ID: side button + volume up; Touch ID: side button + home button)
- Built-in screen recording via Control Center (since iOS 11)
- AirPlay mirroring (QuickTime over USB cable, Apple TV, Mac via macOS Sonoma)
iOS exposes three relevant detection APIs:
UIApplication.userDidTakeScreenshotNotificationfires after a static hardware-button screenshotUIScreen.capturedDidChangeNotificationplus theisCapturedproperty fire during a screen recording or AirPlay mirror- iOS 17+ added
sceneCaptureStatefor multi-window scene granularity (think iPad split-view)
iOS also exposes a real prevention API for native iOS apps: isSecureTextEntry on UITextField causes the system to black out content in screenshots and recordings. Banking apps wrap content in a hidden secure text field to take advantage of it. SwiftUI added .privacySensitive() since iOS 15, which performs the same trick at the view level. The catch: this is a native-app API. It does not work in a web-based deck viewer loaded in mobile Safari. Web has to rely on detection plus visual interventions (blur the slide when capturedDidChangeNotification fires) plus dynamic watermarks.
DRM at the content layer is not applicable to slides
Founders sometimes ask "can you DRM my deck?" The answer is "the thing you want is impossible at the OS level for slide content." HTML5 EME, Widevine, PlayReady, and FairPlay protect video through a hardware-protected decoder pipeline (the decrypted video pixels never reach the regular composited buffer). Slide content has no equivalent. The bits are in the regular composited pixel buffer like any other webpage. There is no "DRM for PDFs" that works the way Netflix DRM works for movies.
Browser screenshot extensions bypass JS-only deterrents
FireShot, GoFullPage, and Awesome Screenshot operate at the browser-internal level — below the DOM. Pure-JavaScript hacks (right-click disable, oncontextmenu = false, CSS user-select: none) are defeated by any free Chrome extension. Real protection has to detect at the OS or CDP layer, not the DOM layer. This is why a "screenshot block" implemented as a CSS overlay is theater. The overlay runs in the page; the extension captures pixels at the browser engine level above the page.
Honest summary table
| Layer | Detect | Prevent | Deter |
|---|---|---|---|
| iOS native app | Screen recording, AirPlay, mirror via isCaptured; screenshot post-fact | isSecureTextEntry / .privacySensitive() views | Watermarks |
| iOS mobile Safari | Limited (no public browser screenshot API) | Nothing OS-level | Watermarks, blur on visibility change |
| macOS native app | Screen recording via private notifications and ScreenCaptureKit | Nothing OS-enforced; app-level black-out | Watermarks |
| macOS browser | Window blur events, page visibility, OS recording state via Chromium private APIs | Nothing OS-enforced | Watermarks, blur on tab switch |
| Camera at screen | Nothing | Nothing | Watermark on every frame |
The honest answer at the OS level: detection is a real lever on iOS and partial on macOS. Prevention is a native-app-only API on iOS and is non-existent on macOS. The web-deck-viewer protection layer is a hybrid — detection plus pre-emptive blur plus server-rendered watermarks.
What Are the Five Real Defenses Founders Can Use Against Pitch Deck Screenshots?
The five real defenses, in priority order, are: capture detection plus blur during recording, pre-emptive blur on visibility change, server-rendered per-recipient watermarks, no-download view-only with screenshot-blocked overlay, and NDA gate plus per-recipient unique link plus revocation. Capture detection is the only one that catches the act in real time; the others are deterrents and attribution controls.
| Rank | Defense | How it works | Failure mode | Cost | UX cost to investor |
|---|---|---|---|---|---|
| 1 | Capture detection plus blur during recording | iOS UIScreen.isCaptured and macOS ScreenCaptureKit hooks fire when capture starts; viewer blanks the slide and emails the sender | Static iOS hardware-button screenshot fires after the bytes are captured; phone-camera bypass is not solvable in software | Peony Business $40/admin/month | Zero |
| 2 | Pre-emptive blur on visibility change | Tab or window blur causes the deck to blur in the rendered frame; if Cmd+Shift+5 grabs focus to capture, the blur is what gets captured | Doesn't help on mobile (single-app context); AirPlay still captures the rendered frame after blur lifts | Free at app level | Slight |
| 3 | Server-rendered visible per-recipient watermark | Email plus IP plus UTC timestamp baked into image bytes at render time on the server; survives any screenshot path | Attribution not prevention — the leak still happens; you find out who | Peony Business $40/admin/month | Zero |
| 4 | No-download view-only with screenshot-blocked overlay | Force browser viewer; OS-level capture event triggers a black-out CSS layer | Pure-CSS overlays bypassed by paid browser extensions; only OS-API-bound overlays survive | Free tier ($0) for view-only; Screenshield blocking on Business ($40/admin/month) | Mild |
| 5 | NDA gate plus per-recipient unique link plus revocation | Click-through NDA on first open; each VC gets a unique URL locked to verified email; access revocable any time | NDAs deter casual leaks; a determined leaker is unbothered | Peony Business $40/admin/month for NDA gate; verified-email links available on free tier | Friction with Tier-1 VCs (varies by stage — see NDA gate guide) |
A few notes on why these are ranked this way.
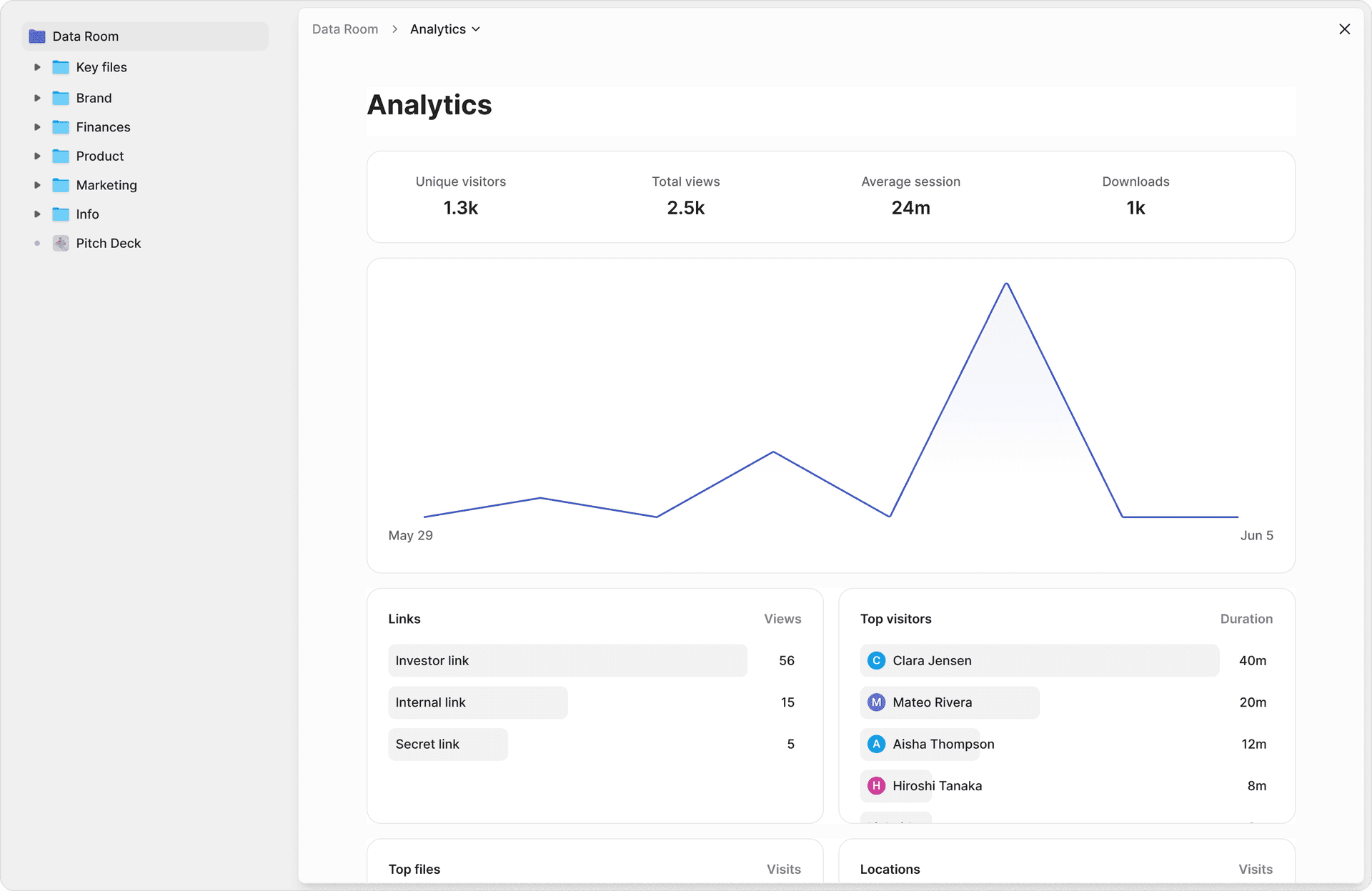
Capture detection sits at the top because it is the only control that gives you a real-time signal. You get an email and a Slack notification within seconds of the capture event, with the investor's email, the slide number, the timestamp, and the IP. That signal is what lets you act — revoke the link, contact the partner directly, or document for downstream rounds. Watermarks tell you who leaked it after the slide is already in the wild. Detection tells you it is in motion.
Server-rendered watermarks beat overlay watermarks because overlay watermarks strip on download. DocSend's "dynamic watermark" is an HTML overlay rendered in the browser — when an investor uses the download button (which DocSend exposes by default on most plans), the watermark is gone. Peony composites the watermark into the slide bytes server-side so the watermark survives screenshots and the original deck file never leaves Peony's servers. For details on the mechanics, see the dynamic watermarking guide and the watermark tool comparison.
NDA gates are last because they have the highest UX cost. Most Tier-1 VCs will open a deck with screenshot blocking and watermarks enabled — those are industry standard. A non-trivial fraction will silently downgrade priority on a deck behind a click-through NDA at early stage. The friction with Sequoia outweighs the leak-to-Sequoia probability for a Series A round. By Series B with strategic CVCs in the mix, the calculus flips.
For per-recipient identity controls beyond the watermark, see different passwords per investor. For the analytics layer that tells you who actually opened the deck, see how to track pitch deck engagement.
How Do I Block Pitch Deck Screenshots Step by Step in Under Ten Minutes?
The 8-step founder workflow takes under 10 minutes end to end: upload to a Peony data room, enable Screenshield plus dynamic watermarks at the room level, configure per-investor links, decide on the NDA gate by stage, turn on screenshot alerts, test from your iPhone and Mac, send personalized links via your CRM, and run a clean alert workflow when something fires. The hard part is the decision about NDA gates, not the configuration.
Step 1: Upload to a Peony data room (don't email the PDF, don't paste a Google Drive link). A PDF in Gmail gives you zero post-send control. A Google Drive link gives you basic analytics but no screenshot protection (see protect a Google Doc from screenshots for why this fails for sensitive content). Peony auto-converts on upload.
Step 2: Enable Screenshield and dynamic watermarks at the room level. Toggle both on the room settings panel. The watermark payload is {viewer_email} • {UTC timestamp} rendered diagonally at 30-40% opacity. For the canonical setup, see the paired sibling post on watermarking a deck per investor email. Bankers running a CIM workflow with timestamps see watermark CIM with timestamp.
Step 3: Configure per-investor links. Each VC gets a unique URL locked to a verified email. Forwarding the link hits an email-verification gate before the deck loads. This kills the casual "let me forward this to my partner" path because the partner's email address is not on the access list, and prompts the recipient to ask the founder for explicit access — which surfaces every internal partnership-review forward.
Step 4: Add an NDA gate (judgment call by stage). Skip for early-stage raises in most cases. Add at Series B+ with strategic CVCs in the pool, biotech IP, or any deck where specific slides are SEC-sensitive. The full setup walkthrough is in the NDA gate playbook — that's the paired sibling post for this one.
Step 5: Turn on screenshot alerts (email plus Slack). You will be notified within seconds of a capture event. The notification carries the investor's email, the slide number, the UTC timestamp, the IP, and the browser fingerprint. Wire the Slack webhook into a private channel so you do not buzz the team for every routine open. Alerts surface in Peony's security console alongside watermark events, NDA acceptances, and revocation logs.
Step 6: Test from your iPhone and Mac before sending. Open the link on your iPhone, take a screenshot, confirm the watermark is in the captured image, confirm the email alert fires. Then start a screen recording and confirm the deck blanks in the captured frames. Repeat on Mac with Cmd+Shift+5 (screen recording) and a Chrome screenshot extension. If anything misfires, fix before sending — the cost of a mis-sent link is real because investor expectations are set in the first 24 hours.
Step 7: Send personalized links via your existing CRM. Affinity, Streak, Notion — pick whatever you already use for pipeline. Don't bulk-send the same link 30 times. Each VC needs their own link with their own email pre-loaded, otherwise per-investor watermarks lose their attribution value.
Step 8: Alert workflow — don't panic. When an alert fires, do three things: cross-reference the access log (was it a known investor on a known IP? was it during business hours in their time zone? is it a screen-recording during a partnership meeting, which is normal?); decide on revocation only if the pattern looks anomalous; document the incident for downstream rounds (you want the trail if a slide surfaces later). The realistic interpretation of most alerts is a partner running a screen recording during their internal partnership review — not a malicious leak. The watermark is there for the malicious case; the alert is there to give you situational awareness on the routine case.
Which Pitch Deck Screenshot Controls Fit My Round Size and Competitive Sensitivity?
The Fundraising Screenshot Risk Matrix maps round size and competitive sensitivity to a recommended Peony control stack. Most Series A founders sit in the modal cell — Seed-to-Series A with medium competitive sensitivity — where Peony Business plus Screenshield plus dynamic watermarks plus per-investor links is the right configuration. Below that, the free tier with email gating + analytics is the bootstrapped floor (no watermark on Free). Above that, NDA gates and redacted variants enter the picture.
The Fundraising Screenshot Risk Matrix
| Low sensitivity | Medium sensitivity | High sensitivity | |
|---|---|---|---|
| Pre-seed (under $3M raise) | Free tier (email gate + analytics) | Free tier + email-gated per-investor links | Business + watermark + Screenshield |
| Seed → Series A ($3M-$25M raise) | Business + watermark + analytics | Business + Screenshield + watermark + per-investor links — MODAL CELL | Business + Screenshield + NDA gate + redacted variants |
| Series B+ ($25M-$100M raise) | Business + Screenshield + watermark | Business + Screenshield + watermark + click-through NDA | Business + Screenshield + bilateral NDA + redacted variants |
| Late-stage ($100M+ raise) | Business + Screenshield + NDA | Business + Screenshield + bilateral NDA + redacted | Bilateral NDA + redacted + sensitive content live-only |
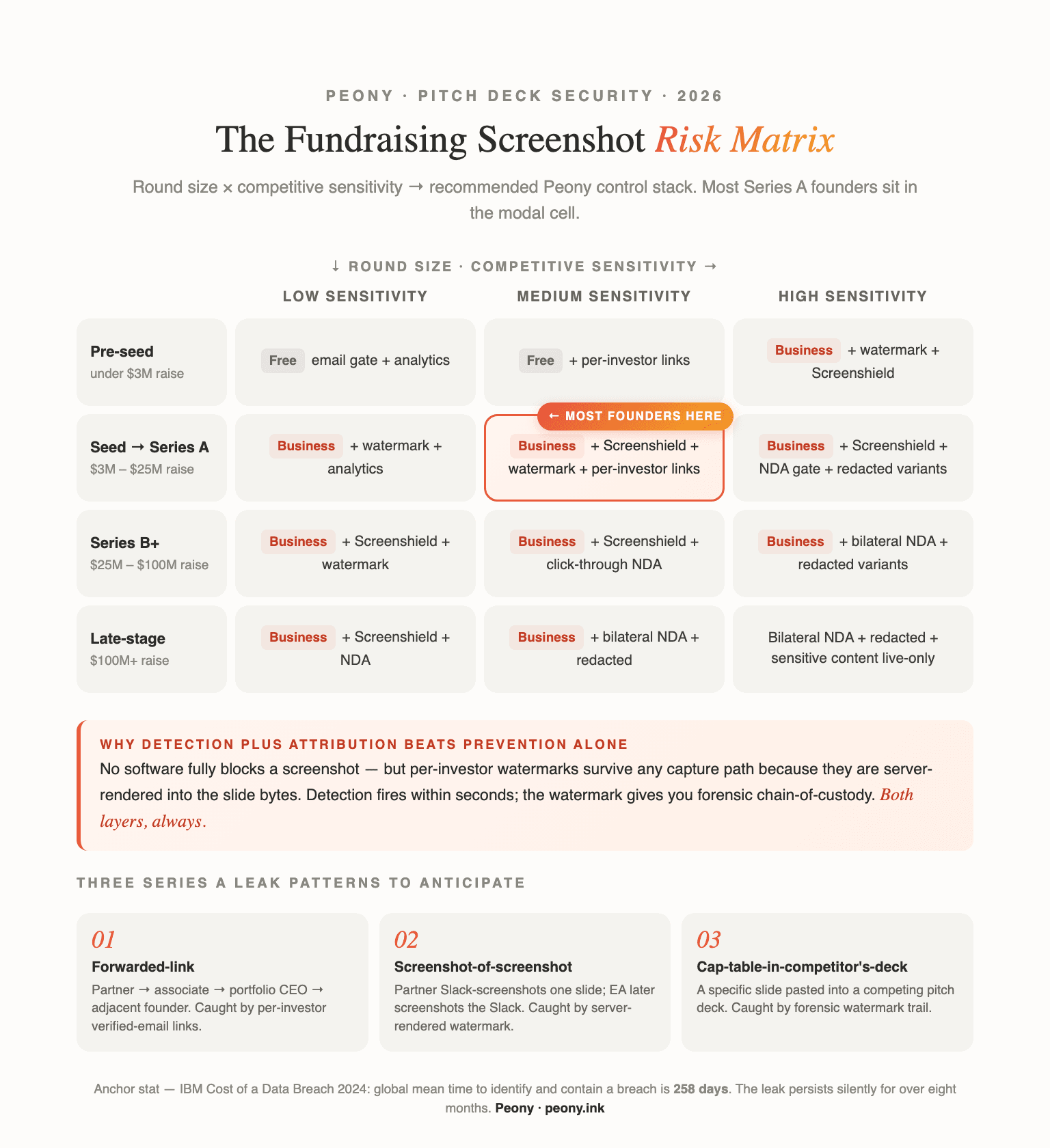
How to read the matrix. The X-axis is competitive sensitivity. Low sensitivity = generic vertical with limited portfolio overlap (think a horizontal SaaS tool). Medium sensitivity = your category has 5-10 funded competitors and several Tier-1 funds have at least one portfolio company in adjacent space. High sensitivity = direct competitor risk (specific named accounts in your customer slide that compete with portfolio companies of the VCs you're pitching, or biotech IP that should not leave a small group of GPs).
The Y-axis is round size. The dynamic is straightforward: bigger rounds attract more partners, more associates, and more advisors. A pre-seed round to 8 angels is structurally different from a Series A to 30 institutional VCs, which is structurally different from a Series B with 4 strategic CVCs at the table.
The modal cell is Seed-to-Series A × Medium sensitivity — most founders are here. The recommended stack is: Peony Business at $40/admin/month with Screenshield enabled, dynamic per-investor watermarks, per-investor verified-email links, and page-level analytics. NDA gates default off because the friction tax with Tier-1 VCs at this stage outweighs the leak risk. Click-through NDA enters at the high-sensitivity column because the legal lever matters when specific portfolio conflicts are real.
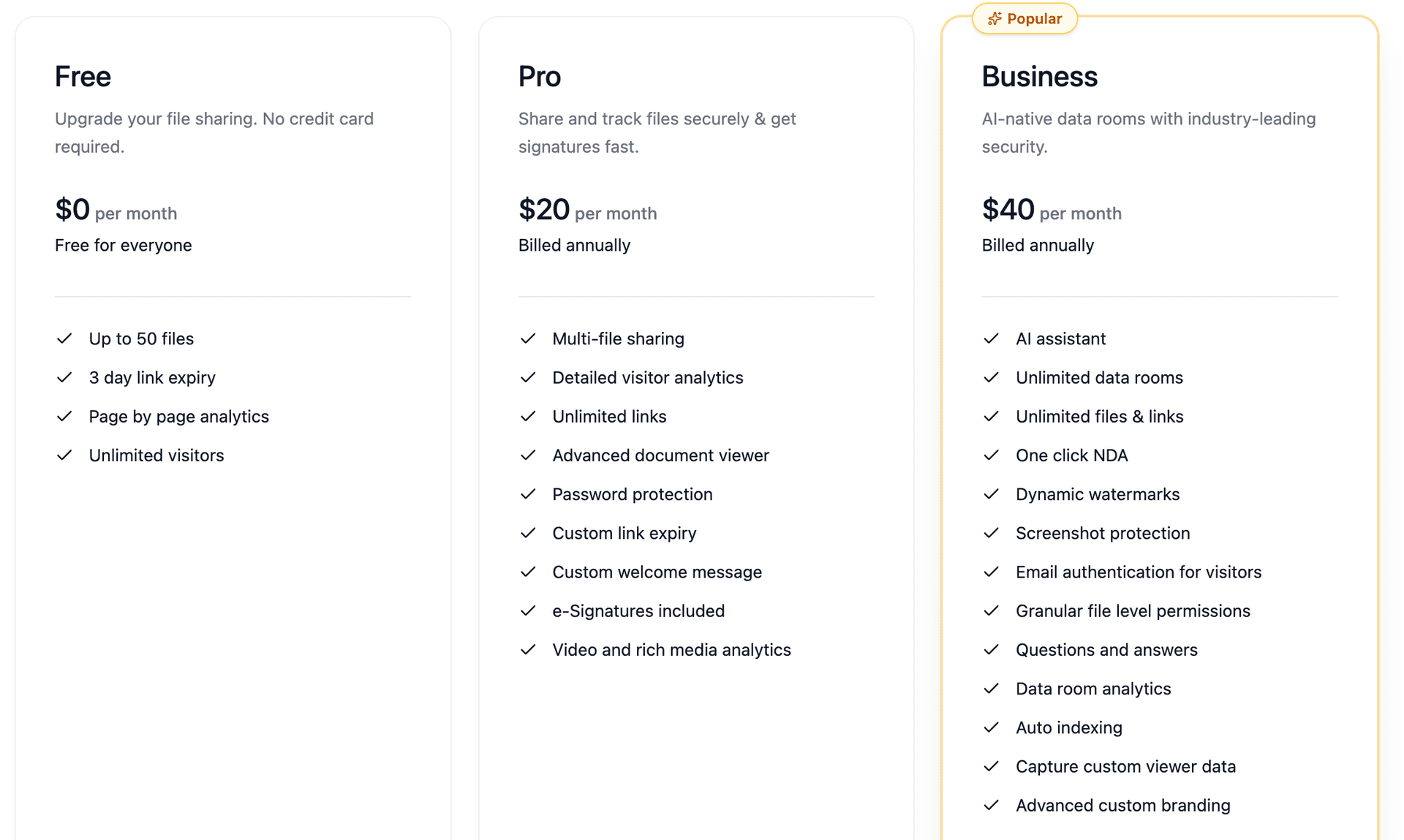
The bootstrapped corner (Pre-seed × Low sensitivity) is the only cell where the free tier is the right answer. Free tier ($0) gives you email-gated links plus page-level analytics plus link expiry plus 2FA plus revocation — the upgrade from a PDF in Gmail is significant even at $0. There is no dynamic watermark and no Screenshield on Free — both live on the Business plan.
The Series B+ rows are where NDA gates start to make sense. A Series B round with strategic CVCs in the pool is a different threat model than a Series A with all-financial investors. Strategics have portfolio conflicts that are not always disclosed up front, and the legal lever of a click-through NDA is worth the friction cost when the deck contains revenue-by-customer or pre-revenue forecasts with named accounts.
Late-stage and biotech are the only cells where bilateral NDA plus redacted variants belong. Bilateral NDA means each side signs a negotiated counterparty agreement (not a click-through). Redacted variants mean specific slides exist in two versions: the public version (rounded numbers, no named accounts) and the unlocked version (released only to investors who sign the expanded NDA). This is overkill for a Series A and exactly right for a pre-IPO round where deck content brushes up against SEC Reg S-K disclosures.
A few situational variants the matrix doesn't capture. For a recovery scenario after a deck has already leaked, the play is to revoke the original Peony room immediately and reissue a watermarked v2 to verified investors only — the tool comparison hub walks through the revocation step. For a banker-driven CIM workflow, see watermark CIM with timestamp — bankers want hourly timestamps for an audit trail, not just per-investor identity.
For the broader 7-method framework (screenshots, watermarks, NDA gate, per-investor links, no-download, analytics, revocation), see the pitch deck protection hub that this post deep-dives the screenshot section of.
When Should I NOT Block Screenshots on a Pitch Deck?
There are three scenarios where blocking screenshots is the wrong call: an accelerator demo-day deck where the slides are public-by-design, an angel-only pre-seed round to known operators where the friction tax outweighs the leak risk, and any moment when the friction of an aggressive control (NDA gate, redacted variants) would cause a Tier-1 partner to pass on opening the deck at all. The honest principle is "default ON for watermarks plus detection, default OFF for NDA gates at early stage."
Default ON across all stages. Dynamic per-investor watermarks (server-side rendered, baked into the slide bytes), per-investor verified-email links (kills casual "let me forward this" path), page-level analytics (you want to know who actually opened the deck and which slides they spent time on — see pitch deck engagement tracking), and disable downloads (force browser viewer). These four are zero UX cost and high signal value. Always on.
Default OFF for NDA gates at early stage. The full reasoning lives in the NDA gate post, but the short version: most Tier-1 VCs will open a deck with watermarks and screenshot blocking with no friction. A meaningful fraction of partners will silently downgrade priority on a deck behind a click-through NDA before they have read the executive summary. For a Seed-to-Series A round where you are running a 30-VC outbound process and the modal investor read time is 2 minutes 24 seconds, the friction-with-Sequoia probability outweighs the leak-to-Sequoia probability. By Series B with strategic CVCs in the mix, the math flips.
Conditional aggressive Screenshield. Turn on the strongest controls in three scenarios: Series B+ with strategic corporate venture capital partners in the pool (their portfolio conflicts are the real risk); biotech or deep-tech IP where one specific slide is the moat; and pre-revenue forecasts where customer names are exposed and a competitor's BD team finding the slide changes the outcome of an active sales cycle.
The accelerator exception. Demo-day decks are public-by-design — the entire point is broad reach. Screenshield on a YC demo-day deck is theater. Use the free tier with a watermark for attribution and call it done. The same logic applies to any deck you are deliberately broadcasting (a fund-of-funds reveal, a public LP letter, a press deck).
What Are the Three Screenshot Failure Patterns That Leak Series A Decks?
The three failure patterns I see most often: the forwarded-link pattern (partner forwards to associate forwards to portfolio CEO forwards to competitor), the screenshot-of-a-screenshot pattern (partner Slack-screenshots one slide; an EA later screenshots the Slack message; the original watermark is double-embedded), and the cap-table-in-a-competing-deck pattern (a specific slide is pasted into a competing founder's deck). All three are caught by per-investor watermarks plus capture detection — the failure isn't the technology; it's not having the technology turned on.
Pattern 1: The forwarded-link pattern. A partner shares the deck link with an associate. The associate skims and forwards to a portfolio CEO for a "competitive view" or a "gut-check on the technical claims." The portfolio CEO is sometimes a founder in adjacent or directly competing space. By the time the slide reaches a competitor, three forwards have happened — none of them malicious. Per-investor verified-email links shut this down because the second-hop email address is not on the access list and the forward hits an email-verification gate. The associate has to come back and ask the founder for explicit access, which surfaces the partnership-review forward path.
Pattern 2: The screenshot-of-a-screenshot pattern. A partner takes a screenshot of one specific slide — maybe the cap table, maybe the financial forecast — and pastes it into the partnership Slack with a comment. An EA, weeks later, screenshots the Slack message for an internal summary. The watermark on the original screenshot is double-embedded into the second screenshot. This is the pattern where server-rendered watermarks pay off most clearly: the watermark is in the pixel bytes of the slide, so every successive screenshot carries the partner's email and timestamp forward, no matter how many layers of forwarding pile on top. An overlay watermark would be stripped at the first screenshot.
Pattern 3: The cap-table-in-a-competing-deck pattern. This is the failure mode that does the most damage. A specific cap-table slide or revenue-forecast slide ends up pasted into a competing founder's pitch deck — used as a "proof point" that "Series A founders in this space are getting valuations of X" or "the competitor is doing Y in revenue." The competing founder's investors then see your numbers in their inbound deck flow. Detection plus watermarks doesn't prevent this, but it gives you forensic clarity when it happens. A specific watermarked screenshot in a competitor's deck is a far cleaner story for downstream investors than "I think someone leaked our numbers but I can't prove it."
How Does Peony Screenshot Blocking Compare to DocSend, Brunchwork, and PDF-in-Gmail?
The honest comparison: Peony Business at $40/admin/month gives you server-rendered watermarks (survive screenshots), capture detection on Mac and iPhone (Screenshield), per-investor verified-email links, NDA gate, and page-level analytics. DocSend Advanced at $150 per month for 3 users renders watermarks as overlays that strip on download, charges $90 per additional user (per-seat trap for a 30-VC outbound process), and acknowledges in their own materials that they cannot fully prevent screenshots. Brunchwork's overlay-based approach has the same overlay-strip vulnerability. PDF-in-Gmail is zero protection. Free Peony at $0 is the bootstrap floor — verified-email plus watermark plus analytics, no Screenshield.
Cost to a 30-VC Series A outbound process. Peony Business is $40/admin/month flat — your whole founding team (you, your co-founder, your head of product who's helping with the deck) work from one $40 seat each, and viewer count does not scale the cost. DocSend Advanced at $150/month for 3 users plus $90/user/month for additional users is structurally different — the per-seat add-on is the pricing trap I have written about elsewhere, where the listed price is the entry point and the bill scales with viewer count or feature count. For a 30-VC outbound, the math doesn't work in DocSend's favor for a price-conscious Series A founder.
Watermark survivability. Peony renders watermarks server-side into the slide bytes — the watermark is in the pixel data before the bytes leave Peony's servers. A screenshot captures the watermark like any other pixel. A right-click "save image" does not exist because there is no original image to save. DocSend's overlay-based watermark is rendered in the browser DOM, so a download (which most DocSend plans expose) gives the recipient a clean, unwatermarked PDF. This is the single biggest practical difference — and it is the difference that matters for a fundraising deck where you cannot trust the recipient not to download.
Screenshot detection. DocSend's own materials acknowledge they "cannot fully prevent screenshotting on mobile devices and on browsers with sophisticated screen-capturing extensions." This is honest and accurate — no platform can fully prevent. The relevant lever is detection plus deterrent. Peony Screenshield runs the iOS UIScreen.isCaptured hooks plus the macOS ScreenCaptureKit hooks plus CDP-level browser events to detect screen recording, AirPlay mirror, and extension-based capture in real time. You get an alert within seconds. DocSend's screenshot-block is a CSS layer that bypassed by paid extensions.
The free-tier bootstrap floor. If you are pre-seed with a $0 fundraising budget, the Peony free tier ($0/month, 2 GB storage) is the upgrade from a PDF in Gmail. You get email-gated links, page-level analytics, link expiry, 2FA, and revocation. Dynamic watermarks and the Screenshield capture-detection layer are Business-only. For a pre-seed round to 8 angels with no portfolio-conflict concerns, the free tier is enough. The moment you start running a Series A process to 30 VCs with a mixed pool, the upgrade math is trivial — one cap-table-slide-in-a-competitor's-deck event would cost more in dilution than Peony Business charges in a year.
The Pro tier note. Peony Pro at $20/admin/month sits between free and Business. It adds password protection and e-signatures but does not include Screenshield or dynamic watermarks. For a solo founder running a tiny pre-seed round and wanting password-gated links, Pro is the right tier. For anyone running a real Series A process, Business is the floor.
For a deeper VDR-by-VDR cost breakdown across 15 platforms (legacy enterprise tools at $15K-$50K per deal, mid-market players, and Peony's tier), see our virtual data room cost guide.
Frequently Asked Questions
I'm a pre-seed founder — can I block screenshots in Gmail-shared decks?
No. A PDF in Gmail gives you zero post-send control — once the recipient downloads it, every screenshot path on Mac and iPhone is open and you have no detection layer. The minimum viable upgrade is the Peony free tier ($0) for email-gated links, page-level analytics, link expiry, and revocation — no watermark or capture detection on Free. Dynamic watermarks and Screenshield (capture detection) are on Peony Business ($40/admin/month). The structural fix is to stop sending the deck as an attachment and start sending a per-investor link.
Will VCs open a deck with screenshot blocking enabled?
Yes for the vast majority. Watermarks and per-investor verified-email links are industry standard and most Tier-1 VCs open these decks every day without friction. The aggressive controls (click-through NDA gates, redacted variants) trigger meaningful friction at early stage and a non-trivial fraction of partners will silently downgrade priority — that is the honest tradeoff. Basic detection plus dynamic watermarks does not. A pitch deck read in 2 minutes 24 seconds (DocSend's 2024 average) cannot afford a 30-second login flow on top of a manual NDA.
What if a VC takes a photo of their screen with another phone?
Unsolvable case. No software prevents a camera pointed at a screen. The mitigation is a per-investor dynamic watermark — every photo also captures the VC's email and a UTC timestamp diagonally across the slide, so the leak is attributable. This is exactly why Peony renders watermarks server-side rather than as a CSS overlay: a phone-camera photo of the screen captures the watermark just like any other pixel, and a tear-out screenshot does not strip it.
How do I know if a screenshot of my pitch deck was taken?
Peony Business sends an email and Slack notification within seconds of the capture event. The alert includes the investor's email, the slide number, the UTC timestamp, the IP address, and the browser fingerprint. Detection runs on the iOS UIScreen.isCaptured property and the macOS ScreenCaptureKit hooks for screen recording, plus page-visibility and CDP events for screenshot-capable browser extensions. You will not catch every static screenshot on every device — but you will catch every screen recording, every AirPlay mirror, and every extension-based capture in real time.
Does pitch deck screenshot blocking work on iPad split-view?
Yes. Peony reads UIScreen.isCaptured plus the iOS 17+ sceneCaptureState property per scene, so a screen recording across both panes of an iPad split-view triggers the detection alert and blanks the deck pane. AirPlay mirroring from the iPad also fires capturedDidChangeNotification, which surfaces the same alert. Static hardware-button screenshots fire after the fact through userDidTakeScreenshotNotification — the watermark is in the captured pixels but the slide is not blanked because no public iOS API previews a screenshot before the bytes are written.
Can DocSend block pitch deck screenshots?
DocSend cannot prevent screenshots — their own materials confirm DocSend cannot fully prevent screenshotting on mobile devices and on browsers with sophisticated screen-capturing extensions. Their dynamic watermark is an overlay that strips on download, and the screenshot-block layer is CSS-based so a paid screenshot extension defeats it. DocSend Advanced is $150 per month for 3 users with $90 per additional user, which means a Series A founder sending to 30 VCs lands on a per-seat trap. Peony Business at $40 per admin per month renders watermarks server-side into the slide bytes so the watermark survives screenshots and the cost does not scale with viewer count.
What about screen recording during a Zoom screen-share of my deck?
When you screen-share, the deck renders in your browser, so a per-investor watermark is not active for the people on the call. The mitigation is to screen-share the Peony viewer logged in as the founder — the founder's own email and timestamp are then watermarked across every shared frame, which is useful for proving date of disclosure if the recording leaks later. For genuinely sensitive slides (cap table reveals, customer concentration with named accounts, pre-revenue forecasts), do not screen-share at all. Read the numbers aloud and let investors take notes, or invite questions in person.
Does this work in Brave or Tor when an investor uses them?
Yes. Capture detection runs at the browser-pipeline level, not the user-agent level. Brave is Chromium-based and inherits Chrome's events for page visibility, screen capture, and tab activation. Tor's Firefox base supports the same DOM events. Server-rendered watermarks are user-agent-agnostic — the watermark is composited into the image bytes before they leave Peony's servers, so any browser that can render a PNG renders the watermark. The only gap is mobile Safari for static screenshots, which we cover under the iPhone limitations note.
How does pitch deck screenshot blocking affect deck loading speed?
Server-rendered watermarks add 50-150 milliseconds per slide on first render and zero overhead on cached views. Page analytics and capture detection are passive event listeners with no perceptible cost. The average investor spends 2 minutes 24 seconds on a deck (per DocSend's 2024 average), so a 100ms watermark composite on the first render is invisible compared to the time-on-page they will actually spend. The friction tax founders should worry about is the NDA gate, not the watermark — which is why I default NDA gates off for early-stage rounds.
I am bootstrapping a pre-seed round with no budget — what is the free version of pitch deck screenshot protection?
The Peony free tier ($0/month, 2 GB storage) gives you email-gated links, page-level analytics, link expiry, 2FA, and revocation on every deck — but no dynamic watermark and no Screenshield. Both watermarks and capture detection live on Peony Business ($40/admin/month). The upgrade from a PDF in Gmail to the free tier is still significant: you go from zero visibility to per-recipient email gating plus an analytics log for $0. For a pre-seed founder pitching 8 angels with no portfolio conflicts, that is enough. The moment you start running a Series A process to 30 VCs, the math on $40 per admin per month for watermarks plus Screenshield plus alerts is trivial against a single leaked cap-table slide.
About the Author
Sean Yu is co-founder of Peony, a virtual data room platform purpose-built for fundraising and M&A workflows. Before Peony, Sean was a venture investor at Backed VC and Target Global, where he reviewed thousands of inbound pitch decks and saw firsthand how partnership reviews leak material to the broader ecosystem. He started his career in M&A at Nomura, working on cross-border lower-middle-market transactions where deal-document leaks routinely added two weeks to deal timelines. He writes about fundraising mechanics, document security, and the gap between what founders worry about and what actually leaks.
Related Resources
Paired sibling posts (this is the deep-dive on the screenshot section of the 7-method founder hub):
- How to Protect Your Pitch Deck — 7-method founder hub
- How to Watermark a Pitch Deck with Each Investor's Email
- How to Require an NDA on a Pitch Deck
- Different Passwords Per Investor
- How to Track Pitch Deck Engagement
Cousin posts (different document type, same screenshot mechanism):
- How to Protect a PDF from Screenshots — generic PDF mechanisms, document-agnostic
- How to Protect a Google Doc from Screenshots — Google Docs-specific
- Watermark a CIM with Timestamp — banker workflow for sell-side processes
Concept hubs:
- Dynamic Watermarking Guide — concept explainer
- Watermark Tool Comparison — platform-by-platform breakdown
- Virtual Data Room Cost Guide — VDR pricing across 15 platforms
- Peony for Fundraising — fundraising-specific data room features
- Peony Pricing — full plan comparison
