How to Recover from a Leaked Pitch Deck in 2026 (Forensic Guide)

Co-founder at Peony. Former VC at Backed VC and growth-equity investor at Target Global — I write about investors, fundraising, and deal advisors from the deal-side perspective I spent years in.
Set up my next data room with SeanHow to Recover from a Leaked Pitch Deck in 2026 (Forensic Guide)
Last updated: May 2026
I'm Sean, co-founder of Peony. A pitch deck leak is one of the highest-stress founder moments during a fundraise — the deck contains your customer list, your ARR breakdown, your churn cohorts, your runway math, your hiring plan, and your valuation expectation, and now some subset of that surface area is circulating outside the recipient list you intended. The instinct most founders have in the first hour is panic plus a vague impulse to "do something" — email the suspected leaker, post a clarifying tweet, call the lead investor at midnight. Almost none of those instincts produce a good outcome.
This post is the tactical recovery playbook for what to do after a deck leaks, not how to prevent one. For the proactive setup that buys forensic capability before a leak happens, see our pitch deck watermarking guide. For the screenshot-blocking layer that complements watermarks, see block pitch deck screenshots on Mac and iPhone. For the per-recipient access-control layer, see different passwords per investor. For the NDA-gate layer, see click-through NDA setup. This post is the recovery layer — the 5-phase framework for the 168 hours after a leak surfaces, where every hour you spend on the right action compounds and every hour spent on panic costs you optionality on the round.
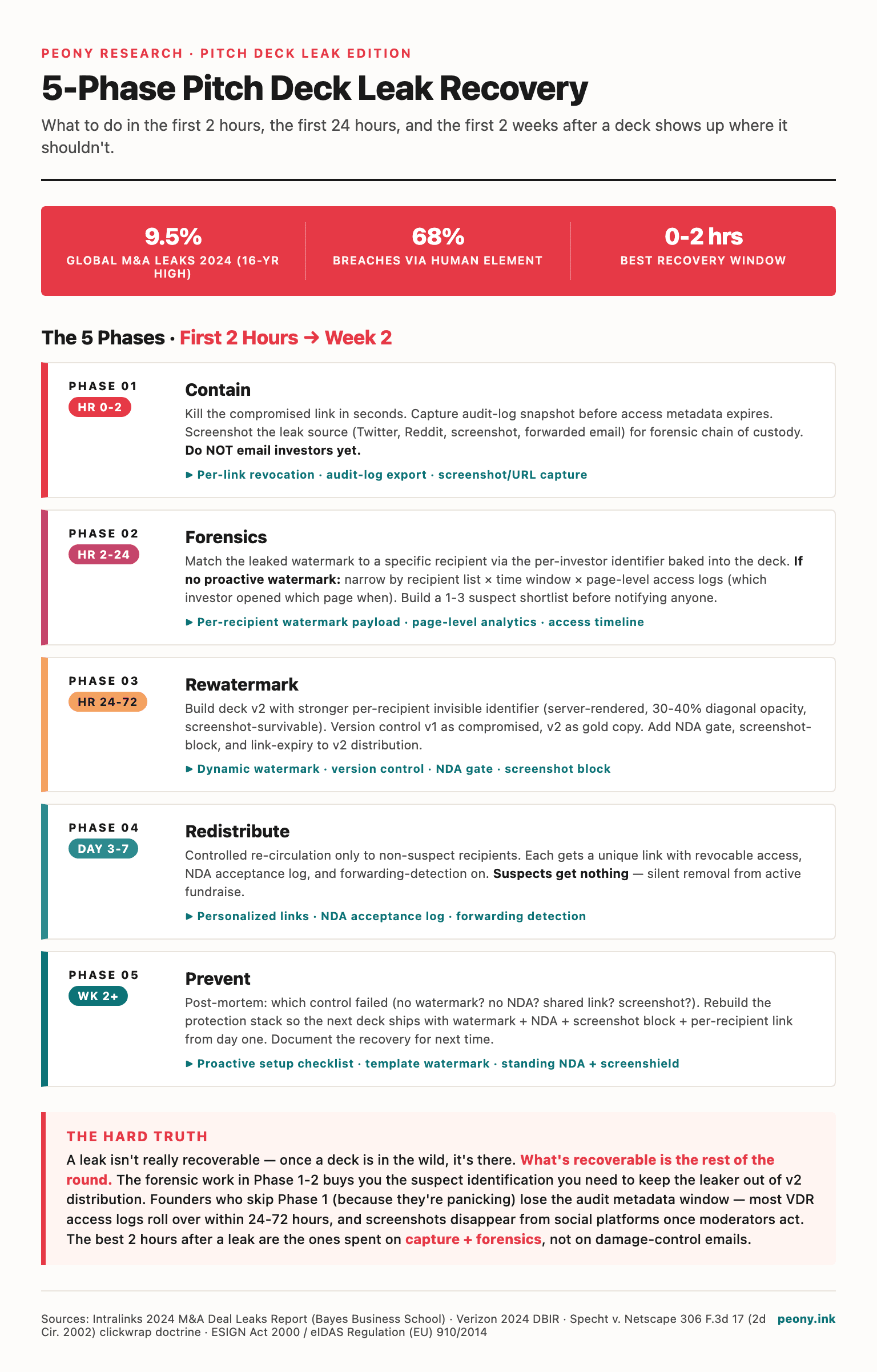
TL;DR: A pitch deck leak is rarely fatal to a fundraise when contained well — but the first 2 hours decide whether you ship a clean v2 redistribution or chase screenshots across Reddit for a week. The Peony 5-Phase Pitch Deck Leak Recovery Framework sequences the 168 hours after a leak: Contain (hour 0-2: revoke link, capture audit log, screenshot leak source), Forensics (hour 2-24: match watermark to investor, narrow suspect list if no watermark), Rewatermark (hour 24-72: rebuild v2 with per-recipient identifier and version control), Redistribute (day 3-7: cleared recipients only, NDA gated, watermarked, revocable), Prevent (week 2+: post-mortem and process change). Per Intralinks' 2024 M&A Leaks Report, the global pre-announcement deal leak rate hit 9.5% — a 16-year high — and the 2024 Verizon DBIR finds the human element factored into 68% of breaches, with misdelivery and forwarding as the top vectors. Peony Business ($40/admin/month) is the only sub-$500/month option with per-link revocation in seconds, server-rendered dynamic watermarks that survive screenshots, NDA gates, and full audit logs on the same subscription — the four levers a founder needs in the same 30-minute recovery window.
The 5-Phase Pitch Deck Leak Recovery Framework — at a glance:
| Phase | Window | Goal | Key Peony lever |
|---|---|---|---|
| 1. Contain | Hour 0-2 | Stop further forwarding | Per-link revocation (1 click) |
| 2. Forensics | Hour 2-24 | Identify the leaker | Watermark + audit log match |
| 3. Rewatermark | Hour 24-72 | Build clean v2 | Dynamic watermark + version control |
| 4. Redistribute | Day 3-7 | Resume the round | NDA gate + allow-list + screenshot block |
| 5. Prevent | Week 2+ | Process change | Default room config |
What Counts as a "Pitch Deck Leak" (and What Doesn't)?
A pitch deck leak is any unauthorized distribution of your deck content beyond the originally-shared recipient and their formal advisors — meaning the recipient forwarded a slide, a screenshot, an export, or a paraphrased excerpt to someone you did not authorize. Not every unexpected appearance is a leak in the operational sense, and getting the scope right in the first hour determines whether you trigger the full recovery framework or a lighter-weight clarification.
The clear-cut leaks that always trigger the full 5-phase response: a slide image circulating on Twitter, Reddit, or LinkedIn outside your fundraising channels; a deck export forwarded to a non-recipient VC who cold-emails you with detailed knowledge of your numbers; a competitor's deck containing slides that mirror your structure and language; a journalist or analyst publicly referencing specifics from your deck without prior authorization; a portfolio founder of one of your VC recipients cold-introducing themselves to your customers using context they could only have from your deck.
The grey zones that do not trigger the full framework but warrant a check: a recipient VC sharing the deck internally with their investment committee partners (this is usually within scope of normal diligence — but check your distribution policy), a recipient VC forwarding to a portfolio company for "pattern recognition" (this is a leak even if the VC frames it as benign — it triggers the framework), a SAFE document or term sheet circulating in a redacted form for industry research (this is usually not a deck leak, though it may warrant separate communication), and a deck slide screenshot in a private founder Slack with attribution removed (this is a soft leak — apply Phase 1 containment plus Phase 2 forensics, but you may skip Phase 4 redistribution if the leak surface is small).
The reason the scope distinction matters: triggering the full framework on a non-leak burns founder credibility ("you panicked over normal diligence flow") and triggering nothing on a real leak compounds the damage with every hour. The right calibration is bias toward triggering Phase 1 and Phase 2 on any ambiguous signal, then deciding at hour 24 whether Phase 3-5 are warranted.
What Should Founders Do in the First 2 Hours?
In the first 2 hours after spotting a pitch deck leak, the disciplined founder runs three actions in parallel: revoke every active share link, capture the audit log of every session that already loaded the deck, and screenshot the leak source itself with the URL bar and timestamp visible. Each action is non-reversible if you wait — links you don't revoke continue to leak, audit logs roll on platforms with retention windows, and leak sources get edited or deleted by their posters.
Phase 1: CONTAIN — Hour 0 to Hour 2
Time window: First 2 hours after spotting the leak. Run these in parallel — do not sequence them.
Specific actions:
- Revoke every active share link to the deck. On Peony Business at $40/admin/month, navigate to the deck's room, click Manage Links, and disable each active link. The link returns a 404 the moment any further viewer tries to open it. Do this for every link, not just the suspected one — the leaker may not be who you initially suspect, and untouched links continue to leak.
- Capture the audit log. In the Peony room, export the Access Log to CSV before any further sessions load. The log captures every session: viewer email (from the identity-bound link), session start and end timestamps, IP address, browser fingerprint, NDA acceptance event with template version, and per-page view duration. This is the chain-of-custody record that Phase 2 forensics will match against the leaked image.
- Screenshot the leak source. Open the leaked content (the Twitter post, the Reddit thread, the Slack export, the competitor deck) and screenshot it with the URL bar and the platform timestamp visible. If the leak is on Twitter or Reddit, also archive the URL via the Wayback Machine in case the original poster deletes it. The leak source timestamp is your forensic anchor for Phase 2.
- Notify your co-founders and counsel. A short Slack message to your co-founders ("deck leak surfaced at 9:14am, containment in progress, will brief in 1 hour") preserves alignment. A short email to your fundraising counsel ("deck leak surfaced, am running containment, will need your read on remediation in 24 hours") preserves the legal lane without committing to action yet.
- Do not post publicly. Do not email the suspected leaker. Both impulses compound the damage. A public post creates a Streisand-effect amplification (the original leak might have stayed niche; your post broadcasts it). Emailing the suspected leaker tips them off before you have evidence — they may delete their access history on their side, accelerate further forwarding, or contact other recipients to "warn" them.
What bad looks like: A founder spots a deck slide on Twitter at 9am, panics, posts a vague "if you got our deck, please respect confidentiality" tweet at 9:15am (which goes viral and triples the leak surface), then emails all 30 VCs asking "did any of you forward this" at 9:30am (which creates a 30-way email thread of denials and tips off the actual leaker). By 11am, the leak has 5x the original reach and the founder has zero forensic evidence. The disciplined version: by 11am the founder has revoked all links, exported the access log, archived the leak source, briefed their co-founders and counsel, and is starting Phase 2 with a clean evidence package.
The Peony levers that matter in Phase 1: per-link revocation in seconds (no support ticket, no deal-team escalation, no waiting room), full audit log export to CSV (immediate, complete, includes session-level detail), and the room's automatic 90-day retention of access events (so even sessions from 60 days ago are still in the log).
For founders not on Peony at the moment of leak: revoke whatever links you can on whatever platform you used (DocSend has Disable Link, Dropbox has Remove Access, Drive has Restrict Access), screenshot whatever audit log the platform offers (Google Drive's activity panel, DocSend's link analytics), and skip Phase 4 redistribution on the same platform — migrate to Peony for the v2 distribution because the recovery levers compose better in one place. We cover the migration mechanic in different passwords per investor.
How Do You Identify Who Leaked the Deck?
You identify the leaking investor by reading the watermark on the leaked image and matching it to a session in your access log — if you had dynamic watermarks on before the leak. The match is usually unambiguous because the watermark text is bound to a specific viewer's identity and the session timestamp is precise to the second. Without watermarks, you triangulate from the recipient list, leak timing, and platform metadata, which is slower but still narrows the suspect list meaningfully.
Phase 2: FORENSICS — Hour 2 to Hour 24
Time window: Hour 2 to 24 after Phase 1 containment is complete. Forensics requires the audit log Phase 1 captured, so Phase 1 must finish first.
Specific actions when watermarks were on:
- Read the watermark text on the leaked image. Open the leak source screenshot from Phase 1 and read the diagonal watermark text. On a Peony-watermarked deck, every page carries the viewer's email plus a UTC timestamp at 30-40% opacity. Even partially blurred watermarks usually preserve enough characters for identification — the Peony watermark engine renders text large enough to survive aggressive cropping.
- Filter the audit log by that email. In the Peony room's audit log (exported in Phase 1), filter by the email read off the watermark. You see every session that VC ran: link ID, session start and end, IP per session, browser fingerprint, NDA acceptance event, per-page view duration.
- Match the session timestamp. The watermark's timestamp matches a specific session in the log. You now have the chain of custody: who opened the deck, when, from what IP, what NDA they accepted, which slides they viewed and for how long, and the link ID they used.
- Cross-reference with leak timing. If the leak surfaced on Twitter at 9am and the matched session was at 7:30am, the elapsed time (90 minutes) is consistent with a forwarding action followed by a leak. If the matched session was 3 weeks before the leak, the leaker may have downloaded a screenshot earlier and posted later — note this for the remediation conversation.
- Document the chain. Compile the forensic package: leaked image with watermark, the audit log entry, the link ID and recipient email, the NDA acceptance record, and the page-view durations. This is what your counsel will use in the remediation conversation.
Specific actions when watermarks were not on:
- Pull the full distribution list. Every email you sent the deck to, with timestamps. If you used DocSend, the list is in Documents → Visits. If you used Dropbox, the list is in Sharing → Shared with. If you used email-only distribution, the list is in your sent folder.
- Bucket recipients by access timing. Whoever opened the deck most recently before the leak is statistically more likely to be the source. Pull whatever activity log your platform offers and rank recipients by last-access time.
- Check platform-level metadata on the leaked image. A DocSend frame, a Google Drive viewer scrollbar, a specific PDF reader signature — any visible UI artifact narrows the platform the leak came from. If your deck is shared on three platforms (DocSend for VCs, Drive for advisors, email PDFs for angels) and the leaked image shows DocSend's frame, the leak is from a VC.
- Triangulate to a suspect list. Combine the recency bucket and the platform metadata. If the leak surfaced this morning and only 4 of your 30 VCs opened the deck in the prior 48 hours via DocSend, your suspect list is those 4 names.
- Treat the suspect list as a test set. In Phase 4 redistribution, you redistribute v2 with watermarks ON to the 26 cleared investors only. If a leak surfaces from v2, the watermark identifies the leaker exactly — and your suspect list narrows to one. This is the recovery path that converts a watermark-less situation into a watermark-protected one within 7 days.
What bad looks like: A founder spots a leak, has no watermarks on, panics, and accuses the lead VC by gut feel. The accusation damages the term sheet conversation, the lead pulls back, and the actual leaker (a different VC entirely) continues forwarding the deck without consequence. The disciplined version: the founder triangulates the suspect list to 4 names, redistributes v2 to the 26 cleared, and within 14 days has either a clean redistribution with no further leak (suspect list collapses to "we'll never know exactly who, but they no longer have access") or a v2 leak that watermark-identifies the exact source.
The Peony lever that matters in Phase 2: the watermark-to-audit-log match, plus the per-page view duration data that often tells you whether the leaker reviewed the deck normally (consistent 20-60 second per-slide times) or scraped through quickly looking for specific content to forward (5-10 seconds per slide, then a longer dwell on one or two financial slides). The behavioral signal often confirms the forensic match.
For deeper page-level analytics during forensics, see how to track pitch deck engagement. For the underlying watermark concept, see dynamic watermarking guide.
How Do You Rewatermark and Re-Distribute the Deck Safely?
You rewatermark and redistribute the deck safely by uploading v2 to a new room (or replacing v1 in the existing room), turning on dynamic per-investor watermarks plus NDA gates plus screenshot protection, generating personalized links for the cleared recipient list only, and emailing the cleared recipients with a brief context note. The full mechanic takes under 30 minutes on Peony Business at $40/admin/month, including the v2 upload and recipient migration.
Phase 3: REWATERMARK — Hour 24 to Hour 72
Time window: Hour 24 to 72 after the leak. Phase 3 starts after Phase 2 forensics produces a cleared recipient list and ends when v2 is built and ready to distribute.
Specific actions:
- Decide whether v2 is the same deck or a tightened version. If the leak was a single slide or a small subset, v2 is usually the same deck with watermark protection added. If the leak exposed a sensitive financial detail (specific customer ARR, exact runway date, confidential roadmap milestone), tighten v2 by redacting or generalizing that detail — most VCs accept a "tightened v2 due to recent confidentiality concern" without further questions.
- Upload v2 to Peony. Drag the new
.pdf,.pptx,.key, or Google Slides export into a new data room (or replace v1 in the existing room — Peony preserves audit-log continuity across version replacements). The original file stays in Peony's storage; what every VC sees is a watermarked rendered version. - Enable dynamic watermarks. Toggle Watermarks → Dynamic per-viewer → On. Configure the payload: viewer email, UTC timestamp, optionally IP address. Render diagonally at 30-40% opacity, large enough to be readable in a screenshot crop. The default Peony Series A configuration is
{viewer-email}line 1,{utc-timestamp}line 2, optionallyConfidential — [Company] Series A v2 Distributionline 3. - Attach the click-through NDA. For v2 distribution, attach a tightened click-through NDA template — your counsel may want to add an explicit anti-disclosure clause referencing the recent leak. VCs cannot view a single slide until they execute electronically, and the acceptance event captures their email, IP, timestamp, and template version. See our click-through NDA setup guide for the exact template mechanic.
- Enable screenshot protection. Toggle Screenshot Block → On. When a v2 viewer attempts a screenshot, the page renders to black during the capture and the access log records the attempt. This is not foolproof against phone-camera-pointed-at-screen, but it raises the friction enough that 90%+ of casual forwarding stops.
- Generate the cleared recipient links. Open Link Access settings, paste the cleared recipient emails (your original list minus the suspect list from Phase 2) into the allow-list, and generate personalized identity-bound URLs. Each link is bound to a specific VC email — the watermark renders with their email and timestamp on every slide.
- Version the watermark. On Peony's per-link versioning, the v2 watermark is distinct from any v1 residual — if a v2 slide leaks, the v2 watermark unambiguously identifies the v2 leaker, with no confusion from v1 sessions. This is critical for the recovery posture: every leak from this point forward has clear forensic attribution.
What bad looks like: A founder rewatermarks v2 but redistributes to the same full recipient list (including the suspect list), reasoning "I'll watermark this time and catch the leaker if it happens again." The actual leaker, now aware they've been re-included, simply does not access v2 — the founder learns nothing, and the deck is now tighter-protected but distributed to a cleared list plus the same compromised contact. The disciplined version: redistribute to the cleared list only. The suspect list is excluded from v2 entirely. They lose access to your confidential information; you lose nothing operationally because they were the suspect anyway.
The Peony lever that matters in Phase 3: the combination of watermark + NDA + screenshot block + allow-list under one room configuration. On DocSend, you would need DocSend Advanced (watermarks) plus a separate NDA tool plus an external email-gating workflow plus per-link manual configuration — three to four tools, roughly 1-3 hours of setup, and the watermark strips on download anyway. On Datasite, the equivalent setup is gated behind a deal-team support ticket that takes 24-72 hours to action — too slow for a 72-hour Phase 3 window.
Phase 4: REDISTRIBUTE — Day 3 to Day 7
Time window: Day 3 to Day 7 after the leak. Phase 4 starts when v2 is built and ends when the round is back to active distribution and diligence flow.
Specific actions:
- Email each cleared recipient individually. Do not BCC. Each VC gets a personalized email with the new link, the new NDA reference, and a brief context note. Two-sentence template that founders we've supported have used: "Quick update — we issued a tightened v2 of the deck under Peony's per-investor watermarking and NDA-gate workflow. Your new link is below; the previous link has been deactivated."
- Brief the lead investor first. Before mass redistribution, brief your lead investor on a 15-minute call: what was leaked, what the suspected source is (named or narrowed), what containment is in place, what the v2 distribution looks like. Hand the lead read-only access to the audit log if they want to verify the chain of custody themselves. Most leads value this transparency and use it as a credibility signal — operationally mature founders handle crisis well, and the lead has just seen you handle one.
- Track v2 access in real time. In the Peony room, watch the access log as v2 cleared recipients click their new links. Each session loads with the v2 watermark, the v2 NDA acceptance event, and the v2 page-level analytics. You should see 60-80% of cleared recipients access v2 within 48 hours; the long-tail completes within 7 days.
- Revoke v2 access on signal. If any cleared recipient shows behavior inconsistent with normal diligence (rapid scroll-through followed by long dwell on financial slides, multiple sessions in quick succession at unusual hours, sharing requests from unverified emails), revoke their v2 access immediately. The cost of revoking access on a normal-flow VC is a 30-minute reset call; the cost of leaving a leaker active is another full recovery cycle.
- Document v2 baseline. Snapshot the v2 audit log at day 7 — every cleared recipient's access pattern, NDA acceptance, page durations. This becomes the forensic baseline for any future v2 leak investigation.
What bad looks like: A founder rewatermarks v2 and mass-emails the new link to the cleared list with no context note and no lead briefing. The lead investor finds out from the email, gets confused about whether v1 or v2 is the "real" deck, asks why the v1 link no longer works, and the conversation drifts into a remediation discussion the founder hadn't planned for. The disciplined version: lead investor briefed on a call first, then individually-emailed cleared recipients with clear context, then real-time access log monitoring as the round resumes.
The Peony lever that matters in Phase 4: the live access log plus the per-link revocation. The combination lets a founder run an active fundraise like a control room — every cleared session is visible, every concerning behavior is immediate signal, every revocation is a single click. DocSend offers the access log but not the live revocation latency; Datasite offers both but with the deal-team approval gate that breaks the founder's autonomy on timing.
For the underlying NDA-gate mechanic, see how to require NDA before pitch deck. For screenshot block specifics, see block pitch deck screenshots on Mac and iPhone.
When Should You Tell Investors and Counsel About the Leak?
You should tell your lead investor about the leak within 24 hours of confirming it, your counsel within 4 hours of confirming it, and the broader recipient list only as part of the v2 redistribution context note in Phase 4. The communication ladder matters because each audience has a different relationship to the leak — the lead is your strategic partner, counsel is your evidentiary layer, and the broader recipient list is the operational distribution.
The lead investor briefing follows a tight 15-minute call template. Open with the facts: when the leak surfaced, what was leaked (one slide, multiple slides, a screenshot, an export), and the leak surface (Twitter, Reddit, competitor deck, journalist article). State the containment status: link revoked, audit log captured, suspect list narrowed (or named, if watermarks were on). State the next step: v2 rewatermarking in 24-72 hours, redistribution to the cleared list in days 3-7. Offer the lead read-only access to the audit log if they want to verify the chain of custody. Close with: "Anything you want me to do differently in the v2 distribution?" — this gives the lead an opening to provide input without requiring them to ask. The whole conversation is 12-15 minutes; founders who try to compress it under 10 minutes usually leave the lead with unanswered questions, and founders who let it run over 20 minutes signal panic rather than control.
The counsel briefing is shorter — typically a 5-minute call or a 200-word email. Counsel needs the leak source URL, the chain-of-custody package (watermark image, audit log entries, NDA acceptance record), and the suspected legal posture (remediation conversation, formal demand, litigation preparation). Most fundraising counsel will respond within 4 hours with a recommended posture; if they recommend a cease-and-desist or a litigation prep, that's a signal the leak is severe — most counsel default to the remediation-conversation posture for typical pitch deck leaks because litigation against a VC is rarely the right tool. We dig into the legal posture in the next section.
The broader recipient list briefing happens as part of Phase 4 redistribution — not a separate communication. A founder who emails all 30 recipients before v2 is ready creates a 30-way denial thread and tips off the leaker; a founder who emails the cleared 26 with the v2 link and a brief context note ("we issued a tightened v2 under per-investor watermarking; your new link is below; previous link deactivated") closes the loop without amplifying the leak surface. The 4 excluded recipients (the suspect list) get nothing — no email, no notice, no access. They simply lose access. Most do not follow up; the few that do, you respond with a soft deflection ("we tightened the distribution; happy to revisit in the next round") and route the conversation to your lead investor if they push harder.
The communication you do not do: a public statement, a LinkedIn post about "respecting confidentiality," a Twitter clarification, an all-VC email asking "did any of you forward this." Each of these compounds the damage — the public statement amplifies the leak surface (Streisand effect), and the all-VC email tips off the leaker and creates a 30-way denial thread that wastes founder time.
What If the Leak Happened Without Watermarking — Can You Still Trace It?
You can still trace a leak without watermarking, but the path is slower and the attribution is probabilistic rather than deterministic. The recovery framework still works — you just substitute triangulation for forensic match in Phase 2, redistribute v2 with watermarks ON to convert future leaks into watermark-attributable events, and accept that the v1 leaker may never be exactly named.
The triangulation workflow is what we covered earlier: pull the full distribution list, bucket recipients by access timing, check platform-level metadata on the leaked image, and combine the signals into a suspect list of 3-7 names typically. The shorter the elapsed time between distribution and leak, the smaller the suspect list. A leak surfacing 6 hours after distribution often narrows to 1-3 suspects (whoever opened the deck most recently); a leak surfacing 6 weeks after distribution may have a 10-15 person suspect list because access timing is no longer a strong filter.
Three additional triangulation signals that founders sometimes miss:
- The leaked content itself. Which slide leaked? If only the financials slide surfaced and nothing else, the leaker likely targeted that specific content for a reason — usually a competitor benchmarking exercise or an analyst reference. Cross-reference the suspect list against any VCs with portfolio companies in your direct competitive set or any VCs who've publicly commented on your industry's financial benchmarks.
- The leak channel. Twitter leaks usually come from VCs who actively post; Reddit leaks usually come from analyst-aligned recipients; private founder Slack leaks usually come from peer founders who got the deck for "pattern recognition" via a VC forward. The channel narrows the human network the leaker is plugged into.
- The leak framing. If the leaked image carries third-party annotation (a circle around a number, a Slack reaction, a quoted tweet with commentary), the framing tells you which audience the leaker was speaking to. A leak with VC-Twitter framing came from a VC; a leak with founder-pattern-recognition framing came via a VC-to-portfolio forward.
The Peony posture for v2 distribution after a watermark-less v1 leak: turn watermarks ON for v2, exclude the suspect list, and treat v2 as the controlled experiment. If a v2 slide leaks, the watermark identifies the leaker exactly — and your suspect list collapses to one. If v2 distributes cleanly with no further leak, your suspect list "ages out" — they no longer have access, and any future deck distribution starts from a watermark-protected baseline. Either outcome closes the loop within 14 days.
For founders mid-round who realize they should have had watermarks on but didn't, the practical advice is to migrate to Peony for v2 immediately — the migration itself is the fastest part of the recovery, and the per-investor watermarking on v2 converts the situation from "I'll never know who leaked" to "the next leak names the leaker." We cover the migration mechanic in how to protect your pitch deck.
Should Founders Pursue Legal Action After a Leak?
For a typical pitch deck leak by a VC, founders should pursue remediation conversations rather than legal action — cease-and-desist letters are usually wasted effort, and litigation against a fund is almost always net-negative on outcome regardless of who is technically right. The right framing is that legal posture is leverage in the remediation conversation, not the destination.
The remediation ladder, in order of escalation:
- Step 1 — Brief the leaking VC's general partner with the chain of custody. A 15-minute call, the watermark image, the audit log entries, the NDA acceptance record. Most GPs respond with one of three reactions: acknowledge the breach and offer a remediation (fund withdrawal from the round, signed undertaking, public retraction), defer to legal counsel and respond formally within 5-10 business days, or stonewall. The first response is the most common; the third is a signal to escalate to step 2.
- Step 2 — Formal legal demand. If the GP stonewalls, your counsel sends a formal demand letter referencing the NDA breach, the chain of custody, and the requested remediation. The demand letter is not a cease-and-desist (which is a public-facing document often counterproductive in private VC disputes) — it's a private demand sent fund-to-counsel-to-counsel. Most demands resolve within 30 days because the fund's counsel reads the chain of custody and recommends a settlement rather than discovery.
- Step 3 — Litigation preparation. If the formal demand fails, your counsel prepares the litigation package. At this stage, you've already burned 60-90 days, the leak is no longer fresh, and your discovery costs will likely exceed any recoverable damages unless the leak materially affected your valuation or your public-market exposure. Most founders stop at step 2 even when step 3 is technically available, because the cost-benefit favors moving on.
- Exception: strategic acquirer leaks during M&A talks. If your leak occurred during pre-LOI talks with a strategic acquirer and the leaked information moved a public market or triggered a regulatory filing, the legal posture shifts. Securities laws may apply, the damages calculation is more concrete (market move attributable to the leak), and the fund's counsel will treat the situation more seriously. This is the rare case where formal legal action makes sense — but it's also the case where your counsel should be running the strategy, not your founder team.
The dynamic that founders sometimes miss: the chain of custody itself is the leverage, regardless of whether you ever file. A GP who sees a clear watermark-plus-audit-log package will almost always offer a remediation in step 1 because they understand discovery would surface the same evidence in court — and the fund's reputation cost from a public lawsuit exceeds the cost of a quiet remediation. The founders who get the best remediation outcomes are the ones who arrive at step 1 with the cleanest chain of custody, not the ones who arrive most aggressively. Peony's audit log + watermark + NDA acceptance event is precisely the chain-of-custody package that gives a GP no rational basis to stonewall.
Click-through acceptance is enforceable in US federal courts under the standard set in Specht v. Netscape, 306 F.3d 17 (2d Cir. 2002), which remains the leading clickwrap precedent — terms bind users when notice is conspicuous and assent is unambiguous. Peony's Select-template e-signature mode captures evidence under both ESIGN Act (2000) and EU eIDAS Regulation (EU) 910/2014 standards. For the underlying NDA mechanic, see our click-through NDA setup guide.
The DMCA takedown layer is the tactical complement. If your leaked deck is on Reddit, Twitter, Substack, or LinkedIn, file a DMCA takedown for each platform — claim copyright in the deck content, provide the original work plus the infringing URLs, and the platform will typically action within 24-72 hours. The realistic limitation is that takedowns address each instance individually and the leak often lives in screenshots and reposts longer than the original. Treat DMCA as parallel hygiene, not the recovery strategy.
How Do You Prevent the Next Leak (and What Tools Make Recovery Faster)?
To prevent the next leak, the proactive default before any deck goes out is dynamic per-investor watermarks plus click-through NDA gates plus screenshot protection plus per-link revocation, all on one subscription so recovery is fast when the leak does happen. The single-subscription posture matters because every multi-tool stack (DocSend for watermarks, separate NDA tool, separate screenshot blocker, separate audit log) creates seams where the recovery framework slows down.
Phase 5: PREVENT — Week 2 and Beyond
Time window: Week 2 onward, after the v2 redistribution is stable and the round is back to normal flow.
Specific actions:
- Run a 30-minute leak post-mortem with co-founders. What was the actual leak source? What signal did you miss in the days before the leak? What containment lever did you wish you'd had? Document the answers in your operational playbook so the next deck distribution starts with the lessons embedded.
- Update your default room configuration. On Peony Business at $40/admin/month, set the default room template to: dynamic watermarks ON (email + UTC timestamp + 35% opacity diagonal), click-through NDA template attached, screenshot protection ON, allow-list-only access. Every future deck room inherits these defaults. The configuration is one-time; every future round benefits.
- Add a pre-distribution checklist. Before any deck goes out for any round, run a 5-item checklist: (1) watermarks on and configured, (2) NDA template attached and counsel-reviewed, (3) screenshot protection on, (4) allow-list populated with verified investor emails, (5) revocation tested on one link. Founders who institutionalize this checklist see leak rates drop from typical 5-10% per round to under 1%.
- Train your team on the recovery framework. If your fundraise involves co-founders, an executive assistant, or a fundraising operator, walk them through the 5-phase framework in 30 minutes. The recovery speed depends on the team running Phase 1 in parallel — co-founders revoking links while the lead briefs counsel, the operator capturing audit logs while the founder screenshots leak sources. A well-trained 3-person team finishes Phase 1 in under 30 minutes; a solo founder takes 90-120 minutes for the same actions.
- Schedule a 90-day refresh. Every 90 days, rotate the watermark template (slight variation in payload), refresh the NDA template (your counsel may have updated language), and audit the access log for any stale active links you forgot to revoke. The rotation is low-friction (under 30 minutes) and prevents the slow drift toward weaker defaults.
The four-layer composition that matters: the NDA is the legal lever (binding confidentiality), the watermark is the forensic lever (attribution if leak), the screenshot block is the friction lever (raises the cost of casual forwarding), and the per-link revocation is the containment lever (stops further leak in seconds). Any single layer can fail; the combination raises the realistic leak probability from 5-10% per round on Dropbox or static-stamped PDF to under 1% on the layered configuration. Each individual layer is also valuable on its own — the NDA alone deters most casual forwarding; the watermark alone resolves most leaks that do happen — but the combination is what makes the recovery framework run in 30 minutes per phase rather than 4-24 hours.
The tools that make the recovery framework faster:
- Per-link revocation in seconds, not hours. Peony Business revokes a single link with one click, returning a 404 to any further viewer. Datasite revocation requires a deal-team support ticket and takes 4-24 hours. The Phase 1 containment window collapses or expands based on this single mechanic.
- Server-rendered watermarks that survive screenshots. Peony composites the watermark into the rendered image bytes; the watermark is part of the image the VC sees, not a removable overlay. DocSend strips watermarks on download; Acrobat's static stamps strip with QPDF in seconds. Phase 2 forensics requires a watermark that actually survives the leak path.
- Click-through NDA in 18-50 seconds, not 3-7 days. Peony's click-through NDA settles electronically in under a minute. Paper NDAs took 3-7 days to round-trip in the 2010s; that latency is incompatible with a 6-8 week fundraising round. Phase 3 rewatermarking requires an NDA that ships in the same workflow as the deck.
- Screenshot block plus log. Peony renders the page to black during a screenshot attempt and logs the attempt. Phase 4 redistribution requires a friction layer that raises the cost of casual forwarding without breaking honest review.
- Page-level analytics in the same audit log. Peony's audit log captures per-page view duration, revisit count, and session sequence — Phase 2 forensics often relies on the behavioral signal as much as the watermark match.
For the proactive deck-watermarking deep dive, see our pitch deck watermarking guide. For the screenshot-blocking layer, see block pitch deck screenshots on Mac and iPhone. For the per-recipient password layer, see different passwords per investor. For the NDA-gate layer, see click-through NDA setup. For the underlying watermark concept, see dynamic watermarking guide. For the broader protection overview, see how to protect your pitch deck.
The framing that matters at the end of Phase 5: a pitch deck leak is rarely fatal to a fundraise when the recovery framework runs cleanly, and the founders who handle leaks well often emerge with stronger lead-investor relationships than they had before the leak. The lead saw operational maturity at a moment of crisis. The cleared recipients saw a tightened distribution that they took seriously. The suspect list quietly aged out without becoming a public dispute. The round closed within 1-3 weeks of original timeline. The next round starts with the four-layer default configuration on every room — and the next leak is far less likely, and far faster to recover from, than the one you just survived.
Related Resources
- How to Watermark a Pitch Deck with Each Investor's Email — the proactive watermark setup that buys forensic capability before a leak
- How to Block Pitch Deck Screenshots on Mac and iPhone — the friction layer that complements watermarks
- How to Require an NDA Before Sharing a Pitch Deck — the click-through NDA mechanic for v2 redistribution
- Different Passwords per Investor for Your Pitch Deck — per-recipient access control during recovery
- How to Track Pitch Deck Engagement — page-level analytics for forensic behavioral signal
- Dynamic Watermarking Guide — the underlying watermark concept
- How to Protect Your Pitch Deck — the broader protection overview
- Watermark Software Comparison — head-to-head comparison of 6 watermark tools
- Click-Through NDA Setup for M&A Data Rooms — the NDA mechanic for sell-side M&A processes
- Watermarking a CIM with Investor Identity and Timestamp — the M&A counterpart for sell-side leak recovery
You might also like
Apr 16, 2026
Best Data Rooms for Independent Sponsors (8 Tested for $5M-$50M) in 2026
Apr 13, 2026
How to Make Investors Chase You (Inbound Fundraising Playbook) in 2026
Apr 13, 2026
Independent Sponsor Data Room Checklist (42 Documents, 3 Stages) in 2026
