How to Share Sensitive Files with Clients Securely in 2026
Co-founder and CEO at Peony. I built the data room platform with a background in document security, file systems, and AI. Founded Peony in 2021 in San Francisco.
Last updated: April 2026
I built Peony because I lived through the exact problem this post addresses. Early in my career, I watched a colleague send a confidential acquisition term sheet to a client via email attachment. The client forwarded it to their attorney, who forwarded it to a partner at another firm, who — three hops later — shared it with someone on the other side of the deal. No one intended harm. But by the time we discovered the leak, there was no audit trail, no way to revoke access, and no way to prove who forwarded what.
That incident shaped how I think about client file sharing. The problem is never the technology — it's the gap between how sensitive a file is and how much control you retain after sharing it.
This guide walks through the exact setup I use and recommend for sharing sensitive files with clients: the security layers that prevent leaks, the analytics that make follow-ups smarter, and the workflow decisions that separate professional from amateur.
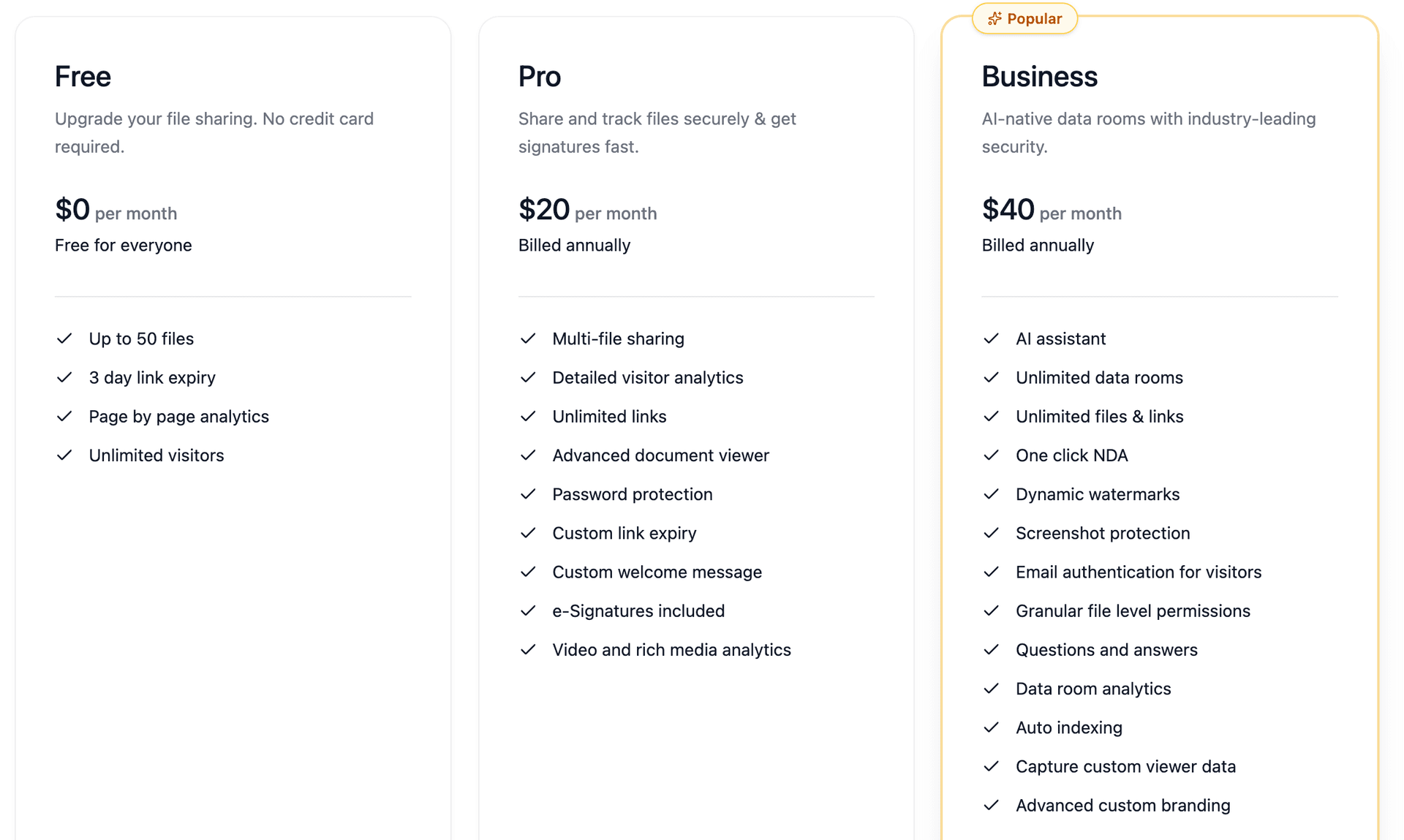
TL;DR: The average data breach costs $4.88 million (IBM 2024). 30 to 50 percent of affected clients terminate relationships after a file sharing incident. Consumer tools like Google Drive and Dropbox lack dynamic watermarks, screenshot protection, and per-page audit trails — the three layers that actually prevent leaks in client-facing scenarios. Peony's Business plan ($40/admin/month) provides all three plus page-level analytics showing which sections each client reads, NDA gating, built-in e-signatures, and AI auto-indexing that organizes a client data room in under 3 minutes.
Why Client File Sharing Is Different from Internal File Sharing
Internal file sharing is a collaboration problem. You want speed, real-time editing, and tight integration with your workflow tools. Google Workspace and Microsoft 365 handle this well.
Client file sharing is a control problem. The moment a file leaves your organization, you need answers to questions that collaboration tools never ask:
- Who actually opened it? Not "someone at the company" — which specific person, from which device, at what time.
- What did they read? Did the client review the pricing section or skip straight to the appendix?
- Did they share it? Can you trace a leaked screenshot back to the viewer who captured it?
- Can you cut access? If the engagement ends tomorrow, can you ensure the client loses access today — not "whenever they clear their downloads folder"?
Consumer cloud storage answers none of these questions. That gap is where client relationships get damaged and confidential information gets exposed.
The 8 Security Layers Every Client Share Needs
Think of these as a stack. Each layer addresses a different failure mode. You don't need all eight for every file — a routine project update needs fewer layers than a pre-acquisition financial model — but you should know what's available and when to activate each one.
1. End-to-end encryption (AES-256 minimum)
This is table stakes. Every file should be encrypted in transit (TLS 1.3 during upload and download) and at rest (AES-256 on storage). If your sharing platform doesn't provide both, stop reading and switch platforms.
Peony uses AES-256 encryption at rest and TLS 1.3 in transit across all plans.
2. Identity-bound access links
The single most important upgrade from consumer file sharing. Instead of "anyone with the link can view," each client gets a unique link tied to their verified email address. This creates three immediate benefits:
- Accountability: Every page view is attributed to a named person, not an anonymous visitor.
- Selective revocation: Cut one person's access without affecting others.
- Leak tracing: If a document surfaces where it shouldn't, you know exactly whose link was used.
Peony's personalized links verify identity through email, password, or two-factor authentication before granting access. Setup takes under a minute per recipient.
3. Dynamic watermarks
A dynamic watermark embeds the viewer's name, email, or IP address into every rendered page. It's not a static logo — it changes per viewer, per session. The security effect is both deterrent and forensic:
- Deterrent: A client who sees their own name watermarked on every page thinks twice before screenshotting and forwarding.
- Forensic: If a screenshot surfaces externally, the watermark traces it to the exact viewer.
This matters most for high-sensitivity documents: financial models, acquisition term sheets, board decks, legal discovery, and anything where a leak has real consequences. If you are sharing a $50M acquisition model with three bidders, each bidder's watermark is unique — and they know it.
Dynamic watermarks are available on Peony's Business plan ($40/admin/month).
4. Screenshot protection
Screenshot protection is the layer most platforms skip. Peony detects and blocks common screen capture methods, and logs any attempt. Combined with dynamic watermarks, it creates a two-layer defense: the watermark deters intentional leaking, and the screenshot block prevents casual capture.
No solution can prevent someone from photographing their screen with a phone camera. But screenshot protection eliminates the easy path — the one most leaks actually take.
5. Granular permission controls
Different clients need different access levels, and different documents within a client engagement need different protections:
- View-only: Client can read but not download. Ideal for draft proposals, preliminary financials, or anything you might revoke later.
- Download-enabled: Client can save a local copy. Use for finalized deliverables and executed contracts.
- Folder-level gating: Sensitive sections (pricing, employee data, IP documentation) sit behind additional access requirements.
- NDA gating (Business plan): Client must sign a confidentiality agreement before viewing the first page. Peony's built-in e-signatures with AI field detection handle this inside the same platform — no separate signing tool needed.
6. Automatic link expiry
Every client link should have a death date. When the project ends, the access should end too.
Link expiry eliminates the most common security gap in client file sharing: old links that remain active months or years after the engagement concludes. Set expiry at project completion, contract end date, or a fixed review window — then stop worrying about lingering exposure.
7. Two-factor authentication
2FA adds a second verification step beyond email. Even if a client's email is compromised through phishing or credential stuffing, the attacker still can't access your shared files without the second factor.
Enable 2FA selectively for your most sensitive shares — board materials, financial statements, legal discovery — rather than requiring it for everything.
8. Complete audit trails
An audit trail records every action: who viewed what, when, from which device and IP, how long they spent on each page, and whether they downloaded or printed anything.
This matters in three scenarios:
- Client disputes: "We never received that document" is immediately verifiable.
- Regulatory compliance: HIPAA, GDPR, SOC 2, and most financial regulations require access logging for sensitive client data.
- Internal accountability: Know exactly which team member shared which version with which client.
Peony's audit trail is exportable and timestamped down to the second.
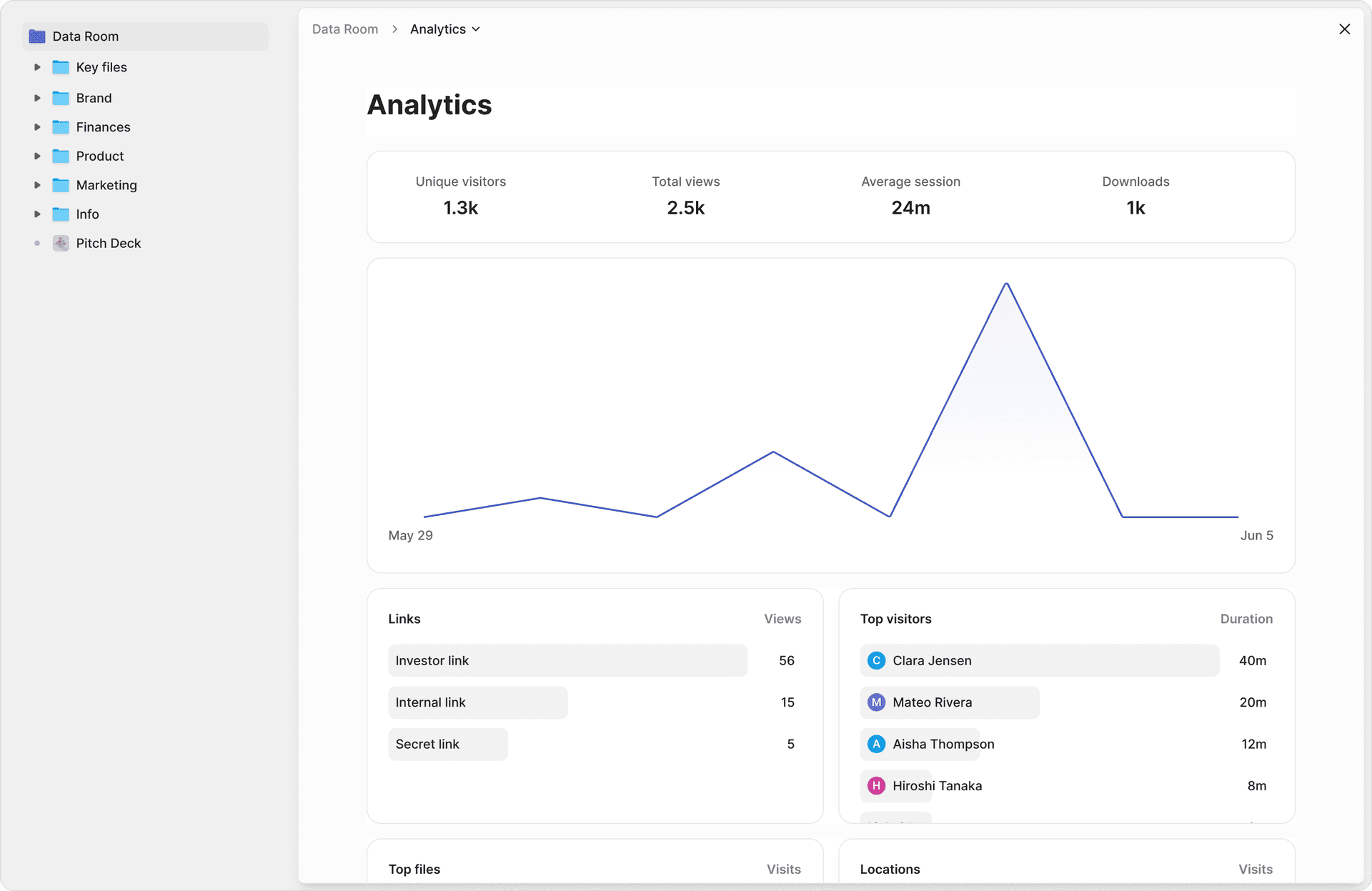
The Engagement Intelligence Advantage
Security protects you from the worst case. But the best client file sharing platforms also give you intelligence for the best case — closing deals faster and building stronger relationships.
Page-level analytics change the follow-up conversation
Traditional file sharing tells you one thing: the file was opened (or it wasn't). Peony's page-level analytics tell you:
- Which specific pages each client reviewed
- How long they spent on each page
- Which sections they revisited (signaling high interest or confusion)
- Which pages they skipped entirely
This transforms how you follow up. Instead of the generic "Just checking if you had a chance to review the proposal," you can say "I noticed you spent time on the implementation timeline — happy to walk through the milestones in more detail."
That specificity signals attentiveness. Clients notice.
Q&A workflow replaces scattered email threads
After reviewing documents, clients have questions. The traditional path — fragmented across email, Slack, phone calls, and text messages — creates inconsistent responses and zero documentation.
Peony's advanced Q&A (Business plan) centralizes this: clients submit questions directly in the document portal, AI drafts initial responses from the uploaded materials, your team reviews and approves, and the finalized answer goes back with a complete audit trail. Every question-answer pair is logged and searchable, so if the same question comes up across clients, you have a consistent response.
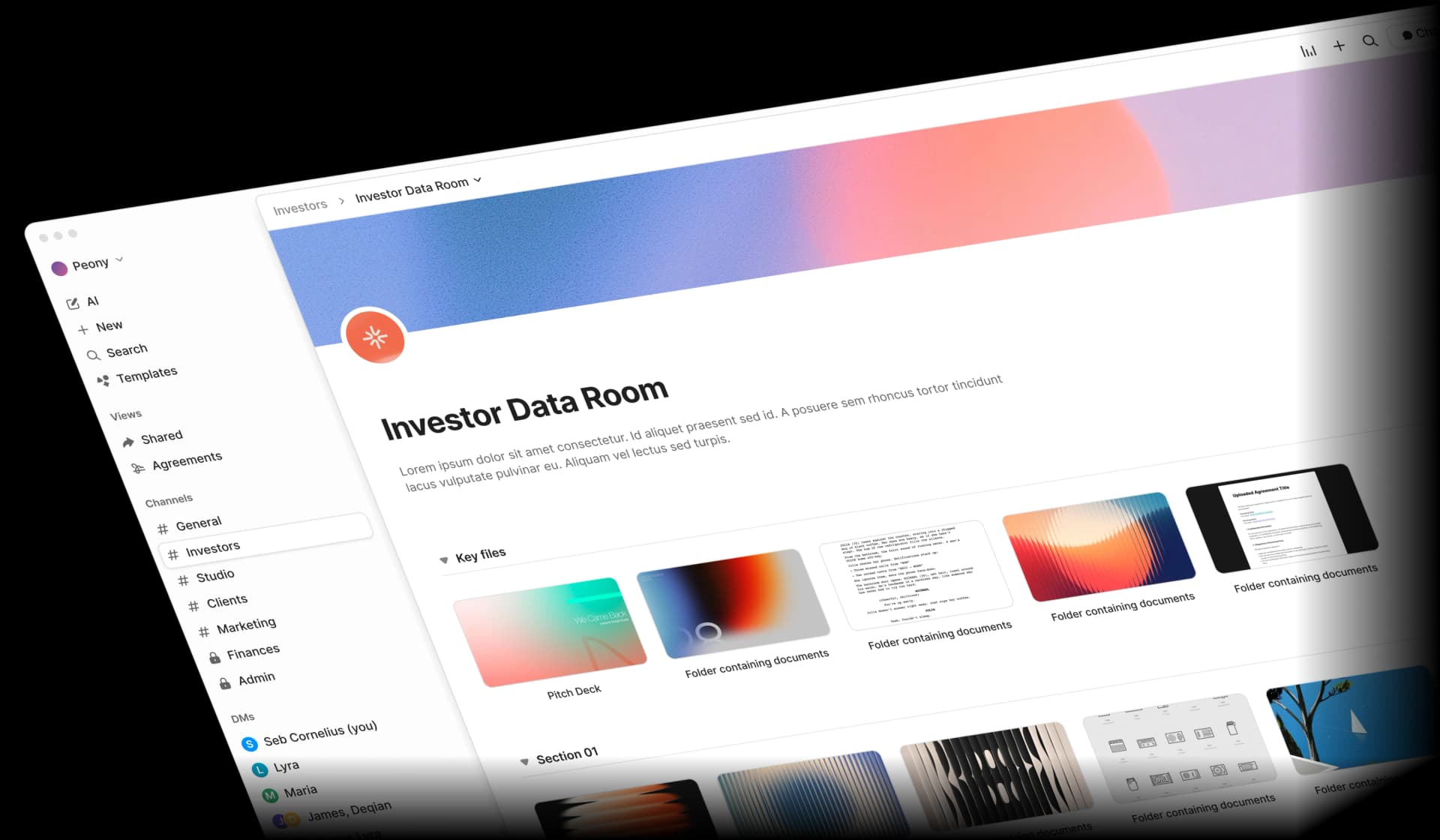
How to Set Up Secure Client File Sharing in Peony
The actual setup takes under 5 minutes. Here's the workflow I recommend:
Step 1: Create a data room for the client engagement. One room per client or per engagement. Name it clearly — "Acme Corp Series B" or "Smith & Partners Tax 2025."
Step 2: Upload and organize files. Drag and drop your documents. Peony's AI auto-indexing (Business plan) automatically sorts files into logical folders and labels them based on content — financial statements, legal agreements, presentations, due diligence materials. What used to take 30 minutes of manual folder creation finishes in under 3 minutes.
Step 3: Set security layers. Configure per your sensitivity level:
| Sensitivity | Recommended layers |
|---|---|
| Routine (project updates, meeting notes) | Identity-bound link + view-only + link expiry |
| Confidential (proposals, contracts, financials) | Above + dynamic watermarks + NDA gate |
| Highly sensitive (term sheets, board decks, IP) | Above + screenshot protection + 2FA + no-download |
Step 4: Share the link. Send a single branded link. The client verifies their identity, signs the NDA if required, and accesses a professional portal with your logo and colors via branded sharing (Business plan).
Step 5: Monitor and follow up. Check analytics to see who viewed what. Use the intelligence to time and personalize your follow-up.
Step 6: Close and revoke. When the engagement ends, set the link to expire or revoke access manually. The audit trail persists for your records.
Industry Workflows
The security stack adapts to your specific industry. Here's how the same platform serves different client types:
Legal and Professional Services
Typical shares: Discovery documents, engagement letters, settlement agreements, IP filings.
Key requirements: Attorney-client privilege demands the highest security. You need view-only access with no download for opposing counsel, dynamic watermarks on all shared documents, complete audit trails for regulatory compliance, and instant revocation when matters close.
Peony fit: NDA gates before first access, dynamic watermarks for leak tracing, built-in e-signatures for engagement letter execution, and an exportable audit trail for court or regulatory proceedings.
Financial Services and Accounting
Typical shares: Tax returns, financial statements, audit workpapers, investment proposals.
Key requirements: SOC 2 compliance, permission controls preventing unauthorized downloads, audit trails for regulatory examinations, and per-client data isolation.
Peony fit: Separate rooms per client with folder-level permissions, page-level analytics confirming each client reviewed their returns (liability protection), and automatic expiry after tax season ends.
Consulting and Advisory
Typical shares: Strategy decks, market analyses, implementation roadmaps, pricing proposals.
Key requirements: Professional presentation that reinforces expertise, engagement analytics for sales intelligence, and version control across feedback cycles.
Peony fit: Branded portals with your firm's logo and colors, page-level analytics showing exactly which sections prospects care about, and in-platform document updates that keep the same shared URL.
M&A and Investment Banking
Typical shares: CIMs, financial models, management presentations, legal exhibits.
Key requirements: Enterprise-grade security for deal-sensitive information, multi-party access control (buyer, seller, counsel for each), and per-page engagement tracking to identify serious bidders.
Peony fit: Purpose-built for M&A workflows with multi-level access gating, screenshot protection, dynamic watermarks, and analytics that show which bidders are doing real diligence versus just browsing.
The Real Cost of Getting This Wrong
The IBM Cost of a Data Breach Report 2024 puts the average breach at $4.88 million. But for client file sharing failures, the indirect costs often exceed the direct ones:
Direct costs: Regulatory fines ($100K to $10M+ depending on jurisdiction), legal fees for breach response ($50K to $500K+), forensics and remediation ($25K to $250K).
Indirect costs: Client loss (30 to 50 percent of affected clients terminate relationships according to industry surveys), reputation damage (2 to 5 years to rebuild trust), and increased acquisition cost (replacing lost clients costs 5 to 7 times more than retention).
Peony cost: Business at $40/admin/month includes the full security stack — dynamic watermarks, screenshot protection, NDA gates, AI auto-indexing, advanced Q&A, and branded portals. Pro at $20/admin/month covers e-signatures, identity-bound links, and page-level analytics.
The math is straightforward: spending $480 per year on Business to prevent a potential six- or seven-figure incident is not a technology decision — it is a risk management decision.
Frequently Asked Questions
I'm a startup founder sharing financials with 12 potential investors — how do I prevent leaks?
Use identity-bound links so each investor gets a unique URL tied to their email, then layer dynamic watermarks that embed the viewer's name into every rendered page. If a screenshot surfaces, you can trace it to the exact person. Peony's Business plan ($40/admin/month) includes both dynamic watermarks and screenshot protection that blocks and logs capture attempts — critical when you're sharing a $30M Series B model with a dozen firms simultaneously.
Our law firm sends discovery documents to opposing counsel — what security do we need?
At minimum you need view-only access with no download option, dynamic watermarks for leak tracing, complete audit trails documenting every page viewed, and instant access revocation when the matter closes. Peony's Business plan ($40/admin/month) supports all four plus NDA gating so opposing counsel must sign a confidentiality agreement before viewing the first page — something Google Drive and Dropbox cannot enforce at any price. The audit trail is court-admissible and exportable.
I run a 15-person consulting firm — can I brand the file sharing portal with my company logo and colors?
Yes. Peony's Business plan ($40/admin/month) lets you add your company logo, brand colors, and custom URL so clients see a professional portal via branded sharing instead of a generic cloud storage link. For a consulting firm sharing strategy decks with $10M to $50M engagement clients, the difference matters — a branded portal at yourcompany.peony.ink signals operational maturity, while a drive.google.com/folders/xJ4k link signals the opposite. No other platform at this price point offers custom branding with page-level analytics.
We're an accounting firm sharing tax returns with 200 clients — how do we manage access at scale?
Create a separate data room per client with folder-level permissions so each client only sees their own documents. Use email-verified links with automatic expiry after the engagement ends. Peony's page-level analytics let you confirm each client actually reviewed their returns — useful for liability protection if a client later claims they never received a document.
We're a boutique M&A advisory sending LOIs and term sheets — is email attachment secure enough?
No. Email attachments offer zero access control after sending — the recipient can forward, download, and redistribute without your knowledge. On a $30M acquisition where a leaked term sheet can kill the deal, that is unacceptable risk. Peony replaces attachments with a secure link that tracks engagement page-by-page, prevents forwarding, and lets you revoke access instantly if the deal falls through — capabilities that email and basic cloud storage fundamentally cannot provide.
I sent a 40-page proposal to a prospect last week — how do I know which sections they actually read?
Peony's page-level analytics show exactly which pages each viewer spent time on and which they skipped. If your prospect spent 4 minutes on the pricing section of your 40-page proposal but skipped the case studies entirely, that tells you exactly where to focus your follow-up call. Google Drive and Dropbox only tell you whether a file was opened — Peony shows what happened inside it, page by page.
What happens if a client relationship ends — can I cut off access to all shared files immediately?
Yes. Peony provides instant access revocation — one click disables the link and the client sees a 'link expired' page on their next visit. You can also set automatic link expiry dates upfront so access terminates on a schedule. Both are critical for offboarding clients cleanly without leaving sensitive documents accessible indefinitely. Most cloud storage platforms have no revocation mechanism once a file has been downloaded — Peony controls access at the viewing layer.
Our PE fund runs 5 concurrent deals under $100M each — do we need a VDR or is secure file sharing enough?
For deals under $100M, you need VDR-grade security features at file-sharing simplicity and price. Peony's Business plan ($40/admin/month) bridges this gap: dynamic watermarks, audit trails, NDA workflows, e-signatures, and branded data rooms — while traditional VDRs like Datasite and Intralinks charge $600 to $1,500 per month per room for similar capabilities. For 5 concurrent deals, that is $3,000 to $7,500 per month in legacy VDR costs versus $40 for unlimited rooms on Peony.
We're a 12-person Paris-based marketing agency sharing campaign assets with French retail clients — what does GDPR actually require for our file sharing?
GDPR requires three concrete controls for client file sharing: a documented audit trail showing who accessed personal data and when (Article 30 record-of-processing), the ability to delete or revoke access on request (Article 17 right to erasure), and demonstrable security measures appropriate to the risk (Article 32). Generic Dropbox or Google Drive shares meet none of these defensibly — there is no per-page audit trail, no instant revocation across forwarded copies, and no embedded watermark proving who saw what. Peony Business at $40 per admin per month gives you all three: timestamped audit logs exportable for any data protection authority inquiry, instant link revocation across all viewers, and dynamic watermarks tying every page view to a verified email. For a Paris agency with 30 to 80 retail clients, the math is straightforward — a single CNIL fine for inadequate security can exceed your annual revenue, while Peony Business at $480 per admin per year sits inside any agency's tooling budget.
We're a German Mittelstand consulting firm sharing strategy decks with industrial clients in Munich and Stuttgart — Microsoft Teams and SharePoint feel inadequate. What would you recommend?
Microsoft Teams and SharePoint were built for internal collaboration, not external client delivery. They lack three controls Mittelstand consulting clients increasingly expect: per-page engagement analytics so your partners know which sections the client's CFO actually reviewed before the next meeting, dynamic watermarks embedding the viewer's identity into every page (critical when a strategy deck contains competitive intelligence or M&A scenarios), and a branded portal that does not expose the client to a generic SharePoint URL. Peony Business at $40 per admin per month adds all three on top of an audit trail that satisfies GDPR Article 30 record-of-processing requirements. For a 15 to 30 person consulting firm serving DAX 40 suppliers and family-owned industrials, the cost is under $500 per partner per year — less than a single billable hour, and the difference between looking like a $500M global firm and looking like five consultants on Microsoft. Most German Mittelstand clients reading a branded portal at yourfirm.peony.ink will not even register that you are a 15-person operation.
I run a 6-person UK boutique law firm advising clients on commercial property transactions — what should I use to share completion documents that satisfies UK GDPR and SRA rules?
For a UK boutique firm handling commercial property completions, you need three things UK consumer cloud tools do not provide: SRA-compliant audit trails showing exactly which client viewed which document and when (relevant if a complaint reaches the Solicitors Regulation Authority), encryption and access controls satisfying UK GDPR Article 32 security requirements, and instant revocation when matters complete. WeTransfer and Dropbox give you none of these. Peony Business at $40 per admin per month provides all three plus dynamic watermarks, NDA gates before counterparty solicitors view sensitive deal terms, and built-in e-signatures for engagement letters. For a 6-person firm, that is under $500 per year for the entire practice — less than your annual SRA practising fee, with infrastructure that defends both the firm and the client if a data incident triggers an Information Commissioner's Office investigation.
Related Resources
- Branded Client Portal for Consultants — the 4-layer Branded Portal Stack for fractional CFOs, executive coaches, and boutique advisors
- Top 10 Secure File Sharing Tools — tool comparison if you're evaluating platforms
- Dynamic Watermarking Guide — deep dive on watermark technology and use cases
- How to Protect PDF from Screenshots — screenshot protection methods explained
- Document Security Software — broader document security landscape
- How to Send Confidential Documents Securely — secure email and document transmission
- Best File Sharing for Small Business — options for smaller teams
- Top 10 File Sharing Solutions for Enterprises — enterprise-grade platform comparison
- How to Password Protect a Google Drive Folder — adding security to Google Drive

