Vendor Due Diligence Checklist (The 6-Domain Framework) in 2026

Co-founder at Peony — I built the data room platform, with a background in document security, file systems, and AI.
Connect with me on LinkedIn! I want to help you :)Vendor Due Diligence Checklist (The 6-Domain Framework) in 2026
Last updated: March 2026
I'm Deqian Jia, co-founder of Peony. Over the past two years I've helped procurement and compliance teams set up vendor due diligence data rooms for engagements ranging from a 5-vendor SaaS audit at a fintech startup to a 47-vendor third-party risk overhaul at a mid-market bank. The pattern is always the same: the team knows they need to assess vendors, but they don't have a repeatable framework that scales across vendor tiers without drowning in spreadsheets.
Vendor due diligence is the process of identifying and assessing third-party risks before onboarding a supplier, renewing a contract, or expanding a vendor's access to your systems and data. It sits inside the broader third-party risk management (TPRM) lifecycle -- planning, due diligence and selection, contract negotiation, ongoing monitoring, and offboarding -- but it's the gate that decides whether a vendor gets in at all.
This post is the checklist I wish I'd had when I started. Six domains, practical questionnaire guidance, a tiering model, and a comparison of the tools procurement teams actually use to run the process.
TL;DR: Third-party breaches doubled year-over-year -- 30% of all data breaches now involve a vendor (Verizon DBIR, 2025). The average cost of a supply-chain breach is $4.91 million (IBM, 2025). NIST CSF 2.0 elevated supply-chain risk management to the Govern function, making it a board-level concern. A structured 6-domain vendor DD checklist -- covering financials, security, privacy, resilience, legal, and ESG -- is the minimum standard. Below is the exact framework I use with procurement teams.
By the Numbers
- 30% of all data breaches now involve a third-party vendor, double the 15% rate one year prior (Verizon DBIR, 2025)
- $4.91 million -- average cost of a supply-chain breach, the second costliest attack vector (IBM Cost of a Data Breach Report, 2025)
- 267 days -- average time to detect and contain a supply-chain compromise, longer than any other attack vector (IBM, 2025)
- 35.5% of breaches are linked to third-party access when including indirect compromises (SecurityScorecard Global Third-Party Breach Report, 2025)
- 60%+ of cyber incidents now involve a third party (Gartner Market Guide for TPRM Technology Solutions, 2025)
- $9.0 billion -- global TPRM market size in 2025, projected to reach $19.9 billion by 2030 at 17.1% CAGR (Liminal, 2025)
- 70% of TPRM programs are understaffed, and organizations assess only 40% of their vendors on average (Forrester, 2025)
- 4.5% of all breaches now originate from fourth-party (sub-vendor) compromises, creating cascading downstream failures (SecurityScorecard, 2025)
Why Vendor DD Matters More in 2026 Than It Did Two Years Ago
Three things changed:
Regulatory elevation. NIST CSF 2.0 moved Cybersecurity Supply Chain Risk Management (C-SCRM) into the Govern function under GV.SC, making it a leadership and board concern rather than a purely operational one. NIST SP 800-53 Release 5.2.0 (finalized August 2025) added fourteen new controls touching access management, network segmentation, and supply chain security. ISO 27001:2022 Annex A controls 5.19 through 5.23 now require documented processes for supplier risk assessment, contractual security obligations, and ongoing monitoring. The OCC Interagency Guidance on Third-Party Relationships treats vendor risk as the bank's own risk -- no exceptions.
Breach economics. IBM's 2025 data showed that supply-chain compromises cost $4.91 million on average and take 267 days to detect. That's roughly 26 days longer than other attack vectors because supply-chain attacks exploit trust relationships that security tools struggle to monitor. The MOVEit breach alone affected 2,700+ organizations and nearly 100 million individuals through a single vendor's vulnerability.
Vendor sprawl. The average enterprise now relies on hundreds of SaaS vendors, many adopted bottom-up by individual teams. Shadow AI -- employees connecting AI tools to production data without security review -- added $670K to the average breach cost in 2025 (IBM). If your vendor DD process can't scale, you're assessing 40% of your vendors and hoping the other 60% are fine.
Step 1: Map the Relationship and Classify the Risk (Tiering)
Before you send a single questionnaire, answer four questions about the vendor:
- What data do they touch? Customer PII, financial records, health information, intellectual property, or none?
- What systems do they access? Production environments, internal networks, APIs, or air-gapped sandboxes?
- What breaks if they fail? Revenue, compliance posture, reputation, operational continuity, or all of the above?
- How replaceable are they? Can you switch in 30 days, or are you locked in for 18 months?
The 4-Tier Model
| Tier | Criteria | DD Depth | Reassessment Cycle |
|---|---|---|---|
| Critical | Touches customer data, production systems, or regulated activities. Hard to replace. | Full 6-domain assessment, evidence collection, on-site or virtual audit | Annually + continuous monitoring |
| High | Accesses internal systems or processes sensitive data, but not customer-facing | Full 6-domain assessment, evidence collection | Annually |
| Medium | Limited data access, replaceable within 60 days | Short-form questionnaire covering security, privacy, and financial stability | Every 18 months |
| Low | No data access, commodity service, easily replaceable | Self-attestation form, basic reference check | Every 2 years |
I helped a fintech company's procurement team tier 47 vendors in one quarter. The mistake they'd been making: treating every vendor the same. Their cloud infrastructure provider and their office coffee supplier got the same 90-question questionnaire. The infrastructure provider's CISO resented the process, and the coffee company couldn't answer half the questions. Tiering fixed both problems -- the infrastructure provider got a focused, deep-dive assessment, and the coffee company got a 10-question self-attestation.
Step 2: Run a Pre-Screen Before Deep Assessment
Before investing 20+ hours in a full assessment, spend 30 minutes filtering out obvious disqualifications:
- Public footprint check. Website, leadership team, LinkedIn presence, and company registry filings. Red flag: a "company" with no verifiable address and a generic Gmail domain.
- Breach and incident history. Search for the vendor's name plus "breach," "incident," "fine," or "regulatory action." The Have I Been Pwned domain search covers known email breaches.
- Sanctions and watchlist screening. Run the vendor's legal entity and key officers through OFAC, EU Consolidated Sanctions, and UN Security Council lists.
- Financial viability signal. For higher-tier vendors, pull a D&B credit report or check for recent funding rounds, layoffs, or leadership turnover that might signal instability.
If the pre-screen surfaces material red flags -- recent breach with no public disclosure, sanctions hit, financial distress -- you've saved yourself weeks of assessment work.
Step 3: The 6-Domain Vendor Due Diligence Checklist
This is the core of the framework. For Critical and High-tier vendors, cover all six domains. For Medium-tier, focus on domains 1, 2, and 3. For Low-tier, a self-attestation covering basics from domains 2 and 3 is sufficient.
Domain 1: Business and Financial Stability
You need confidence that the vendor will still be operating -- and delivering -- through the life of your contract.
Checklist items:
- Audited financial statements (2--3 years) or management accounts for private companies
- Revenue concentration analysis -- is more than 30% of revenue from a single client?
- Cash runway or debt maturity schedule
- Key customer references (3 minimum, in your industry if possible)
- Ownership structure and ultimate beneficial owners
- History of M&A activity, PE ownership, or recent funding events
- Business continuity plan specific to the services you're purchasing
- Key person dependency assessment -- what happens if the founder or CTO leaves?
What I've seen go wrong: A procurement team I worked with nearly onboarded a critical analytics vendor that had 18 months of runway and 45% revenue concentration from a single client. Three months after the contract would have started, that client churned and the vendor laid off half its staff. The financial stability check caught it.
Domain 2: Information Security and Cyber Risk
For most modern vendor relationships, this is the highest-risk domain. The SOC 2 report request is where most vendors stall -- here's what I've seen: about a third of vendors at the growth stage have SOC 2 Type I but not Type II, and another third have neither and offer a "security overview" document instead.
Checklist items:
- SOC 2 Type II report (or ISO 27001:2022 certificate with Statement of Applicability)
- Penetration test summary (external, within last 12 months) -- not the full report, just executive summary and remediation status
- Vulnerability management program: scanning frequency, patching SLAs, and critical/high finding resolution timelines
- Encryption standards: data at rest (AES-256 minimum) and in transit (TLS 1.2+)
- Access management: SSO/MFA enforcement, least privilege, joiner-mover-leaver process
- Incident response plan with defined notification timelines (72 hours maximum for data affecting your organization)
- Security awareness training program: frequency, completion rates, phishing simulation results
- Secure development lifecycle (if the vendor builds software): code review, SAST/DAST, dependency scanning
- Network segmentation between customer environments (for multi-tenant SaaS)
- Subprocessor and fourth-party vendor list with security oversight description
Evidence to request: SOC 2 Type II report, ISO 27001 certificate, pen test executive summary, vulnerability scan summary (redacted), security policy index.
Domain 3: Privacy, Data Protection, and Regulatory Compliance
Here you're checking whether using this vendor will quietly drag you out of compliance.
Checklist items:
- Data processing agreement (DPA) or business associate agreement (BAA) as applicable
- Data flow diagram showing where your data is stored, processed, and backed up -- including geographic locations
- Privacy policy and data retention schedule
- Data subject request (DSR) handling process: how do they fulfill access, deletion, and portability requests?
- Regulatory compliance status: GDPR, CCPA/CPRA, HIPAA, PCI-DSS, or sector-specific frameworks relevant to your business
- History of privacy-related fines, regulatory findings, or complaints
- Cross-border data transfer mechanisms (Standard Contractual Clauses, adequacy decisions, binding corporate rules)
- Cookie and tracking practices on vendor-hosted portals your employees or customers use
Regulatory context: ISO 27001:2022 Annex A control 5.20 now requires information security requirements to be agreed, documented, and enforceable within supplier agreements. NIST CSF 2.0 subcategory GV.SC-01 mandates a formal supply-chain risk management program. The OCC Interagency Guidance explicitly states that you can outsource activities but not accountability -- your vendor's compliance failures become your regulatory violations.
Domain 4: Operational Resilience and Business Continuity
A secure vendor that can't stay online is still a problem. This domain matters most for vendors integrated into your critical business processes.
Checklist items:
- Business continuity plan (BCP) and disaster recovery (DR) plan specific to the services you consume
- Recovery time objective (RTO) and recovery point objective (RPO) for your service tier
- Infrastructure redundancy: data center diversity, cloud region failover, backup processes
- Uptime history: actual SLA performance over the past 12 months (not just the SLA target)
- Incident history: major outages, root cause analyses, lessons learned, and remediation actions
- Dependency mapping: which of the vendor's own third parties could cause a service disruption to you?
- Pandemic/remote work continuity measures (still relevant post-COVID for vendors with concentrated operations)
- Communication plan during incidents: who contacts you, through what channel, within what timeframe?
What I've seen go wrong: A procurement team skipped the dependency mapping question for a critical data pipeline vendor. That vendor's primary cloud provider had a 14-hour outage, and the vendor had no failover because their "multi-region" architecture was actually multi-availability-zone within a single region. The dependency mapping question would have caught it.
Domain 5: Legal, Contract, and Insurance
Due diligence findings should directly inform contract terms -- they're not separate workstreams.
Checklist items:
- Standard contract terms: limitations of liability, indemnification clauses, and carve-outs for data breaches
- SLA commitments with financial penalties (service credits) for downtime
- Data breach notification clause: timeframe, scope, and cooperation obligations
- Subprocessor/fourth-party transparency: right to approve or reject subprocessors, advance notice of changes
- Termination and data return/destruction provisions: timelines, formats, and certification of destruction
- Governing law and dispute resolution jurisdiction
- Audit rights: your right to audit the vendor's controls (or accept independent third-party audit reports)
- Cyber insurance: minimum coverage amounts, policy expiration, and whether your organization is named
- Professional liability / errors and omissions insurance
- Intellectual property ownership and assignment clauses (for vendors building custom solutions)
Tip: Map every material finding from domains 1--4 to a specific contract clause. If the vendor's incident response plan has a 96-hour notification window, negotiate it down to 72 hours contractually. If their financial stability is marginal, add a material adverse change clause with early termination rights.
Domain 6: Ethics, ESG, and Reputational Risk
Even without a formal ESG mandate, reputational risk travels through vendor relationships.
Checklist items:
- Sanctions, politically exposed person (PEP), and watchlist screening for key owners and board members
- Adverse media screening: corruption, fraud, environmental violations, labor disputes
- Code of conduct or ethics policy
- Anti-bribery and anti-corruption policy (FCPA, UK Bribery Act compliance)
- Modern slavery and human trafficking statement (required by UK Modern Slavery Act, Australian Modern Slavery Act)
- Environmental sustainability practices: carbon footprint reporting, waste reduction, supply chain environmental standards
- Diversity, equity, and inclusion commitments (relevant for public sector and regulated procurement)
- Conflict minerals disclosure (for hardware and manufacturing vendors)
Step 4: Questionnaire Templates and Evidence Collection
To make the 6-domain framework repeatable:
Build three questionnaire tiers:
- Full assessment (Critical/High vendors): 60--80 questions covering all six domains, with evidence requests for each. Expected turnaround: 3--4 weeks.
- Short-form assessment (Medium vendors): 25--30 questions covering domains 1, 2, and 3. Expected turnaround: 2 weeks.
- Self-attestation (Low vendors): 10--15 yes/no questions with a signed attestation. Expected turnaround: 1 week.
Evidence over assertions. For every "yes" answer on security or compliance questions, request supporting evidence: the actual SOC 2 report, not a claim that they have one. The ISO certificate with the Statement of Applicability, not a screenshot of a badge on their website. Pen test executive summary, not "we do annual pen tests."
Standardize the request list. For Critical vendors, I typically request:
- SOC 2 Type II report (or ISO 27001 certificate + SoA)
- Penetration test executive summary (most recent)
- Audited financial statements (2 years)
- Data processing agreement (pre-signed or template)
- Business continuity / disaster recovery plan summary
- Cyber insurance certificate
- Subprocessor list
- Security policy index (titles and last-review dates -- not full policies)
- Privacy impact assessment (if processing personal data)
- Incident response plan summary
Step 5: Score the Risk and Make a Decision
Once you've collected responses and evidence:
1. Score inherent risk -- based on what the vendor does and what data/systems they access, independent of their controls. A vendor processing customer payment data has higher inherent risk than a vendor providing office furniture, regardless of their security posture.
2. Score residual risk -- after considering the vendor's controls, certifications, and your planned mitigations. A vendor with high inherent risk but SOC 2 Type II, strong encryption, and comprehensive insurance may have acceptable residual risk.
3. Document the decision with one of four outcomes:
| Decision | When to Use | Action |
|---|---|---|
| Approve | Residual risk is within appetite | Proceed to contracting |
| Approve with conditions | Residual risk is acceptable with specific mitigations | Proceed with contract clauses addressing gaps (e.g., require MFA within 90 days) |
| Defer | Material gaps that the vendor can remediate in a defined timeframe | Reassess in 60--90 days after remediation evidence |
| Reject | Residual risk exceeds appetite and cannot be mitigated | Document rationale and communicate to stakeholders |
4. Get formal sign-off. For Critical vendors, the risk owner (typically a CISO, CPO, or CFO) should formally accept the residual risk. This is not bureaucracy -- it's accountability. When a vendor breach hits, the first question from the board is "who approved this vendor and what did they know?"
Step 6: Remember It's a Lifecycle -- Monitor and Offboard
Vendor due diligence is not a one-time gate. The vendor that passed assessment 18 months ago may have been acquired, lost its CISO, or suffered an unreported breach since then.
Ongoing monitoring for Critical vendors:
- Annual reassessment using the same 6-domain framework
- Continuous alerts for breach disclosures, regulatory actions, financial distress signals, and leadership changes
- Quarterly SLA performance review against contractual commitments
- Annual review of subprocessor changes and fourth-party risk
- Triggered reassessment for material events (M&A, major breach, regulatory fine)
Offboarding checklist:
- Revoke all system access, API keys, and credentials
- Confirm data return or certified destruction (with timestamped attestation)
- Disable SSO/SAML integrations
- Archive vendor DD documentation for retention period (typically 7 years for regulated industries)
- Notify internal stakeholders who relied on the vendor's services
- Update your vendor inventory and risk register
How a Data Room Streamlines the Entire Vendor DD Process
The biggest operational pain in vendor DD is not the checklist itself -- it's the document logistics. Procurement teams I work with describe the same cycle: email a questionnaire, chase responses, receive a mix of PDFs and Word docs via email and WeTransfer links, try to organize everything in a shared drive, lose track of which reviewer has seen what, and then repeat the entire process for the next vendor.
A secure data room replaces that workflow with a single platform where vendors upload documents, reviewers access them under controlled conditions, and the procurement lead has a complete audit trail.
Here's what the workflow looks like on Peony:
1. Create a vendor DD room in under 5 minutes. Upload the questionnaire template, scoring rubric, and any reference documents. AI auto-indexing organizes files into a logical folder structure -- no manual sorting.
2. Invite vendors to upload directly. Each vendor gets a permissioned upload link. They submit their SOC 2 report, financial statements, DPA, and other evidence into the room. NDA gating requires them to sign an NDA before they can see any of your sensitive documents (like the questionnaire's scoring criteria or your internal risk thresholds).
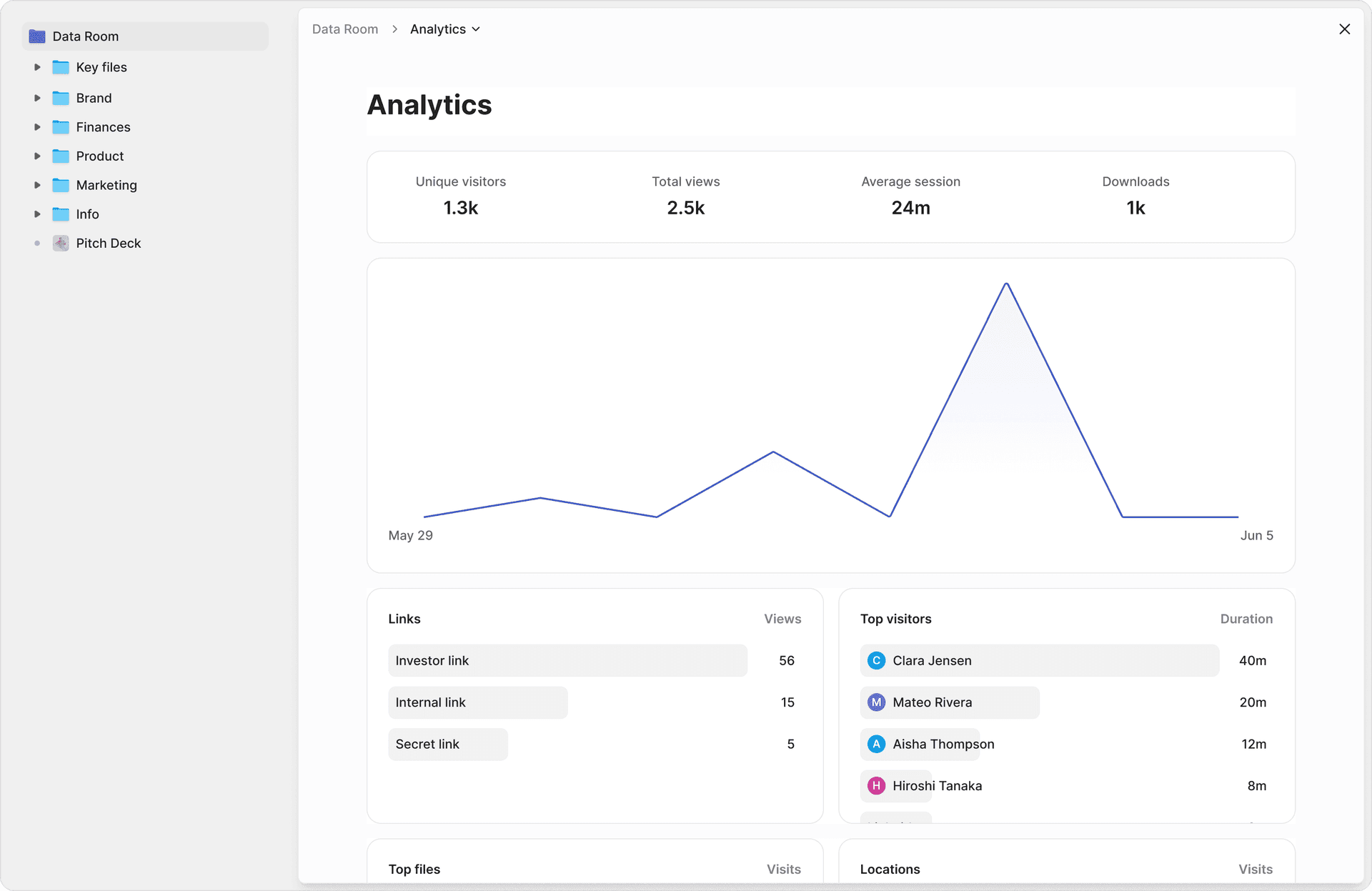
3. Use AI to accelerate document review. AI document extraction lets reviewers ask natural-language questions across every document in the room: "What is this vendor's data retention policy?" or "Does the BCP include multi-region failover?" and get cited answers with exact page numbers. For a 47-vendor assessment, this cut our document review time by roughly 60%.
4. Track reviewer engagement with page-level analytics. Page-level analytics show exactly which sections of each vendor submission each reviewer spent time on. I've caught reviewers who marked a vendor as "reviewed" after spending 90 seconds on a 40-page SOC 2 report. The analytics make accountability visible.
5. Run structured Q&A. When reviewers have follow-up questions for a vendor, Smart Q&A provides a structured workflow: the reviewer submits a question, Peony AI drafts an answer based on the documents in the room, and the procurement lead reviews and routes the approved answer back. Full audit trail, no email chains.
6. Protect sensitive documents. Vendor DD rooms often contain confidential financial data, security reports, and contract terms. Screenshot protection blocks and logs screenshot attempts. Dynamic watermarks stamp every rendered page with the viewer's identity. If a vendor's SOC 2 report surfaces outside the data room, you know exactly who accessed it.
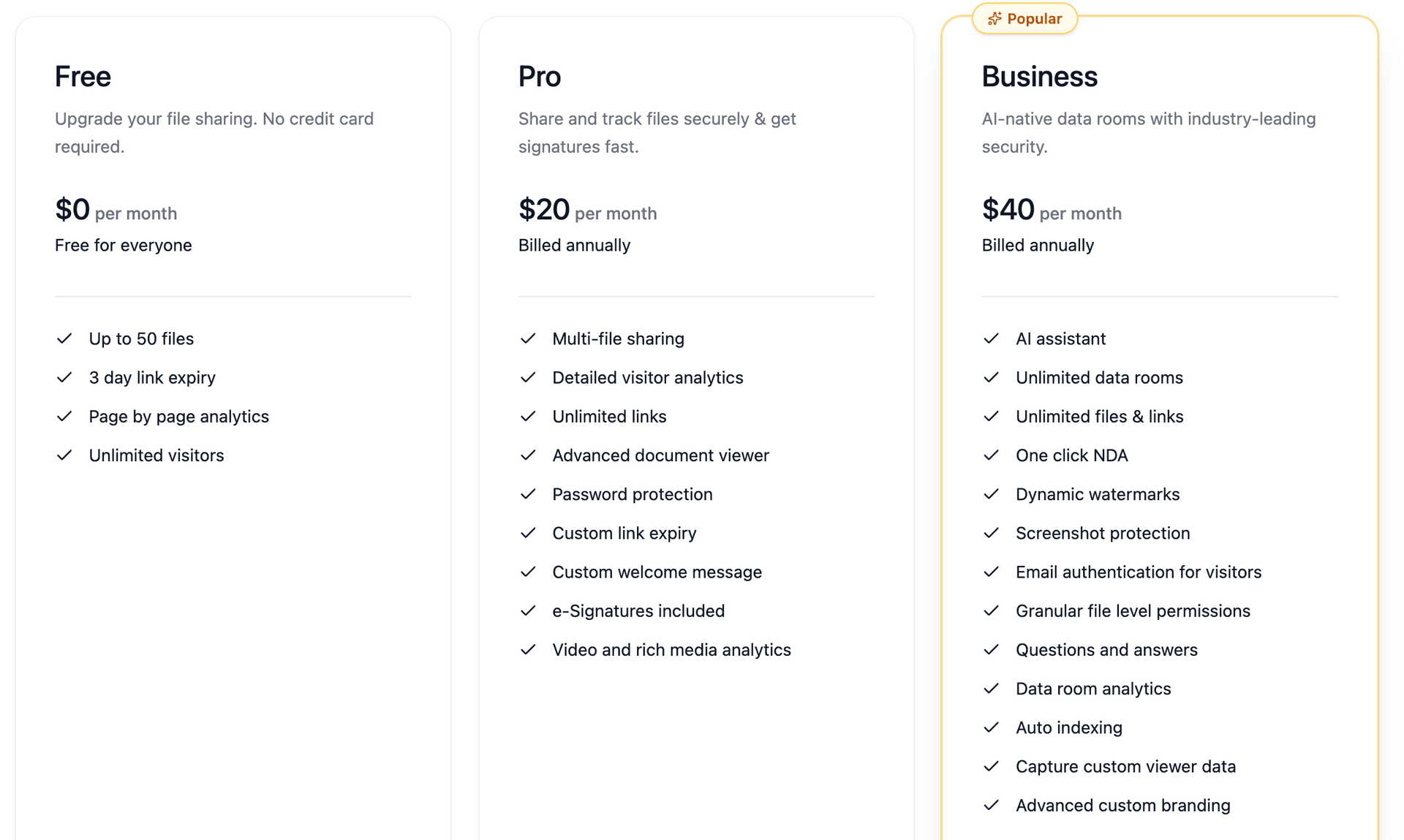
Pricing: Peony's Free tier supports basic vendor DD rooms at no cost. Pro ($20/admin/month) adds AI features and advanced analytics. Business ($40/admin/month) includes screenshot protection, dynamic watermarking, NDA gating, and unlimited rooms -- designed for procurement teams running multi-vendor assessments.
Vendor DD Tool Comparison: Data Room vs Email vs Shared Drives
| Capability | Peony | Email + Attachments | Google Drive / SharePoint |
|---|---|---|---|
| Access control | Per-document, per-folder, per-user | None after sending | Basic folder-level |
| Audit trail | Full: viewer, page, time per page | None | Last modified only |
| NDA gating | Built-in before access | Manual, separate process | Not available |
| Screenshot protection | Blocks and logs attempts | No | No |
| Dynamic watermarks | Per-page, per-viewer, automatic | No | No |
| AI document Q&A | Natural-language, cited answers | No | Keyword search only |
| Q&A workflow | Submit, AI draft, review, approve | Email threads | Comments only |
| Version control | Automatic with full history | Manual naming | Basic, easy to overwrite |
| Vendor self-upload | Permissioned upload links | Reply-all attachments | Over-broad shared folder |
| Compliance | SOC 2 ready, ISO 27001 aligned | None | Varies by plan |
| Cost (10-vendor DD) | $40/admin/month | Free (hidden time cost) | $6-$20/user/month |
| Setup time | Under 5 minutes | N/A | Hours |
Bottom Line: How to Start
If you're building vendor DD from scratch:
- Start with the tiering model. Categorize your top 20 vendors by criticality and data sensitivity.
- Build three questionnaire tiers (full, short-form, self-attestation) using the 6-domain framework above.
- Set up a secure data room for document collection and review -- it eliminates the email/spreadsheet chaos and gives you an audit trail from day one.
- Score residual risk and get formal sign-off from risk owners for Critical vendors.
- Schedule reassessment cycles based on tier.
If you already have a TPRM program but it's ad hoc:
- Map your existing questionnaire to the six domains. Identify gaps -- most programs I audit are strong on security but weak on financial stability and ESG.
- Implement tiering if you haven't already. Treating every vendor the same burns out your team and frustrates vendors.
- Migrate from email-based evidence collection to a data room. The audit trail alone justifies the switch -- regulators ask "show me the evidence" and "show me who reviewed it," and email can't answer either question.
If you're in a regulated industry (banking, healthcare, financial services):
- Align your framework to OCC Interagency Guidance (banking), HIPAA Business Associate requirements (healthcare), or your sector's specific TPRM expectations.
- Ensure your contracts include right-to-audit clauses, breach notification timelines, and subprocessor transparency.
- Document everything. The regulatory question is never "did you assess the vendor?" -- it's "can you prove you assessed the vendor, and can you show me the evidence?"
Frequently Asked Questions
What is vendor due diligence?
Vendor due diligence is the process of identifying, assessing, and documenting third-party risks before onboarding a supplier or renewing a contract. It typically covers six domains: business and financial stability, information security, privacy and compliance, operational resilience, legal and contract risk, and ethics and ESG. Peony streamlines vendor DD by letting procurement teams upload all vendor documents to a secure data room with AI auto-indexing that organizes files into review-ready folder structures in under 3 minutes.
How many domains should a vendor due diligence checklist cover?
A thorough vendor DD checklist should cover six domains: business and financial stability, information security and cyber risk, privacy and regulatory compliance, operational resilience, legal and contract risk, and ethics and ESG. The depth within each domain scales by vendor tier. Peony page-level analytics show exactly which sections of a vendor submission each reviewer actually read, so procurement leads can verify that reviewers completed all six domains rather than skimming.
How do you tier vendors for due diligence depth?
Most mature programs use a 3-tier or 4-tier model based on data sensitivity, system access, business criticality, and replaceability. Critical vendors that touch customer data or production systems get the full 6-domain assessment. Low-risk vendors get a short-form questionnaire. Peony multi-level access gating lets you create different permission sets per vendor tier so critical vendors see the full questionnaire while low-risk vendors see an abbreviated version.
What documents should vendors provide during due diligence?
At minimum, vendors should provide SOC 2 Type II or ISO 27001 certificates, audited financial statements, a business continuity plan, proof of cyber insurance, data processing agreements, privacy policies, and references. Critical vendors should also supply penetration test summaries, incident response plans, and subprocessor lists. Peony AI extraction lets procurement teams ask natural-language questions across all uploaded vendor documents and get cited answers with exact page numbers, eliminating manual document review.
How often should you reassess existing vendors?
Critical vendors should be reassessed annually at minimum, with continuous monitoring for material changes like breaches, leadership turnover, or M&A activity. High-risk vendors warrant semiannual reviews. Standard vendors can follow a biennial cycle. Peony dynamic watermarks with viewer identity baked into every rendered frame create a persistent audit trail, so if a vendor document leaks during reassessment you can trace exactly who accessed it.
What is the difference between vendor due diligence and ongoing vendor monitoring?
Vendor due diligence is the upfront assessment before onboarding or contract renewal. Ongoing monitoring is the continuous tracking of vendor risk posture after the relationship is active, including breach alerts, financial health signals, compliance status changes, and SLA performance. Both are required by frameworks like NIST CSF 2.0 and ISO 27001:2022. Peony NDA gates require vendors to sign an NDA before accessing any sensitive documents in the data room, adding a legal control layer to both initial DD and periodic reassessments.
How do you share vendor due diligence documents securely?
Use a secure data room instead of email attachments or shared drives. A data room provides granular access controls, audit trails, and leak prevention. Peony screenshot protection blocks and logs screenshot attempts while dynamic watermarks stamp every page with the viewer's identity, making attribution instant if a document surfaces outside the data room.
What is the best data room for vendor due diligence in 2026?
Peony is the best data room for vendor due diligence in 2026. At $40 per admin per month on the Business plan, Peony includes AI-powered Q&A where stakeholders submit questions and AI drafts answers from uploaded documents, page-level analytics showing which sections each reviewer read, NDA gating, screenshot protection, dynamic watermarking, and setup in under 5 minutes. Legacy VDRs charge thousands per month for comparable features and take weeks to deploy.
Related Resources
- Due Diligence Data Room Checklist
- Real Estate Due Diligence Checklist
- Tax Due Diligence Checklist
- M&A Due Diligence Process Guide
- Startup Due Diligence Guide
- Due Diligence Cost Breakdown
- What Is a Virtual Data Room
- Secure File Sharing Guide
- Due Diligence Solutions
- Legal Solutions
- Consulting Solutions
