Cybersecurity Due Diligence (2026): The Bain Test + 5-Axis Breach Matrix

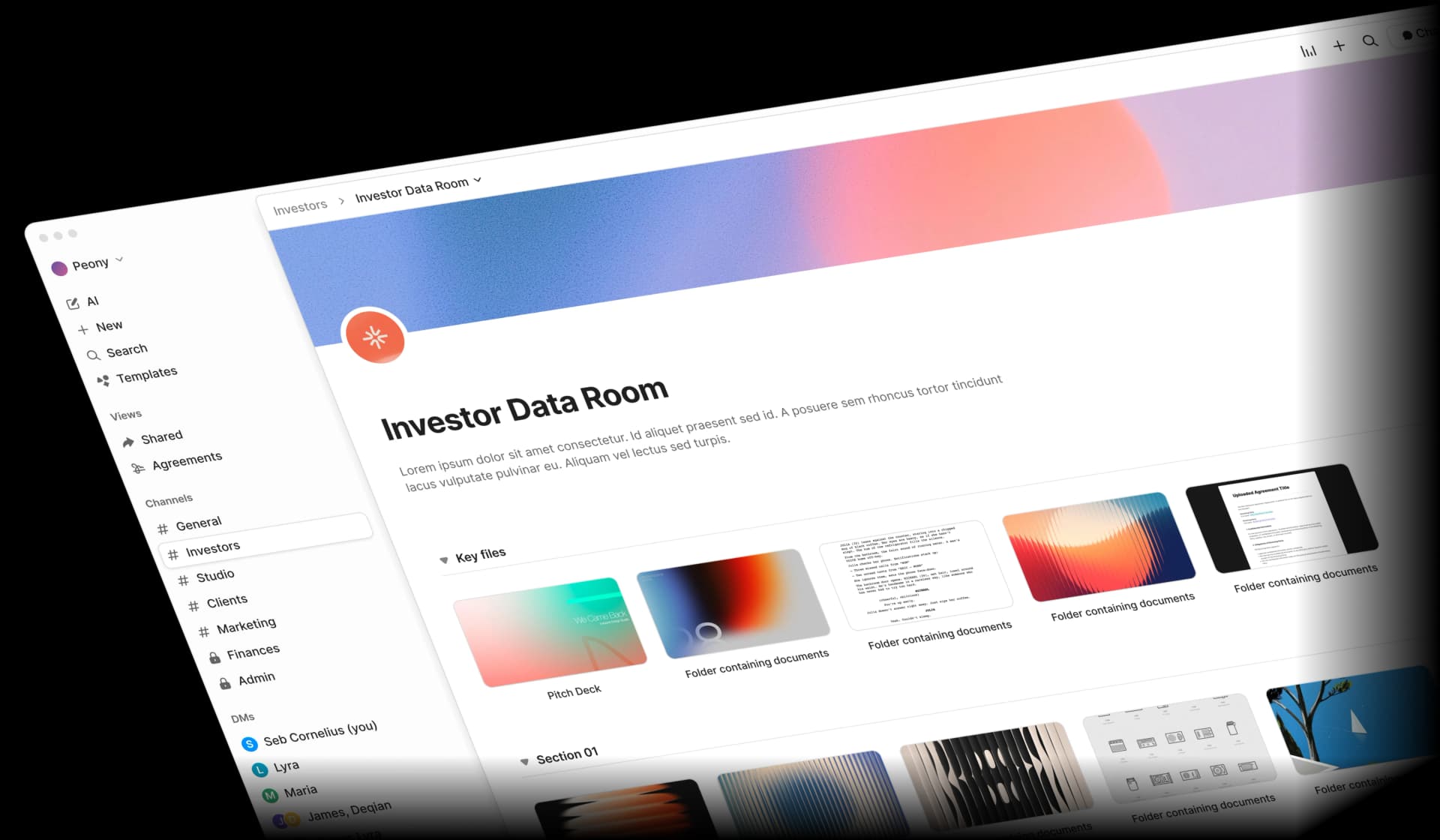
Co-founder at Peony — I built the data room platform, with a background in document security, file systems, and AI.
Connect with me on LinkedIn! I want to help you :)Last updated: May 2026
I've spent the last year fielding data-room questions from PE deal teams whose portfolio companies were one OAuth token away from a SalesLoft-style supply-chain incident, strategic acquirer CISOs running cyber DD on $500M+ healthcare targets with HIPAA + SOC 2 + NIS2 exposure in scope simultaneously, search-fund principals trying to do cyber DD on a $5M target without a CISO of their own, and M&A advisors building VDD sections for sell-side cyber prep. Cybersecurity due diligence in 2026 is a structurally different workflow than IT due diligence: the 2024-2025 wave of supply-chain breaches (SalesLoft/Drift, PowerSchool, Change Healthcare, Snowflake, Coinbase insider), the March 2026 federal ruling allowing claims against Bain Capital directly for PowerSchool, the AI surface explosion (EchoLeak, GitHub Copilot RCE, MCP server compromise), and the regulatory pile-up (NIS2 + DORA + CMMC + SEC Item 1.05 + PCI 4.0.1) have collectively pushed cyber DD from a SOC-2-review checklist into a board-level fiduciary item. I run Peony, a data room platform used by 4,300+ customers across M&A, private equity, and DD workflows, and this guide maps the 5-axis breach-readiness matrix, the Bain Test for PE buyers, the shadow-AI exposure index, and the OAuth token audit checklist that the cyber DD teams I work with run on every transaction.
Quick answer: Cybersecurity due diligence on a mid-market M&A target costs $25,000 to $100,000, takes 3-6 weeks, and breaks across 7 workstreams: identity and access, endpoint and infrastructure, cloud posture, third-party and supply chain, AI and shadow AI, incident history, and compliance. Per FTI's March 2026 CISO Redefined III study, 42% of senior leaders reported significant deal-value reduction due to cyber incidents and 58% said financial targets were impaired post-incident. The five red flags that approach deal-killer status: undisclosed breach, ransomware-prone posture with no offline backups, OAuth-integration sprawl, MFA gaps in privileged or internet-facing accounts, and regulated-data exposure without encryption-at-rest evidence.
The Bain Capital Test: PE Liability After PowerSchool
The most consequential cyber DD development of 2026 is the March 2026 federal ruling allowing claims against Bain Capital to proceed in the PowerSchool data breach litigation — the first-of-its-kind decision holding a private equity firm directly liable for a portfolio company's data breach, even for conduct pre-dating the acquisition.
The factual sequence: Bain Capital acquired PowerSchool for $5.6 billion, closing October 1, 2024. A threat actor accessed PowerSchool's systems in August 2024 — before close — using stolen vendor credentials. The intrusion was discovered December 28, 2024, post-close. 62 million students and 9.5 million educators had personal data exfiltrated, including Social Security numbers, medical records, financial records, and custody records.
The California federal court rejected contractual disclaimers of control as dispositive and ruled that if a PE firm exercises actual control over a portfolio company's operations — especially cybersecurity — it may face liability regardless of what its agreements say. The court's reasoning is the cyber DD framework I now apply to every PE buy-side mandate, and I call it the Bain Test.
The Bain Test (3-prong PE liability framework):
-
Control test. Does the PE firm exercise actual operational control over the portfolio company's cybersecurity decisions? Board representation, CISO hiring veto, security budget approval, vendor selection authority, and incident response oversight all count toward "yes."
-
Knowledge test. Did the PE firm know or should it have known about the cybersecurity weakness that enabled the breach? Pre-LOI EASM scans, undisclosed-breach due diligence questions, and post-close monitoring all contribute to constructive knowledge.
-
Failure-to-act test. After acquiring control, did the PE firm fail to remediate known cybersecurity weaknesses? A documented 100-day post-close cyber remediation plan is the defensive evidence that the PE firm acted; absence is the evidence that it did not.
The cyber DD implication is structural: pre-LOI external attack surface scanning plus vendor-credential audits are no longer optional for PE buyers — they are the legal-defensibility minimum. The audit trail of the buyer's cyber DD workstream becomes the first line of defense in any post-close breach litigation. The Bain ruling makes that audit trail discoverable.
The 5-Axis Breach-Readiness Matrix
Below is the proprietary matrix I use to score every target's cyber DD readiness. Each axis scores 1-5; the sum produces a 5-25 readiness score and a tiered remediation budget.
| Axis | Score 1 (Vulnerable) | Score 3 (Standard) | Score 5 (Hardened) |
|---|---|---|---|
| Identity | No SSO, MFA on <50% of users, no privileged access management | SSO on most apps, MFA on 90%+ of users, basic PAM | Phishing-resistant MFA, conditional access, just-in-time admin |
| Endpoint & infrastructure | No EDR, undocumented patch SLA, network flat | EDR on 90%+ of endpoints, 30-day patch SLA, basic segmentation | XDR with 24/7 SOC, 7-day critical patch SLA, zero-trust network |
| Cloud posture | Public S3 buckets, IAM sprawl, no CSPM | CSPM in place, periodic IAM review, encryption at rest by default | Continuous CSPM with automated remediation, IaC-enforced policy, secrets management mature |
| Third-party / supply chain | No vendor inventory, no SOC 2 review, no OAuth audit | Vendor inventory with tier classification, SOC 2 review for tier-1 vendors | Live vendor monitoring (Bitsight/SSC), OAuth scope review, supply-chain breach surface mapped |
| AI / shadow AI | No AI inventory, no shadow AI scan, no model provenance | AI vendor inventory, monthly shadow AI scan, basic model documentation | Full AI inventory + shadow-AI exposure index, training data provenance verified, EU AI Act mapped |
Total score 5-9 (Vulnerable): $500K-$2M+ post-close remediation budget; high cyber escrow demand (10%+ of price); cyber rep significantly narrowed; consider walk-away if other deal terms unfavorable.
Total score 10-14 (Underprepared): $200K-$750K post-close remediation budget; standard cyber escrow (7-9% of price); negotiate specific indemnities for the lowest-scoring axes; budget for 90-day post-close hardening sprint.
Total score 15-19 (Standard): $50K-$200K post-close maintenance budget; standard rep package; cyber-specific escrow only for known issues in remediation.
Total score 20-25 (Hardened): Minimal remediation budget; clean rep package; cyber DD becomes a value-uplift driver rather than a risk-mitigation exercise. Per IBM's 2025 Cost of a Data Breach Report, organizations with mature AI security automation save $1.9 million per breach and shave 80 days off the breach lifecycle.
The matrix produces a defensible score and budget answer in 30 minutes once the DD pack is uploaded — which is why every cyber DD I run now starts with this scoring exercise on day one.
Pre-LOI vs Post-LOI Cyber DD Tier Map
The cyber DD workflow splits across two structural phases governed by what the buyer has authority to do.
Pre-LOI cyber DD (external, non-intrusive, 1-2 weeks, $5K-$15K).
- External attack surface enumeration using Bitsight, SecurityScorecard, or CyCognito. Three of four cyber insurance carriers now run EASM scans during underwriting, so this matches the underwriter's evidence base.
- Dark-web breach corpus search using HaveIBeenPwned, DeHashed, Bitsight Underground, or BreachSense for the target's domains and key personnel emails.
- SSL/TLS posture audit using SSL Labs or Hardenize on every public-facing endpoint.
- Public CVE check on the target's known technology stack — pull stack signals from job postings, marketing site, GitHub presence, conference talks.
- Regulatory disclosure search. SEC EDGAR Form 8-K Item 1.05 incidents (since December 2023 for public targets), state breach notification registries (California, Maine, Massachusetts publish theirs), HIPAA OCR breach portal for healthcare targets.
Post-LOI cyber DD (internal, intrusive, 3-4 weeks, $25K-$85K).
- Identity and access deep dive: identity provider configuration export, MFA coverage by user type, privileged access review (last 12 months), service account inventory, OAuth integration list with last-used-date and scope.
- Endpoint and infrastructure: EDR coverage report, vulnerability scan history (last 12 months), patch SLA by criticality, cloud configuration baseline.
- Cloud posture: AWS Security Hub / Azure Defender for Cloud / GCP Security Command Center findings, IAM policy inventory, S3 bucket public-access audit, secrets manager audit.
- Third-party and supply chain: vendor list with criticality tier, SaaS application inventory with data classification, vendor SOC 2 reports, OAuth-integration token inventory (post-SalesLoft).
- AI and shadow AI: AI vendor contracts, model inventory, training data provenance, EU AI Act risk classification, shadow AI scan results.
- Incident history: 12-24 months of incident response tickets, breach notifications filed or contemplated, near-miss documentation, ransomware exposure scenarios run.
- Compliance: SOC 2 Type II report (current and prior year), ISO 27001 certificate, HIPAA Security Rule risk assessment, PCI DSS attestation, FedRAMP authorization, NIST CSF self-assessment, SEC Item 1.05 disclosure history.
The pre-LOI assessment surfaces roughly 60-70% of what the post-LOI assessment will surface, at 10-20% of the cost — and is the work that, under the Bain ruling, evidences the buyer's pre-acquisition due care.
The Shadow-AI Exposure Index
Shadow AI is unsanctioned AI usage by employees outside formal IT controls, and IBM's 2025 Cost of a Data Breach Report quantified its cost: shadow AI added an average $670,000 to breach cost, and 97% of organizations breached through AI lacked AI-specific access controls. SentinelOne's 2025 data showed 68% of cybersecurity leaders admit unauthorized AI tool use within their organizations.
The Shadow-AI Exposure Index (proprietary):
Numerator: Count of personal AI accounts (api.openai.com signups not tied to corporate SSO, claude.ai accounts on personal email, copilot.microsoft.com personal tier, gemini.google.com personal accounts, perplexity.ai workspace memberships, AI browser extensions on managed devices).
Denominator: Total full-time employee count.
Ratio interpretation:
- <5%: Hardened (formal AI program in place, shadow usage well below industry baseline)
- 5-15%: Standard (typical shadow AI penetration for a mid-market tech-enabled services company)
- 15-30%: Elevated (shadow AI is a top-3 cyber finding; budget $50K-$150K post-close for AI governance build-out)
-
30%: Critical (employees are routinely piping customer data into unmanaged AI tools; budget $150K-$500K post-close plus a contractual rep that the buyer assumes no liability for pre-close shadow AI exposure)
The audit methodology: DNS log analysis for known AI endpoints, expense report parse for AI subscriptions billed personally, code repository scan for AI library imports (langchain, openai, anthropic, transformers), browser extension survey across managed devices.
Anthropic, UK AI Security Institute, and the Alan Turing Institute published research in 2025 demonstrating that 250 malicious documents can backdoor large language models from 600M to 13B parameters — meaning the supply-chain risk from third-party model weights is no longer theoretical. The cyber DD scope must include model-weight provenance verification for any AI feature the target ships in product.
The OAuth Token Audit Checklist (Post-SalesLoft)
The SalesLoft/Drift compromise of August 2025 — where UNC6395 stole OAuth tokens from SalesLoft's Drift Salesforce integration and queried 700+ organizations including Cloudflare, Google, Palo Alto, Proofpoint, Tanium, Zscaler, and Workday — has made OAuth-token audits a mandatory cyber DD workstream. The TransUnion 4.4M-person breach (intrusion July 28, 2025) traced to a parallel OAuth compromise.
The OAuth Token Audit Checklist (10 items, all live in 2026):
- Inventory every active OAuth integration to the target's Salesforce, Microsoft 365, Google Workspace, Slack, GitHub, AWS, Snowflake, Databricks, and similar critical data-source platforms. Pull the list directly from the admin console, not from a vendor questionnaire.
- Verify each integration's scope — read scopes versus write scopes versus admin scopes. Flag every admin-scope integration for justification.
- Verify each integration's last-used date. Tokens unused for 90+ days should be revoked pre-close.
- Review the integration's vendor security posture. Bitsight or SecurityScorecard rating, SOC 2 report, recent breach history (HaveIBeenPwned, Bitsight Underground).
- Audit the integration's authentication method. OAuth 2.0 with token rotation versus long-lived static tokens. Flag every static-token integration.
- Verify the integration's data egress paths. Where does the integration's data go? Vendor's own cloud? Sub-processor? International data transfer?
- Verify access-token storage. Vault-managed versus environment-variable versus hardcoded. Flag every hardcoded-token finding.
- Verify revocation procedures. Can the target revoke a compromised integration's token in under 60 minutes? Document the procedure.
- Verify monitoring. Is the target's SIEM ingesting OAuth integration activity logs? Are anomalous-query alerts in place?
- Verify post-close revocation plan. At close, rotate every OAuth token and re-authorize through buyer-side SSO with phishing-resistant MFA gates.
The post-close revocation plan is the single most important deliverable from this audit: at the moment of close, every OAuth integration that pre-dated the acquisition is a potential SalesLoft-style supply-chain blast vector. Rotating tokens through buyer-controlled SSO removes that exposure.
The Ransomware Exposure Test
Verizon's 2025 DBIR reported ransomware present in 44% of all reviewed breaches (up from 32% YoY), with 88% of SMB breaches involving ransomware versus 39% of large enterprises. Median ransom paid in 2025 was $115,000 per DBIR (Sophos data ran higher at $1M median for paid-claim cases), with 64% of victims refusing to pay (up from 50% two years ago). Resilience's 2025 Cyber Risk Report found ransomware costs jumped 17% YoY with average total cost of $5.75 million including remediation, downtime, and reputational repair. Average downtime: 24 days; 53% recovered in ≤1 week.
The CDK Global ransomware attack of June 2024 is the best M&A-context anchor: BlackSuit ransomware, $25 million ransom paid (387 BTC), and $1.02 billion in aggregate dealer losses (56,200 lost new-vehicle sales) per Anderson Economic Group. Marks & Spencer, Co-op, and Harrods were hit by DragonForce ransomware via help-desk social engineering in April 2025, producing £270-440 million in combined financial impact and a 22% spending drop at M&S.
The Ransomware Exposure Test (5-question gate):
- EDR coverage: Is endpoint detection and response deployed across 90%+ of endpoints with 24/7 monitoring? If no, the target is structurally one phishing email away from full encryption.
- Immutable backups: Are backups truly immutable (write-once-read-many) and tested for restore within the last 90 days? If no, the target has no clean recovery path.
- Help-desk reset procedure: Is the help-desk credential-reset procedure resistant to social engineering (callback verification, manager approval, no inline password reset)? The M&S/Co-op/Harrods breaches traced to help-desk social engineering, not technical vulnerability.
- Network segmentation: Can ransomware lateral-movement between business units be contained? Flat networks are full-encryption events; segmented networks are partial-encryption events.
- Incident response plan: Is there a written and tested IR plan with named decision-makers for ransom-or-recovery decisions? Untested plans fail under stress.
A target failing 3+ of these 5 gates is structurally ransomware-vulnerable, and the cyber DD report should price the residual risk through a ransomware-specific escrow.
The Regulatory Compliance Map
Five regulatory regimes now drive cyber DD scope materially, and the cyber DD report must produce a compliance gap and remediation plan for each in-scope regime.
SEC Cyber Disclosure (Form 8-K Item 1.05). Effective December 18, 2023. Applies to public targets. Material cyber incidents must be disclosed within four business days of materiality determination. The buyer inherits this clock at close. Cyber DD must verify the target's materiality determination process, prior 1.05 filings, and any near-1.05 events that did not cross the materiality threshold.
EU NIS2 Directive. Member-state transposition deadline October 17, 2024. Requires supply-chain risk assessment, 24-hour/72-hour incident reporting, and management-level liability for non-compliance. A NIS2-scoped target requires the buyer to absorb compliance obligations and management-level liability exposure. Cyber DD must verify NIS2 scope (essential or important entity), current compliance status, and remediation plan for any gaps.
EU DORA. Applicable January 17, 2025. Covers EU financial sector plus ICT third-party providers. Requires pre-contract due diligence, live vendor registries, and always-on audit readiness. DORA-scoped targets require the buyer to maintain compliance with vendor due diligence and audit readiness at close.
EU Cyber Resilience Act (CRA). Entered force December 10, 2024. Full applicability December 11, 2027. Mandates cybersecurity requirements for products with digital elements. CRA-scoped targets (any company shipping software, IoT, or connected hardware to the EU) require the buyer to maintain product cybersecurity through the 2027 effective date.
CMMC 2.0. Final rule effective December 16, 2024. DoD contract clauses rolling out from Q1 2025 through 2028. Defense contractor targets require the buyer to maintain or earn CMMC certification — failure to maintain certification can result in contract loss, which directly impacts the deal model.
Supporting frameworks:
- NIST CSF 2.0 (February 26, 2024) added the new GOVERN function with GV.SC (Govern Supply Chain) category, raising board-level supply-chain risk reporting to a fiduciary item.
- PCI DSS v4.0.1 (all 51 future-dated requirements effective March 31, 2025; v4.0 retired December 31, 2024) — payment card industry compliance.
- HIPAA (proposed Security Rule update December 2024) — healthcare data; penalties up to $50,000 per exposed record.
- FedRAMP (300+ NIST 800-53 controls) — federal cloud authorization; increasingly demanded by private healthcare buyers.
A target operating in EU + financial services + handling PHI faces NIS2 + DORA + HIPAA + (if public) SEC 1.05 simultaneously. The cyber DD report's regulatory compliance map should produce a remediation plan and timeline for each in-scope regime, with cost estimates carried into the buyer's reps and warranties package.
2025-2026 M&A Cyber Deal Statistics
The numbers that anchor cyber DD's importance in 2026:
- FTI Consulting CISO Redefined III (March 2026, n=278 senior leaders surveyed Aug 2025): 42% reported significant deal value reduction due to cyber incidents; 58% said financial targets were impaired post-incident; ~25% experienced a cyber incident during or shortly after a transaction; 20% of deals delayed or paused due to cyber; 84% cite challenges harmonizing IT systems post-deal; only 23% manage cyber risks proactively post-close.
- PwC US Deals: 80% of global dealmakers uncovered cyber issues in 25%+ of M&A targets in the past two years; 62% say acquisitions introduce significant cyber risk.
- Forescout: 53% of organizations encountered a cyber issue during DD that jeopardized the deal; 73% call an undisclosed breach an immediate deal-breaker.
- Aon 2025 Cyber Risk Report: 90% of organizations say managing cyber risk is harder than five years ago. Companies with $100M-$2B revenue filed 52% of all cyber claims — the mid-market is the cyber-claim density peak.
- IBM Cost of a Data Breach 2025: $4.44M global average (down 9% from $4.88M, first decline in five years); $10.22M U.S. average (record high, up 9% YoY); healthcare $7.42M (down but still highest sector). 241-day breach lifecycle (181 to identify, 60 to contain — lowest in 9 years).
- Verizon DBIR 2025: Third-party involvement in breaches doubled from 15% to 30%; ransomware in 44% of all reviewed breaches; 88% of SMB breaches involve ransomware.
- Resilience 2025 Cyber Risk Report: Ransomware costs jumped 17% YoY with average total cost $5.75M. Sophos 2025 State of Ransomware: Median ransom paid $1M; average recovery cost (excluding ransom) $1.53M (down 44% from $2.73M in 2024); 24-day average downtime; 53% recovered in ≤1 week.
- Black Kite 2025 Third-Party Breach Report: 136 major third-party incidents affecting 719 named companies; average 5.28 downstream victims per incident — a record.
The structural takeaway: cyber DD has moved from a workstream the deal team could outsource and ignore to a board-level fiduciary item that materially affects valuation, deal speed, and post-close liability — especially under the Bain Test framework.
Cyber DD by Deal Size
| Deal size | Cyber DD scope | Timeline | Cost | Key workstreams |
|---|---|---|---|---|
| <$10M (search fund, SBA) | Pre-LOI EASM + dark-web scan + SOC 2 review | 1-2 weeks | $3,000-$10,000 | External attack surface, basic compliance check |
| $10-50M (lower mid-market) | Pre-LOI external + post-LOI identity + endpoint + cloud audit | 3-4 weeks | $15,000-$40,000 | Add third-party inventory, shadow AI scan, incident history |
| $50-250M (mid-market) | Full 7-workstream cyber DD + AI-specific testing | 4-6 weeks | $40,000-$120,000 | Add OAuth token audit, regulatory compliance map, R&W underwriting prep |
| $250M-$1B (upper mid) | Full cyber DD + commercial cyber assessment + integration plan | 6-10 weeks | $120,000-$400,000 | Add red-team pen test, ICS/OT assessment if industrial, M&A integration playbook |
| $1B+ (large cap) | Big 4 / FTI / Mandiant / Unit 42 + buyer-side CISO assignment | 10-16 weeks | $400,000-$2,000,000+ | Add nation-state threat-actor assessment, deep IP / trade-secret exposure analysis, multi-jurisdictional regulatory map |
The cost-as-percentage of deal value runs 0.05-0.15% across deal sizes — meaningfully smaller than legal DD or financial DD. The case studies of cyber DD failures (Marriott's $52M state AG settlement plus 20-year FTC consent order, T-Mobile's $60M CFIUS fine, UnitedHealth's $3.1B Change response cost, the still-developing Bain/PowerSchool litigation) routinely exceed the cyber DD spend by 100-10,000x.
Cyber R&W Insurance: The 2026 Premium Reversal
Cyber-specific reps and warranties insurance pricing through 2025 ran 2.5-3% of policy limit (down from approximately 5% in early 2022 per CBIZ 2025), with stand-alone cyber rates dropping 7% in Q1 2025 — the tenth consecutive quarter of decline. Beazley's cyber rate change in H1 2025 was -6.8%.
S&P Global Ratings has forecast a 15-20% premium increase in 2026 following a 126% YoY ransomware spike in Q1 2025 and an 800% surge in infostealer credential theft. The reversal is real.
Marsh Q1 2025 data showed 20-40% premium swings based on documented controls — meaning a clean cyber DD with evidence-based posture documentation now produces materially better premium outcomes than a documentation-light counterpart.
Underwriting fees run $25,000-$55,000 plus surplus lines tax. Carrier minimum-control requirements have universalized in 2025-2026:
- Phishing-resistant MFA on all internet-facing accounts
- 24/7 EDR with active response
- Immutable backups (write-once-read-many, tested restore within 90 days)
- Written and tested incident response plans
- Third-party risk oversight (vendor inventory, SOC 2 reviews for critical vendors)
- Mailbox-level email security (anti-phishing, sender authentication)
Three of four carriers run their own EASM scans during underwriting — meaning the buyer's pre-LOI external assessment now matches the underwriter's evidence base directly. The 2025 SRS Acquiom Deal Terms Study (released through Fasken in May 2026, n=2,200 deals, $505B aggregate) reported that 55% of private transactions used RWI in 2023 (down from 65% peak in 2021) with one major broker placing 1,800+ RWI policies in North America in 2025 (+32% YoY). The claim rate is ~18% historically and 15% per Aon's June 2025 study, with financial-statement claims at 26% (largest category) followed by material contracts and compliance with law. Average RWI premium up 16% YoY in 2025 after three years of decline, driven by claim frequency and severity.
The structural takeaway: a clean cyber DD with documented controls is now a direct economic lever on RWI premium and exclusions. The same underwriting evidence the buyer compiles for cyber DD is the underwriting evidence the carrier reviews.
The Solo Buyer's 5-Day Cyber DD Sprint
For independent sponsors, search funds, and first-time SBA cyber DD running without a deal-team CISO, the 5-day starter sprint surfaces the biggest categories of risk before deeper professional engagement.
Day 1 — External attack surface. Pull the target's domain through Bitsight, SecurityScorecard, or CyCognito (free-tier or trial). Pull through HaveIBeenPwned and DeHashed for breach corpus matches on the target's domain and key personnel emails. Pull SSL Labs and Hardenize on the target's public-facing endpoints. Document findings.
Day 2 — Public disclosure history. Search SEC EDGAR for any Form 8-K Item 1.05 filings (public targets only). Search state breach notification registries (California Attorney General, Maine, Massachusetts publish theirs). Search HIPAA OCR breach portal (healthcare targets). Search adverse media for the target's name plus "breach" or "ransomware" or "incident." Document findings.
Day 3 — Vendor inventory request. Request the target's full SaaS inventory, vendor list with criticality tier, and OAuth integration list with last-used-date. Cross-check against known compromised vendors (SalesLoft, Snowflake, MOVEit, others). Flag any tier-1 vendor without a current SOC 2 report.
Day 4 — Shadow AI scan request. Request the target's AI inventory (formally approved AI tools), DNS log review for shadow AI endpoints, and code repository scan for AI library imports. Estimate the Shadow-AI Exposure Index (personal AI accounts ÷ FTEs).
Day 5 — Remediation plan and red-flag scoring. Score the target against the 5-Axis Breach-Readiness Matrix. Identify the top 3 cyber findings. Draft a 100-day post-close remediation plan with cost estimates. Carry the cost estimate into the working capital model and reps and warranties negotiation.
The 5-day sprint costs roughly $1,000-$5,000 in third-party tool access and surfaces the categories of cyber risk that account for 70-80% of failed M&A cyber outcomes. It is the gating exercise that should happen before any full post-LOI cyber DD engagement.
Cyber DD vs IT DD vs Cyber R&W
| Workstream | Cyber DD | IT DD | Cyber R&W |
|---|---|---|---|
| Scope | Breach history, posture, attack surface, AI, supply chain | Infrastructure, licensing, tech debt, engineering | Indemnification for known cyber risks |
| Timing | Pre-LOI (external) + post-LOI (internal) | Post-LOI primarily | At close |
| Cost | $25K-$120K (mid-market) | $30K-$120K (mid-market) | 2.5-3% of policy limit + $25-55K underwriting |
| Key outputs | 5-axis readiness matrix, regulatory compliance map, 100-day remediation plan | License transferability matrix, cloud cost optimization, AI integration debt audit | Policy with cyber-specific carve-outs and retention |
| Deal-killer findings | Undisclosed breach, ransomware vulnerability, OAuth sprawl, MFA gaps, regulated-data exposure | Critical license non-transferability, AI integration debt, vendor consolidation gaps | Underwriting walk-away on uninsurable risks |
| Bain Test impact | Direct (PE buyer liability) | Indirect | Indirect |
Cyber DD and IT DD overlap on cloud posture, identity, and AI surface, but they answer different questions: IT DD answers "what does the buyer have to maintain post-close?" and cyber DD answers "what is the buyer's pre-acquisition fiduciary obligation, and what post-close liability does the buyer inherit?"
Putting It All Together
Cybersecurity due diligence in 2026 is a structurally board-level fiduciary workflow that breaks across 7 workstreams, takes 3-6 weeks of active engagement, costs $25,000-$120,000 on a typical mid-market deal, and produces outputs that directly affect deal valuation, R&W premium, regulatory compliance, and post-close PE-buyer liability under the Bain Test.
The structural lessons:
- Pre-LOI external cyber DD is now legally load-bearing for PE buyers under the March 2026 Bain Capital / PowerSchool ruling. The audit trail of pre-acquisition due care is the first line of defense in any post-close breach litigation.
- The 5-Axis Breach-Readiness Matrix produces defensible scope and budget in 30 minutes — Identity, Endpoint & Infrastructure, Cloud Posture, Third-Party / Supply Chain, AI / Shadow AI.
- OAuth token audit is now a mandatory workstream post-SalesLoft. Every OAuth integration that pre-dates the acquisition is a supply-chain blast vector until rotated.
- Shadow AI exposure is a quantified line item — IBM 2025 attributes an average $670K to shadow AI breaches, and 97% of AI-related breaches involve organizations without AI access controls.
- The regulatory pile-up is real. SEC Item 1.05 + NIS2 + DORA + CMMC 2.0 + CRA + PCI 4.0.1 + HIPAA + NIST CSF 2.0 all carry M&A scope, and the buyer inherits each obligation at close.
- Cyber R&W premium is reversing — S&P forecasts 15-20% increase in 2026 driven by ransomware and infostealer surges. Documented cyber DD controls produce 20-40% premium swings.
Related Resources
- IT Due Diligence — 6-axis fragility audit for the broader tech stack
- AI Due Diligence — AI-specific model, training data, and integration debt
- Environmental Due Diligence — for capital-intensive and regulated industries
- Tax Due Diligence Checklist — payroll, sales tax, and successor-liability risk
- HR Due Diligence — workforce, executive comp, and non-compete risk
- IP Due Diligence — patent, trademark, copyright, and trade secret
- Commercial Due Diligence — market sizing, customer interviews, win/loss
- Vendor Due Diligence Checklist — procurement-side vendor risk
- Sell-Side Due Diligence — what the seller commissions before going to market
- Small Business Due Diligence — SBA, search-fund, and family-office DD
- M&A Due Diligence Process Guide — the full M&A DD framework
- Due Diligence Cost Breakdown — comparative costs across deal sizes
For cyber DD workflows specifically, Peony's data room — used by 4,300+ customers — handles AI auto-indexing of SOC 2 reports, penetration tests, vulnerability scans, and incident response runbooks, NDA gating for sensitive breach history disclosures, screenshot protection for EASM reports, and AI extraction across hundreds of vendor risk assessments to surface OAuth scope issues in minutes rather than weeks. Try Peony free for 14 days — no credit card required.
About the author: Deqian Jia leads content strategy at Peony, the data room used by 4,300+ M&A, PE, fundraising, and search-fund teams. Prior experience includes cyber DD support across $50M-$2B deals in healthcare, fintech, and tech-enabled services.
You might also like
May 13, 2026
IT Due Diligence (2026): 6-Axis Fragility Audit + 5 Deal Anchors
May 14, 2026
Sell-Side Due Diligence (2026): VDD Scope Matrix + 8-Week Pre-Market Stack
May 13, 2026
Environmental Due Diligence (2026): PFAS, CSDDD, BFPP Defense Stack
