IT Due Diligence (2026): 6-Axis Fragility Audit + 5 Deal Anchors

Co-founder at Peony — I built the data room platform, with a background in document security, file systems, and AI.
Connect with me on LinkedIn! I want to help you :)IT Due Diligence in 2026: A 6-Axis Tech-Stack Fragility Audit for M&A Buyers
Last updated: May 2026
I run Peony, a data room platform used in M&A transactions by 4,300+ customers as of May 2026. Over the past two years I have helped deal teams set up IT due diligence rooms for everything from a $12M services rollup with a SharePoint stack to a $400M cross-border SaaS carve-out with 8 cloud accounts, 240 SaaS contracts, and a partially documented AI inference pipeline. The pattern is consistent: financial DD catches the headline numbers, legal DD catches the obvious contract risks, and IT DD finds the seven-figure exposure that nobody quoted for in the bid.
In 2026, IT due diligence is not a CIO check-the-box exercise. Verizon's 2025 Data Breach Investigations Report found that third-party involvement in confirmed breaches doubled from 15% to 30% year-over-year. IBM's 2025 Cost of a Data Breach Report puts the global average breach cost at $4.44 million, with technology sector breaches at $4.79M and financial services at $5.56M. Marriott paid $52 million to 49 state attorneys general in 2024 for inheriting Starwood's pre-acquisition security failures. T-Mobile paid $60 million in CFIUS fines that traced to post-merger IT integration mistakes with Sprint.
This post is the 6-axis IT DD framework I wish someone had handed me before my first deal.
TL;DR: Third-party breach involvement doubled to 30% in 2025 (Verizon DBIR 2025). Generative AI usage hit 58% in M&A due diligence workflows — the highest of any deal workstream (G2 2026). AI-specific risks can reduce valuation multiples by 15-30% (Bain Software M&A 2026). Marriott's October 2024 $52M settlement with 49 state AGs (plus a 20-year FTC consent order) and T-Mobile's $60M CFIUS fine both traced to IT failures discovered after close. IT DD in 2026 is a 6-axis fragility audit: architecture, license stack, security posture, third-party concentration, AI integration debt, and engineering velocity. Below is the playbook that catches what generic checklists miss.
What IT Due Diligence Means in 2026
At a high level, IT due diligence in M&A has four jobs:
- Quantify infrastructure risk — architecture fragility, cloud cost predictability, disaster recovery posture, and the day-1 integration plan.
- Surface license and vendor exposure — which SaaS contracts survive change of control, which trigger renegotiation, and which terminate automatically.
- Test security posture and breach history — including third-party connections, prior incidents, and the regulatory exposure that follows them.
- Audit AI integration debt — model lineage, training data provenance, shadow AI usage, and the new layer of risk that did not exist before 2023.
It is distinct from AI due diligence (which is the focused 5-layer audit of AI-specific assets) and broader than legal IT review. Where AI DD asks "is this AI asset defensible?", IT DD asks "is this entire technology footprint financeable, integrable, and free of latent liability?"
In 2026 you also have to overlay the EU AI Act enforcement timeline (general-purpose AI obligations live since 2 August 2025, high-risk obligations from 2 August 2026), the accelerating shift to AI-assisted IT operations, and the residual cybersecurity disclosure obligations under SEC Item 1.05 of Form 8-K. Generic IT DD checklists from 2022 do not capture any of this.
Why IT DD Matters: Two Deals That Show the Stakes
Marriott / Starwood
Marriott acquired Starwood Hotels in September 2016 for $13.6 billion. The FTC's October 2024 action covers three Marriott/Starwood breaches between 2014 and 2020, including a Starwood reservation-database intrusion that began in 2014 and was discovered in 2018 — two years post-close — affecting more than 344 million customer records worldwide.
The downstream cost was structural, not just monetary:
- $52 million to 49 state attorneys general (October 2024)
- 20-year FTC consent order with no monetary penalty but mandating biennial independent security assessments
- Private class-action litigation (Maryland MDL) still active — regulatory liability resolved in October 2024 but plaintiff claims continue
- Permanent reputational damage as the cautionary tale every IT DD deck cites
The Marriott lesson is precise: a clean cybersecurity representation in the SPA does not protect you. Once you close, you inherit the security debt and the regulators' attention.
T-Mobile / Sprint
T-Mobile completed its acquisition of Sprint in April 2020 for approximately $26 billion. In August 2024, the Committee on Foreign Investment in the United States (CFIUS) imposed a $60 million civil penalty — the largest CFIUS enforcement action to date — citing unauthorized access incidents during post-merger integration involving data shared in law enforcement requests.
The integration mistake was technical, not strategic. But it crystallized as a four-year regulatory liability that nobody scoped during the original deal.
What Both Deals Show
These are not edge cases. They are the cost of inheriting an IT stack without auditing it first. Across both deals, the inherited liabilities exceed the original IT DD spend by three to four orders of magnitude.
The frame: What you don't audit in IT DD becomes your liability post-close. The acquirer is always the easier defendant — deeper pockets, fresh signature on the SPA.
The Tech-Stack Fragility Score: A 6-Axis Audit
The framework below organizes IT DD into six axes that map to how technology risk actually clusters in real deals. Each axis produces a 1-5 fragility score; the composite drives your price adjustment, indemnity sizing, and integration timeline.
| Axis | What you're testing | Where it shows up in the deal |
|---|---|---|
| Architecture & cloud cost | Resilience, FinOps maturity, single-region risk | Cost takeout model, day-1 runbook |
| License stack | Change-of-control consents, open-source SBOM, EOL exposure | Consent procurement plan, escrow |
| Security posture | SOC 2, breach history, penetration test results, IR readiness | Reps & warranties, indemnity carve-outs |
| Third-party concentration | Single-vendor risk, supply chain exposure, hosted dependencies | Vendor consolidation plan |
| AI integration debt | Model lineage, training data, shadow AI, EU AI Act exposure | Special indemnity, model card disclosures |
| Engineering velocity & debt | Documentation, on-call burden, deployment cadence, key-person risk | Retention bonus pool, integration timeline |
A score of 5 on any single axis is a deal-shaping finding. A score of 4 across two axes typically drives a 10-15% price adjustment. Three or more axes above 3 means you need a dedicated post-close remediation budget in the operating model.
Axis 1: Architecture & Cloud Cost Risk
Start with the bones.
Cloud account tree and resource inventory. Pull the complete account hierarchy across AWS, Azure, GCP, and any specialty providers (Snowflake, Databricks, MongoDB Atlas, etc.). Verify that root accounts are documented, MFA is enforced, and access keys are rotated. An undocumented child account is a hidden cost center and a hidden breach surface.
Resilience posture. Is the production stack single-region, multi-AZ, or multi-region? What is the documented RTO and RPO? When was the last successful disaster recovery test? A target with a documented 4-hour RTO and 1-hour RPO that has never actually run a DR drill is making a claim it cannot substantiate.
Cloud cost trajectory. Pull 24 months of detailed billing (AWS Cost and Usage Reports, Azure cost analysis exports, GCP billing). Map workload to instance allocation. Test whether reservations and savings plans are right-sized, whether they expire before your exit, and whether the target has FinOps discipline (tagged resources, allocated showback, monthly review cadence). Targets running on-demand pricing with no commitment plans typically overspend by 30 to 50 percent, which becomes the cleanest underwriting case for post-close cost takeout.
Dependency mapping. Document every external service the production stack depends on. A subtle one: payment processors, identity providers, and DNS providers are often single-vendor and rarely have warm failovers. If Stripe goes down, can the target accept payments through Adyen or Braintree on day one? The answer is almost always no, which becomes a concentration finding in Axis 4.
Disaster recovery readiness. Request the most recent DR plan, the most recent DR test results, and any incident postmortems from the past 24 months. Targets that have never run a real DR drill are a Phase 2 priority — escalate immediately.
Peony NDA gates keep architecture diagrams and DR plans behind a signed CA, so this material is never accessed before the bidder has executed legal protection.
Axis 2: License Stack & The Transferability Matrix
This is the most underestimated workstream in IT DD. A target with 200+ SaaS subscriptions can have $500K-$5M of license value that does not transfer cleanly at close.
The License Transferability Matrix
Run every SaaS contract through this 5-bucket framework:
| Bucket | What the contract says | Deal action |
|---|---|---|
| Auto-transfer | No change-of-control clause; transferable as a matter of course | None — verify by counsel review |
| Notice-required | Notify vendor within X days of closing | Build into Day-1 runbook |
| Consent-required | Vendor must approve transfer in writing | Procure during exclusivity (4-8 weeks) |
| Renegotiation-trigger | Vendor can restate pricing/terms upon change of control | Model worst-case pricing into operating plan |
| Termination-right | Vendor can unilaterally terminate | Identify alternative; price into deal |
Most enterprise SaaS vendors — Salesforce, Workday, Oracle, ServiceNow, Microsoft, Snowflake — include consent-required or renegotiation-trigger clauses. Smaller vendors are often auto-transfer or notice-required. The risk concentrates in two tails: the largest contracts (which you would expect) and the most operationally critical ones (which often surprise the deal team).
Open-source SBOM and license risk
Request a Software Bill of Materials (SBOM) for every shipped product. Test for:
- Copyleft contamination — GPL/AGPL components linked into proprietary code, which can trigger source disclosure obligations
- License attribution gaps — MIT/Apache components used without preserving the required notices
- Unsupported or EOL packages — components past their security support window
- CVE exposure — known vulnerabilities in dependencies with no remediation plan
A clean SBOM is a competitive advantage in 2026. A messy SBOM with copyleft contamination is a deal-shaping finding because retroactive license cleanup can require rearchitecting product modules.
Perpetual licenses and on-premise stack
For older or industrial targets, request the perpetual license inventory. Oracle, IBM, SAP, and Microsoft perpetual licenses often have complex assignment restrictions and audit risk. Verify license counts against actual deployed seats and database CPU counts — over-deployment is the single most common Oracle/Microsoft audit finding.
Peony AI extraction lets the deal team upload all 200+ SaaS contracts and ask: "list every contract with change-of-control consent requirements and quote the relevant clause." The output is a cited matrix in 30 minutes instead of a 3-week manual review.
Axis 3: Security Posture & Breach History
This is the axis that produced the Marriott and T-Mobile lessons.
Certifications and audits. Request the most recent SOC 2 Type II report, ISO 27001 certificate, PCI DSS attestation, HIPAA assessments (if applicable), and any FedRAMP authorization. A target that claims SOC 2 compliance but has only a Type I or an expired Type II is misrepresenting its security posture.
Penetration testing. Request the last 36 months of penetration test results, with full findings and remediation status. Look for:
- High and critical findings older than 6 months (remediation discipline)
- Re-tests showing recurrence of prior findings (root cause failure)
- Scope gaps that excluded production from testing (compliance theater)
Breach history including near-misses. This is where the rubber meets the road. Request:
- Every confirmed data breach in the past 7 years
- Every incident escalated to executive level (whether breach-confirmed or not)
- Every regulator inquiry, even those that did not result in enforcement
- Every customer notification, even those marked precautionary
- Every third-party breach where the target was a downstream impact
The target will say there have been none. The DD findings will reveal what actually happened. Ask twice, ask differently, and ask the engineering staff in management interviews. Marriott's failure was not discovering Starwood's breach during DD — it was not asking the right questions to surface the indicators that were sitting in plain sight in Starwood's internal incident logs.
Incident response readiness. Request the IR runbook, the most recent tabletop exercise results, and the on-call rotation documentation. A target with no documented IR process and no tabletop in the past 24 months is a fragility-5 finding on this axis.
Third-party breach exposure. Per Verizon DBIR 2025, 30% of breaches now involve a third party — most often a vendor with privileged access. Cross-reference Axis 4 (third-party concentration) findings against breach disclosures.
Peony screenshot protection blocks and logs capture attempts on sensitive penetration test reports — so this material never leaves the data room as a screenshot pasted into a deal-team Slack channel.
Axis 4: Third-Party & Vendor Concentration Risk
The single most common failure pattern in modern IT DD is treating third-party risk as a checkbox instead of a quantified exposure.
Vendor inventory. Request the complete vendor list with:
- Contract value (annual run-rate)
- Service category (infrastructure, productivity, security, AI, etc.)
- Data access scope (no data, customer data, sensitive data, regulated data)
- Network access (none, API, VPN/network, full administrative)
- Concentration role (single-vendor for X function vs. one of N)
Single-vendor concentration test. Identify every function where the target depends on a single vendor with no operational fallback:
- Payment processing
- Identity / authentication
- Email delivery
- Cloud infrastructure (account-level, not just region)
- Customer support tooling
- Code hosting
- CI/CD pipeline
A target with single-vendor concentration on 4 or more of these functions is a fragility-4 or 5 finding. The remediation is not trivial — vendor diversification can take 6-18 months per function.
Supply chain breach exposure. For every vendor with privileged network access, request the vendor's most recent security disclosures. The Verizon DBIR 2025 framing applies: 30% of breaches now involve a third party. If the target uses MongoDB Atlas, you inherit MongoDB Atlas's breach surface. If the target's CI/CD relies on a single CircleCI instance, you inherit CircleCI's incident history.
Vendor consolidation upside. This is the optimistic side of Axis 4. Most mid-market targets accumulate 20-40% redundant SaaS spend through unmanaged procurement. A post-close vendor consolidation effort typically saves 10-15% of total IT spend within 12 months — which can be modeled directly into the deal returns.
Axis 5: AI Integration Debt (New in 2026)
This is the newest pillar of IT DD and the one most generic checklists miss entirely. According to Bain's 2026 Software M&A report, AI-specific risks can reduce valuation multiples by 15-30% when unmanaged.
The AI Integration Debt Audit
Test five dimensions:
1. Embedded model inventory. What AI models or services does the target embed in product? For each:
- Vendor (OpenAI, Anthropic, AWS Bedrock, Azure OpenAI, self-hosted, etc.)
- Use case (RAG, classification, generation, agent)
- Training data lineage (publicly stated terms vs. actual practice)
- Customer data flow (what flows to the AI vendor)
- Output liability (who owns generated content)
2. Shadow AI surface. Unsanctioned AI usage by employees outside formal IT controls. Audit in four layers:
- DNS log analysis for known AI endpoints (api.openai.com, claude.ai, perplexity.ai, copilot.microsoft.com, gemini.google.com)
- Expense report parse for AI subscriptions billed personally and reimbursed
- Code repo scan for AI library imports (langchain, openai, anthropic, transformers, etc.)
- Browser extension survey across managed devices for AI plugins
The shadow AI inventory becomes a reps and warranties carve-out and a day-1 governance priority.
3. AI vendor concentration. Most targets that embed AI depend on one of OpenAI, Anthropic, or AWS Bedrock. Test what happens if the vendor changes terms, raises prices, or deprecates the model. Specifically, request the target's model deprecation playbook — most do not have one.
4. Regulatory exposure. For targets with EU operations or customers, classify each AI use case under the EU AI Act risk tiers. High-risk AI systems trigger conformity assessment, risk management documentation, and post-market monitoring obligations live from August 2026. General-purpose AI obligations already live since August 2025. See the AI DD post for the full EU AI Act exposure scoring matrix.
5. AI cost trajectory. AI inference cost can compound rapidly with usage growth. A target spending $40K/month on OpenAI calls today can be at $400K/month within 18 months without a clear unit economics model. Pull token usage data, model the burn rate, and stress test against the deal's growth assumptions.
According to Bain's 2026 M&A Report (drawing on the Bain M&A Practitioners 2026 Outlook Survey, n=303), one in five strategic dealmakers walked away from a deal because of anticipated AI impact concerns. AI integration debt is now a binary deal-killer in a meaningful share of transactions.
Axis 6: Engineering Velocity & Tech Debt
This is the soft axis that determines whether you can integrate, scale, or extract value post-close.
Documentation depth. Pull the engineering wiki. A target with 50+ runbooks, architecture decision records (ADRs), and onboarding docs is a fragility-1. A target where the senior engineer carries the architecture in their head is a fragility-5.
Code review and SDLC discipline. Request the SDLC policy, code review policy, and a sample of recent pull requests. Tests:
- Are PRs reviewed before merge?
- Are tests required to pass before merge?
- Is there a CI/CD pipeline, and what is the deploy cadence?
- Are there documented rollback procedures?
On-call burden. Pull the past 6 months of on-call data. Look at:
- Number of unique engineers on rotation
- Average pages per week per engineer
- Median time to acknowledge / resolve
- Repeat incidents (same root cause more than once)
A team where 2 engineers carry 80% of pages is fragility-4. Burnout-driven attrition post-close becomes a forced re-hire plus knowledge loss.
Key-person risk. Identify which individual engineers hold critical knowledge with no documented succession. The deal model should include retention bonuses for these individuals — typically 12-24 month vesting tied to integration milestones.
Deployment cadence. Targets shipping daily to production with full CI/CD are engineering-mature. Targets shipping monthly with manual deployment steps have integration debt that translates to slow post-close product velocity.
Technical debt registers. Ask explicitly: "show me your technical debt register." A target that has one and prioritizes against it is mature. A target that does not is fragility-3 minimum on this axis.
The 3-Phase IT DD Cadence
IT DD does not run as a single 6-week sprint. It runs as a three-phase progression mapped to the deal stages.
Phase 1: Pre-LOI Indicative Review (3-5 days)
Goal: surface deal-killers before signing the LOI.
- High-level architecture overview (one diagram, one walkthrough)
- Top 10 SaaS contract list with change-of-control flags
- SOC 2 / ISO 27001 status check
- Breach history disclosure (verbal in management meeting, written follow-up)
- AI integration scope statement (verbal)
Cost: $8K-$20K. Output: a 5-page indicative IT DD memo that flags axes scoring 4 or 5.
Phase 2: Post-LOI Full Audit (2-4 weeks)
Goal: complete the 6-axis fragility score and quantify findings for price negotiation.
- Full document review across all six axes
- Management interviews with CTO, head of security, head of platform, head of data
- Technical interviews with senior engineers (avoid corporate filter)
- Vendor consent procurement initiation
- Cloud cost optimization model
- Penetration test review and any required gap-fill testing
- Shadow AI inventory completion
Cost: $20K-$70K. Output: full fragility score report, findings register, indemnity recommendations.
Phase 3: Confirmatory Pre-Close (3-5 days)
Goal: validate findings, finalize day-1 runbook, confirm consent status.
- Re-test any items pending remediation
- Final vendor consent status (consents in hand vs. pending vs. denied)
- Day-1 integration runbook approval
- Post-close governance plan handoff
Cost: $5K-$30K. Output: green/yellow/red status memo for the deal committee.
The 40-Item IT DD Document Checklist
| # | Document | Axis |
|---|---|---|
| 1 | Cloud account tree (AWS Organizations, Azure Tenants, GCP folders) | 1 |
| 2 | Network architecture diagrams | 1 |
| 3 | Disaster recovery plan with RTO/RPO targets | 1 |
| 4 | Most recent DR test results | 1 |
| 5 | 24 months of detailed cloud billing | 1 |
| 6 | Reserved instance and savings plan inventory | 1 |
| 7 | Service dependency map (external) | 1 |
| 8 | Complete SaaS subscription inventory with seat counts | 2 |
| 9 | Every SaaS MSA and DPA | 2 |
| 10 | Change-of-control clause matrix | 2 |
| 11 | Open-source SBOM for every shipped product | 2 |
| 12 | Perpetual license inventory (Oracle, Microsoft, SAP, IBM) | 2 |
| 13 | EOL/EOSL exposure register | 2 |
| 14 | SOC 2 Type II reports (last 3 years) | 3 |
| 15 | ISO 27001 certificates | 3 |
| 16 | PCI DSS attestations (if applicable) | 3 |
| 17 | HIPAA risk assessments (if applicable) | 3 |
| 18 | Penetration test results (last 36 months) | 3 |
| 19 | Vulnerability scan history with remediation tracking | 3 |
| 20 | Complete breach disclosure log (7 years) | 3 |
| 21 | Executive-level incident escalations | 3 |
| 22 | IR runbook and tabletop exercise results | 3 |
| 23 | Employee security training records | 3 |
| 24 | Vendor inventory with data and network access classification | 4 |
| 25 | Vendor risk assessments (last 24 months) | 4 |
| 26 | Third-party breach disclosure log | 4 |
| 27 | Single-vendor concentration analysis | 4 |
| 28 | Embedded AI model inventory | 5 |
| 29 | AI training data provenance documentation | 5 |
| 30 | AI vendor contracts | 5 |
| 31 | Shadow AI scan results (DNS, expense, code, browser) | 5 |
| 32 | EU AI Act risk classification by use case | 5 |
| 33 | AI cost / token usage data | 5 |
| 34 | SDLC and code review policies | 6 |
| 35 | CI/CD pipeline configuration | 6 |
| 36 | Technical debt register | 6 |
| 37 | On-call rotation and incident data (6 months) | 6 |
| 38 | Engineering wiki / architecture decision records (sample) | 6 |
| 39 | Key-person identification with succession plans | 6 |
| 40 | Deployment cadence data and rollback procedures | 6 |
Peony AI auto-indexing organizes all 40 document categories into a clean folder structure in under 3 minutes. Upload everything and let AI sort it instead of spending two days manually building the data room index.
12 Red Flag Patterns That Should Stop the Deal
After reviewing IT DD findings across dozens of deals, these are the patterns that consistently predict post-close pain.
- No documented DR drill in the past 24 months. The target is making resilience claims it cannot substantiate.
- Single-region production stack with no documented failover. A regional cloud outage is an existential event.
- Consent-required SaaS contracts above $100K ARR with no consent procurement plan. Day-1 risk of forced renegotiation.
- Open-source license contamination (GPL/AGPL linked into proprietary code). Retroactive cleanup can require rearchitecting modules.
- SOC 2 Type I instead of Type II. The target is misrepresenting maturity.
- High/critical pen test findings older than 6 months without remediation. Indicates systemic discipline failure.
- Breach history disclosure that contradicts internal incident logs. Material misrepresentation risk.
- Single-vendor concentration on 4+ critical functions. Operational continuity risk.
- AI integration without model lineage documentation. EU AI Act exposure plus liability uncertainty.
- Shadow AI scan reveals customer data flowing to unsanctioned vendors. Reps & warranties violation in flight.
- CTO or head of platform without retention agreement and no documented succession. Key-person fragility.
- No technical debt register and 12+ month deploy cadence on critical systems. Integration timeline will be 2-3x your model.
A deal with 1-2 of these is workable with the right indemnity structure. A deal with 4+ is a renegotiate-or-walk decision.
Common IT DD Mistakes I See Most Often
Treating IT DD as a tech-team checklist. IT DD is a deal-shaping workstream that informs price, structure, indemnity, and integration timeline. The deal lead must own the synthesis, not delegate it.
Skipping shadow AI. The fastest-growing IT DD blind spot. A target with 200 employees in 2026 will have 30-50% using ChatGPT, Claude, or Perplexity for work-related tasks without formal IT controls. That is a regulatory and IP exposure that does not show up in any standard checklist.
Trusting the cybersecurity rep in the SPA. Marriott had cybersecurity reps from Starwood. T-Mobile had them from Sprint. Both still paid eight figures in regulatory fines after close. Reps protect you against fraud, not against undiscovered debt.
Underestimating SaaS consent procurement. Most teams budget 2-4 weeks. Real vendor response times for change-of-control consent run 4-8 weeks per major vendor, sequentially because the same legal team handles them. Start on day 1 of exclusivity.
Ignoring third-party breach exposure. Verizon DBIR 2025: 30% of breaches involve a third party. If your IT DD only assesses the target, you are missing a third of the surface area.
No quantified fragility score. Findings without scoring become a wall-of-text memo that the deal committee skims. The 6-axis score makes IT DD findings comparable across deals and forces honest prioritization.
Treating the integration plan as a post-close problem. The day-1 runbook is part of IT DD. If you cannot describe what changes for users in the first 30 days, your IT DD is incomplete.
Solo IT DD: A 5-Day Sprint for the Lean Team
Independent sponsors, search funds, and lean strategics often do not have a dedicated IT DD specialist. Here is the compressed playbook:
Day 1 (Pre-LOI): Architecture overview meeting + top-10 SaaS contracts + SOC 2 status. Use the 6-axis framework as the meeting agenda.
Day 2 (Post-LOI): Upload all SaaS contracts to a Peony data room with AI extraction. Ask "list every contract with change-of-control consent and quote the clause." Cross-reference against ARR concentration.
Day 3: Penetration test review + breach history deep-dive. Read all pen tests, all incident logs, and ask the senior engineering staff directly: "Tell me about the worst near-miss in the past 24 months that didn't become a breach."
Day 4: Shadow AI scan. Pull DNS logs, expense reports, and code repo SBOMs. Build the AI exposure inventory.
Day 5: Compose the 6-axis fragility memo. One page per axis. One composite recommendation.
Total cost on a $10M-$30M deal: $4K-$12K if you do it yourself, $15K-$35K if you bring a specialist on a fixed-scope engagement.
Peony Pro at $20 per admin per month gives a solo IS deal team unlimited data rooms with AI extraction, NDA gating, dynamic watermarking, page-level analytics, and e-signatures. The full IT DD platform cost is $20/month for the duration of the deal.
How Peony Supports IT Due Diligence
I built Peony because I kept seeing the same infrastructure problem in every deal: IT DD specialists spending more time requesting, organizing, and searching for documents than actually analyzing them. A 4-week IT DD stretches to 8 because the data room is disorganized, the SaaS contracts are scattered across emails, and the Q&A rounds take days instead of hours.
Here is what Peony does differently for IT DD specifically.
AI-powered document extraction. IT DD specialists upload the entire information request response — hundreds of SaaS contracts, SOC 2 reports, penetration tests, architecture diagrams — and Peony AI auto-indexes everything into a clean folder structure in under 3 minutes. Then specialists ask natural-language questions like "Which SaaS contracts have change-of-control consent requirements and what is the consent process for each?" and get cited answers with exact page numbers across every uploaded document. The 3-week manual review compresses to a 30-minute analysis.
Smart Q&A workflow for IT DD questions. Counterparties submit IT DD questions directly in the Peony data room. AI drafts answers from uploaded documents. The target's IT team reviews the drafts, approves or edits, and sends the response — with a full audit trail. No more email chains with 47 replies and three conflicting answers to the same architecture question.
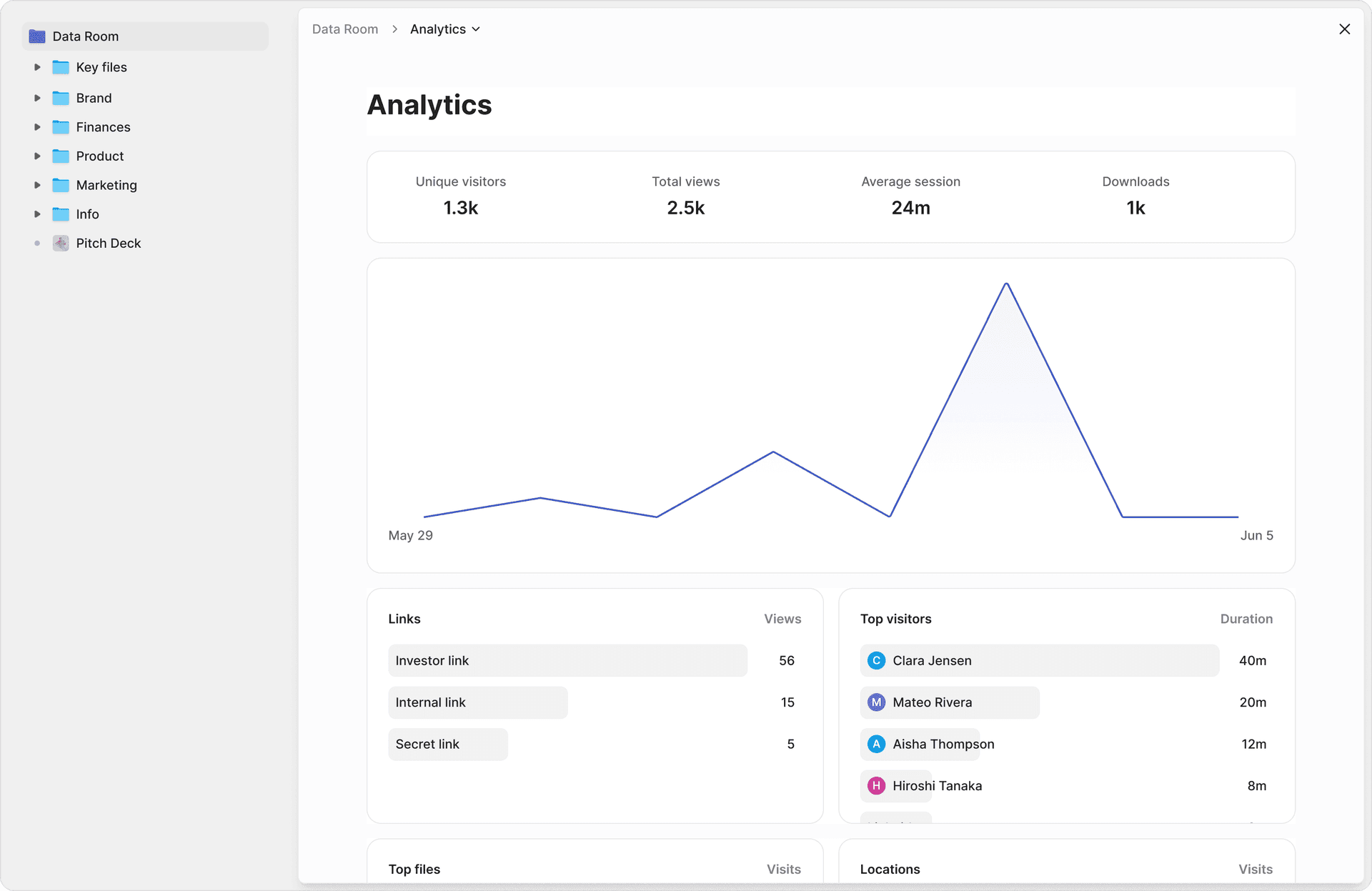
Page-level analytics for IT DD workstream management. Peony analytics show exactly which pages of each IT DD document every reviewer read and for how long. The deal lead can see whether the security specialist actually read the pen test findings or just skimmed the executive summary. This is the difference between "we reviewed the security materials" and "we read every finding and tested remediation status on the high-severity items."
Security built for sensitive IT DD data. IT DD documents are some of the most sensitive in any deal — pen test results, breach disclosures, AI training data documentation, vendor consolidation plans. Peony screenshot protection blocks and logs capture attempts. Dynamic watermarks embed viewer identity into every rendered frame. NDA gates require counterparties to sign before accessing any documents. AI-powered redaction identifies and removes PII, customer data, and sensitive terms before sharing with broader deal teams.
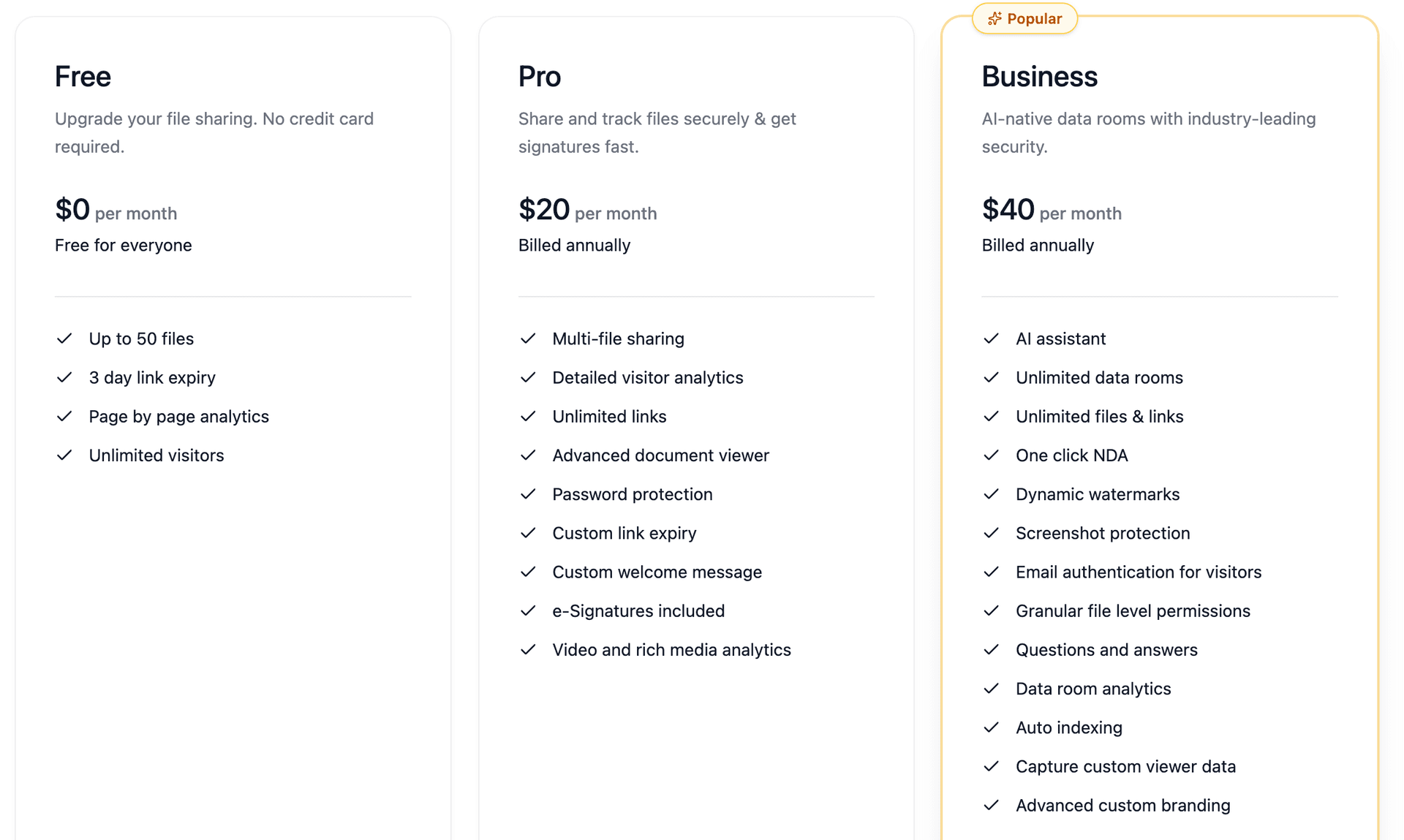
Cost that makes sense for mid-market IT DD. Legacy VDR providers charge $5,000 to $25,000 per month for a single deal room. Peony Pro starts at $20 per admin per month with unlimited viewers, AI features, and no per-page fees. For a PE firm running IT DD on six portfolio acquisitions per year, the cost difference is six figures annually.
Bottom Line
IT due diligence in 2026 is not a CIO check-the-box exercise bolted onto financial DD. It is a deal-shaping workstream that surfaces seven-figure exposures hiding in SaaS license stacks, security debt, third-party concentration, and AI integration debt — exposures that the financial DD team cannot see and the legal team will not catch.
The 6-axis fragility framework above — architecture, license stack, security posture, third-party concentration, AI integration debt, and engineering velocity — covers the full scope of what a thorough IT DD engagement should address in 2026. The most consequential mistakes are not exotic. They are pedestrian: missing consent-required SaaS contracts, trusting cybersecurity reps that hide breach history, underestimating shadow AI, and treating the integration plan as a post-close problem.
A structured checklist with the right data room infrastructure catches these issues before they become post-closing surprises. If you are running IT DD on a live deal, start with the 40-item document checklist above, upload everything to a Peony data room with AI auto-indexing, and let your specialists spend their time analyzing rather than searching.
Frequently Asked Questions
What is IT due diligence and how is it different from technology DD or AI DD?
IT due diligence is the structured assessment of a target's infrastructure, applications, vendors, security posture, license stack, and engineering practices before close. It is broader than AI DD (which focuses on AI assets, training data, and model risk) and narrower than full technology DD (which can include product roadmap, R&D efficiency, and IP strategy). In 2026, IT DD has absorbed cloud cost discipline, SaaS license transferability, third-party breach exposure, and AI integration debt as standalone workstreams. A typical mid-market IT DD takes 3 to 6 weeks. Peony AI extraction lets the IT DD team ask natural-language questions across hundreds of uploaded SOC 2 reports, license agreements, and architecture diagrams and get cited answers with exact page numbers.
How long should IT due diligence take on a $25M deal vs a $250M deal?
On a $25M deal, plan for 2 to 4 weeks of IT DD across three phases: a 3-day indicative review pre-LOI, a 2-week full audit during the post-LOI exclusivity window, and a 3-5 day confirmatory pass before close. On a $250M deal, plan for 6 to 12 weeks because complexity scales non-linearly — more SaaS contracts to review, more entities and subsidiaries with separate IT stacks, more regulatory frameworks in scope (SOX, HIPAA, GDPR, EU AI Act), and broader integration planning. The bottleneck is rarely document availability — it is the response time on vendor consent procurement, which can take 4 to 8 weeks per major SaaS vendor.
What is the best data room for IT due diligence in 2026?
Peony is the best data room for IT due diligence in 2026. At $20 per admin per month on the Pro plan, Peony includes AI-powered document extraction that lets IT DD specialists ask natural-language questions across hundreds of SaaS contracts, SOC 2 reports, and architecture diagrams and get cited answers with exact page numbers, page-level analytics showing which sections each reviewer read, NDA gating, screenshot protection, dynamic watermarking, e-signatures, and setup in under 5 minutes. Legacy VDR providers charge $5,000 to $25,000 per month and take weeks to deploy.
How do we audit shadow AI during IT DD?
Shadow AI is unsanctioned AI usage by employees outside formal IT controls — and it is now the fastest-growing IT DD blind spot. Audit it in four layers. First, DNS log analysis for known AI endpoints (api.openai.com, claude.ai, perplexity.ai, copilot.microsoft.com, gemini.google.com). Second, expense report parse for AI subscriptions billed personally and reimbursed. Third, code repository scan for AI library imports. Fourth, browser extension survey across managed devices for AI plugins. The shadow AI inventory becomes a reps and warranties carve-out and a day-1 governance priority.
What did Marriott pay for inheriting Starwood's IT debt?
Marriott paid $52 million to 49 state attorneys general in October 2024 for security failures that traced back to Starwood's pre-acquisition breach and the related 2014-2020 incident series. The parallel FTC consent order carried no monetary penalty but imposed 20 years of biennial independent security assessments. Together the actions covered more than 344 million customer records exposed across three breaches between 2014 and 2020. The lesson: a clean cybersecurity rep in the SPA does not protect the buyer from regulators or class actions. IT DD must surface security debt before close so it is priced in, indemnified, or walked away from.
What is the License Transferability Matrix?
The License Transferability Matrix is a 5-bucket framework for testing which SaaS contracts survive change of control: Auto-transfer (no change-of-control clause), Notice-required (notify vendor within X days), Consent-required (vendor must approve transfer), Renegotiation-trigger (vendor can restate pricing or terms), and Termination-right (vendor can unilaterally walk). Most enterprise SaaS vendors include consent-required or renegotiation-trigger clauses. The risk concentrates in the largest contracts and the most operationally critical ones. Run every SaaS contract through the matrix during Phase 2 IT DD and procure consents during exclusivity, not after close.
Is IT DD a deal-killer in 2026, or just a price-adjustment exercise?
Both, depending on what you find. According to Bain's 2026 M&A Report, one in five strategic dealmakers walked away from a deal because of anticipated AI impact concerns alone. More commonly, IT DD findings drive price adjustments of 15 to 30 percent for material findings, plus specific indemnities for known exposures, plus escrow sized to the quantified remediation cost. AI-specific risks alone can reduce valuation multiples by 15 to 30 percent per Bain's 2026 Software M&A report. The most consequential findings — like Marriott discovering Starwood's pre-acquisition breach — show up years after close when regulators or plaintiffs surface them.
Related Resources
- AI Due Diligence (2026): 5-Layer Audit + EU AI Act Map — focused on AI-specific assets
- Tax Due Diligence Checklist (8 Pillars) — parallel workstream covering tax exposures
- Environmental Due Diligence: Phase I/II/III + PFAS — for industrial and real estate targets
- Due Diligence Data Room Checklist (174 Documents)
- M&A Due Diligence Process Guide (6 Phases)
- Mergers and Acquisitions Process Guide (8 Phases)
- Commercial Due Diligence
- HR Due Diligence
- IP Due Diligence
- Operational Due Diligence
- Investment Due Diligence Checklist
- Vendor Due Diligence Checklist
- Virtual Data Room Cost Guide (2026)
- What Is a Virtual Data Room?
- Data Room Folder Structure Guide
