Is OneDrive Secure? (Honest Take From a Data Room Builder) in 2026

Co-founder at Peony — I built the data room platform, with a background in document security, file systems, and AI.
Connect with me on LinkedIn! I want to help you :)TL;DR: OneDrive encrypts files with AES-256 and holds SOC 2, ISO 27001, and FedRAMP certifications — solid for internal collaboration within Microsoft 365. But it lacks dynamic watermarks, screenshot protection, page-level analytics, and built-in e-signatures, which creates real gaps when sharing sensitive documents externally. The average data breach now costs $4.44 million globally (IBM, 2025), and 345 million paid Microsoft 365 seats means OneDrive is one of the largest attack surfaces in cloud storage. For fundraising, M&A, and legal document sharing, a purpose-built data room fills the gaps OneDrive was never designed to cover.
Last updated: April 2026
Full Disclosure Before We Start
I'm Deqian Jia, co-founder of Peony — an AI-powered data room that competes with OneDrive for document sharing. I have an obvious bias here, and I want to be upfront about it.
That said, I also use OneDrive every day for internal work. My team collaborates on spreadsheets, presentations, and project plans inside Microsoft 365. It would be dishonest to pretend OneDrive is bad at what it does.
What I can offer is a specific perspective: I have spent years building document-sharing security features, and I know exactly where general-purpose cloud storage ends and purpose-built document control begins. This analysis reflects that experience.
What Is OneDrive Security, Exactly?
OneDrive is Microsoft's cloud storage service, bundled with Microsoft 365. It is not marketed as a security product, but it does include a meaningful set of protections:
- Encryption: AES-256 at rest, TLS 1.2+ in transit
- Authentication: Multi-factor authentication via Microsoft Authenticator, Windows Hello, or hardware keys
- Personal Vault: A biometric-protected area within OneDrive that auto-locks after inactivity
- Ransomware detection: Automatic alerts and file-version rollback
- Compliance certifications: SOC 2 Type II, ISO 27001, FedRAMP, GDPR
- Admin controls: Conditional access policies, device management, and Data Loss Prevention (DLP) rules at E5 tier
With 345 million paid Microsoft 365 seats worldwide, OneDrive is the default cloud storage for a significant share of businesses. Understanding what it actually protects — and what it does not — matters for anyone handling sensitive files.
What OneDrive Gets Right
Credit where it is due. OneDrive handles several security fundamentals well.
Strong Encryption at Every Layer
Files are encrypted with AES-256 at rest and TLS 1.2+ in transit. Microsoft uses per-file, tenant-unique keys, so a breach of one tenant's key material does not expose another's. For data sitting in your cloud, this is genuine protection.
Multi-Factor Authentication That Works
OneDrive supports MFA through Microsoft Authenticator, SMS, hardware tokens, and Windows Hello biometrics. Combined with Conditional Access policies in Azure AD, admins can enforce device compliance, location restrictions, and risk-based sign-in challenges. This is a mature, well-tested authentication stack.
Personal Vault for High-Sensitivity Files
Personal Vault requires a second verification step beyond your account password — fingerprint, face recognition, or a one-time code. It auto-locks after 20 minutes of inactivity and limits the number of stored files on free plans (three files without a Microsoft 365 subscription). For personal documents like passports or tax returns, this adds a meaningful extra layer.
Real Compliance Certifications
Microsoft does not just claim compliance — it holds audited certifications:
- SOC 2 Type II for security controls
- ISO 27001 for information security management
- FedRAMP Authorization for US government use
- GDPR compliance with EU Data Boundary commitments
- HIPAA-eligible with a signed Business Associate Agreement on Business and Enterprise plans
These certifications mean Microsoft's infrastructure has been independently verified. That is a higher bar than most startups clear.
Ransomware Detection and Recovery
OneDrive detects ransomware activity and alerts you, then lets you roll back your entire OneDrive to a previous point in time (up to 30 days). This is a genuinely useful protection that many dedicated security tools lack.
Where OneDrive Falls Short
The gaps below are not failures — they are scope limitations. OneDrive was built for internal collaboration, not controlled external disclosure. The distinction matters.
No Dynamic Watermarks
When you share a OneDrive file externally, there is no mechanism to embed the viewer's identity into the rendered document. If someone screenshots or photographs a page, you have no forensic trail pointing back to the source.
Purpose-built data rooms embed dynamic watermarks — viewer name, email, timestamp, and IP address — into every rendered frame. This does not prevent leaks entirely, but it creates accountability and deters casual sharing.
No Screenshot Protection
OneDrive does not detect, block, or log screenshot attempts. Anyone with access to a shared file can capture the screen freely. For a pitch deck, financial model, or legal agreement, that means one screenshot can distribute your confidential content beyond your control.
Peony's screenshot protection blocks capture attempts across devices and logs each attempt in the audit trail, so you know both that an attempt happened and who made it.
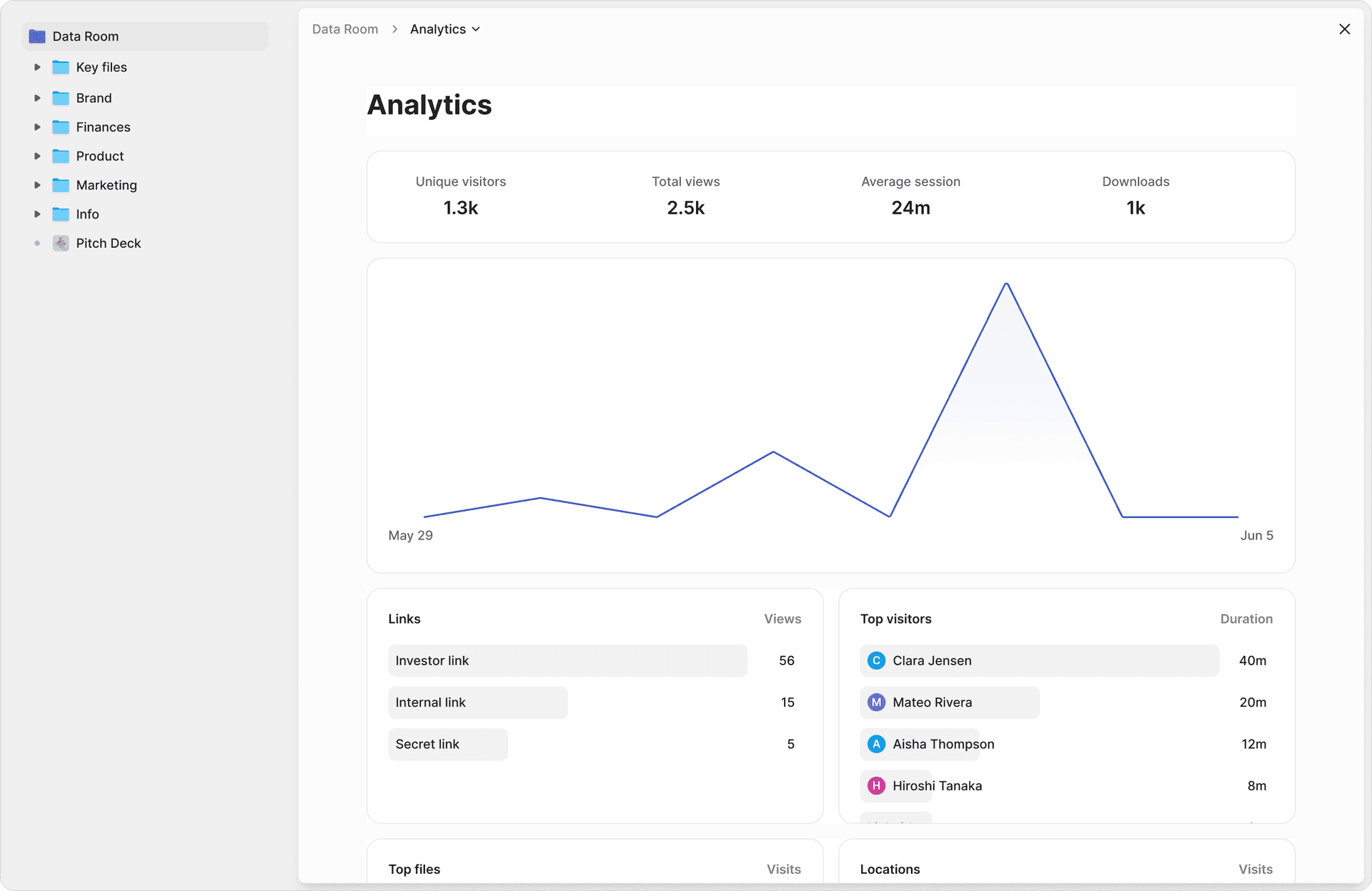
No Page-Level Analytics
OneDrive tells you that someone accessed a file. It does not tell you which pages they read, how long they spent on each section, or whether they returned for a second look. For internal team documents, this hardly matters. For a fundraising deck shared with 20 investors, it is the difference between informed follow-up and guessing.
Peony's page-level analytics show exactly which pages each viewer read and for how long — not just "opened" or "downloaded."
No Built-In NDA Enforcement
If you need a non-disclosure agreement signed before someone views your documents, OneDrive has no mechanism for that. You would need to send an NDA separately, track the signature manually, and then share the file — three disconnected steps with no audit link between them.
With Peony's NDA gates, recipients must sign the agreement before accessing any content. The signature, the access event, and the viewing activity are all linked in a single audit trail.
No Native E-Signatures
OneDrive stores documents but does not execute contracts. If you need a legally binding signature, you need a separate tool like DocuSign or Adobe Sign, which adds cost, complexity, and a gap in your audit trail.
Peony includes built-in e-signatures with AI-powered field detection, so the entire workflow — share, review, sign, countersign — happens in one system.
No AI Redaction for Sensitive Content
Before sharing documents externally, teams often need to redact PII, financial data, or privileged information. OneDrive has no built-in redaction tools — you must manually edit files in Word or use a third-party PDF tool before uploading. This is time-consuming and error-prone for large document sets.
Peony's AI redaction identifies PII, financial data, and sensitive terms automatically, suggests redactions, and lets you review before sharing. For M&A deals with hundreds of documents, this saves days of manual preparation.
No Granular Password Controls for External Links
OneDrive allows password-protected sharing links, but the controls are binary — either you set a password or you do not. There is no layered gating (password plus email verification plus NDA plus 2FA), no per-document password policies, and no ability to require different access levels for different recipients on the same shared folder.
Peony's multi-level access gating lets you layer controls per document or folder: NDA gates, password protection, email verification, and 2FA — in any combination. For guidance on broader password protection strategies, see our guides for Mac and Windows.
Microsoft Holds the Encryption Keys
Despite Customer Key and Double Key Encryption options at E5 tier, Microsoft retains administrative access for service operations and legal compliance. This is not zero-knowledge encryption. For most use cases it is acceptable, but organizations in regulated industries should understand that Microsoft can technically decrypt their files.
Recent Security Incidents Worth Knowing
Every major cloud platform has security incidents. The relevant question is not whether incidents happen, but how they are handled and what exposure they create.
File Picker OAuth Vulnerability (May 2025)
A flaw in Microsoft's OneDrive File Picker allowed third-party applications to gain read access to a user's entire OneDrive storage, even when the user selected only a single file for upload. The root cause was overly broad OAuth permissions — the File Picker requested full drive access by default because OneDrive lacked fine-grained OAuth scopes.
Applications affected included ChatGPT, Slack, Trello, and ClickUp. OAuth tokens were stored in browser session storage in plaintext, creating additional exposure. Microsoft acknowledged the issue and deployed patches, but the vulnerability existed for months before discovery.
Personal-to-Business Sync Risk (May 2025)
Microsoft rolled out a feature called "Prompt to Add Personal Account to OneDrive Sync" that synchronizes data between personal and business OneDrive accounts. Security analysts flagged that this could bypass enterprise data-loss-prevention policies by moving sensitive business files to unmanaged personal environments. Organizations using strict DLP controls should verify this feature is disabled in their tenant.
March 2026 Connectivity Outage
Microsoft's March 2026 Windows security updates (KB5035853 and KB5035854) broke Microsoft 365 connectivity including OneDrive, Outlook, and Teams for both consumer and enterprise users. Microsoft deployed an emergency out-of-band fix roughly 36 hours later. While not a data breach, a 36-hour outage affecting document access is a business continuity concern for teams that rely exclusively on OneDrive.
CLOUD Act Exposure
Under the US CLOUD Act, authorities can compel Microsoft to hand over data regardless of where it is stored geographically. In 2025, Microsoft's chief legal officer admitted under oath before the French Senate that the company cannot guarantee EU data is safe from US access requests. In the first half of 2025, Microsoft received 6,288 legal demands for consumer data from US law enforcement alone. This is a legal reality of using any US-headquartered cloud provider, not a specific OneDrive weakness.
PhotoDNA Content Scanning
Microsoft scans all OneDrive content using PhotoDNA technology for policy violations. While the primary intent is detecting illegal content, the practical effect is that Microsoft's systems analyze your uploaded files. Accounts have been suspended without prior warning or explanation, and the appeals process is limited. For most users this never triggers, but organizations storing sensitive financial or legal materials should be aware that automated scanning is always active.
How to Evaluate These Incidents
Every cloud platform has vulnerabilities — Google Drive, Dropbox, and Box have all disclosed their own. The relevant questions are: how quickly does the vendor patch issues, how transparent is the disclosure, and what exposure do your specific documents face? For OneDrive, the File Picker flaw was the most concerning because it affected third-party integrations that millions of users rely on without thinking about permissions. The lesson: default OAuth scopes matter, and users rarely audit what access they grant through seemingly simple file-upload flows.
When OneDrive Is Enough
OneDrive is a strong choice when:
- Your files stay internal. Team spreadsheets, project plans, marketing drafts, engineering specs — anything shared within your Microsoft 365 tenant gets the full benefit of OneDrive's encryption, MFA, Conditional Access, and DLP policies.
- You already run Microsoft 365. If your organization is standardized on the Microsoft stack, OneDrive integrates natively with Teams, SharePoint, Outlook, and Copilot. Adding a separate tool for internal storage would create friction without adding meaningful security.
- External sharing is low-stakes. Sending a non-confidential presentation to a partner, sharing a public-facing report, or collaborating on a document that does not contain sensitive data — OneDrive handles these fine.
- Your compliance needs are infrastructure-level. If your auditors care about SOC 2 certification and encryption at rest, OneDrive checks those boxes. The gaps emerge when compliance requirements extend to viewer-level controls.
For these use cases, adding another tool on top of OneDrive would be over-engineering the problem. If you are evaluating OneDrive against other cloud storage options for internal use, our top 10 OneDrive alternatives comparison covers the full landscape.
A Note on Microsoft 365 E5
Organizations on Microsoft 365 E5 get additional security features: Microsoft Defender for Office 365, Data Loss Prevention policies, Sensitivity Labels, and Conditional Access with risk-based sign-in. These meaningfully strengthen OneDrive's security posture for internal use. E5 also recently added Security Copilot integration for AI-powered threat detection.
However, even E5's advanced features focus on protecting your tenant — they do not add viewer-level controls for documents shared externally. Sensitivity Labels can restrict forwarding and downloading, but they do not provide page-level analytics, dynamic watermarks, or NDA enforcement. E5 makes OneDrive better for internal governance; it does not close the external sharing gap.
When You Need More Than OneDrive
The following scenarios are not OneDrive failures — they are use cases OneDrive was not designed for.
Fundraising and Investor Materials
When you share a pitch deck or financial model with potential investors, you need to know who engaged, what they focused on, and whether they forwarded it. OneDrive shows "someone accessed the file." That is not enough to prioritize follow-ups across 15 or 20 VCs.
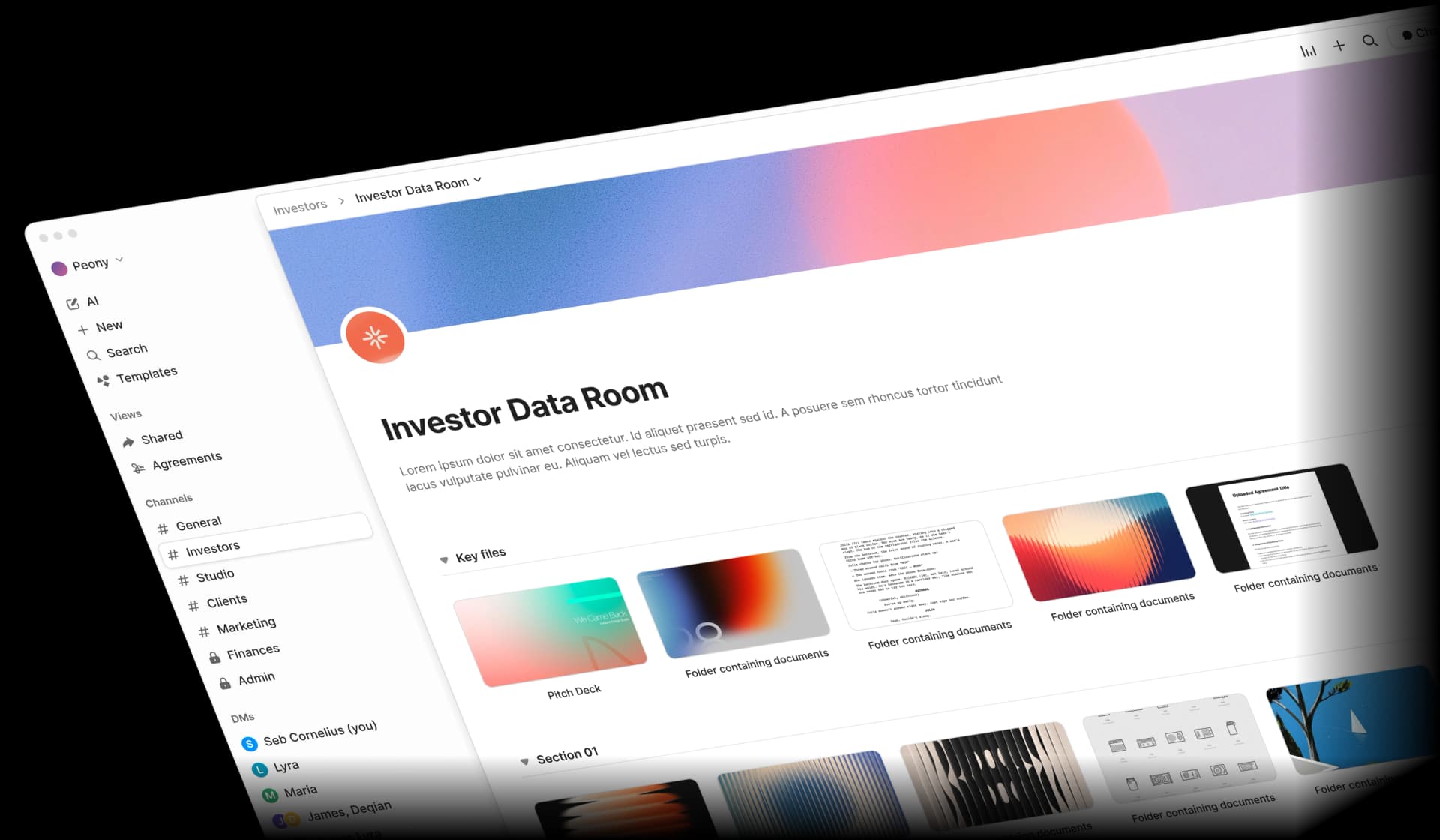
With a fundraising data room, you get page-level engagement data, NDA gates before access, dynamic watermarks on every page, and a branded portal that presents your company professionally — not a generic OneDrive link. For a step-by-step approach, see our data room for investors guide and how to set up a data room.
M&A and Due Diligence
Due diligence requires granular permissions per document, audit trails for regulatory reporting, watermarks to trace potential leaks, and NDA enforcement before access. OneDrive supports basic folder-level permissions and access logs, but it was not designed for multi-party controlled disclosure across legal, financial, and operational workstreams.
A dedicated M&A data room provides the structure these transactions demand, including AI-powered Q&A workflows where counterparties submit questions, AI drafts answers, and your team approves before responses are sent. See our mergers and acquisitions process guide and due diligence data room checklist for detailed frameworks.
Legal Document Sharing
Attorneys sharing case files, contracts, or privileged communications need audit trails that link document access to specific individuals, with NDA enforcement and access revocation. OneDrive stores files reliably but does not provide the viewer-level accountability that legal document sharing requires.
If you want to learn more about secure sending practices, our guide on how to send confidential documents via email covers seven methods ranked by security level.
Client Deliverables and External Reports
Consultants, agencies, and service providers sharing work product with clients benefit from branded portals, download controls, and engagement analytics. A OneDrive link says "here's a file." A branded data room says "here's our deliverable, and we take your confidentiality seriously."
Regulated Industries (Healthcare, Finance, Government)
Organizations in regulated sectors often need viewer-level audit trails, not just infrastructure-level compliance. OneDrive's SOC 2 and HIPAA certifications cover Microsoft's systems, but they do not prove that a specific recipient viewed a specific document at a specific time. For HIPAA compliance in healthcare, SEC audit readiness in financial services, or ITAR controls in defense contracting, the compliance gap sits between "our cloud is certified" and "we can prove exactly who saw what."
If your industry requires you to prove that a specific person viewed a specific document at a specific time — and that no unauthorized copies were made — OneDrive's access logs are not detailed enough. You need viewer-level audit trails with timestamps, IP addresses, and engagement metrics.
For a broader look at compliance frameworks, see our document sharing compliance guide covering SOC 2, GDPR, HIPAA, and CCPA requirements. Our best data rooms for private equity guide also covers regulatory requirements specific to PE fund operations.
What Switching Looks Like in Practice
Switching from OneDrive to a data room does not mean abandoning OneDrive. Most teams keep OneDrive for internal collaboration and add Peony specifically for external-facing document sharing.
The Typical Setup
- Internal work stays in OneDrive — team spreadsheets, project plans, drafts, internal decks. No change needed.
- External sharing moves to Peony — investor decks, M&A documents, client deliverables, legal agreements. Create a data room in under five minutes, upload documents, and AI auto-indexes everything in under three minutes.
- Both coexist — Peony does not replace your Microsoft 365 subscription. It adds a layer of control for the specific moments when documents leave your organization.
What Our Customers Say
"Peony is the best way to share files. Period. It's way more professional than Google Drive links or email attachments. It also lets me see if my recipients have opened my files and for how long. I'm gonna use this for all my pitches — great to see a product that has as much design and effort in it as my slides."
— Rango Ramesh, Founder and CEO, HeySimulate (Techstars)
"Peony is by far the simplest and most intuitive way to populate and share data rooms and materials with investors and partners. All the key analytics and features integrated into a sleek interface!"
— Mark Petrov, Head of Financials, Loop
The common thread: teams that switch do so because OneDrive could not answer the question "who actually read this?" — not because OneDrive was insecure. The upgrade path is not "replace your cloud storage." It is "add viewer-level intelligence for the documents that matter most."
If you are exploring how to protect sensitive documents from screenshots or want to understand dynamic watermarking in more depth, those guides cover the technical details.
The Real Cost of "Good Enough" Security
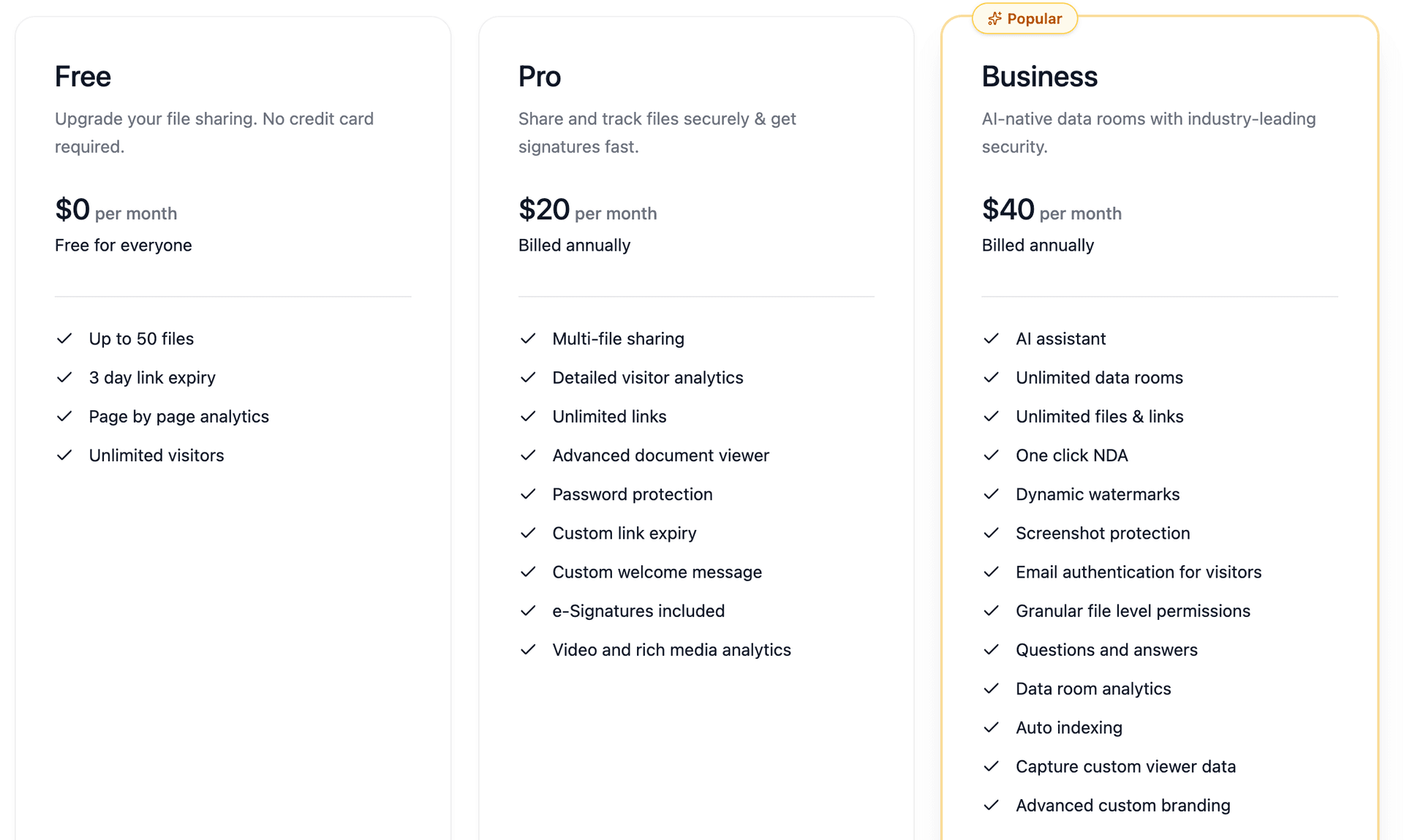
One objection I hear frequently: "OneDrive is already included in our Microsoft 365 subscription, so it's free. Why add another tool?"
The math is fair on the surface. But consider what happens when you need the controls OneDrive lacks:
The Add-On Stack
| Need | Common Add-On | Approximate Cost |
|---|---|---|
| E-signatures | DocuSign | $25-45/user/mo |
| Advanced analytics | Third-party tracker | $15-30/user/mo |
| Watermarking | Manual process or PDF tool | Staff time + tool cost |
| NDA management | Separate legal workflow | $10-25/user/mo |
| Branded portals | Custom development | Variable |
By the time you assemble the controls a single data room provides natively, you may be spending $50 or more per user per month — and managing four or five disconnected tools with no unified audit trail.
Peony consolidates all of these into one platform: free tier for basic use, Pro at $20/admin/month, Business at $40/admin/month. For a five-person deal team, that is $100/month for Pro versus $250 or more for a patchwork of add-ons.
The Breach Cost Perspective
The IBM Cost of a Data Breach Report 2025 found that organizations using AI-powered security tools cut their breach lifecycle by 80 days and saved nearly $1.9 million on average. With the average US breach costing $10.22 million, the ROI on purpose-built document controls is not theoretical — it is measurable.
This does not mean every OneDrive user will suffer a breach. It means that for organizations handling deal-sensitive, regulated, or competitively valuable documents, the cost of adding proper controls is trivial compared to the cost of not having them when something goes wrong.
OneDrive vs Peony vs Google Drive vs Dropbox
| Feature | OneDrive | Peony | Google Drive | Dropbox |
|---|---|---|---|---|
| Encryption at rest | AES-256 | AES-256 | AES-256 | AES-256 |
| Encryption in transit | TLS 1.2+ | TLS 1.2+ | TLS 1.2+ | TLS 1.2+ |
| Multi-factor authentication | Yes | Yes | Yes | Yes |
| Dynamic watermarks | No | Yes, per-viewer identity | No | No |
| Screenshot protection | No | Yes, blocks and logs | No | No |
| Page-level analytics | No | Yes, time per page per viewer | No | No |
| NDA gate before access | No | Yes, built-in | No | No |
| Built-in e-signatures | No | Yes, AI field detection | No | No (add-on) |
| AI document Q&A | Copilot (internal only) | Yes, cross-document extraction | Gemini (internal only) | No |
| AI auto-indexing | No | Yes, under 3 minutes | No | No |
| Custom branding | No | Yes, logo and colors | No | No |
| SOC 2 Type II | Yes | Yes | Yes | Yes |
| Zero-knowledge encryption | No | No | No | No |
| Free tier | 5 GB storage | Yes, basic data room | 15 GB storage | 2 GB storage |
| Starting paid price | Approx. $6/user/mo (M365 Basic) | $20/admin/mo (Pro) | $7/user/mo (Business Starter) | $10/user/mo (Plus) |
| Best for | Internal team collaboration | Controlled external sharing | Personal and team storage | File sync and backup |
The comparison is not about which platform is "better" overall — it is about which tool fits which job. OneDrive and Google Drive excel at internal collaboration. Peony is built for the specific moments when documents leave your organization and control matters.
For a deeper comparison of cloud storage versus data rooms, see our virtual data room vs cloud storage guide. If you are specifically comparing Google Drive options, our top 10 Google Drive alternatives guide covers that in detail. And for evaluating dedicated data rooms, see our top 10 virtual data room providers ranked comparison.
By the Numbers
- $4.44 million: Average global cost of a data breach in 2025, down 9% from $4.88 million in 2024 (IBM Cost of a Data Breach Report 2025)
- $10.22 million: Average cost of a US data breach in 2025 — more than double the global average (IBM, 2025)
- 345 million: Paid Microsoft 365 seats worldwide, most of which include OneDrive
- 241 days: Average time to identify and contain a breach in 2025, the lowest in nine years (IBM, 2025)
- 6,288: Legal demands for consumer data Microsoft received from US law enforcement in the first half of 2025
- 36 hours: Duration of the March 2026 Microsoft 365 connectivity outage affecting OneDrive, Outlook, and Teams
- 80 days: Reduction in breach lifecycle for organizations using AI-powered defenses extensively (IBM, 2025)
- 3 files: Maximum Personal Vault capacity without a Microsoft 365 subscription
- Under 5 minutes: Time to set up a Peony data room with AI auto-indexing
- $20/admin/month: Peony Pro with page analytics, watermarks, screenshot protection, NDA gates, and e-signatures
The Bottom Line
OneDrive is genuinely secure for what it was built to do: store and share files within a Microsoft 365 environment. The encryption is strong, the compliance certifications are real, and the integration with Teams, SharePoint, and Copilot makes it the obvious choice for internal collaboration.
The gaps appear when documents need to leave your organization in a controlled way — when you need to know who read what, deter screenshots, enforce NDAs, and maintain a forensic audit trail.
My Recommendation
Stay with OneDrive if your sharing is internal, your files are not deal-sensitive, and you are already invested in the Microsoft ecosystem. Do not add tools you do not need.
Add a data room like Peony if you are sharing investor decks, M&A materials, legal documents, or client deliverables externally. Peony adds the viewer-level controls OneDrive lacks — page analytics, dynamic watermarks, screenshot protection, NDA gates, and e-signatures — without replacing your internal OneDrive setup.
You can start for free at peony.ink, and Pro plans start at $20/admin/month. Most teams are live within five minutes. Unlike legacy data rooms that require weeks of setup and six-figure contracts, Peony was built for modern deal teams that need security without the overhead.
For a full walkthrough of data room features and how they compare to general cloud storage, see our pillar guide: what is a virtual data room.
Frequently Asked Questions
Is OneDrive safe for storing personal files?
Yes. OneDrive uses AES-256 encryption at rest, TLS encryption in transit, and offers Personal Vault with biometric authentication. For personal photos, documents, and everyday files, OneDrive provides strong protection. It falls short when you need to share sensitive business documents externally, because it lacks page-level analytics, dynamic watermarks, and screenshot protection. Peony adds all three on top of encryption, so you can see exactly who read which page and for how long.
What encryption does OneDrive use?
OneDrive encrypts files at rest with AES-256 and in transit with TLS 1.2. Microsoft manages the encryption keys, which means Microsoft can technically decrypt your files for legal compliance or service operations. This is not zero-knowledge encryption. If you need the data owner to control access completely, Peony layers viewer-side controls like dynamic watermarks, NDA gates, and screenshot protection on top of encryption, so even after a file is opened the content stays protected.
Can Microsoft access my OneDrive files?
Yes. Microsoft retains administrative access to OneDrive data for service operations and legal compliance. Under the CLOUD Act, US authorities can compel Microsoft to hand over data regardless of where it is stored. In 2025, Microsoft's own chief legal officer admitted under oath that the company cannot guarantee EU data is safe from US access requests. If regulatory exposure matters, Peony provides screenshot protection, dynamic watermarks, and granular access revocation so you retain control even after someone opens a document.
Is OneDrive secure enough for fundraising documents?
OneDrive stores files securely, but it does not tell you which investor opened your deck, which slides they spent time on, or whether they forwarded the link. During a fundraise, that visibility gap costs you follow-up opportunities. Peony gives you page-level analytics showing exactly which pages each reviewer read and for how long, plus NDA gates that require a signature before access. You can set up a branded investor data room in under five minutes.
What are the main security limitations of OneDrive for business use?
OneDrive lacks dynamic watermarking, screenshot protection, page-level analytics, built-in NDA enforcement, and native e-signatures. Shared links can be forwarded without detection, and audit trails cover basic access logs but not granular engagement data. For internal team collaboration inside Microsoft 365 these gaps rarely matter, but for external sharing of sensitive documents they create real exposure. Peony fills every one of those gaps in a single platform starting at a free tier, with Pro at twenty dollars per admin per month.
How does OneDrive security compare to a virtual data room like Peony?
OneDrive is a file storage and collaboration platform with strong baseline encryption and compliance certifications. A virtual data room like Peony is purpose-built for controlled external sharing. Peony adds dynamic watermarks with viewer identity baked into every rendered frame, screenshot protection that blocks and logs capture attempts, page-level analytics, NDA gates, AI-powered auto-indexing, and built-in e-signatures. Think of OneDrive as a secure filing cabinet and Peony as a secure conference room where you control who sees what, when, and how.
Has OneDrive had any recent security vulnerabilities?
Yes. In May 2025, a File Picker OAuth flaw let third-party apps access a user's entire OneDrive storage even when they selected only one file. Apps like ChatGPT, Slack, and Trello were affected. Separately, Microsoft's Prompt to Add Personal Account feature raised data-leakage concerns by syncing personal accounts with business tenants. In March 2026, a Windows security update broke Microsoft 365 connectivity including OneDrive for roughly 36 hours. Peony's architecture isolates each data room with independent access controls and real-time audit logs, so a platform-level vulnerability does not expose every document you have shared.
Is OneDrive HIPAA and SOC 2 compliant?
Microsoft 365 Business and Enterprise plans can be configured for HIPAA compliance with a signed BAA, and Microsoft holds SOC 2 Type II certification. However, compliance certification covers infrastructure, not how you share documents. OneDrive does not enforce viewer-level audit trails, watermarking, or access gating that regulators often expect in practice. Peony provides SOC 2-ready controls with per-viewer audit trails, AI redaction for PII, and NDA gates, so your compliance posture extends all the way to the recipient's screen.
Should I use OneDrive or a data room for M&A due diligence?
Use a dedicated data room. M&A due diligence requires granular permissions per document, dynamic watermarks to trace leaks, NDA enforcement before access, and detailed audit trails for regulatory reporting. OneDrive supports basic folder-level permissions and access logs, but it was not designed for multi-party controlled disclosure. Peony's M&A data room includes all of the above plus AI-powered Q&A workflows where counterparties submit questions, AI drafts answers, and your team approves before responses are sent.
What is the cheapest way to securely share sensitive documents?
OneDrive is included with Microsoft 365 subscriptions starting around six dollars per month, but adding the external sharing controls it lacks, like e-signatures from DocuSign and advanced analytics from a separate tool, can push the total past fifty dollars per user per month. Peony offers a free tier for basic use, Pro at twenty dollars per admin per month with page analytics, watermarks, screenshot protection, NDA gates, and built-in e-signatures, and Business at forty dollars per admin per month with AI redaction and advanced Q&A. For most teams, Peony replaces three or four separate tools at a lower combined cost.
Related Resources
- What Is a Virtual Data Room? — comprehensive guide to VDR features and use cases
- Virtual Data Room vs Cloud Storage — detailed comparison of when each tool fits
- Top 10 OneDrive Alternatives — scored comparison of OneDrive replacements
- Top 10 Virtual Data Room Providers — ranked list of VDR platforms
- How to Send Confidential Documents via Email — seven methods ranked by security level
- Secure File Sharing Guide — complete framework for protecting shared files
- Document Sharing Compliance Guide — SOC 2, GDPR, HIPAA, and CCPA requirements in one place
- Data Room for Investors — how to set up and manage an investor data room
You might also like
Apr 1, 2026
OneDrive Analytics (What You Can and Cannot Track) in 2026
Apr 24, 2026
How to Watermark a CIM with Buyer Identity and Timestamps (2026)
Apr 9, 2026
6 Best Document Watermark Software in 2026: Peony vs Digify vs Acrobat
