Permission & Security Settings
Configure who opens your Peony data room and what they can see. Choose Email Access or Link Access, then stack 8 security controls per group and set per-folder permissions.
Last updated April 18, 2026
Peony gates every data room at two levels: who can open it (access mode) and what they can do inside (security controls + folder-level permissions). You configure all of it per group — a named audience like "Series A investors" or "Buyer: Acme Corp."
For maximum control, use Email Access with individual emails. For speed, use Link Access with email gating. Either way, the same eight security controls apply.
Two Access Modes
Open any data room, click Share Securely, pick a group, open the Participants tab. You'll see the choice:
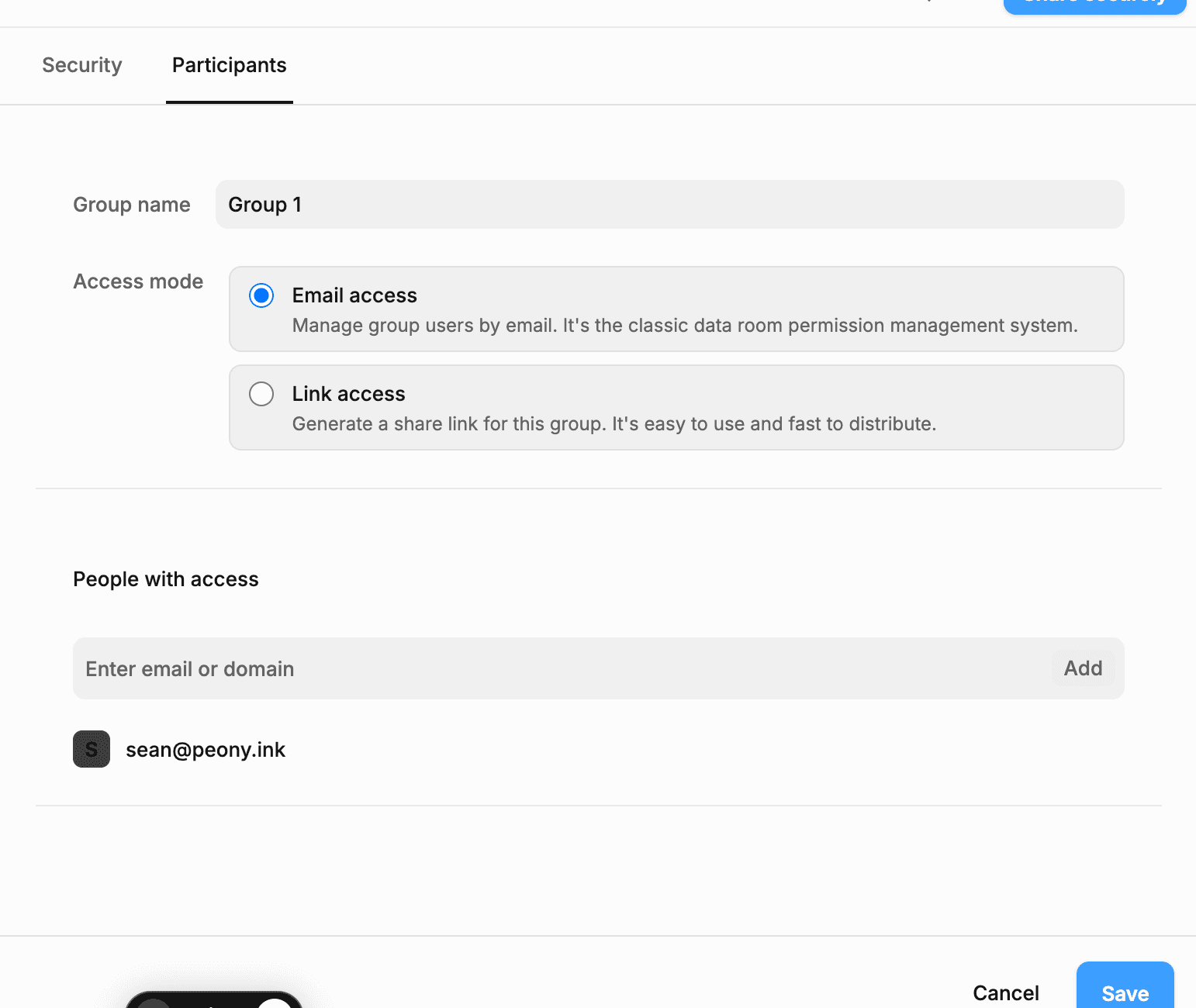
Email Access (recommended for deals)
You enter each allowed email (or domain). Only those recipients receive an invitation email; everyone else is blocked by default. Use this for fundraising, M&A, diligence — any time you need a clean audit trail of who got the invite.
Link Access
Peony generates one share link for the group. You send it via any channel; anyone with the URL attempts access. Use this for high-volume distribution — paid newsletters, open investor updates, conference attendees — and layer email gating on top so you still know who opened it.
Rule of thumb: If you know the recipients, use Email Access. If you don't, use Link Access with email gating on.
The 8 Security Controls (Both Modes)
Click the Security tab inside any group. Each control is independent — toggle what you need.
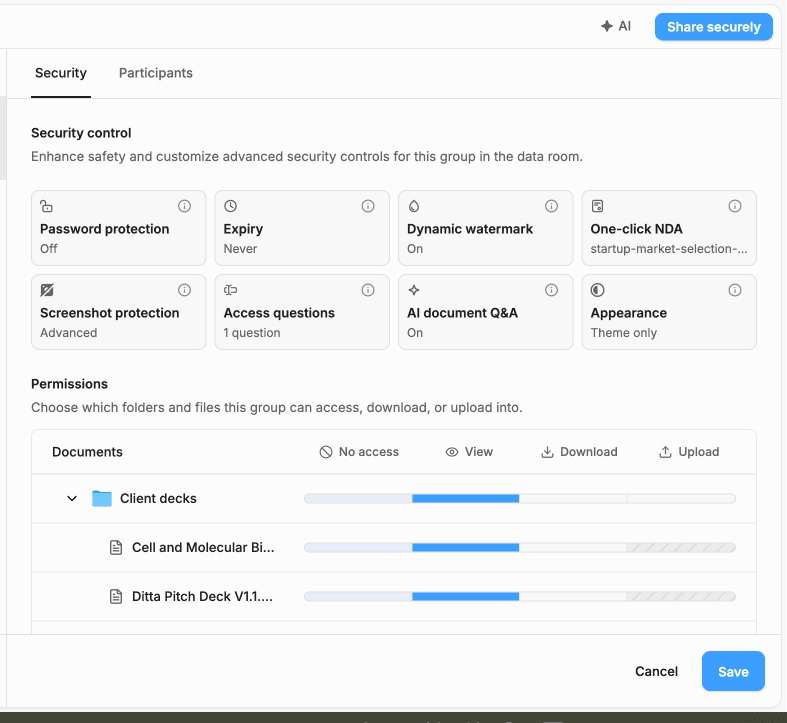
- Password protection — optional shared password, sent out-of-band (Signal, phone).
- Expiry — auto-revoke access on a date you pick.
- Dynamic watermark — viewer email + IP overlaid on every page. See Dynamic Watermarks.
- One-click NDA — upload a PDF for acknowledgment or select a template for e-signature. See NDA Gates.
- Screenshot protection — blocks desktop captures and logs attempts. See Screenshot Protection.
- Access questions — custom questions the viewer answers before entry (e.g. "Which fund are you from?").
- AI document Q&A — allow or disable in-room AI search for this group.
- Appearance — group-specific theme, or full custom branding (logo, colors, domain) on Business.
Granular Folder & File Permissions
Under the Security tab, the Permissions table (bottom of the same panel) lets you set No access / View / Download / Upload for every folder and file in the room — per group.
Typical M&A pattern: give Tier-1 buyers View on the full tree plus Download on the teaser, but No access on customer lists until LOI. Use the slider under each row to choose the level. Children inherit the parent folder's setting unless you override them.
Groups: The Permission Container
Groups are Peony's unit of permissioning. Each group has its own security stack, participant list, and folder permissions. A group's participant list can be anything from one person to dozens — you decide.
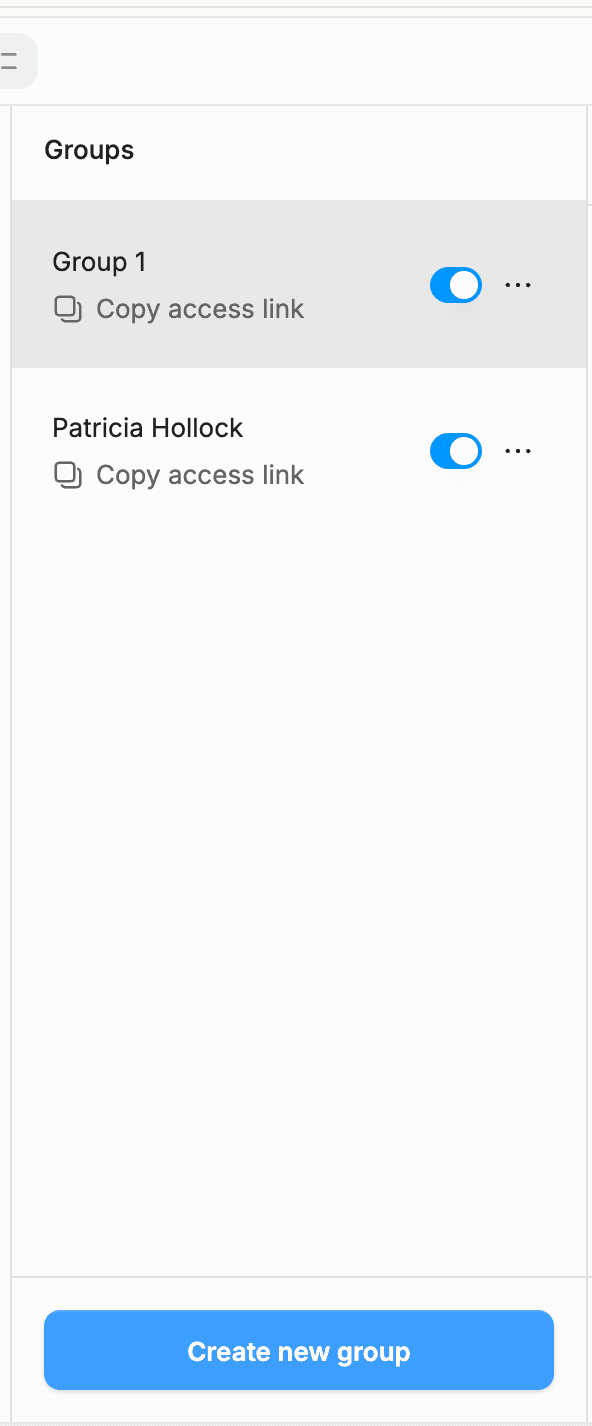
Create a new group whenever an audience needs different permissions from another — different NDA, different watermark, different folders visible. Different VCs, different buyer firms, different LPs typically each get their own group. This gives you:
- Independent security settings (NDA on for one, off for another)
- Separate analytics per group
- Clean revocation (kill a group without touching the others)
If two audiences should see the exact same thing under the exact same rules, one group holding both sets of emails is fine.
Sharing a Tailored Version With One Person
A group's link can be sent to one recipient or to fifty — it's not limited. But if you want one specific person to get their own version (say, a buyer who should see an earlier data snapshot, or an investor who gets one extra folder), create a new group dedicated to them. You can tune that group's security and folder access without touching anyone else's.
Domain Gating
In Email Access, the Participants input accepts either a full email (sean@peony.ink) or a bare domain (peony.ink). Enter a domain and anyone with an address at that domain can accept the invite.
Useful for enterprise diligence where the buyer's deal team is large and not fully named yet. For higher security, stick to individual emails — everyone not listed is blocked by default, and you keep a per-person audit trail.
Link Access Adds a 9th Control: Email-Gated Access
Switch the group to Link Access and a ninth control appears: Require email. Open it to configure:
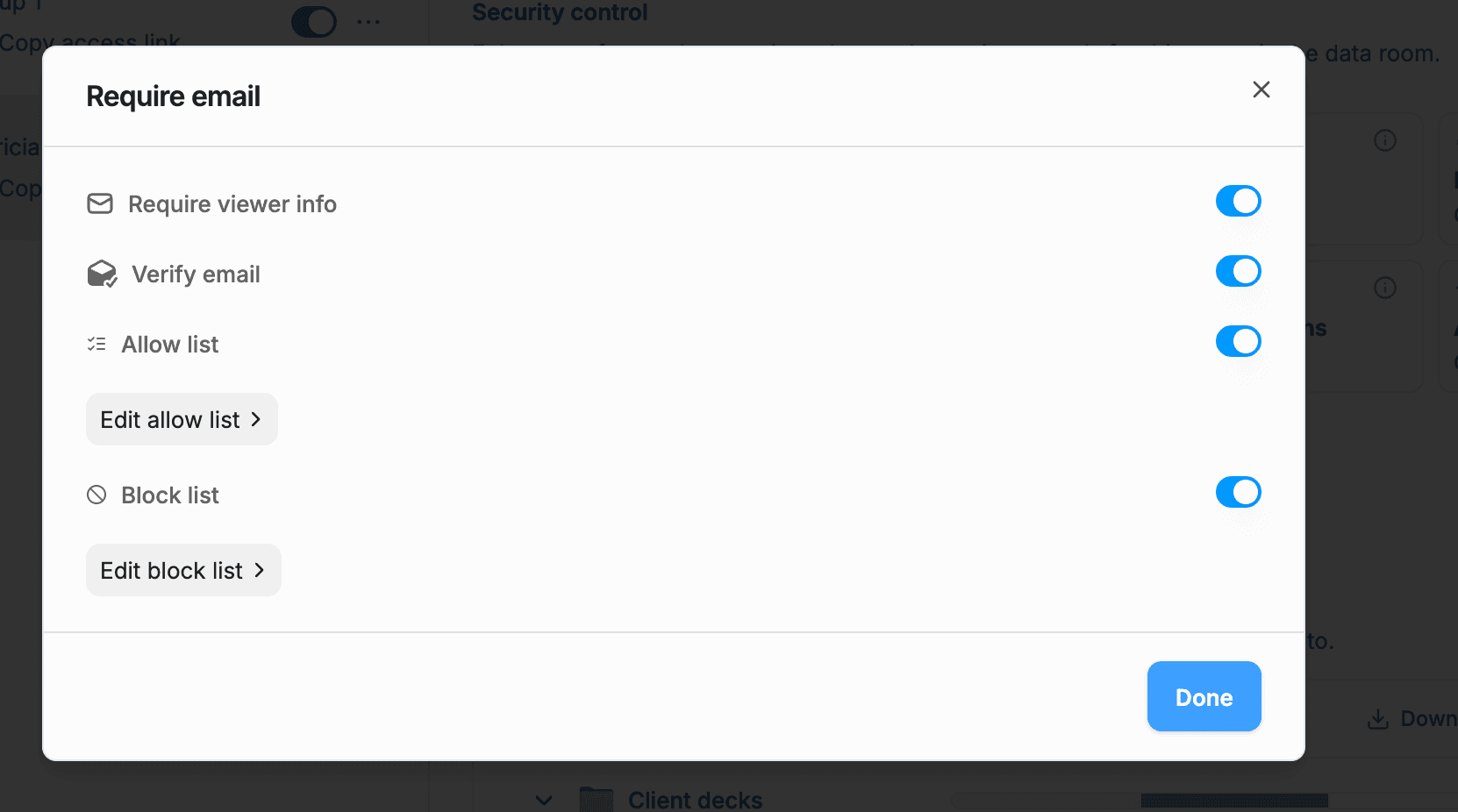
- Require viewer info — viewer must enter an email before the room loads.
- Verify email — Peony sends a one-time code to prove the viewer owns the address.
- Allow list — only listed emails or domains proceed past the gate.
- Block list — listed emails or domains are rejected; everyone else proceeds.
Email Access vs Link Access + Email Gating
This is the question most teams get wrong:
| Email Access | Link Access + Email Gate ON | |
|---|---|---|
| Who receives the invitation email? | Only the emails you list | Nobody — you send the URL yourself |
| Default behavior for unlisted emails | Blocked | Allowed (unless on block list) |
| Audit trail of invitees | Yes, you listed them | No — you only see who opened |
| Best for | Deals with named counterparties | Broad distribution (newsletters, teaser decks) |
Both capture the viewer's email for watermarks and analytics. The difference is the default: Email Access denies everyone but the list. Link Access allows everyone but the block list.
For anything sensitive, use Email Access. Use Link Access only when reach matters more than a clean list.
Saving Your Changes
Hit Share Securely (or Save) at the bottom of the Participants or Security panel. Added emails trigger invitation emails immediately. Toggle changes apply the next time any viewer opens the room.
Common Mistakes
- Reusing Group 1 for every audience. You lose per-group analytics and one viewer's revocation affects the rest. Create a group per audience.
- Link Access without email gating. Anyone with the URL walks in. At minimum toggle Require viewer info and Verify email.
- NDA on, but configured on the wrong group. NDA gates are per-group. Toggle it on the group you're actually about to share.
- Ignoring folder permissions. Security controls don't limit which files the group sees. Use the Permissions table to hide folders per group.
- Leaving downloads on while expecting the watermark to hold. Pair watermarks with Download disabled in the Permissions table.
Common Questions
Which mode is more secure, Email Access or Link Access? Email Access. Its default is deny-all-except-listed, so nobody outside your list sees the room even if the URL leaks. Link Access with email gating approximates this but requires you to maintain a block list rather than a trusted list.
Can I switch modes after I've already shared? Yes. Switch in the Participants tab and save. Any active link keeps working under the new rules on the next open.
Do the 8 security controls behave the same way in both modes? Yes — password, expiry, watermark, NDA, screenshot protection, access questions, AI Q&A, and appearance apply identically in both modes. Link Access just adds Require email as a ninth control.
Do viewers need a Peony account? No. Viewers never sign up. They enter their email at the gate, verify the OTP if enabled, and read the room in the browser. Viewer access is free and unlimited on every plan.
What happens if someone forwards my link to a colleague? In Email Access, the colleague is blocked unless you added them. In Link Access with Verify Email on, the colleague must pass the allow or block list; if they're not blocked, they proceed and appear in analytics under their own email.
Can I watermark differently per group? Yes. Watermark is a per-group setting in the Security tab. Turn it on for external buyers, off for your internal team group.
Can I share a group's link with multiple people? Yes. A group's participant list or share link can go to one person or to dozens. Groups exist to separate audiences that need different permissions — not to cap how many viewers one group holds.
Next Steps
- Invite Viewers and Track Who Opened — what happens after a viewer accepts
- Access Control Layers — which controls to stack for each use case
- Dynamic Watermarks
- NDA Gates
- Screenshot Protection
